Cybersecurity Certifications: A Major Asset
In today’s digital era, where security breaches and cyber threats loom larger than ever, the demand for cybersecurity professionals who are able to implement effective cyber risk management programs continues to grow. Cybersecurity certification is a cornerstone for practitioners aiming to enter or excel in the field. Cybersecurity certifications validate the expertise, skills, and commitment of an information security professional and proves to employers and clients their ability to problem solve. Systems administrators, information security managers as well as early career security analysts can all benefit from various cybersecurity certifications.

Cybersecurity certifications test an individual’s competencies and skills in the various domains of cybersecurity. These certifications are governed by accredited bodies and are designed to assure employers and clients of an IT professional's technical acumen and adeptness in securing information systems facing cyber threats. At a time when the digital landscape is rapidly evolving and becoming increasingly complex, cybersecurity certifications can also ensure that professionals are continually expanding their knowledge of new tactics and best security practices.
What is a cybersecurity certification?
Cybersecurity certification is a formal process by which individuals demonstrate their knowledge, skills, and abilities in various areas of information security. Professional certification typically involves passing an exam that covers a range of topics, from network security and risk management to compliance and incident response. According to the International Information System Security Certification Consortium, most often known as ISC2, cybersecurity certifications are essential as they validate an individual’s ability to effectively design, implement, and manage best-in-class cybersecurity programs. Similarly, the Information Systems Audit and Control Association (ISACA) notes that certifications like the Certified Information Security Manager (CISM) are critical in establishing global standards for understanding and navigating the complex governance of IT and the safeguarding of data assets. Cyber and IT professionals gain a competitive edge in the job market and contribute to raising the standard of practice within the industry, making certified professionals an invaluable asset to their organization.
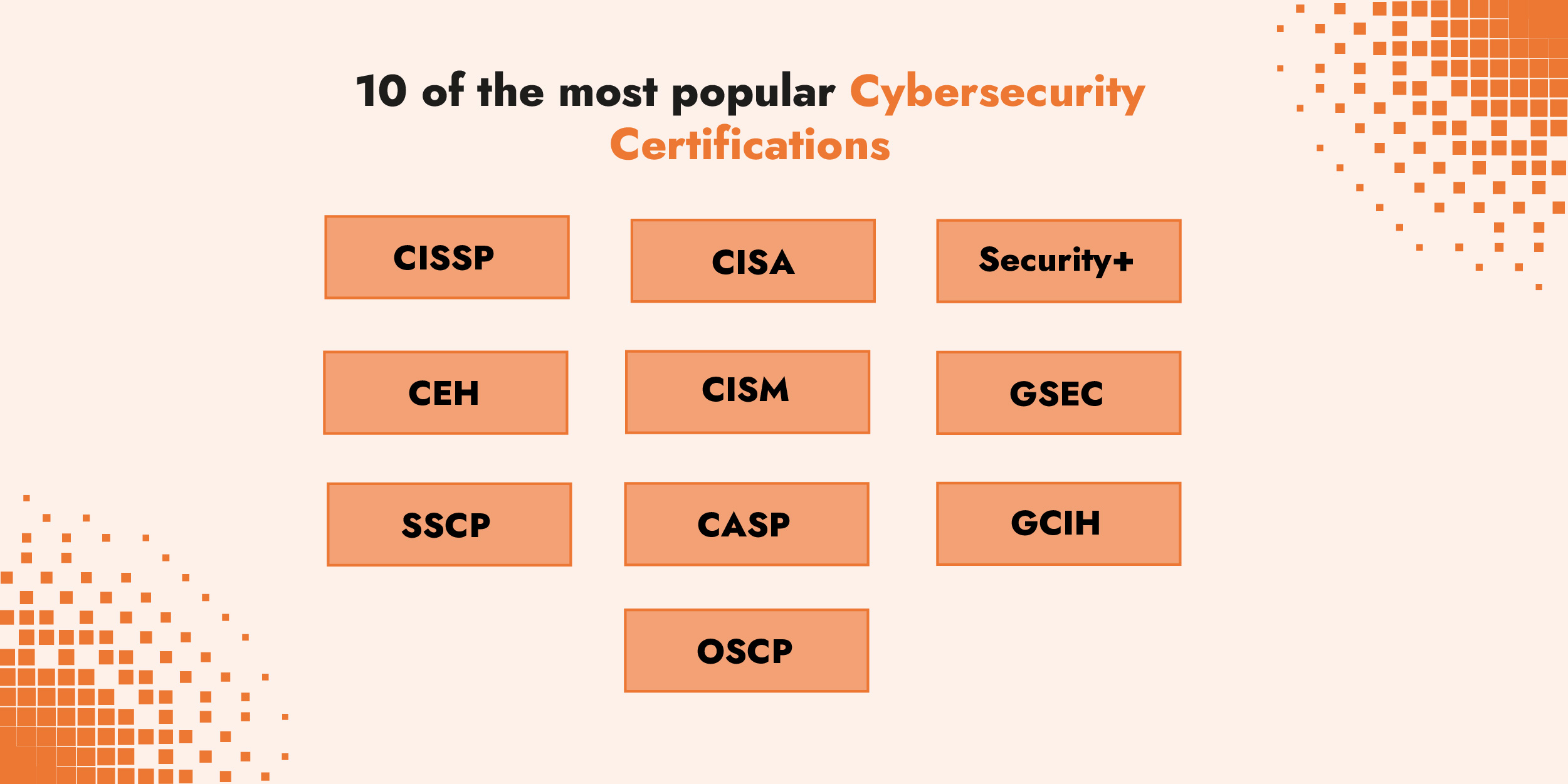
In March 2024, Coursera, the open online course provider, published a list of the top ten cybersecurity certifications from job listings in the US across LinkedIn, Indeed and Simply Hired.
The CISSP from ISC2 was the most requested certification for LinkedIn job offers. Whereas CompTIA Security+ was more common on the hiring site Simply Hired. There is no consensus on the best certification to have, but continually adding to your knowledge base and validating your new skills with certifications will help advance in your career.
Prerequisites for professional cybersecurity certifications
Before preparing for a cybersecurity certification, it's crucial to understand the prerequisites each certification requires. These prerequisites vary widely among different certifications and are designed to ensure that candidates have the necessary foundation of knowledge and experience. For instance, some certifications may require candidates to have several years of relevant professional experience in cybersecurity roles such as systems administration or network security. Others might mandate that candidates first obtain a preliminary certification before advancing to more specialized certifications. This tiered approach to certification helps maintain a standard of proficiency, ensuring that professionals are adequately prepared for the complex challenges they will face in the field and are not just theoretically but practically equipped to tackle real-world security issues.
According to ISACA, CISM certification, for example, requires candidates to have five years of experience in the Information Security Management field before qualifying to take the exam. Typically, to take the CISSP exam a candidate is required to have five years of full-time experience in two or more of the eight domains of the current CISSP Exam Outline. However, if a candidate does not fulfill the work experience requirement, they can still take the exam and become an Associate of ISC2. Then they will have six years to earn the required five years of work experience to become a Certified Information Systems Security Professional.
Academic approach to cybersecurity certification
Beyond professional certifications, there is an academic route that future cybersecurity experts can pursue. Most universities around the world have a computer science program that offers courses in information security and cybersecurity, blending current practices with cutting-edge research. These academic programs often integrate coursework with professional certifications and specializations in areas such as penetration testing, cloud security, and systems administration. For aspiring professionals, the academic approach provides a solid theoretical foundation coupled with hands-on training, preparing young professionals for the complexities of real-world cybersecurity challenges.
In the United States, computer science ranks among the top ten most popular undergraduate degree programs, reflecting a growing interest in the technical and security disciplines. Graduates of these programs emerge proficient in security fundamentals, with a deep understanding of information security, application security, and network security principles. This knowledge equips them to effectively analyze and resolve security challenges across diverse contexts.
Additionally, these programs cultivate leadership skills tailored for cybersecurity, enabling graduates to identify, analyze, model, and prioritize threats. They learn to categorize and mitigate risks, crafting comprehensive strategies to reduce organizational vulnerabilities. Incident response and management also form a crucial part of the curriculum, where students study both successful and unsuccessful security responses, gaining insights into how enterprises assess impacts and strategize to mitigate damage while preventing future breaches.
An undergraduate or post-graduate degree will further a student's technical and theoretical knowledge and prepare them to lead with confidence in their future cybersecurity careers, making university programs a cornerstone for developing future leaders in the field.

Validation of skills and expertise in cybersecurity
Adapting to technological advancements and evolving threats is important for cyber professionals, certifications ensure that professionals are up to date with the latest security practices and technologies. Preparing for a certification exam shows a high level of dedication and commitment on the part of the IT professional. The certification process requires individuals to invest significant time and effort in studying and mastering new concepts. Employers and clients recognize this commitment, viewing certified professionals as individuals who are serious about their careers and willing to go the extra mile to ensure excellence.
For employers, this reduces the risk associated with hiring and provides assurance that a cyber professional is competent and has specific knowledge for their role. For the professional, it offers a pathway for career advancement within the industry.
Trust and credibility in the market
In a business environment where trust is paramount, having certified cybersecurity professionals can significantly enhance an organization’s reputation. Clients and partners feel more secure knowing that their sensitive information is protected by individuals who have proven their expertise through certification. This trust is crucial for building long-term relationships and securing business deals.
Competitive advantage for both the employee and employer
For Employees
Career Advancement
Certified professionals often find it easier to advance in their careers. Certifications can open doors to higher-level positions, increased responsibilities, and better salary prospects.
Increased Marketability
In a crowded job market, having a certification sets a candidate apart from others. It demonstrates to potential employers that the individual has the necessary skills and knowledge to excel in their role, making them more attractive to hire.
Professional Network
Earning a cybersecurity certification like CISSP or CISM provides access to a network of other professionals. This can lead to valuable connections, mentorship opportunities, and insights into industry trends and best practices.
For Employers
Enhanced Security Posture
Hiring certified professionals ensures that the organization has skilled individuals capable of protecting its digital assets. This reduces the risk of cyber incidents and enhances the overall security posture of the company.
Regulatory Compliance
Many industries require organizations to comply with specific cybersecurity standards and regulations. Employing certified professionals helps ensure that the organization meets these requirements, avoiding potential fines and legal issues.
Client Confidence and Trust
Clients and partners are more likely to trust an organization that employs certified cybersecurity professionals. This trust can lead to stronger business relationships, repeat business, and an enhanced reputation in the market.
Competitive Edge
Organizations that prioritize hiring certified professionals demonstrate a commitment to excellence and security. This can be a significant differentiator in the market, attracting clients who value robust cybersecurity practices.

Entry level to advanced: differences in cybersecurity certification
Cybersecurity professionals can pursue various levels of certification to demonstrate their expertise and advance their careers. Certifications range from entry-level to advanced, each designed to equip candidates with the necessary skills and knowledge to address specific cybersecurity challenges. Understanding these differences is crucial for professionals at any stage of their career.
Entry-Level Certifications
Entry-level certifications are intended to validate the skills and knowledge of entry-level cybersecurity professionals or early-career professionals.
Certified Ethical Hacker (CEH)
The CEH certification is an entry level certification for beginners looking to enter the field of ethical hacking. It focuses on identifying vulnerabilities in computer systems and networks using the same tools and techniques as malicious hackers. Candidates learn about hacking laws and ethics, reconnaissance techniques, system hacking, malware threats, sniffers, social engineering, denial-of-service attacks, and more. This certification is beneficial for those aspiring to roles such as penetration testers or security analysts.
CompTIA A+
CompTIA A+ is often considered a starting point for anyone new to IT, including cybersecurity. It covers foundational IT concepts such as hardware, networking, mobile devices, operating systems, and troubleshooting. Although not exclusively focused on cybersecurity, it provides the necessary IT background that is essential for a career in cybersecurity. It is a vendor-neutral certification, making it versatile for various IT roles.
ISACA Cybersecurity Fundamentals Certificate
Aimed at individuals just starting in cybersecurity, this certification provides a solid foundation in the key areas of cybersecurity. It covers essential concepts such as threat landscape, security operations and response, information security fundamentals, and securing assets. This certification is good for students or professionals looking to up-skill or to pivot into cybersecurity from another field.
Intermediate to Advanced Certifications
As professionals gain experience and knowledge, they may seek intermediate to advanced certifications to specialize in specific areas or take on leadership roles.
CompTIA PenTest+
This certification is for beginners to learn some of the foundational skills and principles related to penetration testing and vulnerability management. It validates hands-on skills required to test devices in new environments such as the cloud and mobile, along with traditional desktops and servers. Topics covered include planning and scoping, information gathering and vulnerability identification, attacks and exploits, reporting and communication, and tools and code analysis.
Certified Information Systems Security Professional (CISSP)
The CISSP is an advanced certification for experienced cybersecurity practitioners. It covers a broad range of topics, including security and risk management, asset security, security architecture and engineering, communication and network security, identity and access management, security assessment and testing, security operations, and software development security. It is highly regarded and often required for senior security roles.
Certified Information Security Manager (CISM)
CISM is designed for management-focused individuals who build and manage enterprise information security programs. It focuses on risk management, governance, incident management, and program development and management. This certification is ideal for those seeking to transition from technical roles to managerial positions.
Offensive Security Certified Professional (OSCP)
The OSCP certification is known for its hands-on examination, where candidates must demonstrate their ability to exploit vulnerabilities and perform penetration testing in a controlled environment. It is highly respected in the field of ethical hacking and penetration testing.
Certified Cloud Security Professional (CCSP)
With the growing adoption of cloud technologies, the CCSP certification addresses the unique security challenges of cloud computing. It covers cloud architecture, governance, risk management, compliance, cloud data security, and cloud platform security.
FAIR certification and cybersecurity-adjacent certifications
In addition to the most well-known cybersecurity certifications, there are specialized certifications and training programs that cater to specific needs of cybersecurity professionals and emerging areas within cybersecurity governance, compliance and sustainability. Risk management and business continuity are massively important to cybersecurity strategies. Cybersecurity professionals with these kinds of polyvalent skills are highly sought after.
Factor Analysis of Information Risk (FAIR) certification
The Open FAIR™ (Factor Analysis of Information Risk) standard is an accurate quantitative risk analysis model that helps organizations understand, analyze, and measure information risk in financial and probabilistic terms. Within a security program, FAIR is used by cybersecurity and risk management analysts to decompose cyber risk scenarios, map controls to a cyber kill chain, assess third-party risk, prioritize security investments and communicate with leadership. A data-driven, risk-based approach to cyber risk management is a way to meet new regulatory requirements on governance and risk.
Training in Cyber Risk Quantification using the FAIR methodology
FAIR training equips professionals with the skills to apply this model effectively. C-Risk provides training focused on using an accurate model, including understanding risk measurement concepts, developing risk scenarios, using FAIR to analyze risk, and communicating risk in financial terms. C-Risk’s CRQ training is particularly valuable for risk analysts, security managers, and executives involved in risk management decisions.
Business Continuity Certification
The Business Continuity Institute provides comprehensive business continuity training courses and certification that cover the full range of practices used by business continuity professionals to develop, implement, and maintain an effective business continuity management system.
Disaster Recovery Certified Expert
The Disaster Recovery Institute International is a non-profit organization that helps organizations prepare for and recover from disasters by providing training courses, certification exams, and thought leadership on resilience and disaster recovery.
ISO 27005/27001 Lead Certification
The ISO 27005 and ISO/EC 27005 Lead certification validates an individual's ability to establish implement and manage an information security management system (ISMS).
Conclusion
Cybersecurity certification is a major asset for professionals seeking to excel in their field. Certifications validate your expertise and enhance career prospects and credibility among your peers and higher ups. As cybersecurity threats continue to evolve, it is crucial for professionals to stay updated with the latest practices and technologies.
Whether you're an early-career professional or an experienced cybersecurity risk manager, investing in cybersecurity certification and training is a strategic move.
For more information on C-Risk's CRQ training, please visit our contact page for more information or schedule a call with our training manager here.
Related articles
Read more on cyber risk, ransomware attacks, regulatory compliance and cybersecurity.

.svg)


