CISSP: An in-demand certification for cybersecurity professionals
The CISSP certification is considered the gold standard for cybersecurity and IT professionals within the information security industry. Becoming CISSP certified can have a profound impact on your career trajectory. This globally recognized certificate validates in-depth knowledge and hands-on experience of cybersecurity and IT/ICT professionals within the eight domains of information security defined by (ISC)². Employers actively seek out CISSP-certified professionals for their ability to effectively design, implement, and manage a best-in-class cybersecurity program.

What is the CISSP certification?
The Certified Information Systems Security Professional (CISSP) certificate is an advanced-level cybersecurity management certification for IT professionals. It is issued by (ISC)², a non-profit that specializes in training and certifications for cybersecurity professionals. The certification requires cybersecurity professionals to have at least five years of work experience before sitting the exam.
What is (ISC)²?
The International Information System Security Certification Consortium, more commonly referred to as (ISC)², is a non-profit organization that was created in 1989. It specializes in education and certifications for information security professionals. (ISC)² is known for developing the CBK, or Common Body of Knowledge.
History of CISSP
In 1989, the International Information Systems Security Certification Consortium, Inc., also known as (ISC)², was established as a non-profit corporation. It was also the year the (ISC)² developed the CBK prototype. In 1994, the first CISSP credential was established and the first iteration of the exam was launched. Additional certifications have been developed and accredited since then and the membership numbers grew.
Since its creation, the CISSP has gained significant recognition to become one of the most sought-after certifications in the information security field. It is globally recognized and is often considered a prerequisite for many senior-level information security roles.
The Common Body of Knowledge
The (ISC)2 CBK is a regularly updated collection of topics that are relevant to cybersecurity professionals around the world. Topics include skills, techniques and best practices. The CBK is a standardized framework for information security terminology and principles. It enables information security professionals around the world to use a common vocabulary to discuss and find solutions to issues they face in their working lives. The CBK has been divided into eight domains which cover the full spectrum of information security.

What are the 8 Domains of CISSP?
The 8 domains of the CBK make up the CISSP (Certified Information Systems Security Professional) certification. The certification is designed to ensure that professionals have a broad understanding of information security principles, ethics, practices, etc. There is some overlap between the domains, particularly where concepts such as risk management, security architecture, and access controls intersect across various aspects of IT security, underscoring the interconnected nature of information security efforts. Each domain has a number of objectives. For example Communication and Network Security has only 3 objectives while Security Operations has 15 objectives. Below are the 8 domains:
o Security and Risk Management
o Asset Security
o Security Architecture and Engineering
o Communication and Network Security
o Identity and Access Management (IAM)
o Security Assessment and Testing
o Security Operations
o Software Development Security
CISSP certification in 2024
The CISSP is the regarded as the gold standard in the field of information security. One of the reasons it remains so well respected by cybersecurity professionals is because the exam topics are continuously reviewed. The (ISC)² process ensures that the credential remains relevant taking into consideration the developments in technology and the threat landscape.
On April 15, 2024, the CISSP exam will update the weighting of the 8 Domains for grading purposes.
Key aspects of the CISSP certification exam
Global Recognition: CISSP is a globally recognized certification in the field of information security and IT. It can help you in your job search or help you move up within your company.
Comprehensive Coverage: The CISSP curriculum and exam covers the eight domains of the Common Body of Knowledge (CBK).
Experience Requirement: To obtain the CISSP certification, candidates must have at least five years of cumulative, paid work experience in two or more of the eight domains of the CISSP CBK. Qualifying certifications or graduate degrees may reduce the requirement by one year.
CISSP Associate: A CISSP certification candidate who doesn't have the required work experience will receive the title of CISSP Associate designation by successfully passing the CISSP exam. The Associate of (ISC)² will then have six years to earn the five years of required work experience in one of the 8 domains. Upon completion of the work experience the title will change to CISSP certified.
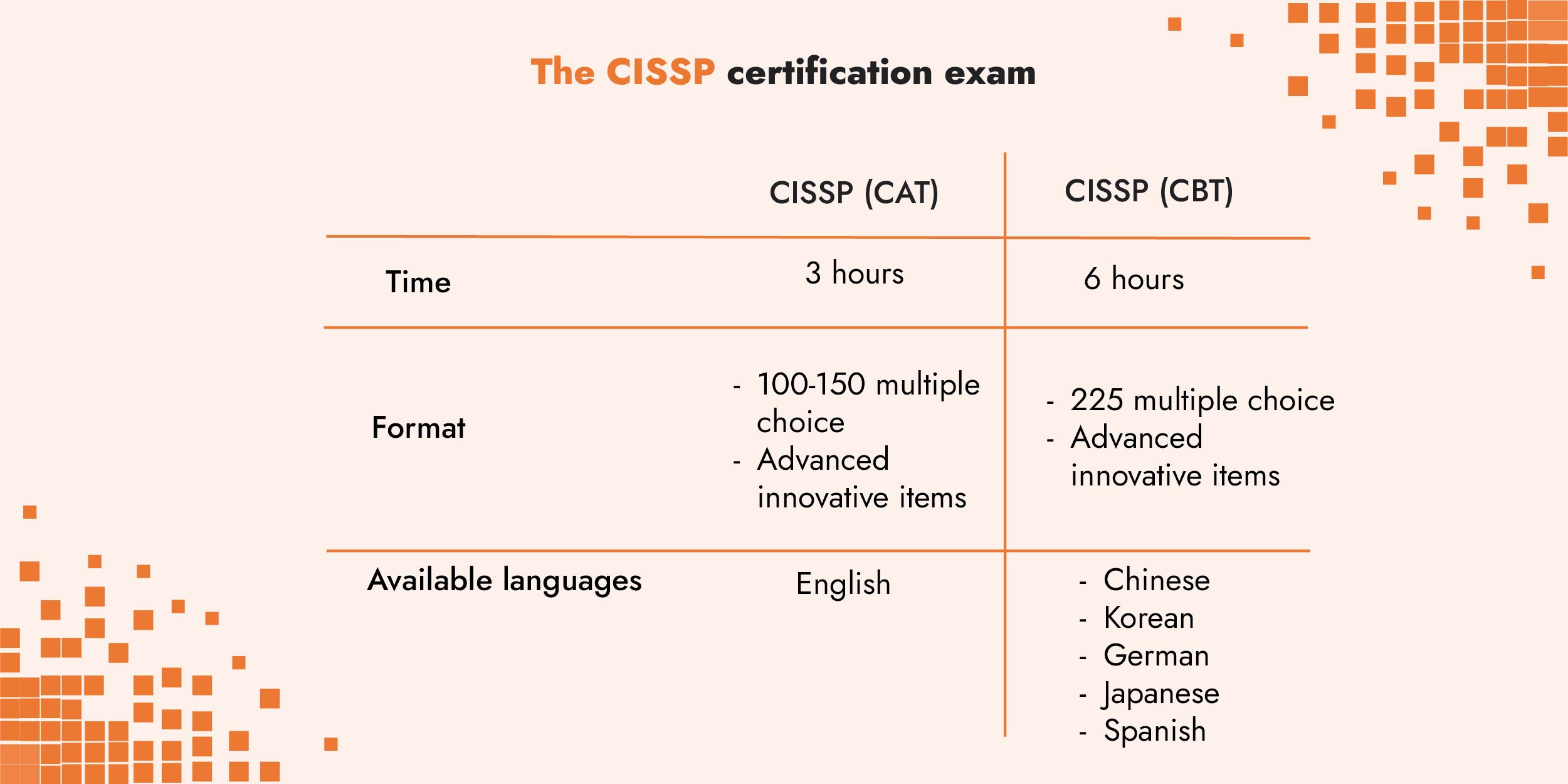
Examination: Two types of exams are offered.
o The CISSP (CAT) is a computer adaptive test. You are given 3 hours to answer between 100-150 multiple choice and advanced innovative items. This exam is only offered in English.
o The CISSP (CBT) is offered in Chinese, Korean, German, Japanese, and Spanish, and contains 225 multiple choice and advanced innovative items. The allotted time for the exam is 6 hours.
Endorsement and Maintenance: After passing the exam, candidates must be endorsed by another (ISC)² certified professional and adhere to the ISC² Code of Ethics. CISSP certification holders must also earn and submit 120 Continuing Professional Education (CPE) credits over a three-year period after becoming certified to maintain their certification. The information on what qualifies as CPE credits is covered on the (ISC)² website.
Career Advancement: CISSP certification is highly regarded in the information security industry. Becoming certified can lead to a better salary and more advanced career opportunities. It's often required for positions such as Security Manager, Security Analyst, Chief Information Security Officer, and many others.
Ethical Standing: CISSP emphasizes the importance of ethical behavior and professional conduct in the field of information security. As stated above, to be certified you are required to follow the (ISC)² Code of Ethics.
How to prepare for the CISSP exam?
As with many exams, there are several ways to prepare for the exam online, self-paced, with textbooks and study groups or as part of a bootcamp. The cost can vary from free if you go the library and check out the official study guide and use free online materials all the way to several thousand dollars if you sign up for a bootcamp.
For the self-paced learner, there are free study materials online as well as paid online courses. The ISC2 offers free CISSP test prep flash cards. There is an official study guide app that exists in a freemium version or a paid version. It is best to reference the ISC2 website for the latest resources.
CISSP, your salary, and job security
On the job market, CISSP certified cybersecurity and IT/ICT professionals can expect to be earn better than their non-certified peers. According to Payscale, of the salaries reported, a Cyber Security Analyst makes between $65k and $104k while a Chief Information Security Officer (CISO) makes between $145k and $252k. The average salary for CISSP-certified professionals for all roles is $128k.
In addition to a higher salary, CISSP certified professionals will benefit from job security. The demand for cybersecurity professionals continues to grow across the globe. According to the U.S. Bureau of Labor Statics, the growth rate for cybersecurity professionals by 2030 is 22%.
Continuing education and training for risk professionals
The dynamic nature of the cyber risk landscape highlights the effectiveness and necessity of continuing education for information security and IT professionals. The CISSP certification remains as a highly-valued certificate for employers and a major accomplishment for those who pass the exam. The path of continuous learning and certification, such as with CISSP certification, ensures that risk professionals remain relevant and integral to shaping a secure digital future.
If you are interested in other types of continuing education, C-Risk provides training in Cyber Risk Quantification for professionals working in the risk management space or anyone who would like to learn more about quantification using the FAIR methodology. To find out more visit the CRQ training page on our website or schedule a meeting with our training manager.
Who should pursue the CISSP Certification?
CISSP is ideal for experienced security practitioners, managers, and executives interested in proving their knowledge across a wide array of security practices and principles. This includes positions such as Security Managers, Security Analysts, Chief Information Security Officers (CISOs), IT Directors/Managers, Security Auditors, Security Architects, and Network Architects.
What are other important cybersecurity and information security certifications besides CISSP?
There are several other key certifications in the cybersecurity and information security fields that professionals can pursue to enhance their knowledge, skills, and career opportunities. Some of these include Certified Information Security Manager (CISM), Certified Information Systems Auditor (CISA), CompTIA Security+, and Certified Ethical Hacker (CEH).
Is C-Risk's CRQ training only for cybersecurity professionals?
C-Risk's Cyber Risk Quantification training programs are designed for business and information security professionals, with an introductory course for non-practitioners as well as an advanced course for risk professionals, who would like to achieve FAIR certification. The FAIR standard is a quantitative model for information security and operational risk. FAIR provides a model for understanding quantifying cyber risk and operational risk in business-relevant terms.
Related articles
Read more on cyber risk, ransomware attacks, regulatory compliance and cybersecurity.

.svg)


