DORA and NIS2: strengthening digital resilience across the EU
The European Union has introduced two major legislative frameworks to address growing cyber and technology risks: the Digital Operational Resilience Act (DORA) and the NIS2 Directive. This article discusses how DORA and NIS2 differ in scope and implementation, while reinforcing the same core principle: operational resilience. Both frameworks extend accountability to ICT and digital third parties, making supply-chain and third-party vendor risk management a regulatory priority for organizations operating in Europe
- DORA applies directly and uniformly across the EU, while NIS2 is implemented through national legislation and varies by Member State
- NIS2 significantly expands the number of in-scope organizations across critical and important sectors
- Both frameworks extend accountability to ICT and digital third parties
- Governance, incident reporting, business continuity, and third-party risk management are central to demonstrating resilience
- A risk-based, data-driven approach supports proportional compliance and sustainable operational resilience
DORA: Strengthening Digital Resilience Across the Financial Sector in the EU
What is DORA?
The EU’s Digital Operational Resilience Act (Regulation (EU) 2022/2554, DORA) will broadly influence how financial entities improve ICT governance, manage ICT risks, disclose incidents, and strengthen their resilience. The financial sector is increasingly dependent on digital services and technology to deliver their services. This digital transformation has made financial entities more vulnerable to cyberattacks and incidents.
DORA is a European regulation introduced by the European Commission in September 2020. The regulation entered into force on January 16, 2023 and became applicable on January 17, 2025. DORA is part of the EU’s digital strategy, which aims to strengthen the digital operational resilience of financial entities operating in Europe and their ICT third parties by establishing a common set of rules and standards to mitigate Information and Communications Technology (ICT) risks.
The financial entities and the ICT services that support the financial entities represent a vital component of the EU’s critical infrastructure. When not managed properly, ICT risks can cause disruptions across borders and across sectors, having an impact on the economy at large. It is also an opportunity for intelligence sharing related to threats and vulnerabilities.
Harmonization for the financial sector across Europe
Prior to the introduction of DORA, the financial services sector in the EU operated without a common framework for ICT and cybersecurity. The regulatory landscape was characterized by a complicated patchwork of both European and national standards that were not harmonized. Additionally, financial institutions had to navigate the complexities of data protection as mandated by the EU's General Data Protection Regulation (GDPR), alongside the necessities of safeguarding critical infrastructure as per the Network and Information Systems (NIS) directive. With no EU regulation, it was left to each Member State to implement and enforce their own laws to address these multifaceted risk management issues.
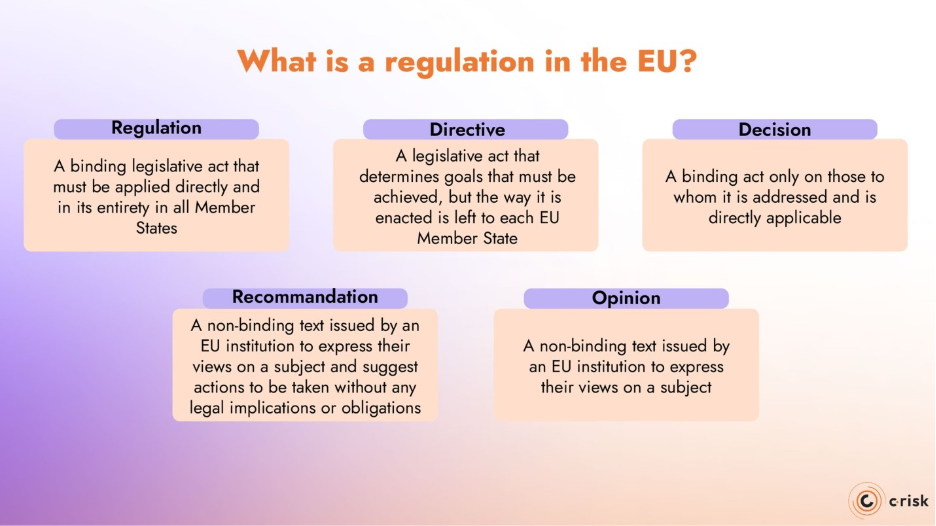
What is a regulation in the EU?
Before diving into the Digital Operational Resilience Act, it is important to understand what the term “regulation” means when discussing EU policies and other types of EU legislative acts.
Outside the EU, their meanings vary from country to country. In the EU, there are five types of legislative or legal acts that enable the EU treaties to achieve their goals. These are regulations, directives, decisions, recommendations, and opinions.
Regulation: A binding legislative act that must be applied directly and in its entirety in all Member States.
Directive: a legislative act that determines goals that must be achieved, but the way it is enacted is left to each EU Member State. The NIS2 Directive came into force in 2023 and every Member State must implement the Directive into national law.
Decision: a binding act only on those to whom it is addressed and is directly applicable. For example, when the Council issues a decision on a Member State adopting the euro, it only concerns a specific country.
Recommendation: a non-binding text issued by an EU institution to express their views on a subject and suggest actions to be taken without any legal implications or obligations on those addressed in the recommendation.
Opinion: a non-binding text issued by an EU institution to express their views on a subject.
What is the scope of DORA?
DORA applies to all financial institutions in the EU which includes traditional financial entities, such as banks, investment firms and credit institutions, as well as non-traditional entities, such as crypto-asset service providers. Article 2(1) of DORA sets out the exhaustive list of covered entities for the EU’s financial sector, with exceptions listed in Article 2(3). In addition, ICT third-party service providers do not have to be based in Europe to come under the regulation. Any third party providing services to a European company is concerned. The specific provisions for the FEs and third-party services providers will be addressed in another post.
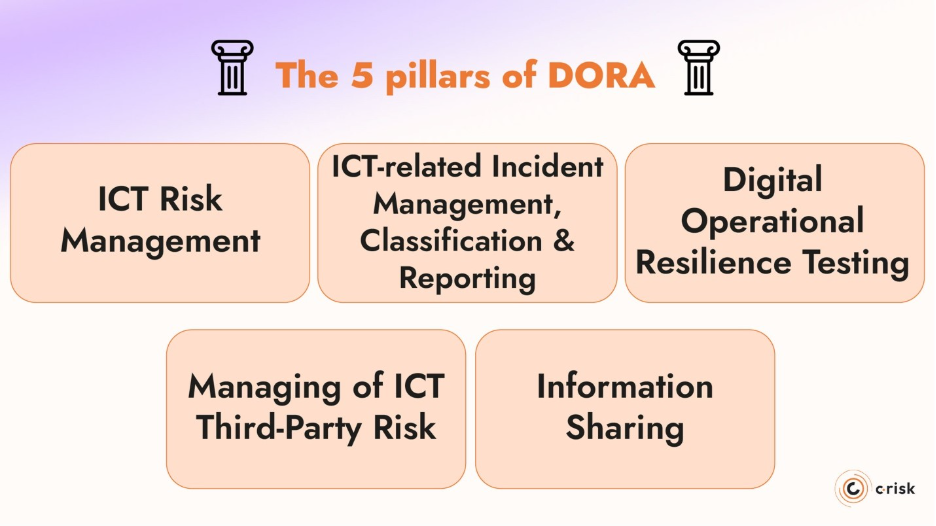
The five key pillars of DORA
The text of the regulation defines five pillars that cover different domains and aspects of ICT and cyber risks that must be addressed by the financial entities to ensure compliance.
ICT Risk Management
Financial entities must have robust governance and control frameworks for effective ICT risk management. This includes, but not limited to, preparing for ICT risks, maintaining up-to-date systems, and implementing digital operational resilience strategies.
ICT-Related Incident Management, Classification and Reporting
Financial entities must establish a process for identifying and managing ICT-related incidents, with major incidents reported to the relevant authority.
Digital Operational Resilience Testing
Regular testing of ICT systems and tools to identify and correct weaknesses or gaps in digital operational resilience. This includes third-party penetration testing and threat-led penetration testing.
Managing of ICT Third-Party Risk
This pillar focuses on the sound management of risks associated with ICT third-party service providers, including due diligence, contractual provisions, and ICT concentration risk.
Information Sharing
Information-sharing with the authorities and among financial entities contributes to the digital operational resilience, particularly in the context of cyber threats and vulnerabilities.
European Supervisory Authorities and DORA
The European Supervisory Authorities (ESAs) work primarily on harmonizing financial supervision in the EU with a set of prudential standards for financial institutions. The ESAs help to ensure compliance and “create a level playing field”. They are also mandated to assess risks and vulnerabilities in the financial sector. The ESAs are:
· the European Banking Authority (EBA)
· the European Insurance and Occupational Pensions Authority (EIOPA)
· the European Securities and Markets Authority (ESMA)
To operationalize the application of DORA, the ESAs though Joint Committee and in consultation with the European Central Bank (ECB) and European Union
Agency for Cybersecurity (ENISA) are mandated to develop 13 policy products in two batches. These policy products include regulatory technical standards (RTS), implementing technical standards (ITS) and guidelines (GL). These policy instruments are necessary to provide detailed technical specifications for the implementation of the legislation.
The first batch of policy products includes:
- RTS on ICT risk management framework and RTS on simplified ICT risk management framework
- RTS on criteria for the classification of ICT-related incidents
- ITS to establish the templates for the register of information
- RTS to specify the policy on ICT services performed by ICT third-party providers
The second batch includes:
- RTS and ITS on content, timelines and templates on incident reporting
- GL on aggregated costs and losses from major incidents
- RTS on subcontracting of critical or important functions
- RTS on oversight harmonization
- GL on oversight cooperation between ESAs and competent authorities
- RTS on threat-led penetration testing (TLPT)
Challenges for DORA compliance
Key challenges for achieving compliance under DORA run parallel to the five pillars of the regulation. Organizations concerned by the regulation need to focus on implementing risk-based policies and procedures to identify, measure, monitor, report, and mitigate ICT and cyber risks. In addition, an essential component for overall digital operational resilience is the regular assessment of ICT and cyber capabilities and security in the event of an ICT-related incident or cyberattack.
NIS2: Strengthening Cybersecurity Across Critical and Important Sectors
What is NIS2?
The NIS2 Directive (Directive (EU) 2022/2555) is the EU’s updated framework for cybersecurity and risk management across critical and important sectors of the economy. It aims to improve the overall level of cybersecurity in the EU by addressing weaknesses identified under the original NIS Directive and by responding to the growing scale, sophistication, and systemic impact of cyber threats.
NIS2 entered into force on January 16, 2023. As a directive, it sets binding objectives at EU level but must be transposed into national law by each Member State. The transposition deadline was October 17, 2024. However as of the writing of this article 17 out of 27 EU Member States have transposed the NIS2 Directive into national law.
While the directive is in effect, implementation and enforcement depend on national legislation, which means requirements and supervisory approaches may vary across countries during the transposition phase.
Like DORA, NIS2 reflects the EU’s recognition that digital and cyber risks can no longer be managed in isolation.
What is the scope of NIS2?
The NIS2 Directive applies to medium and large organizations operating in sectors considered critical to the functioning of the economy and society in the EU. Its scope is significantly broader than that of the original NIS Directive and is based on sector and company size.
NIS2 distinguishes between two categories of in-scope organizations:
- Essential entities, which operate in sectors where disruption could have severe societal or economic consequences
- Important entities, which operate in other critical sectors but are subject to lighter supervisory regimes
The classification determines how supervision and enforcement are applied, but both categories must comply with the same core cybersecurity risk management and incident reporting obligations.
Covered sectors include, among others:
- Energy, transport, banking, and financial market infrastructures
- Health, drinking water, and wastewater
- Digital infrastructure, including cloud service providers, data centers, content delivery networks, managed service providers, and managed security service providers
- Public administration at central and regional levels
- Space, postal and courier services
- Manufacturing of critical products (such as pharmaceuticals, medical devices, and certain industrial goods)
In general, NIS2 applies to organizations with 50 or more employees or an annual turnover exceeding €10 million, although some entities are included regardless of size due to their systemic importance.
More importantly, NIS2’s scope extends beyond the directly regulated entity. NIS2 includes a much wider ecosystem of third-party vendors, suppliers, and digital service providers that support critical activities across Europe.
Core Focus Areas of the NIS2 Directive
There are several focus areas that medium and large organizations must address to strengthen their cybersecurity and operational resilience. These focus areas align closely with the principles underpinning DORA and reflect the EU’s broader, risk-based approach to digital resilience.
Governance and accountability
NIS2 places oversight responsibilities on executives. Management bodies are responsible for approving cybersecurity risk management measures, overseeing their implementation, and ensuring that appropriate policies, controls, and training are in place.
Incident handling and reporting
Entities must be able to detect, assess, and respond to cyber incidents and report significant incidents to national authorities within defined timelines. NIS2 introduces a more structured reporting framework, including early warnings, incident notifications, and final reports, reinforcing the need for clear escalation paths and repeatable reporting processes.
Third-party and supply chain risk management
Organizations must address cybersecurity risks arising from suppliers and service providers, particularly where third-party dependencies affect the delivery of critical services. This effectively extends cybersecurity expectations across the supply chain.
Business continuity and crisis management
NIS2 requires entities to ensure the continuity of critical services through measures such as backup management, disaster recovery, crisis response planning, and timely system restoration following an incident.
Navigating NIS2 Compliance Across EU Member States
A key difference between NIS2 and DORA lies in how they are implemented and enforced across the European Union. DORA is an EU regulation, meaning it applies directly and uniformly in all Member States without the need for national implementing legislation. Once applicable, its requirements are the same across the EU, creating a harmonized framework for the financial sector.
NIS2, by contrast, is a directive. While it entered into force in January 2023, each Member State is responsible for transposing its requirements into national law. This process requires each country to define its supervisory authorities, enforcement mechanisms, and certain procedural details at national level. As a result, the practical application of NIS2 can vary across Member States.
Going Beyond NIS2 and DORA Compliance
Compliance with NIS2 and DORA requires organizations to implement comprehensive cybersecurity and operational resilience capabilities that span technology, processes, governance, and people. For many organizations enterprises, this represents a significant allocation of resources and a shift in how cyber and ICT risks are managed across the organization.
What Role Does Governance Play in Compliance?
Governance is a central component of compliance under both NIS2 and DORA. Meeting requirements related to risk assessment, incident reporting, business continuity, and third-party oversight depends on clear accountability, defined decision-making structures, and coordinated processes across the organization. These obligations cannot be met through technology alone and must be sustained over time as part of day-to-day operations.
How do Organizations Demonstrate Resilience under DORA and NIS2?
DORA and NIS2 both encourage exchanging information and intelligence on threats, tactics or other methods used by cybercriminals to harm organizations. Regulators expect organizations to provide objective, repeatable evidence that cyber and ICT risks are identified, prioritized, and addressed in a way that protects critical services and consumers.
Operational resilience under NIS2 and DORA include:
- Executive accountability for cybersecurity and operational resilience decisions
- Information and intelligence sharing with your peers and regulators about cyber threats, techniques and procedures
- Documented processes for risk assessment, incident response, and continuity planning
- Oversight of third parties and supply chains, including ICT service providers and critical vendors
- Risk-based prioritization, ensuring resources and controls align with the criticality and potential impact of services
Data-driven risk management using quantitative analysis
Building a risk-based program from proportional regulatory requirements
Both NIS2 and DORA are designed to be proportionate. While they set clear expectations around governance, risk management, incident handling, and resilience, the depth and intensity of supervisory scrutiny will vary based on factors such as organizational size, sector, criticality of services, and risk profile.
This proportionality does not reduce the need for structure or discipline. Instead, it reinforces the importance of a risk-based approach that allows organizations to allocate resources in line with actual exposure and potential impact. A risk-based program enables organizations—regardless of size—to demonstrate that compliance efforts are aligned with what matters most, rather than applied uniformly across all risks and controls.
Using data and quantification to demonstrate resilience
Under both DORA and NIS2, resilience must be demonstrated through evidence. Organizations are expected to show that risks are understood, decisions are justified, and critical services can be maintained or restored within acceptable timeframes.
Data-driven risk management and cyber risk quantification make this possible by translating technical risk into measurable outcomes, including financial impact. Quantitative analysis supports clearer governance decisions, more accurate incident reporting, and risk-based prioritization of controls and third-party relationships. When risk is measured consistently over time, resilience becomes observable and auditable.
From regulatory compliance to actionable insight with C-Risk
Cybersecurity and operational resilience regulations such as DORA and NIS2 continue to evolve as threat landscapes, technologies, and dependencies change. In this context, maintaining compliance over time depends on having a data-driven, risk-based approach that can adapt to new requirements without constant rework of controls and documentation.
A data-driven risk management program provides a stable foundation for this adaptability. C-Risk uses cyber risk quantification to address regulatory requirements and help grow your business.
C-Risk helps organizations:
- Quantify cyber and ICT risk in financial terms, supporting risk-based prioritization and proportional decision-making
- Link regulatory requirements to measurable outcomes, rather than checklist-based controls
- Support governance and board oversight with clear, consistent risk metrics
- Assess and compare third-party risk based on criticality, exposure, and potential impact
- Demonstrate resilience over time through repeatable, evidence-based analysis
By embedding quantitative risk analysis into governance, third-party risk management, and resilience planning, C-Risk enables organizations to use compliance as a foundation for evidence-based management of cyber and ICT risk, regardless of size or regulatory scope.
