GDPR compliance and cybersecurity: new challenges for the health sector
Whether you’re building tools to manage a vaccination campaign or share medical information within a hospital system, GDPR compliance and cybersecurity is fundamental.
Why is GDPR compliance so important in times of cybersecurity crisis? While health data are intangible, their disclosure can have very tangible consequences: identity theft, fraud, financial penalties, etc.
Therefore, the best way for a company or public body to protect its data and business is to comply with the GDPR.

GDPR: what is it?
Context: personal data, data processing
Let’s put the GDPR (General Data Protection Regulation) in context before going further. The two pillars of the GDPR are the notions of personal data and data processing. But what do they mean in practice?

According to the French Data Protection Authority, the CNIL (Commission Nationale de l’Informatique et des Libertés), personal data are any anonymous data that can be double checked to identify a specific individual (e.g. fingerprints, DNA, or information such as “the son of the doctor living at 11 Belleville St. in Montpellier does not perform well at school”).
For example: a name, a photo, a fingerprint but also an IP address, a computer login identifier, etc.
Processing personal data means “carrying out an operation or a set of operations involving personal data, regardless of the process used (collection, storage, modification, transmission, etc. ).”
For example: keeping a register of subcontractors, managing payrolls, managing information of marketing prospects, etc.
However, let’s be clear: the GDPR is not so much the birth of a regulation on personal data protection.
In France, a legal framework on data processing was set up as early as the 1970s, with the Law on Information Technology and Freedom of 6 January 1978. This gave birth to the CNIL, an independent administrative authority whose main role is to ensure personal data protection. French legislators were already reflecting on data protection more than 40 years ago.
In Europe, too, the issue was debated for several decades. It was in the 1990s when the foundation of the current legal framework was laid. Faced with rapidly changing technologies and the Internet, the EU recognized the need to legislate on these new subjects. In 1995, it passed a European directive on data protection: the European Data Protection Directive. This text established minimum standards in terms of confidentiality and data security.
These examples of national legislation and the European Data Protection Directive served as the basis for the development of the GDPR that we know today.
Creation, implementation, and objectives of the GDPR
Although several European countries, like France, enacted legislation on personal data protection, the issue was only dealt with at the national level. There was no consensus on all aspects of personal data protection. The process of creating the GDPR began when the European Commission decided to take up this important subject in January 2012.
After consultation rounds, the first draft of the regulation was published in November 2013. Then the legislative back and forth started. The text evolved over the course of negotiations between the European Commission, the European Parliament and the Council of the European Union. In April 2016, just two years after the first draft was submitted, the final version of the text we know today was adopted. This is due to the natural inertia of Europe’s cumbersome lawmaking process as well as the importance of the text that was adopted and the participation of various actors: Member States, companies, and citizens.
The GDPR entered into force in 2016 and applies since 25 May 2018. The general objective of the Regulation is to establish a regulatory framework for personal data protection. This framework is extended and applied equally to all EU Member States. It makes it easier for all EU citizens to understand how their data are used and, if necessary, to lodge a complaint about the processing of their data. This objective is summarized in three key points by the CNIL:
- Strengthening the rights of individuals
- Empowering actors involved in data processing (processors and processors);
- Increasing the credibility of regulation through enhanced cooperation between Data Protection Authorities
GDPR : who’s concerned?
It applies to almost everyone…
As mentioned above, the GDPR aims in particular to make data processing actors responsible. To achieve this, it standardizes the obligations. And that is why it applies de facto to everyone.
Any organization, regardless of its size, country of location and activity, may be affected. If an organization processes personal data on its behalf, it is sufficient for one of the following two criteria to be verified for it to be subject to the GDPR:
- It is established in the territory of the European Union, or
- Its activity directly targets European residents
For example, a foreign company with an e-commerce site in French and delivering products in France must comply with the GDPR because their activity falls under the criteria to be subject to the GDPR.
There is only one exception: the GDPR only applies to legal persons and excludes “any processing by a natural person in the course of a strictly personal or domestic activity.” This prevents the regulation from becoming a legal stranglehold for a small personal website publisher for example.
…and has the merit of not ignoring cases of subcontracting
One of the major flaws of the GDPR could have been to ignore the case of subcontractors. Indeed, many companies and organizations of all kinds rely on third parties to process and collect data on their behalf. And many companies have tried to shift their data protection responsibility onto these subcontractors.
This context has been well understood and the GDPR takes outsourcing into consideration: it also concerns and applies to subcontractors. The Regulation defines data processor as “any natural or legal person who processes personal data on behalf of the controller in the context of a service or provision.”
The CNIL provides a guide to support them (Source) and gives us concrete examples of subcontractors:
- Providers of IT services (hosting, maintenance, etc.),
- Software integrators,
- Computer security companies,
- Digital service companies or formerly Computer Services and Engineering Companies (ITSSs) that have access to the data,
- Marketing or communication agencies that process personal data on behalf of their customers
Finally, all subcontractors must comply with clear obligations in terms of information security, confidentiality and even responsibility.
If you’re a subcontractor, this issue of data protection should be taken into account “by design”, from the very conception of the service or product. Doing so will allow to avoid a lot of potential issues in the future. It is a question of implementing measures that will guarantee optimal data protection.
For example, if a company processes data, having a ROPA (Record Of the Processing Activities) in place is a basic measure necessary for optimal data protection. In specific cases, subcontractors must also appoint a Data Protection Officer DPO, a requirement similar to that of their clients.
To conclude, subcontractors processing personal data on behalf of other companies have a duty to advise them and assist them in complying with the GDPR.
The health sector on the front line
More and more health data provoke envy
The health sector as a whole is closely scrutinized by Data Protection Authorities such as the CNIL. The reason is simple: the industry is the leading producer and user of particularly critical health data. But what do you call health data?

According to the CNIL, health data is “personal data relating to the physical or mental health, past, present or future, of a natural person (including the provision of health care services) that reveal personal information about the state of health of that person. ” Therefore, some measurement data, that would allow for the deduction of information about an individual’s health status, are also included.
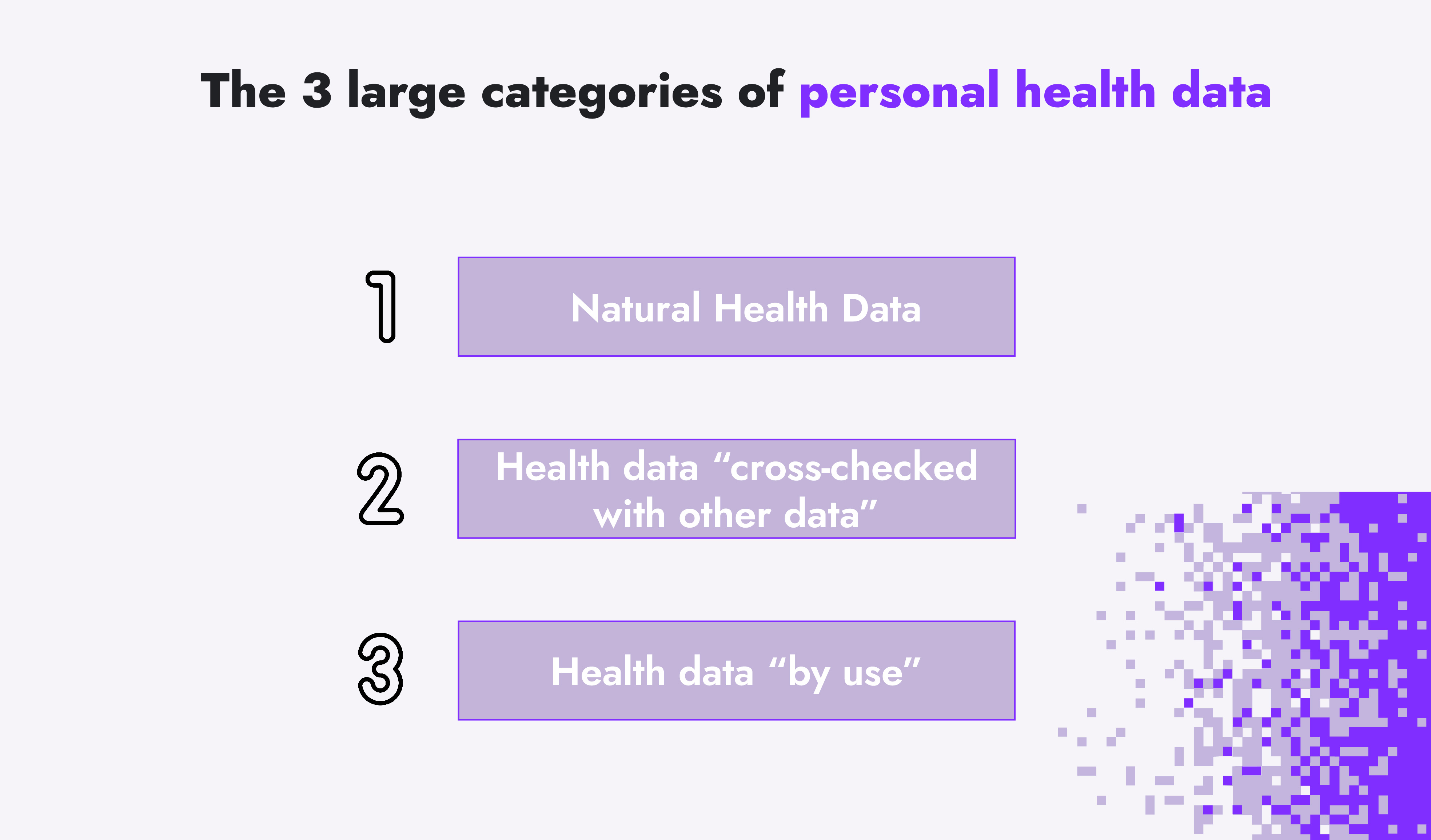
We can then draw 3 large categories of personal health data:
- “Natural” health data: medical history, diseases, care provided, test results, etc.
- Health data “cross-checked with other data”: crossing of tension with effort measurement, crossing of weight with number of steps, etc.
- Health data “by use”: data becoming health data through their medical use
Making an appointment on a platform like Doctolib, consulting a doctor, getting a prescription, going to the pharmacy, etc. Each of these seemingly innocuous gestures leaves a trace. The list is long if one wishes to list all the acts that create health data.
Health data is a key issue today. According to the article Sizing up big data, published in Nature Medecine in January 2020, the total volume has increased tenfold since 2013 and this increase is far from trivial. The whole field of health monitoring is growing rapidly. And it relies essentially on the availability of a large number of health data and its analysis by artificial intelligence.
Legally obtained health data are very valuable. And so is data obtained by unscrupulous methods. This is evidenced by a report by the American cybersecurity company VMware Carbon Black published on June 5, 2019. It shows that, on average, health data (medical records, prescriptions, etc.) are sold three times as much as “classic” personal data (name, first name, telephone number, etc. ). To give an idea, for the researchers of the PrivacyAffairs website (Source), you can find credit card numbers with owner IDs on the dark web for an average EUR 125 to EUR 200 depending on the money available in the account.
The first explanation for this price difference is to be found in the nature of the data concerned. It is easy to object on a credit card, but a medical record contains information that cannot be changed such as a patient’s history of illnesses. Health data is also a gateway to scams and other identity theft to obtain false insurance refunds. Of course, all of these numbers become even more important when it comes to research data, lab intellectual properties and so on, which have been stolen in sophisticated attacks.
Envy exacerbated by the dual context of digital transformation and the health crisis
The value of the stolen data alone does not justify a steady increase in cyber attacks against health sector actors. The current context is particularly conducive to attempts to steal and resell data.
As the FAIR (Factor Analysis of Information Risk) method rightly points out: for a potential attacker, the probability of taking action depends on the value of the asset being targeted (in this case, health data) but also on the level of effort that the attacker will have to make to achieve their goals.
Digital transformation is in full swing and the whole health sector is on the front line because of the covid-19 crisis. In such context, the health sector’s actors are, paradoxically, in a very fragile state of health. A quick overview confirms what we said:
- Hospitals have gone beyond the status of health centres. They are run like businesses and there is increasing talk of hospitals being grouped into hospital centres. Local hospitals seen through an individual prism are becoming less common. And like businesses, both health centres and hospitals rely heavily on subcontracting for certain tasks. Besides, the successful integration of all these organizations requires the use of digital technology: electronic healthcare record (EHR), information stored in the Cloud, and machines connected to a network are used in most services.
- Doctors also use databases, which are seldom well-protected because doctors are neither the most aware or trained against the risks of data breaches.
- Medical research laboratories are still prime targets for IP theft. The attacks on laboratories such as AstraZeneca or Moderna are proof of this.
The bottom line is that none of the companies or organizations in the health sector excel at protecting the health data they create, use and maintain. And it is not the massive spread of remote working caused by the pandemic that will prove otherwise. It further expands the attack surface of companies and organizations.
How to combine health, GDPR compliance and innovation?
Undertaking a paradigm shift: from “weight” to “lever”
Innovation is vital for the health sector. And the Covid-19 crisis is a stark reminder of how having a strong medical industry, and resilient health care structures are prime concerns for countries. These two elements necessarily require in-depth consideration of data protection, which, as we have seen, are the backbone of the war for the health sector. So what is the role of the GDPR in this reflection?
Ms. Dixon, president of the Irish Data Protection Authority, admits in a New York Times article: « the GDPR has not brought about a fundamental change in the way data is collected and used by large companies. »
Being compliant with GDPR is mostly seen by companies as an important effort to make. And dominant idea remains for organizations to do the minimum to avoid being sanctioned. However, with such a starting point, we are as far as ever from the in-depth reflection that needs to be undertaken. It’s the whole paradigm of seeing the GDPR as a barrier that needs to evolve.
One of the ways to go beyond this idea of “ GDPR stranglehold” is perhaps to see the latter as a lever. Why not try to see the GDPR as a lever for innovation, for example?
Being compliant is not an end in itself and some have already understood this. Companies that want to continue sharing or using their customers' data are now looking to keep it anonymous. While there is no consensus today on how to achieve this objective, innovations are emerging in all sectors. In particular, the one we are interested in: the health sector.
The Wall Street Journal reported in a February 2019 that the healthcare sector was at the heart of innovations in this regard. For example, healthcare and pharmaceutical companies are already anonymizing the data they collect from clinical trials before sharing it with researchers and other companies. Large American hospital groups, for example, have decided to set up their own specialized companies. The objective is to collect and sell their anonymized data for research and drug development purposes.
GDPR compliance will need to be supported by public authorities and a cybersecurity strategy
The paradigm shift with respect to GDPR and innovation will never be the sole responsibility of the private sector. This line of thought is still largely underestimated. There is therefore also a need for real awareness and support from the public authorities on these issues. The GDPR must be the starting point, not the finish line.
In France, the issue is already being taken seriously by the competent authorities. The CNIL, in particular, has decided to make health data security one of its priority themes in 2021, along with cybersecurity. In practical terms, this means that it will carry out a minimum of formal control procedures in connection with this issue. This is in fact a continuation of its 2020 strategy. But as we said earlier, controls and sanctions alone are not enough. We also need to be able to support thinking and innovation on these issues. Here, too, the CNIL intends to play a role. The Commission wants to help e-health actors combine innovation and compliance with the GDPR. All this through privileged contacts with its legal and technical teams. Only the 3 winners of a call for projects will be able to benefit from it, but the objective is clear: to implement “privacy by design” i. e., to consider the protection of health data from the development phase of a product or service.
But it must also be highlighted that GDPR compliance cannot be considered without a strong cybersecurity strategy. The two are closely linked.
ANSSI (National Agency for the Security of Information Systems) defines cybersecurity as “the desired state of an information system that enables it to withstand cyberspace events that may compromise availability, integrity or confidentiality the data stored, processed or transmitted and the related services provided or made available by those systems. »
On the one hand, we have the GDPR, which regulates personal data protection. And on the other Cybersecurity, which by its very nature seeks to fulfill a data security objective. Data security is thus one of the pillars of personal data protection.
Cybersecurity and GDPR are closely linked. But how is this relationship reflected in the law ? The Regulation requires “ the implementation of appropriate technical and organizational measures to ensure a level of security appropriate to the digital risk. ” Specifically, such measures may take the form of data encryption or, more broadly, means of ensuring the confidentiality, integrity and availability of data.
Again, let us remember that all this must be supported by the public authorities. In France, ANSSI provides everyone with a “data security kit” (Source). It brings together best practices, solutions and other recommended tools to enhance the security of personal data.
GDPR compliance using a risk-based approach means avoiding sanctions thanks to quantified efforts
The GDPR and its sanctions apply to all sectors, including the health sector
Not being GDPR compliant means that in the event of data theft, investigation of a Data Protection Authority or formal complaint, the data controller concerned may face sanctions. They may be non-financial: call to order, restriction of data processing, suspension of data flow, etc. But these sanctions can also amount to up to €20 million or, in the case of a company, up to 4% of annual global turnover. What is the actual situation regarding the application of these sanctions since the implementation of the GDPR?
If some still doubted it, law enforcement is becoming a priority for DPA. This is evidenced by the total amount of fines, which more than doubled in 1 year according to data from enforcementtracker.com. In fact, in 2020, the total amount of sanctions for GDPR violation amounted to €171 million. While it was €72 million in 2019. However, these figures should be put into perspective: out of more than 280 000 complaints, 613 fines were imposed, 8 of which exceeded €10 million. France, which used to impose the heaviest fines (a record of €50 million imposed on Google in 2019), is now only sixth in 2020 with approximately €3 million in fines imposed. Italy is in the lead with €58. 16 million in sanctions. But these declining figures in France are not synonymous with a drop in vigilance. The record fines against Amazon, €35 million, and Google, €60 million, related to data protection (the cookie policies in these cases), but were imposed under the French data protection law (Law on Information Technology and Freedom) and not under the GDPR.

Finally, we have previously confirmed the attention paid to the protection of health data. It is therefore very logical that the GDPR and its sanctions apply equally to health actors. The figures compiled by C-Risk confirm this. Since the implementation of the GDPR, 52 fines have been imposed on industry players. Enough to be in the top 5 of the most sanctioned sectors, but still far from the top: the media and telecom sector with 123 fines. Moreover, between 2018 and 2020, the minimum amount of a sanction for a health actor was €510 while the maximum sanction was €1.24 million. The hospitals are the most-sanctioned health actor.
How to avoid these sanctions ?
The approach favored by C-Risk is to consider the GDPR from the perspective of risk scenarios (operational and cyber security) to:
- Understand the risks faced by the data controller (company, public body, etc. ) and the financial implications of these risks
- Be able to make informed decisions, with a real return on investment, to address quantified risks and avoid sanctions and other potential financial losses
It is the FAIR method that quantifies the risks faced by a company or organization wishing to comply with the GDPR. This is done in several steps:
- The first thing to do is to map the exposure to “GDPR risk” taking into account two points of view. The point of view of the data subject first. This can be illustrated with the risk of data breach such as PII (Personally Identifiable Information). Then the complementary point of view of the data processing company. Here the risk may be in the form of fines, penalties, or loss of reputation. Simultaneously, a mapping of the most important PII databases must be performed.
- Second, it’s necessary to ensure that the processes in place comply with the GDPR requirements. For example, having a clear policy in place in the event of data breaches. If an incident occurs, the data controller has 72 hours to notify the breach to the supervisory authority. Transparency with regulators and speed of response are keys. Failure to check these two boxes often results in higher penalties. It is also necessary to identify and/or put in place the controls and means available to improve data security. This may be technical solutions (data encryption, etc.) or contractual solutions (identification of third parties responsible for processing, verification of contractual controls, etc.).
- The next steps will be to continue collecting information and then start creating risk scenarios to quantify potential financial losses using the FAIR methodology.
Health data processing versus GDPR: a debate that has only just begun
Health data processing: the digital transformation
We explored some ideas on the relationship between the GDPR and health data processing, as well as potential solutions to help comply with the requirements of the regulation. Finally, more than questioning sanctions or compliance, the GDPR should also lead us to rethink our vision of what’s considered a “good” processing of health data.
Today, it’s hard to deny the need to collect and process health data. The transfer of physical healthcare records to electronic healthcare records is probably the most concrete example. This means, among other things, better coordination of care between different healthcare professionals, greater flexibility and easier access to this information for patients themselves. Health data processing addresses specific needs for transparency, information, as well as efficiency and health safety.
In the same vein, Covid-19 is a clear demonstration of the importance of health data for research. Vaccines were developed in record time (10 months instead of 10 years). There are several reasons for this: virus is not completely unknown, huge investments, new vaccine technologies, etc. But all of this requires researchers to have access to the old SARS CoV-1 data. This requires the collection of volunteer data, the rapid sharing of the results to the supervisory authorities, etc. To sum up: this requires efficient processing of health data.
Are we opening Pandora's box?
The health sector, which is changing and under pressure during crises such as the Covid-19 pandemic, undoubtedly has concrete needs for effective and large-scale data processing. And to meet these needs, the digital giants are eager to offer their solutions.
Google launched its Google Health Studies app in December 2020. The objective? To assist researchers in the collection of a large and representative body of health data. Every Android smartphone owner can now register and provide data requested by researchers. In France, the Health Data Hub was created on November 30, 2019 with the same goal: to facilitate the sharing of health data to promote research. The cloud hosting the data: Microsoft.
More recently, it was the partnership between the Doctolib platform and the French government that made the headlines. Doctolib becoming an official appointment-making platform for Covid-19 vaccination. Physician and patient associations believed that Doctolib’s cloud provider, Amazon Web Services, had access to insufficiently protected health data.
It’s therefore easy to see from all these examples that the processing and storage of health data goes far beyond the scope of the GDPR. It feeds the debate on the principles of data protection and emphasizes major geopolitical issues. First and foremost: national sovereignty. Are we condemned to use GAFAMs to collect and store the precious health data of our fellow citizens? Is the GDPR an effective deterrent against bad corporate practices? Especially when some companies are subject to extraterritorial laws that are inherently opposed to GDPR (the US Cloud Act in particular)?
We do not have clear answers to these questions yet, but this debate is far from over. One thing is certain: Europe is leading the way with a regulation that inspires others (cf. California Consumer Privacy Act). The GDPR is under close scrutiny because the issue of data protection is is a growing issue everywhere.
Does GDPR compliance and cybersecurity concern my company?
The GDPR is first and foremost a requirement for data controllers, in order to guarantee the protection of the data of every European citizen. These requirements apply both to companies and to their subcontractors responsible for data processing. Cybersecurity, on the other hand, is undeniably a major issue and risk for businesses and individuals. The consequences of a cyber security breach are diverse, from the « simple » financial loss to reputation losses etc. GDPR compliance and cybersecurity are issues that concern us all, especially if you or your company are processing sensitive personal data vital to your business.
Why are GDPR compliance and cybersecurity tightly linked?
The GDPR, as its name suggests, focuses on data protection. Its primary objective is to regulate their use. Cybersecurity is all the means by which data protection can be ensured. This is why the two issues are closely linked. We can even observe a virtuous circle: improving one of them has often good rippling effects on the other. That is why the GDPR requires “the implementation of appropriate technical and organizational measures to ensure a level of security appropriate to the digital risk. ”
How is CRQ helping me with the GDPR?
There are a number of ways to improve data protection and GDPR compliance. But the same problem comes up again and again: how to efficiently justify the implementation of a particular tool, project, etc to someone not well versed on these technical subjects? Using FAIR simply means quantifying in financial terms the risks we’re exposed to. Specifically, the risks associated with non GDPR compliance or a lack of data protection. After a risk assessment and a quantification, the solutions put in place and their returns on investments are now justifiable in a language understood by all stakeholders.
Related articles
Read more on cyber risk, ransomware attacks, regulatory compliance and cybersecurity.

.svg)

.png)
