Managing crisis communication after a cyberattack
A cyberattack does not only impact a company's computer systems, it also provokes a crisis situation, which threatens reputation, financial stock, and business continuity. In the event of a crisis due to a cyber incident, confidence of internal and external stakeholders and public perception of the company are at stake.
This is why you need to put in place effective crisis communication strategies, to mitigate the negative consequences of an attack. However, when it comes to crisis management, there is no ready-made solution. Digital security threats are too diverse and complex to be tackled at the same time in one internal memo. You need to build a bespoke crisis plan for your business, your stakeholders, and your operating environment. In order to face and manage the crisis, you need a plan ready to help you manage all types of cyber incidents.

What is crisis communication?
Crisis communication refers to all the means of communication a company can use to address an issue that affects its organization and its reputation. A crisis is a situation where the organization of the company is likely to be thrown off balance, disrupting its processes and operating environment in the process.
Crisis communication mainly aims to limit the negative impact of a crisis on a brand and its products. In the event of a crisis, disaster prevention efforts, crisis responsiveness, and short-term decision-making are required. You can manage communication effectively and bypass potential controversies thanks to successful crisis communication planning.
Crisis communication should also be part of a company’s fundamental communication strategy, as it impacts all communication channels, from internal and external communication, public and press relations, and social media.
Furthermore, crisis communication is an integral part of crisis management, so it also calls for continuous consultation with general management and members of the crisis unit.
There are two commonly recognized components of crisis communication:
- Communication on crisis management, which consists of warning stakeholders and coordinating repair operations by giving effective instructions.
- Communication on how the crisis is dealt with, which helps protect the company's reputation.

Why communicate in the event of a crisis?
Crisis communication is a central part of crisis resolution. Without an appropriate crisis response, employees and other stakeholders are left to interpret the situation in their own way, encouraging the crisis to grow and develop to the point of threatening the organization’s survival. A company going through a crisis due to a cyberattack therefore has a duty to go public with its side of the story and reassure its audiences.
The main objective of crisis communication is to allay concerns and protect the image of the company. Be careful, however, not to communicate for the sake of communicating – your crisis communication must convey your genuine intention to provide durable solutions to current malfunctions.
What is the context for crisis communication after a cyberattack?
The general public is increasingly aware of the risks associated with digital security and cybercrime, and a company that realizes how sensitive its audience is to these issues is more likely to communicate successfully.
Since 2016, the implementation of the General Data Protection Regulation (GDPR) also demands communication in the event of a confirmed cyber risk. To be thorough, articles 33 and 34 of this regulation stipulate that organizations should provide “detailed information to the supervisory authorities within 72 hours of detecting the problem, and as soon as possible to each natural person concerned if there is a high risk of infringement of their rights”. (Source: CNIL, In the event of personal data breach)
This is why the IT department, in collaboration with the communication department, must prepare crisis communication strategies, depending on the type of cyberattacks or system failures involved. In 2022, the most recurring cyber crimes targeting companies are:
- ransomware attacks;
- scams based on identity theft;
- personal data breaches;
- theft of passwords or user names;
- DDoS (Distributed-Denial-Of-Service) attacks, which take online services down.
The trick to surviving a crisis situation is to know how to appropriately time your communication. Sharing information with the public too early can negatively impact customer, shareholder, and stakeholder behavior. Communicating too late, on the other hand, can deal a fatal blow to a company's reputation and financial stock.

Understanding the life cycle of a crisis in order to communicate well
Communicating about a crisis implies controlling the narrative and adapting the message to each stage:
1 / The pre-crisis phase:
Despite an apparent calm, signs of weakness nevertheless begin to arise. The conditions for the onset of the crisis start coming together. Internally, disturbing rumors begin to appear, which should set the communication and IT departments into motion.
2 / The acute crisis phase is when it really begins:
At this stage, the company is at risk of losing control of the situation, and the media and stakeholders are alerted. It requires the activation of the crisis communication team and the implementation of the crisis communication plan that has been prepared upstream.
3 / Then comes the chronic phase:
The crisis has been disturbing the company’s operations with its employees, shareholders, and stakeholders for a while. It is now, more than ever, time for the crisis communication team to reassure these different players by carefully choosing its communication channels and taking protective and restorative measures.
4 / The post-crisis phase sees the company adapt to its new circumstances:
It should learn from the crisis and adjust its structure and procedures. In the event of a cyberattack, for instance, the company could invest in a more robust antivirus protection system.
The post-crisis phase constitutes an exit from the crisis situation: relevant data is archived and the crisis task force is shut down – things are now “back to normal”. However, this cooling down should not be taken for granted. Crisis communication theorists indeed observe that organizations that assume that a crisis is over too soon can quickly return to a pre-crisis phase.
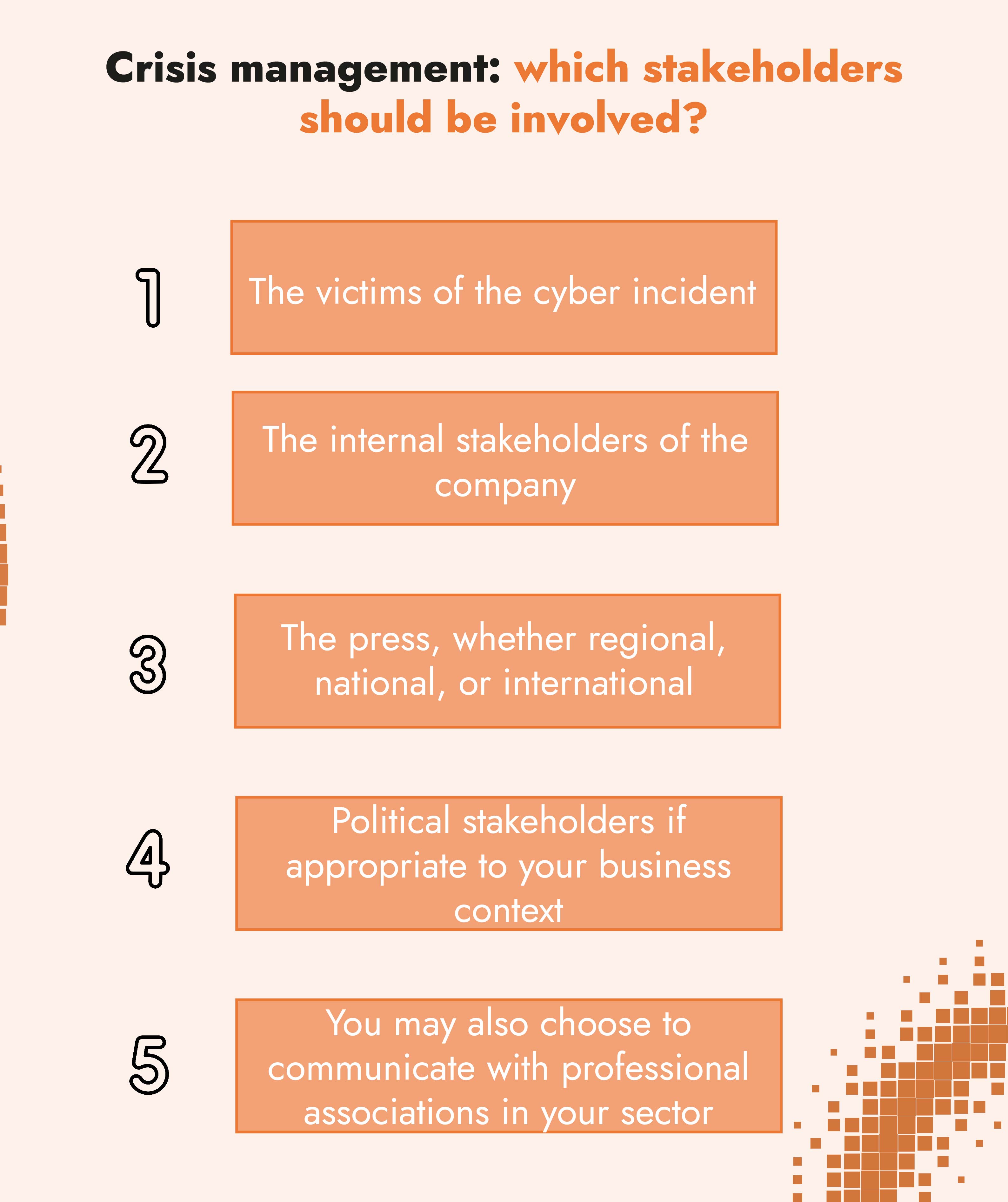
Crisis management: which stakeholders should be involved?
A crisis has an impact on various players who stand out as priority targets in your crisis communication. These stakeholders are, in order of priority, as follows:
1 / The victims of the cyber incident are your “priority target”. These may be customers whose personal data has been stolen or internet users who can no longer access your website.
2 / The internal stakeholders of the company are your “secondary targets”. Informing your employees enables you to influence their own communication with the outside world. Do not bet on confidentiality in this situation – you may have to mop up leaks. On the contrary, reassure staff, anticipate the sorts of requests that they might encounter and give them the appropriate tools to communicate.
This crisis communication target includes unions and staff representatives, executives, various departments, suppliers and wholesalers, prospects, and consultants (accountants, lawyers, and insurance agents). Of course, this audience also includes investors and stock markets.
3 / Next comes the press, whether regional, national, or international. It is up to you to determine whether your press release should primarily target general or specialized media and whether it should target television, radio, or print media first, depending on your activity and the nature of the cyber crisis.
4 / If appropriate to your business context, also consider contacting political stakeholders such as elected officials, the relevant administrative institutions, and the official inspection authorities.
5 / Ultimately, you may also choose to communicate with professional associations in your sector. This move helps maintain your reputation if you are seen to be focused on solving the crisis.
Crisis communication: how to set it up after a cyberattack?
Functional crisis communication depends on how successful the company was in anticipating upstream. This is why crisis communication has to follow a meticulous procedure, detailed in the digital security risk management plan.
A detailed crisis management plan upstream
If it is well constructed, your crisis management plan includes a communication strategy that breaks down into the following major components:
- For what purpose do you communicate during the crisis? Is it to reassure? To detail remedial measures?
- Who are your targets, in order of priority?
- On which topic should you send priority messages: the current system failure? Your action plan? Your preventive measures?
- Who should embody crisis communication: is it the general management? The head of IT? Your lawyer? The communication department?
Also, consider having your operational crisis communication process typed or written down on paper; if a crisis occurs because of a cyberattack, you may no longer be able to access the digital version.
These components are also based on concrete assets:
- List of contacts able to help you in the event of a cyberattack
- Break-down of stakeholders
- List of communication channels and press contacts that might come in handy
- Table that cross-references urgent tasks and appointed people of responsibility
- Diagram of appropriate messages for each cyberattack scenario provided for in your cyber risk analysis
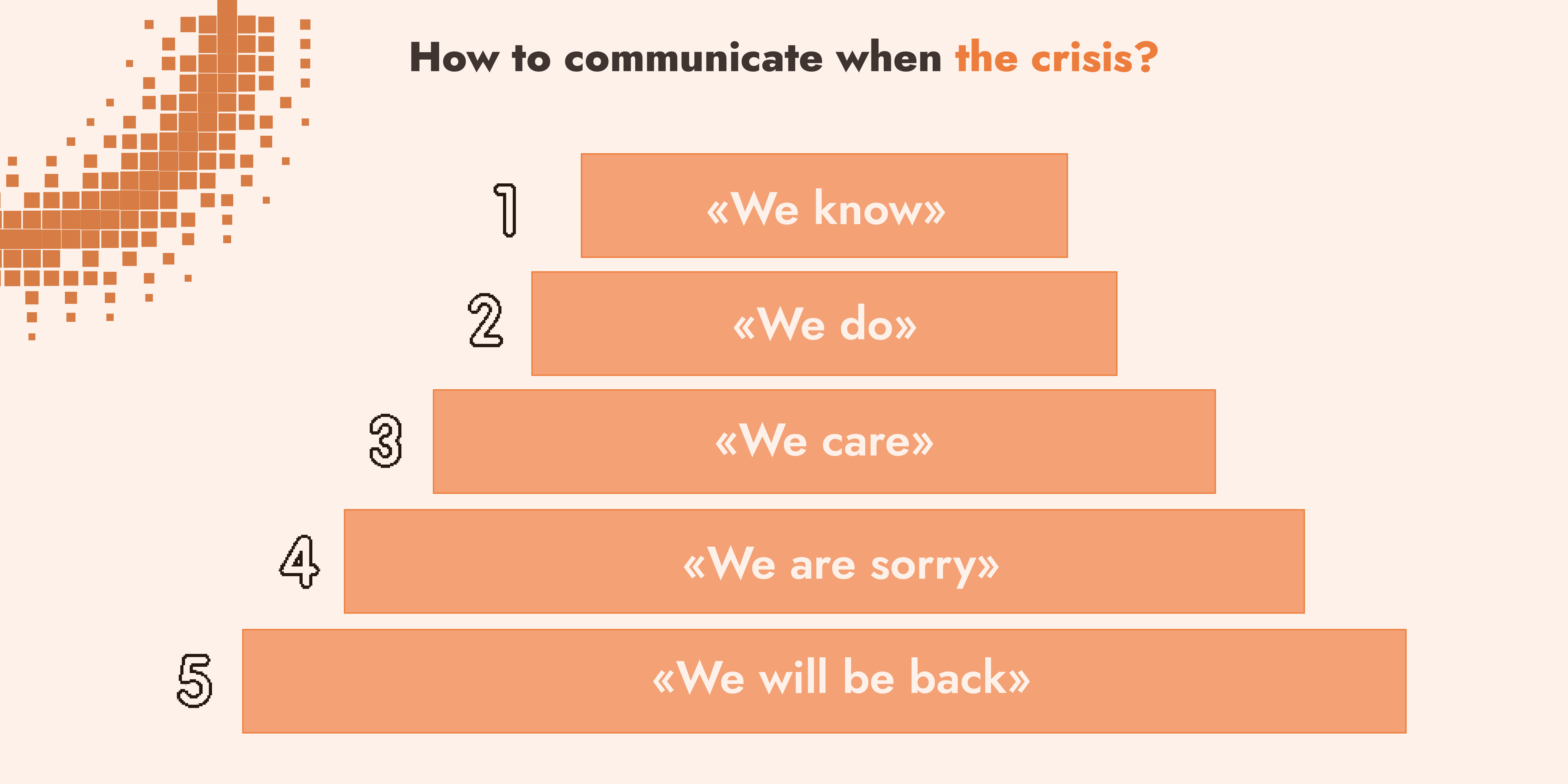
How to communicate when the crisis occurs
In the event of a crisis, your company is vulnerable to major disruptions. To be effective, your crisis communication team needs to show rapid decision-making and must apply the crisis management plan with pragmatism.
Your team needs to adapt to the specific fallouts brought on by a cyberattack, and it is also required to determine who the victims are. By doing all of this, your team members will be able to adjust your communication strategy. In any case, keep a few major crisis communication principles in mind, even if it means straying from the plan:
- Be transparent about the incident and its consequences
- Show your solidarity with the victims and your eagerness to find solutions
- Send clear, short, jargon-free messages
- Speak up and give your interpretation of the problem before outside players do
In addition to these major rules, you should tailor your communication plan to the reality of the cyber incident:
- Analyze the current crisis: does it look like an anticipated scenario? Or is it completely new?
- Should you reevaluate who, among the stakeholders, needs to be involved in the crisis communication process?
- Where are you in the life cycle of the crisis? What media risk does this phase represent?
- What is the most suitable communication channel for your main target, given the state of your information systems? Is it a video, a press release, an email? Should you set up phone trees? Are you, ethically speaking, the most adapted person for the chosen medium?
- How often will you communicate?
- Which messages do you send to your different audiences?

Sending the right messages
The first messages you broadcast to outpace the press must include these few essential elements:
- We know: We know there has been a cyber incident.
- We do: We are working on the following solutions.
- We care: We understand the gravity of the situation and we care about the victims.
- We are sorry: This one is very important! We apologize for this incident.
- We will be back: Finally, we will keep you informed.
Structuring your communication in this way helps you to break it down into factual and emotional messaging, both of which can be beneficial in the right measures. It is up to you to work out which angle best suits your situation and objectives. Whatever happens, never settle for a “no comment” that could be construed as an admission of guilt.
Effective communication with risk-informed cyber strategy
Effective crisis communication must go hand in hand with a robust, data-driven cyber risk management strategy. CISOs and risk teams can leverage data to identify and prioritize top risks, enabling more informed communication across the enterprise and to key stakeholders. By understanding the most significant vulnerabilities, leaders can tailor their messaging to not only address immediate concerns but also demonstrate their commitment to long-term cyber resilience.
C-Risk's CRQ as a Service simplifies this process. We assist in scoping top risk scenarios, providing board-ready reports, and supporting the possible implementation of advanced tools like SAFE One from Safe Security. With real-time assessments and comprehensive dashboards, SAFE One empowers organizations to communicate risk effectively across departments and ensure that everyone— from technical teams to executives— is aligned on the steps needed to mitigate cyber threats and build resilience.
What are the goals of crisis communication?
Crisis communication aims to prevent the company from having its image tarnished, losing consumer confidence, and suffering financial stock losses.
When should you resort to crisis communication?
Cyber crisis communication is akin to a natural disaster, as you have to deal with hard circumstances: pressure from external players, daunting challenges of survival, impossible deadlines, and uncertainty.
What are the three crisis communication approaches?
Companies can opt for acknowledging the failure, which is the most common position in a cyberattack. Secondly, in some instances, they may choose to create a diversion by talking about other issues and putting the blame on outside players. Alternatively, they might decide not to communicate at all, but this is a risky option.
Related articles
Read more on cyber risk, ransomware attacks, regulatory compliance and cybersecurity.

.svg)


