IT DRP : how best to plan your company’s recovery from a cyber crisis?
Today, cybersecurity challenges are so critical that you also need to consider the possibility that your protective measures are not sufficient. For an organization, IT security also anticipates a possible shutdown of an IT infrastructure for any reason - a system failure, malware, or a cyberattack.
An IT Disaster Recovery Plan (DRP) details the procedures and technological resources that your company would need to deploy (risk management) in order to resume its strategic activities in the event of such a disaster. In this article we will look at a DRP and the usual stages of its implementation.

What is a Disaster Recovery Plan?
A Disaster Recovery Plan (DRP) enables companies to resume normal operations after a disaster. In an IT context, this disaster generally involves a cybersecurity breach: the loss, theft, or disappearance of sensitive data; a virus, a cyberattack, or cybercrime.
Definition of the Business Recovery Plan
In an IT context, the DRP aims to achieve several sub-goals which lead to the main goal: safeguarding the sustainability of your company's activities. These sub-goals are:
- anticipating and mitigating the impact of any cyber crisis;
- guaranteeing the protection of sensitive digital data in the event of a disaster;
- ensuring the continuity of the structure's activities, in the face of an IT crisis;
- setting up a backup system to resume critical IT applications.
A DRP is a document that outlines all the processes your company must put in place to maintain or rebuild its IT infrastructure in the aftermath of a cyber crisis. It indicates how and when to defer to the backup system, as detailed in the crisis management plan, and specifies which backup system to activate in order to ensure the security of confidential data.
Furthermore, the Disaster Recovery Plan sets out how long each department can afford to be paralyzed – also known as the Recovery Time Objective (RTO) – and, finally, the maximum acceptable data loss, or Recovery Point Objective (RPO).
Differences between DRP and BCP
The scopes of Business Continuity Plans (BCPs) and DRPs have evolved over time. Originally, the BCP was required to anticipate the impact of a disaster on a company and provide measures to mitigate the negative consequences of crises, while the DRP functioned like the BCP, but only dealt with IT issues.
Over time, the Business Continuity Plan and the Disaster Recovery Plan have both taken on more precise meanings. Each now has a specific role regarding a company's IT system.
What is a BCP in the current climate?
The BCP now consists of a portfolio of procedures and resources that help to safeguard the continuity of the organization's activities should a problem occur. Its objective is, before anything else, to avoid interruption of IT systems and prevent operational disruptions. It must therefore be built in such a way that all of a company's IT structures remain available: networks, servers, and data centres alike.
From a strict IT perspective, a distinction is made between the operational continuity plan – which includes the company as a whole – and the IT Continuity Plan – which specifically targets the procedures and resources to put in place to ensure the continuous operation of information systems.
What does an IT DRP look like today?
A Disaster Recovery Plan focuses on making sure a company's activity can return to an operational status. In IT, this means backing up vital infrastructure. The plan can be activated when there is an obvious shutdown of information systems, and companies can ensure the post-disaster reconstruction of IT infrastructures and the reboot of the most critical applications to company operations.
Its objective is to guarantee a satisfactory resumption of activity as soon as practicable, in order to reduce the financial consequences linked to a cyber crisis. This is why it has to rely on careful risk mapping to provide adequate backup IT systems and ensure data redundancy, which is the practice of saving the same data on different devices (phone, computer, external hard drive, digital drive, or tablet).

The IT Disaster Recovery Plan in CIO terminology
To summarize, Chief Information Officers (CIOs) generally consider that the BCP specifies measures for ensuring the continuity of activity, while the DRP details measures that guarantee the resumption of activity after an IT shutdown. After all, the Disaster Recovery Plan is activated when the infrastructure is unavailable.
In the event of a cyberattack, there are generally two execution scenarios for the DRP:
- Your company was prepared for IT crises, and had a BCP to mitigate the impact of the disaster. In this case, your company can reduce the RTO and RPO to a minimum and apply a “warm restart” of the applications. This is a quick restart of activities on one or more backup servers, all based on pre-disaster data saves.
- Your structure did not have a BCP or the technical means to execute an effective crisis management plan. In this case, a “cold restart” is required, a process which can last several hours or days after the disaster. In this scenario, the recovery is based on the company’s latest backups. However, with the increasing uptake of cloud data storage, this cold procedure is becoming less frequent.
When should you set up your IT recovery?
By definition, the DRP is only activated when the company suffers a genuine shutdown of its IT activities. If you want this IT recovery plan to perform well and enable you to quickly resume your activities, you must think it through well in advance of the actual onset of a cyber crisis. As a general guideline, you should allow an average of three months to design it, although you may need more or less time depending on the size of your structure.
Once the cyberattack, computer failure, or human error has been recorded and damage to your infrastructure begins, the execution of your DRP should help minimize your operational downtime. The longer the recovery, the more the company’s financial results are jeopardized.
Advantages and disadvantages of the DRP
The main mission of the Disaster Recovery Plan is to ensure a rapid restart of your operations. Any service interruption that is too long has an impact on your reputation and, as a consequence, on your financial value. Moreover, if an isolated incident threatens the fulfilment of your regulatory and contractual obligations, your business could incur harmful legal consequences.
Nevertheless, setting up a DRP comes at a cost, although it could be considered an investment that pays for itself when you take into account that it helps avoid harmful consequences in the event of a cyberattack or an IT failure:
- alteration or disappearance of all or part of sensitive data;
- loss of turnover due to the shutdown of IT systems;
- damaged reputation with customers, partners, and investors;
- legal risks.
A DRP relies on a third-party computer network and data backups to ensure satisfactory IT operations. Like a BCP, the advantages of a Disaster Recovery Plan can only be appreciated if good practices are complied with. Using Cyber Risk Quantification (CRQ) methods, you can better understand the risks your organization faces in financial terms. This is a plan that should be thought through and regularly tested using quantitative methods. Its development takes time and a significant budget to be effective.

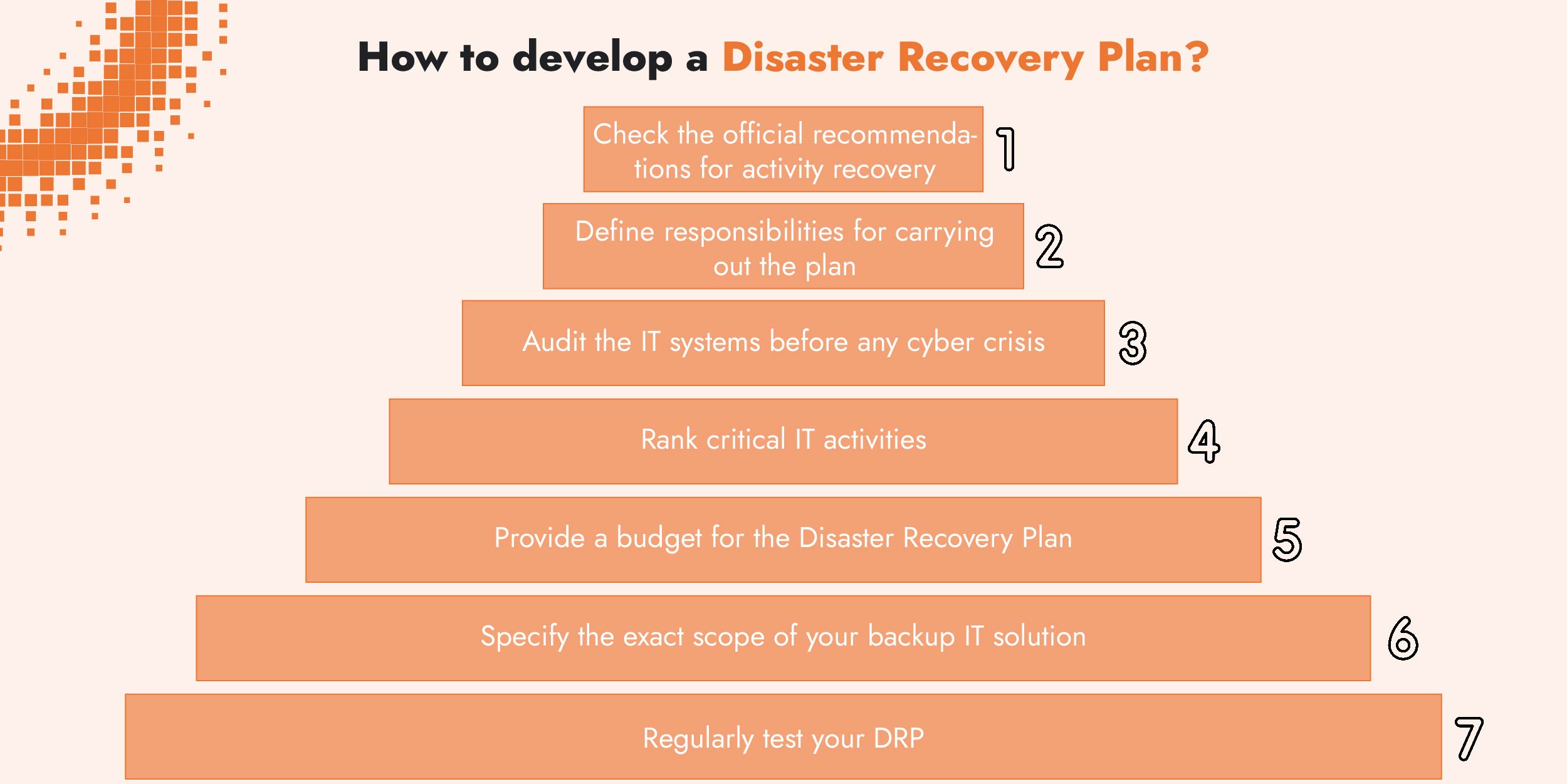
How to develop a DRP
The implementation of an IT Business Recovery Plan can be broken down into several stages. In general terms, it is above all a matter of writing specification notes that determine the critical IT applications for your structure. These applications are the ones which require an emergency “backup” in the event of an IT shutdown.
It is also a question of identifying which backup system you need to set up and which data backup model you opt for. Your DRP must also provide for regularly updated measures.
1 / Check the official recommendations for activity recovery
Depending on your sector of activity, there may be regulations and standards that govern the resumption of activity, including the methods for carrying out your DRP. The ISO 22301 standard thus organizes business continuity management for a certain number of areas.
The banking and finance sector is particularly affected by this type of regulatory obligation. The Financial Conduct Authority (FCA), for example, states that approved companies specializing in portfolio management must have a DRP in place.
2 / Define responsibilities for carrying out the plan
A IT Disaster Recovery Plan will of course harness the skills of your CIO and general management. More broadly, each department will have to participate in its development to determine which IT applications are essential to the proper functioning of the company.
In order to develop the DRP smoothly and coherently, it may also be useful to appoint a person responsible for its overall implementation. This person, generally from the IT department, has the role of assessing which infrastructures need to be backed up as a priority in the event of an IT shutdown, after having consulted with the other departments.

3 / Audit the IT systems before any cyber crisis
To draw up a list of the essential IT tools for an effective recovery of activity, it is important to focus on the following elements:
- needs in terms of network, and in particular internet speed;
- available servers;
- software applications that are used on a daily basis;
- automatic backups, especially their frequency and volume.
4 / Rank critical IT activities
The next step is to organize the applications according to their degree of criticality for the proper functioning of the company. In the day-to-day life of your organization, some activities are less resilient than others to unexpected IT shutdowns.
You must rank these activities and the corresponding IT applications from most critical to least critical in order to define the effective scope of your Disaster Recovery Plan. You should also compare this criticality with the risk probability. This is a standard approach to managing risks and anticipating cybersecurity breaches.
This step also implies defining acceptable RTOs and RPOs for your business. In other words, it is important to detail the maximum downtime that your structure can tolerate before a return to service, as well as the maximum tolerable timeframe during which data is not being recorded. CIOs are well-versed in these issues, as they are directly related to the frequency of data backups.
5 / Provide a budget for the Disaster Recovery Plan
Designing and activating a DRP involves considerable human and financial investment, although, in turn, it does contribute to preventing financial losses. The question of the budget dedicated to this Disaster Recovery Plan is, however, all the more central as it dictates the type of backup solution you should favor in the case of an IT shutdown.
For a reasonable budget, compare any expenses incurred through the execution of the DRP with those inherent to a shutdown of your company’s IT operation (see CRQ).
6 / Specify the exact scope of your backup IT solution
Once you have gathered all of this preliminary data, you still need to define which IT infrastructure will host your backup applications. Many companies plan what they call a “backup site”, which is a second location equipped with the necessary IT infrastructure and a data replication system. This solution is interesting because it works according to a principle of reciprocity: both sites protect each other.
However, this is an expensive endeavor, which is why many organizations prefer to work with a service provider that hosts their remote infrastructure. For this reason, DRP on Cloud and DRaaS (Disaster Recovery As A Service) are some popular options that are gaining ground.
7 / Regularly test your DRP
Designing a Disaster Recovery Plan only makes sense if you take into account the new software acquired by your company along the way as well as corresponding updates. The backup applications and data replication procedures must also be regularly tested to verify their suitability for your continued IT upgrades.
You also need to make sure your Recovery Plan fits to the logistical habits of your human resources. It must be activated in accordance with your overall management plan in the event of a cyber crisis. This requirement can be part of the simulation exercises provided for in your cyber crisis management strategy.
What is the definition of an IT “DRP”?
The Disaster Recovery Plan (DRP) comprises a set of documents detailing the steps for setting up a backup IT infrastructure. This infrastructure’s aim is to safeguard the usual course of business activities in the event of an unexpected shutdown of IT systems. This shutdown could be due to a cyberattack, a computer breach, human negligence, or data loss or theft.
What is DRaaS?
Disaster Recovery as a Service is a cloud backup solution provided by a third party where your data server is replicated on your service provider’s facility via the cloud, thus making it easy for you to recover any data lost during a disaster. It is a simple solution that removes the need to develop a complex and thorough plan. Also, the maintenance costs associated with running a second site become a thing of the past, since you only have to pay for a subscription.
Is it possible to have a DRP without a BCP?
There are sectors for which an interruption of activity, even of one minute, represents a tangible financial loss or danger to data integrity. In these sectors, having a BCP is essential. Companies whose activities have a lower level of criticality and who can afford longer IT downtime can settle for a DRP alone.
Related articles
Read more on cyber risk, ransomware attacks, regulatory compliance and cybersecurity.

.svg)


