The FAIR™ Methodology for Cyber Risks
Business-related cybersecurity challenges are on the rise. Cyberattacks are carried out by criminals with ever more substantial means, and the attacks are increasingly frequent. Cyber risk, which was initially a technological risk, has now transformed into an business risk. Today, it affects all layers of a company, all the way up to the CEO. These relatively new cybersecurity challenges are pushing organizations to take an interest in cyber risk analysis and management methods.
ISO 27005, CIS RAM, COSO Risk Framework, NIST CSF or EBIOS: it is difficult to choose the approach best suited to a given structure. This choice is all the more complex as these are often based on a qualitative risk analysis. This leaves little room for researching reliable probability data on the occurrence of a cyber risk. The FAIR™ (Factor Analysis of Information Risk™) methodology was designed to remedy that problem. Here are some explanations.

The FAIR™ methodology: how to conduct a probabilistic cyber risk analysis
The range of cyber risk analysis methods is rather wide. The FAIR™ analysis method fills two gaps. The NIST cybersecurity framework (CSF), for example, is a very popular approach worldwide. This is also the case for the ISO 27005 method.
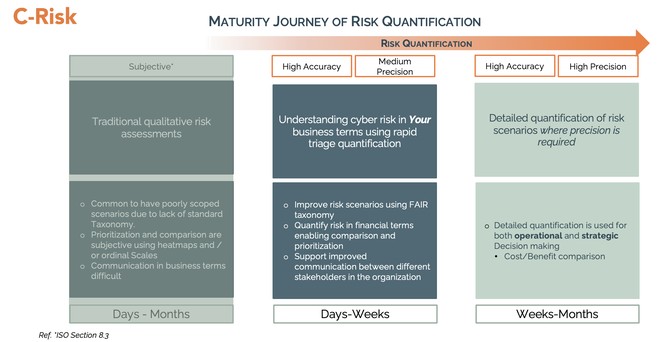
However, those are primarily intended for cybersecurity experts. Besides, they are usually non-prescriptive, which leaves the decision on how to measure risk to the practitioners, who typically base their work on an inherently subjective qualitative approach. (see ISO27005, section 8.3).
The FAIR™ taxonomy complements those qualitative methods by responding to their limitations on how to measure risk.
Why the need for a new cyber risk analysis method?
All risk analysis methods (ISO 27005, NIST CSF, COSO, OCTAVE, among others) that have existed on the market for the last thirty years are qualitative. They are based on IT “expert opinions and experience'' to rank risks with subjective scales. With such scales, the risk is stamped as “low” or “high” and the results of the analyzes most often come as a color-based risk map (heatmap), which goes from green to red.
Of course, these methods provide good practice and necessary cyber hygiene habits. However, since they rely on subjective risk analysis, they do not grant all business functions a common basis on which to work.
In order to choose the right cyber risk management strategy, all of a company's divisions must share the same terminology and the same understanding of risk. Risk analysis is the cornerstone of an organization's cybersecurity strategy: if it remains qualitative, it cannot be entirely useful.
The FAIR™ method offers an objective and quantifiable risk analysis model, which results in a mathematical risk estimate. This then leads to the development of risk scenarios that can be compared to one another. Taking all of this into account, analysts and information security experts have everything they need to design effective cyber risk prevention measures.
Definition and objective of the FAIR™ standard
The FAIR™ standard offers a taxonomy and a methodology for cyber risk analysis in all business functions. Through financially quantified risk scenarios, the FAIR™ framework establishes a link between cybersecurity experts, business managers, and general management. This standard is designed, supported and promoted by the FAIR™ Institute, a professional non-profit organization.
This approach to cyber risk analysis first proposes a taxonomy of the distinct factors that constitute risk, a collection of definitions which clarify certain concepts: risk, threat, danger, asset, control, audit. The FAIR™ method explains the connections between these factors, giving a company food for thought.
The FAIR™ standard also provides a methodology for breaking down risk into distinct measurable factors and for using statistics and probabilities to quantitatively estimate risk. The objectives are to analyze complex risks, to identify key data for quantification and to understand the interdependencies between risk factors.
Then, on the basis of logical, easy-to-explain, repeatable, and defensible scenarios, forecasts of future loss (in GBP, EUR, USD, or other currencies) can be presented to decision makers.
What questions does this methodology address?
Organizations across the globe trust this approach because it enables management to make informed decisions about cybersecurity. The FAIR™ standard thus helps answer the following questions:
- How many times could a disaster occur in a given time interval?
- How much will this disaster cost?
- What are the main cyber risks?
- Which assets are concerned?
- How and how much money should one invest to reduce those risks?
- Between two control solutions, which one would reduce the risk most effectively?
- What risks call for the use of insurance and for what coverage amount?
- Which insurance policy best suits the company’s risks?
By extension, the FAIR™ analysis method gives you the opportunity to have an effective thought process about your cybersecurity budget. It also helps you to choose the risk reduction solution that will yield the best return on investment. This approach also facilitates regulatory compliance.
How does the FAIR™ methodology work?
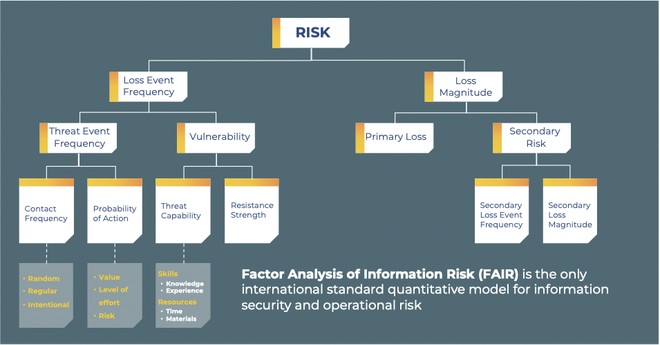
The FAIR™ methodology relies on the taxonomy featured in the diagram below. It is based on a “frequency x magnitude” model which is applicable to all situations and exportable to all businesses.
The results (in GBP, EUR, USD, or other currencies) may be used by different divisions of an organization, by the board of directors, or by general management.
For instance, if a company estimates that a loss event could occur once every 10 years, and that it involves a 20,000,000 USD loss, then the formula would be:
A loss event frequency (LEF) of 1/10 year x 20,000,000 USD loss = 2,000,000 USD/year.
This risk model leaves the decision makers with two ways of reducing loss exposure:
- reducing the LEF – the number of times that loss events occur;
- mitigating the amount of financial losses that would result from such events.
The risk taxonomy on which the FAIR™ standard can be schematized:
Risk according to the FAIR™ method
The FAIR™ philosophy is about conceiving risk as an uncertain event, the probability and consequences of which need to be measured. The FAIR™ standard is probabilistic rather than predictive. Risk is therefore defined as the probability of a loss event relative to an asset. It is “the probable frequency and probable magnitude of a future loss”.
Risk is then broken down into factors that make up the probable frequency and the probable loss:
- threat event frequency;
- threat contact frequency;
- probability of threat agents taking action;
- vulnerability;
- threat capacity;
- loss event frequency (LEF);
- primary loss magnitude;
- secondary loss event frequency;
- secondary loss magnitude;
Factors which affect loss
These factors are the attributes or properties of an asset, of a threat, of an organization, or even the external environment, which will affect the magnitude of the loss for the party involved in a disaster. These can impact primary or secondary loss in any of the four following categories: the asset and the threat (primary loss) and the organizational and external factors (secondary loss).
Loss factors of an asset in the FAIR™ standard
The variables of loss of an asset comprise its value and/or its liabilities (personal information which must be protected under the UK General Data Protection Regulation, for example).
The value and/or liabilities of an asset play a very important part in the nature and magnitude of the loss. The value of an asset can be evaluated according to the following criteria:
- Criticality: an index measuring an organization’s loss of productivity if it can no longer produce its goods or provide its services;
- Cost: the intrinsic value of the asset (cost of replacement or repair);
- Sensitivity: damage that would result from unintentional publication.
The loss factors of threat in the FAIR™ standard
These factors are the action of a threat, its competence, whether it is internal or external, and how the threat agent exploits the breach.
Threat agents can use an asset for the following purposes:
Impact on confidentiality
- Access: unauthorized access to data without any further action;
- Abuse: unauthorized use of the asset such as identity theft, misuse of servers and other IT resources;
- Disclosure: unlawful sharing of sensitive data.
Impact on integrity
- modification of any information or information handling process which results in its inaccuracy, unreliability, or untrustworthiness.
Impact on availability
- the threat agent prevents or denies legitimate and authorized access to an asset (e.g., deletion of information, system disconnection, ransomware, among others).
The effect of these threats depends on the specific properties of the asset. If the “sensitive data” asset is disclosed, for example, this will not necessarily have an effect on productivity. However, the company's responsibility in terms of legal compliance will be affected. This is why the properties of the asset and the type of threat both determine the nature and magnitude of financial loss, be it primary or secondary.

Benefits and limitations of the FAIR Standard
C-Risk uses an approach such as the FAIR™ standard because the quantification of cyber risks in financial terms really optimizes the governance of an information system’s security. Professional organizations or associations such as NIST, the SANS Institute, the OCTAVE method by Carnegie Mellon SEI, ISACA, or even COSO, now reference this approach to supplement their databases in order to quantify the risks.
The frequency/magnitude pair leads to a logical result, while the nominal scales used to categorize risks do not permit risk comparison or future loss estimation.
As indicated before, the FAIR™ methodology is a probabilistic approach, it does not leave room for prediction and no method does. It does not achieve exhaustiveness, either, but rather focuses on the assets most critical to the functioning of an organisation. It accounts for the most probable scenarios rather than pushing you to try to imagine everything that could happen, as some other methods would.
What is the FAIR™ methodology’s definition of risk?
In the FAIR™ standard, risk is defined as the "probable frequency and probable magnitude of future loss".
What are the steps of the FAIR™ methodology?
The FAIR™ methodology has 4 steps: - identifying the components of the scenarios; - evaluating the frequency of loss events; - estimating the magnitude of the future loss; - calculating the risk.
Is it a foolproof methodology?
You will not be able to make a prediction with the FAIR™ methodology, but it will provide you with the best possible estimate of cyber risk-induced potential loss, according to the available data.
Related articles
Read more on cyber risk, ransomware attacks, regulatory compliance and cybersecurity.

.svg)

.png)
.png)