How to set up an effective cyber risk management strategy
Cybersecurity represents a major challenge for companies in 2022, requiring methodical and efficient management strategies. To that end, companies must develop risk management solutions. Although, today, cyber risk is a recurring topic, its definition can often vary depending on the school of thought you follow. From these conceptions arise different theories of what good risk management processes look like. What is the definition of risk in cybersecurity? How can you deal with the unpredictable?

How to define cybersecurity-related risks?
The concept of “risk” is used on a daily basis, yet it does not have one obvious definition, especially when it comes to businesses. However, when you try to come up with a definition, a notion of exposure to danger is usually implied. How can one clear the fog and make sense of it all?
Definition of risk, from the company perspective
The ISO 31000 standard gives the following definition of risk: “the effect of uncertainty on objectives”. The ISO / IEC Guide 73 standard further specifies this point, stating that risk is about the “combination of the probability of an event and of its consequences”.
This official and academic definition therefore implies that the consequences of a risk could be either positive or negative; beneficial or harmful to a company. Risk management therefore becomes threat management, but also opportunity management.
However, company functions rarely use the term ‘risk’ to refer to a positive opportunity. This definition of risk seems at odds with certain business principles. How can one claim that a risk related to employee safety can have positive consequences?
What is cyber risk?
As within other areas of a company, there are several definitions of risk in IT:
ISO: the possibility that a given threat exploits the vulnerabilities of an asset or group of assets and thereby causes harm to the organisation. It is measured by combining the probability of an event occurring with its consequences.
NIST SP800-30: Risk is a function of the probability that a given threat source will exert a particular potential vulnerability and the impact of that adverse event on the organisation.
Cyber risks of this nature can result from cyberattacks, that is to say from attacks carried out for malicious purposes on your information systems. As we laid out in our article on cyberattacks, these attacks can be split into 4 categories: cybercrime, image damage, espionage, and sabotage. However, in a large proportion of incidents, cyber risk originates from human error or technical failure. These two major families of risks affect businesses of all sizes.
At C-Risk, in order to reduce risk, we use the Factor Analysis of Information Risk (FAIR™) standard definition, which describes cyber risk as the probable frequency and extent of a future financial loss resulting from a cyber incident. A cyber disaster is any event that impacts the confidentiality, integrity, or even the availability of the information system or computer data (Confidentiality, Integrity, and Availability: the CIA triad).
What is risk management?
Risk management essentially depends on how you define risk. If a risk can have positive consequences, as suggested by ISO 31000, then risk management may also involve managing “good surprises”.
Yet, this definition does not translate particularly well to cybersecurity. In this area, risk management is firstly about identifying risks and understanding cyber threats, and then about mitigating risks to maintain them at a level deemed acceptable by your company.
Cross definitions of risk management
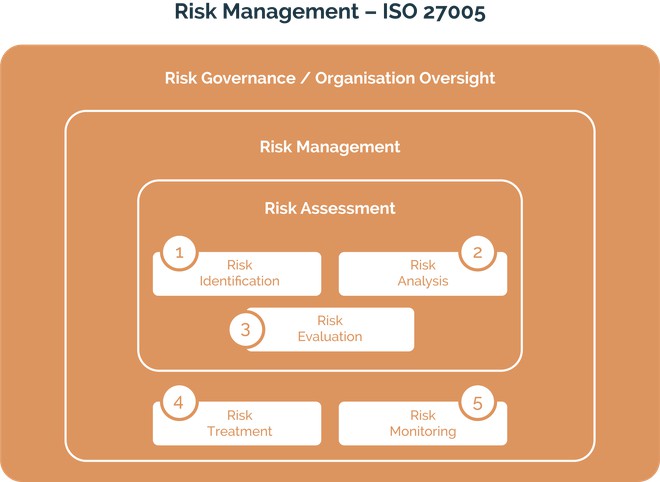
According to ISO 27005 and 31000, risk management is the process by which a company deals with potential risks in a “methodical” way. The whole process covers both the identification of significant risks and the implementation of adapted responses – adapted treatments in particular. Yet, contrary to common belief, dealing with risk does not equate to seeking to reduce or eliminate all types of risk.
This is why the new version of ISO 31000 says that risk management must allow “realisation and protection of value”. This definition aligns with the vision of quantitative cyber risks management that we develop at C-Risk. Our vision consists of identifying and then dealing with cyber risks based on the potential financial losses they represent. Quantitative risk analysis allows for good risk management.
Risk management: a method with benefits on many levels
As shown with the above definitions, risk management is primarily a matter of applying a specific method. It is indeed a “continuous improvement process”, to quote the reference framework for risk management, published by the Federation of European Risk Management Associations (FERMA).
Risk management regroups several objectives, including:
- providing a method that regulates all future projects to ensure more security;
- improving the use, allocation, and preservation of company capital;
- facilitating the decision-making process by prioritising threats;
- protecting the image of the structure, and in doing so, its value.
The different stages of risk management
Risk management is a method that can be broken down into 6 main stages:
1/ risk assessment, which covers both risk analysis and risk evaluation;
2/ report on risk assessment;
3/ decision-making;
4/ implementation of risk management solutions;
5/ internal and external communication on identified risks;
6/ long term monitoring of risk management strategies.
1. Assessing the risk
Risk assessment refers to the process that includes the analysis and evaluation of risk, according to ISO / IEC 73. Its first step, analysis, itself covers four sub-steps: identification, description, estimation, and evaluation of risks.
1.1 Identifying the risk
Risk identification serves to determine the threats your company faces by methodically scanning its environment and its strategic and operational objectives. This scan should enable you to isolate your structure’s significant activities, and is also used to pinpoint instabilities that may present a risk.
These “significant activities” may refer to:
- Strategic objectives, as described by your board of directors. These can be threatened by many cyber risks, related to reputation, identity theft, data theft and espionage, or shutdown of IT activities.
- Day-to-day operational activities;
- Data protection;
- Financial management;
- Compliance regarding data protection, as required by the European GDPR (general data protection regulation), for instance.
1.2 Describing the risk
During this stage, you will need to structure the presentation of risks in order to better communicate them internally. To do this, you may want to create a table of identified risks, specifying:
- their consequences, especially financial;
- the probability that the risks occur. This data needs to be cross-referenced with the consequences to establish a ranking of risks;
- the affected stakeholders;
- the tolerance of your company vis-à-vis those specific risks;
- existing protocols to mitigate the threats;
- actions for improvement on existing measures;
- the designated people in charge of working on each risk.
1.3 Estimating the risk
Finally, estimating the risk is a delicate step for which the methods diverge. You can estimate the risk qualitatively, i.e., by naming the threat according to a classification designed for this analysis: “strong”, “medium”, “weak”, for example. The risk probability can also be assessed by name: “high”, “average”, “low”.
This very common method is used by the National Institute of Standards and Technology (NIST) in its Guide for Conducting Risk Assessments, as well as in ISO 27005. The results from the risk analysis are then compiled into a matrix – every company or even every analysis has its own matrix – and ranked following a colour code: red for the risks deemed to be the most severe, orange for average, and green for the least severe. The limits of this type of approach, which does not stipulate how to estimate the risks, are unfortunately numerous and well-documented. Section 8.3 ISO 27005 thus warns that this qualitative approach suffers from the subjectivity of the scales. Many studies, such as the one conducted by Andrew and Michael J. Mauboussin, demonstrate the limits of nominal and ordinal scales.
At C-Risk, however, we favour more pragmatic and prescriptive quantitative risk estimation methods, which do not allow for any subjective interpretation. This is why we use the FAIR™ method: “Factor Analysis of Information Risk”.
This method breaks down risk factors into quantifiable variables, which make it possible to quantitatively estimate the acceptable and unacceptable financial losses for your company. The FAIR™ risk model is the only quantitative method for measuring IT risks. It is the 2005 OpenFAIR standard of the Open Group consortium or TOGAF™.
For more information on risk analysis in cybersecurity, we invite you to read our dedicated article.
1.4 Evaluating the risk
Once risk analysis is done, you need to compare the risks resulting from the estimate, according to chosen criteria. In the case of the FAIR™ method, this comparison is based on quantitative criteria related to costs. Some companies may prefer other criteria, such as regulatory compliance or stakeholders’ concern.
Risk evaluation should help you to determine the importance of all the risks, as well as how tolerant of them the company can be. It then leads to a decision-making stage. This ability to tolerate (or not) a risk is what determines which ones to treat as a priority.
2. Dealing with cyber threats
This is a specific step in risk management, all about taking action. It is no longer a question of measuring, but of implementing measures to mitigate or eliminate threats. These measures can actually fall into 4 categories, referred to as the 4 “T”s:
- Tolerate; accepting the risk
- Treat; taking action to reduce the number of disasters or the extent of their impact
- Terminate; removing the processes or assets that cause this risk
- Transfer; compensating potential financial losses, for example through a cyber insurance policy.
During this phase of implementation of preventive measures, you need to aim to re-establish the proper functioning of your structure and for compliance with the appropriate regulations. When dealing with cyber risks, it is necessary to take an interest in regulations on the protection of privacy and personal data, such as GDPR, for example, but also foreign regulations concerning subsidiaries, particularly in the United States and China.
The choice of one risk treatment measure over another depends on several factors:
- it must eliminate or substantially mitigate a risk;
- the cost of installing preventive measures must not exceed the financial risks your organisation faces.
3. Communicate on your risk management strategies
Your company should at the same time develop both internal and external communication on its risk management processes.
Internal risk communication has several goals:
- briefing general management on the main threats to the structure, and their financial and strategic implications;
- ensuring all employees are aware of the main risks. This a particularly necessary approach in cybersecurity because most computer security breaches in 2021 still resulted from human vulnerabilities, according to Stanford researchers;
- preparing for crisis management;
- specifying the levels of responsibility of each company division in risk management;
- facilitating risk monitoring and information feedback.
Risk communication is also an obligation towards stakeholders. It is about demonstrating your company’s performance in terms of prevention, which necessarily implies choosing the right method. Shareholders and investors need to know that their interests are safe and that your business will continue to generate value.
4. Risk monitoring
Risk monitoring ensures the relevance of the risk management approach you chose in terms of:
- compliance with legislation, which often changes in this area;
- threat control;
- capacity to evolve with the business environment;
- enforcement of preventive measures;
- efficiency of the procedures.
How to prevent cyber risks
The treatment and prevention of cyber risks obviously take different forms depending on the structure concerned. A good quantitative analysis should let you identify the factors that contribute to the frequency or significance of the impact, in order to determine which control mechanisms are the most effective. This is why, ahead of a disaster, you need to focus your action on what is called preventative controls (avoidance, deterrence, and resistance) in order to reduce the probability of a disaster occurring. Downstream, to limit the post-disaster consequences, response controls (detection, response, and recovery) need to be implemented.
During this stage, you then need to draw up a business continuity plan in the event of a cyberattack, but also a disaster recovery plan:
- The BCP, or business continuity plan, enables your company to maintain minimum operations in the event of a crisis. This plan helps protect sensitive and confidential data, despite a hack of your information systems. It also provides for the use of a back-up computer system in the event of a complete system failure.
- The DRP, or disaster recovery plan, helps determine how to make your IT system operational again. An IT DRP also includes measures to mitigate the impact of possible security breaches. In addition, it details the maximum IT interruption time, and the maximum data loss your company can recover from – this is the Recovery Point Objective.
Finally, note that the pervasiveness of cyber risks in recent years may entice companies to try certain beneficial approaches:
- making boards of directors aware of cybersecurity issues, ensuring that they always appear on the agenda at meetings;
- considering cyber risk as a transversal threat, which of course concerns the IT systems department (CIO), but also potential suppliers, subsidiaries, the supply chain, and partners;
- develop dialogue between the IT team, the board of directors, and general management.

What is a risk management procedure?
Risk management, when applied to businesses, refers to a procedure aimed at identifying, preventing, and dealing with risks likely to come up in the course of a company’s day-to-day operations.
What is the difference between risk management and risk analysis?
Risk management is a broader process than risk analysis, which is only one stage of the former.
What are the stages of risk management?
Because of the different theories, the stages of risk management vary, but we generally find: risk identification, risk analysis, risk evaluation, the development of a preventive action plan, and a final phase dedicated to monitoring progress
Related articles
Read more on cyber risk, ransomware attacks, regulatory compliance and cybersecurity.

.svg)

.png)
