Cyber Insurance: A Strategic Guide for CISOs and Risk Leaders
Cyber insurance transfers financial risk. It does not prevent incidents or reduce breach probability. It shifts a portion of the financial impact of a loss event from your balance sheet to an insurer’s. This article covers how cyber insurance works as a risk transfer strategy, what is changing in the market, and how cyber risk quantification (CRQ) enables more effective coverage decisions.
- Cyber insurance shifts financial impact from your balance sheet to an insurer when a major incident occurs.
- Today’s cyber landscape is changing the structure and limits of cyber insurance policies.
- Sublimits and retentions determine what your policy pays out per loss event up to the aggregate amount.
- Quantified risk data gives CISOs and executives a stronger position when deciding how much risk to retain and how much to transfer.
Cyber Insurance in the Current Risk Landscape
Market Conditions Shaping Coverage Decisions
Ransomware remains the primary driver of cyber insurance claims, and the threat is not slowing down. The Ransomware-as-a-Service model has expanded the attacker pool, AI-generated phishing has improved initial access rates, and double and triple extortion tactics have increased the financial pressure on victims. When attacks succeed, losses regularly exceed $1 million in incident response, business interruption, and recovery costs combined.
For organizations buying or renewing cyber insurance, these conditions create a challenging dynamic. Underwriters are requiring more evidence of security maturity before offering terms. Application questionnaires have become more technical, and carriers increasingly verify control implementations through external scans and supplementary documentation. At the same time, exclusion language continues to expand, particularly around systemic events, infrastructure outages, and state-backed operations. The result is that the gap between what an organization expects its policy to cover and what it will actually pay out in a loss event requires careful scrutiny.
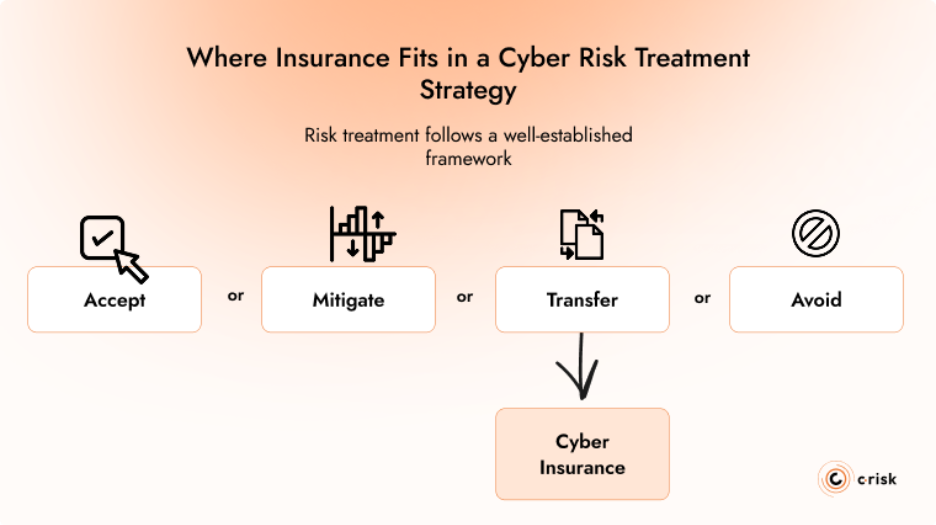
Where Insurance Fits in a Cyber Risk Treatment Strategy
Risk treatment follows a well-established framework: you can accept a risk, mitigate it, transfer it, or avoid it. Cyber insurance is the transfer mechanism. It belongs in the same decision-making process as controls investment, architecture choices, and incident response planning.
Insurance does not reduce the frequency of attacks or the probability of a breach. It provides financial recovery capacity for loss events that exceed what the organization is prepared to absorb. This is why underwriters increasingly evaluate the maturity of an insured's security program before offering terms. They are not just assessing what could go wrong; they are assessing the likelihood that it will, and whether the organization can contain the damage when it does.
Why the CISO Is Central to the Insurance Conversation
CISOs have operational visibility into the controls environment, the threat landscape relevant to the organization, and the residual risk that remains after mitigation. That understanding of loss likelihood and potential impact is exactly what underwriters are trying to assess through questionnaires and external scans. A CISO who can articulate that picture clearly, backed by quantified data, is better positioned to influence coverage terms, negotiate on exclusions, and ensure the policy reflects the organization's actual risk profile rather than a generic industry benchmark.
What Cyber Insurance Covers (and What It Doesn't)
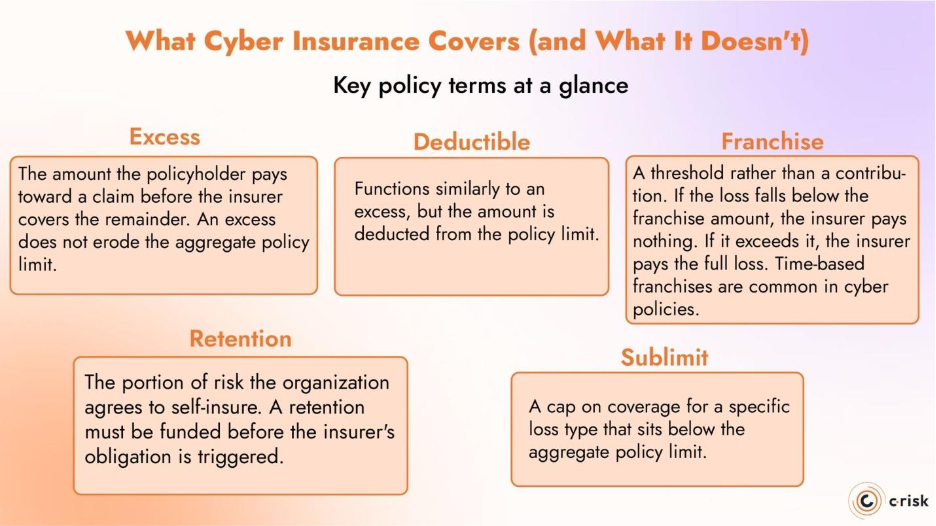
Coverage Structure, Sublimits, and Excesses
A cyber insurance policy's total coverage tells you little about the protection it provides in a loss event. What matters is how coverage is allocated across loss types, how sublimits constrain payouts, and how deductibles or retentions determine what you absorb before the policy responds.
Most policies distinguish between first-party coverage (your direct costs: incident response, business interruption, data recovery, extortion) and third-party coverage (claims made against you: regulatory defense, data breach liability, network security liability). A single incident can trigger losses across both categories simultaneously. How the policy allocates coverage between them, where sublimits apply to specific loss types, and what retention level you are expected to absorb before the insurer pays all determine the actual financial protection the policy delivers. These are the details that matter at renewal, and they require a clear view of your loss exposure to negotiate effectively.
Key policy terms at a glance
Excess: The amount the policyholder pays toward a claim before the insurer covers the remainder. Unlike a deductible, an excess does not erode the aggregate policy limit.
Deductible: Functions similarly to an excess, but the amount is deducted from the policy limit. On a $10 million policy with a $500,000 deductible, the maximum insurer payout is $9.5 million.
Franchise: A threshold rather than a contribution. If the loss falls below the franchise amount, the insurer pays nothing. If it exceeds it, the insurer pays the full loss. Time-based franchises (e.g., 24-hour waiting periods on business interruption) are common in cyber policies.
Retention: The portion of risk the organization agrees to self-insure. A retention must be funded before the insurer's obligation is triggered.
Sublimit: A cap on coverage for a specific loss type (e.g., ransomware, regulatory fines) that sits below the aggregate policy limit.
How the Evolving Threat Landscape Shapes Policy Terms
As the cyber threat landscape shifts, so do the policies designed to cover it. Insurers adjust their underwriting criteria, exclusion language, and sublimit structures in response to emerging attack patterns and loss trends. Understanding how these changes affect your coverage is essential to ensuring your policy aligns with your organization's risk appetite and broader cyber strategy. Three areas are evolving particularly fast:
- Ransomware remains the primary driver of claims severity, and many policies now apply specific sublimits to extortion-related payments
- War and state-backed attack exclusions have expanded significantly since Lloyd's of London began requiring them in standalone cyber policies from March 2023
- Systemic events, such as recent global endpoint failures, are testing the boundaries of what cyber insurance was designed to cover. Some insurers have introduced triggers for non-malicious system failures, but terms and sublimits vary widely
Each time a renewal or new placement is on the table, policy language should be reviewed against your specific risk scenarios. A clear, quantified understanding of your own risk profile is what enables evidence-based decisions about where coverage is adequate and where it needs adjustment.
The Economic Case: Quantifying Retention vs. Transfer
Using CRQ to Determine Optimal Coverage Levels
The decision about how much insurance to buy is fundamentally a question about loss exposure. Without a quantified view of that exposure, organizations default to buying what they bought last year, matching a peer benchmark, or selecting a round-number policy limit. None of these approaches is defensible.
Cyber risk quantification using the FAIR (Factor Analysis of Information Risk) methodology provides the analytical basis for a rational coverage decision. FAIR models specific loss scenarios in financial terms, producing probability-weighted estimates of potential loss magnitude. When you know, for example, that a ransomware event affecting your ERP systems carries a probable maximum loss of $12 million at the 95th percentile, you can make an informed decision about where to set the policy limit, what retention level to accept, and whether the premium represents a reasonable cost of transfer relative to the exposure.
The FAIR-MAM (Materiality Assessment Model) extension adds further precision. It breaks loss magnitude into ten primary modules, including business interruption, response costs, regulatory fines, and reputational harm, that align directly with how insurers categorize claims. This alignment is practical: it means the output of your risk analysis maps to the structure of your policy, making it possible to identify gaps between your modeled exposure and your actual coverage at a granular level.
Supporting Procurement and Leadership with Quantified Data
Insurance decisions involve procurement, legal, the CFO, and the board from a governance perspective. The CISO's contribution is providing the risk data that informs those decisions. Without quantified inputs on loss scenarios and their financial impact, the conversation defaults to benchmarks, broker recommendations, or last year's policy renewed as-is. CRQ translates the CISO's operational understanding of risk into modeled loss scenarios by type, frequency, and probable financial impact, giving each stakeholder the data they need to evaluate terms, compare retention against transfer costs, and align the policy with the organization's risk appetite.
Getting More Value from Your Cyber Insurance Policy
Strengthening Your Position in the Underwriting Process
Underwriters assess your risk profile through application questionnaires, external scans, and supplementary documentation. Carriers often require evidence of specific controls, including:
- MFA across privileged and remote access
- EDR coverage
- Network segmentation
- Offline backups
- Tested incident response plans
With a quantified approach, CISOs can bridge the gap between internal risk reporting and what the underwriting application asks for. Internal reporting may focus on maturity scores and compliance status, while underwriters want to know about specific configurations and operational readiness.
Presenting quantified risk data during underwriting and renewal bridges that gap. When you can demonstrate that you have modeled your top loss scenarios and aligned controls to the exposures that drive the most risk, you provide evidence that goes beyond checkbox compliance and puts you in a stronger position to negotiate on sublimits, retention levels, or coverage extensions.
Cyber Insurance Claims Readiness
The value of cyber insurance depends on whether it transfers risk when a loss event occurs. Many policies require notification to the insurer within 24 to 72 hours, and may mandate the use of pre-approved forensic and legal vendors. Failing to meet these conditions can result in a reduced or denied claim regardless of whether the incident falls within scope.
Claims readiness should be part of your business continuity planning, just as it is for regulatory disclosure. That means aligning incident response procedures with policy requirements and ensuring the organization can act within the timelines the policy demands.
Aligning Insurance with a Data-Driven Cyber Risk Strategy
Cyber insurance is one component of a broader risk treatment strategy. Its value depends on how well it is integrated with the rest of your cyber risk management program. Purchased in isolation, it is an expense. Aligned with quantified risk data, it becomes a financial tool that extends the effectiveness of your security investments.
C-Risk works with CISOs and risk leaders to build this alignment. Using the FAIR methodology, we quantify loss exposure across the scenarios that matter most to your organization, map those scenarios to policy coverage and exclusions, and identify where your current policy may be over- or under-covering your actual risk.
C-Risk supports security and risk leaders in:
- Quantifying top cyber risk scenarios using FAIR to establish defensible coverage requirements
- Aligning FAIR loss categories with insurance policy structures to identify coverage gaps
- Preparing data-driven inputs for underwriting conversations and renewal negotiations
- Integrating insurance decisions into broader risk treatment and reporting frameworks
If you are approaching a renewal, evaluating your current coverage, or building a risk transfer strategy for the first time, a quantified view of your exposure is the starting point.
