Cybersecurity governance, risk & compliance: Turning cyber risk into a strategic advantage
In today’s hyperconnected economy, cybersecurity governance, risk, and compliance (GRC) have become essential pillars of enterprise resilience. This article explores how boards and executives can transform cyber risk into a strategic advantage that links governance frameworks, regulatory expectations, and data-driven decision-making to build stronger, more resilient organizations capable of thriving amid uncertainty.
- Cyber incidents now trigger billion-dollar losses and global disruption
Events like the CrowdStrike outage can escalate into systemic crises. Organizations must treat cyber resilience as essential to business continuity.
- Boards are legally accountable for cyber security
New rules from the SEC and new regulations such as DORA, and NIS2 impose clear expectations, and in some cases, personal liability, on board members for cyber oversight failures.
- Regulatory demands call for board-level cyber risk oversight
Boards must demonstrate informed, risk-based decision-making, ensure appropriate resourcing, and oversee cybersecurity as a core strategic priority.
- Effective cyber governance is risk-based and data-driven
Cybersecurity, enterprise risk management, and business objectives need to be aligned. This requires clear roles, shared metrics, integrated decision-making, and methodologies like FAIR to quantify cyber risk in business terms.
Why cyber governance is a board-level concern
As organizations digitize core operations, cyber governance is at the forefront. Boards must recognize that digital dependency introduces systemic risks capable of disrupting business continuity, eroding stakeholder trust, and triggering significant financial losses. The integrity of data, technology, and operations now directly affects corporate reputation, investor confidence, and long-term enterprise value.
Board oversight of cyber risk is a fiduciary responsibility. Directors are expected to ensure that management embeds cybersecurity within enterprise risk management frameworks and that the organization’s risk posture reflects its strategic objectives. Failure to do so can result in financial or reputational damage, in addition to legal and regulatory fines.
Cyber Oversight Is the New Governance Imperative
In a 2023 PwC report, Overseeing cyber risk: the board’s role, 49% of directors identified cybersecurity as a significant oversight challenge, underscoring the growing complexity of managing digital risk. Boards must bridge the knowledge gap between technical operations and strategic decision-making, ensuring that cybersecurity goes beyond compliance and is treated as a business enabler. By adopting a data-driven, risk-based approach, board members can make informed decisions that balance innovation, risk appetite, and resilience.

How the 2024 CrowdStrike Incident Exposed GRC Gaps
In July 2024, a flawed software update from cybersecurity provider CrowdStrike triggered a global IT outage. Delta Air Lines was among the hardest hit. They canceled over 7,000 flights and incurring more than $500 million in losses. While the root cause was technical, the fallout revealed deeper governance failures: overreliance on a single vendor, outdated infrastructure, and inadequate crisis response planning.
The incident sent more than eight million computers into a “reboot death spiral,” disrupting critical sectors from air travel to healthcare. With total expected damages exceeding $10 billion, the event illustrated how non-malicious cyber incidents can escalate into systemic crises. When Delta sued CrowdStrike to recover losses, the dispute highlighted an uncomfortable truth—resilience failures can stem from governance gaps as much as from technical faults.
Delta sued Crowdstrike in 2024 to claw back some of their losses, saying the faulty software deployment caused “catastrophic” damage to the company. However, Crowdstrike pushed back on the claim, stating that Delta’s own response and IT infrastructure was at fault for their inability to resume normal operations.
Where Do We Go from Here?
This incident brings into sharp focus the growing reality: cyber risk is business risk, capable of inflicting operational damages and financial losses at scale. To meet this moment, business leadership must elevate cybersecurity governance, risk and compliance from a technical function to a strategic, priority anchored in boardroom cybersecurity oversight.
What is cybersecurity governance?
Cybersecurity governance defines how decisions are made, who is accountable, and how cyber risk is managed across the enterprise.
The US cyber defense agency, CISA, has defined cybersecurity governance as:
a comprehensive cybersecurity strategy that integrates with organizational operations and prevents the interruption of activities due to cyber threats or attacks.
Features of cybersecurity governance include: Graphic here
- Accountability frameworks
- Decision-making hierarchies
- Defined risks related to business
- Mitigation plans and strategies
- Oversight processes and procedures
For cybersecurity governance to be effective, it requires clear accountability, risk-based decision-making, and integration with core business operations.
Risk-based decision-making is a multi-modal, data-driven process comprising analysis, planning, monitoring, and review, considering the potential impact of risk on objectives. The data-driven process is key to a defensible governance.
Cyber Risk oversight: Expanding board responsibilities and stakeholder expectations
While executives and board members have traditionally borne ultimate responsibility for enterprise risk, including cybersecurity, today’s environment demands far more than nominal oversight. High-impact incidents like the CrowdStrike outage have crystallized the need for active, informed, and documented governance of cyber risks at the board level.
Cyber expertise of board members
In 2023, the US Securities and Exchange Commission (SEC) considered a rule that would have required public companies to disclose whether any members of their boards possessed cybersecurity expertise. While the rule wasn’t adopted, the agency has emphasized the importance of transparent reporting on how companies oversee and manage cybersecurity risks.
While the SEC’s final rules still do not mandate disclosure of individual board members' cybersecurity expertise, they do require companies to:
- Describe Board Oversight: Companies must detail the board of directors' oversight of cyber risks, including any committees responsible for such oversight.
- Detail Management's Role: Companies are required to describe management's role and expertise in assessing and managing material risks from cybersecurity threats.
These disclosures aim to provide investors with a clearer understanding of how companies manage cybersecurity risks without imposing prescriptive requirements on board composition.
Liability and accountability of board members for cyber risk
In the European Union, regulatory expectations for board-level oversight of cybersecurity have significantly intensified. The Digital Operational Resilience Act (DORA) formalizes this shift by placing explicit accountability on executive leadership. Notably, under DORA, board members of financial entities may be held personally liable, including facing criminal penalties, for severe failures in digital risk governance. This underscores a growing regulatory trend: cybersecurity is a core boardroom issue with legal, financial, and reputational consequences.
Business leadership compensation tied to cybersecurity performance
Historically, executive compensation packages have rarely reflected cybersecurity performance. This is beginning to change. After two high-profile state-sponsored cyberattacks, the Chinese-backed Storm-0558 breach and the Russian Midnight Blizzard intrusion, Microsoft decided to tie senior leadership’s compensation directly to cybersecurity outcomes.
Tying financial incentives to cyber resilience demonstrates to stakeholders that governance is from the top, aligning leadership priorities with long-term security and trust.
Foundations of effective cyber governance, risk and compliance
Compliance is no longer enough. Today’s threat landscape demands cybersecurity governance that is proactive, strategic, and integrated with business objectives. It’s an issue that is being addressed by regulators, standards bodies, industry leaders, boards of directors and cyber risk experts.
In early 2024, NIST released a updated cybersecurity framework (CSF), NIST CSF 2.0, which placed the new Govern function at the center of the other five functions: Identify, Protect, Detect, Respond and Recover. NIST placed the Govern function at the center of the wheel “because it informs how an organization will implement the other five functions.”
Guiding principles of integrated cybersecurity governance
Effective cyber governance is:
- Risk-based – Prioritizes controls and investments based on potential business impact
- Cross-functional – Involves executive management, legal, risk, finance, and operational leaders
- Transparent – Establishes clear roles, processes, policies, and reporting mechanisms
- Dynamic – Evolves with the business context, regulatory context, and threat landscape
- Outcome-oriented – Links cyber efforts to measurable outcomes: risk reduction, resilience, and trust
Cybersecurity frameworks
Cybersecurity frameworks are evolving to reflect the growing importance of strategic decision-making and governance. Leading frameworks and regulations are converging around a shared principle: cybersecurity must be risk-based, independent, and aligned with enterprise objectives.
Strategic elevation of cybersecurity governance frameworks
The NIST Cybersecurity Framework (CSF) 2.0 introduced a new “Govern” function that sits at the center of the original functions, explicitly calls for cybersecurity governance to be aligned with broader enterprise risk management. The Govern function stresses the importance of understanding the organizational context in establishing a cybersecurity strategy and cybersecurity supply chain risk management.
The Control Objectives for Information Technology (COBIT) from ISACA is a long-used enterprise IT governance framework. It has 6 key concepts for a governance system for IT:
- Provide stakeholder value
- Holistic approach
- Dynamic governance system
- Governance distinct from management
- Tailored to enterprise needs
- End-to-end governance system
The ISO 27000 family published an updated ISO 27014 in 2020 to provide guidance on the objectives and processes for information security governance. Governing bodies and executive management are responsible to:
- Evaluate
- Direct
- Monitor
- Communicate
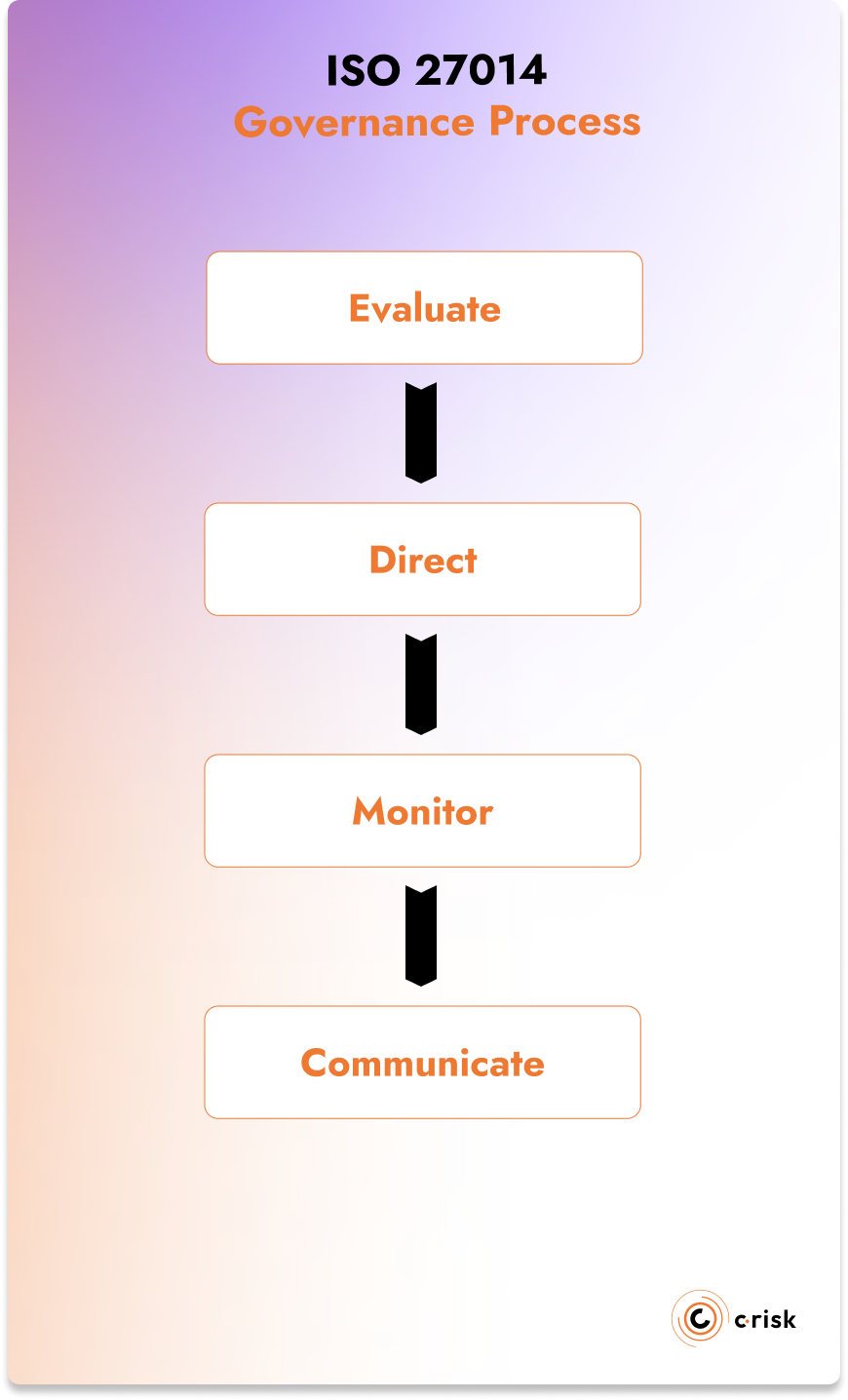
For each of these pillars, the role or process that either the governing body or executive management should perform is detailed. For example, under “Direct” the governing body should “determine the organization’s risk appetite”, while the executive management should “align information security objectives with business objectives.”
Three lines model of cybersecurity governance
The Three Lines Model, also known as the Three Lines of Defense Model, is a governance model that divides organizational risk management responsibilities into three “lines”. The updated framework underscores the importance of the governing body for managing cybersecurity risk within an organization.
- Governing Body: accountable for governance and setting up appropriate structures and processes to enable the achievement of the goals of the organization
- First Line – Operational Management: responsible for executing controls and security measures in day-to-day operations.
- Second Line – Risk Management and Compliance: responsible for the oversight of emerging risks and ensures that the organization complies with relevant laws, regulations, and standards.
- Third Line – Internal Audit: provides objective and independent assurance on the effectiveness and integrity of an organization's risk management processes and controls.
These frameworks all emphasize the importance of governance in establishing processes and objectives. Boards of directors are accountable to their employees, shareholders and regulators. The ability to respond to a crisis situation is fundamental.
Legal frameworks for cybersecurity governance
The EU Digital Operational Resilience Act (DORA) is a regulation that is meant to strengthen digital resilience of financial entities entered into application on January 17, 2025. The text of the new regulation directs management bodies to align business strategies with the information and communication technology (ICT) risk management, stating:
“[…]management bodies should be required to maintain a pivotal and active role in steering and adapting the ICT risk management framework and the overall digital operational resilience strategy.”
There is also a new EU directive known as NIS2 that provides a legal framework for critical and important entities on cybersecurity risk management measures and obligations. It states that management bodies are required to follow training and offer training to their employees on a regular basis to be able to effectively assess risks and cyber security practices.
The EU is forcing boards of directors to take an “active role” in the management of cyber risk and to build digital resilience. To get to the point of digital resilience, these legal frameworks require governing bodies to stay informed and educated and provide resources to their cybersecurity risk management teams.
Cybersecurity governance roles and responsibilities
A mature governance system requires clearly defined roles, aligned with both organizational strategy and cyber risk exposure. Key actors include:
- Board of Directors: Provide oversight, set risk appetite, and ensure accountability at the highest level
- Executive Management (CEO, CFO, COO, CRO): Integrate cybersecurity into business strategy and enterprise risk management (ERM)
- CISO: Leads strategy development and risk reduction efforts, translating cyber risks into business-relevant language, using consistent methodologies like FAIR
- Legal and Compliance: Align cyber efforts with regulatory obligations and manage liability
- Business Unit Leaders: Own and manage risk at the operational level; ensure cyber risks are considered in business decisions
- IT and Security Operations: Implement controls, monitor systems, and respond to incidents
- Third Parties: Extend the organization’s attack surface and must be assessed and governed accordingly
These roles map to widely recognized frameworks including NIST CSF 2.0’s Govern function, ISO 27014’s “Evaluate–Direct–Monitor–Communicate” model, and the Three Lines Model. They ensure that cyber governance is not only defined, but actionable, measurable, and auditable.
Cross-functional collaboration for better governance
Effective cross-functional coordination requires both structured mechanisms and a culture of collaboration. Coordination should be reinforced through established processes defined by the board, such as cross-functional committees or cyber risk management teams, where stakeholders from IT, legal, compliance, risk, and business units regularly review and prioritize key issues. These committees ensure that cybersecurity decisions reflect a balanced view of risk, operational impact, and compliance obligations.
Additionally, organizations should align around shared performance indicators. For example, establishing common metrics such as risk reduction targets, response times, or resilience benchmarks helps create mutual visibility and strengthen accountability. Consistent reporting and regular cross-departmental communication are also essential to break down silos and ensure coordinated, enterprise-wide action.
- Formalize cross-functional cooperation and designate risk liaisons to bridge communication between IT, legal, compliance and executive leadership
- Adopt frameworks like FAIR to enable business-aligned risk language across functions and business units, making cybersecurity actionable for all stakeholders
- Develop a dashboard of key risk indicators to promote transparency and accountability for actions
- Implement regular reviews of cyber risk posture and governance effectiveness with to refine policies and processes
From oversight to insight
The CrowdStrike incident shows that cyber resilience is inseparable from business resilience. Organizations that implement mature cybersecurity governance transform risk management from a cost center into a strategic differentiator.
The path forward requires:
- Board members who understand that cyber risk is business risk
- Executive teams that embed cybersecurity into strategy
- Governance structures that enable data-driven, risk-informed decisions
- A culture where cybersecurity is everyone's responsibility
As regulatory expectations intensify and cyber threats evolve, how quickly can your organization adapt?
At C-Risk, we help organizations move beyond compliance checklists and a reactive, ad hoc security strategy... We empower boards, executives, and business leaders to address cyber risk using objective data with the same rigor applied to financial and operational risks.
In an era where regulatory accountability is intensifying and cyber threats are escalating, boards can no longer afford to treat cybersecurity as a back-office issue. It’s a boardroom priority, and an essential part of fiduciary oversight.
C-Risk can help you:
- Build a data-driven cyber risk program using adapted cybersecurity frameworks to your business context
- Quantify cyber risk in financial terms using the Open FAIR™ model, enabling business-aligned communication and decisions
- Facilitate cross-functional alignment through tailored workshops, training, e-learning and dashboards
- Deploy the SafeOne platform to operationalize your cyber GRC roadmap
Contact us to discuss how a data-driven approach will improve your cyber risk management program.
