Cyber risk management: Fundamentals, challenges, and strategic evolution
Cyber risk is business risk. As organizations expand their digital services and onboard third parties, cyber and technology risks have become inseparable from business risk itself.
CISOs have witnessed this evolution firsthand. Effective cyber risk management demands more than compliance checklists—it requires data-driven methods, quantitative analysis, and frameworks that create a common language for risk. When technical teams and business leaders can discuss cyber risk meaningfully, security decisions align with business objectives, and better decisions follow.
- Business risk reality: Cyber risk has become inseparable from business risk, with third-party breaches doubling in 2024 and incidents like Change Healthcare demonstrating how single attacks can paralyze entire industries and affect millions.
- Qualitative limitations: Traditional color-coded risk matrices and subjective assessments create calibration problems, human bias, and lack the financial context executives need to make defensible investment decisions.
- Power of speaking the language of business: Data-driven cyber risk management allows security leaders to communicate in business terms and improve cyber resilience at the top level.
- FAIR™ framework foundation: Factor Analysis of Information Risk provides the systematic methodology to break down complex scenarios into actionable financial insights that align cybersecurity investments with business objectives.
What is cyber risk management?
ISO 31000 defines risk management as “coordinated activities to direct and control an organization's risk.” In this context risk is defined as “the effect of uncertainty on objectives.”
Applied to cybersecurity, cyber risk management refers to the structured process of identifying, assessing, and addressing risks arising from digital systems, data, and technology use that could disrupt business objectives or create financial, operational, or reputational harm.
At its core, cyber risk management is about making informed, evidence-based decisions that balance protection, performance, and cost. It aims to answer a critical question:
How can we identify our most significant cyber and technology risks, and manage them in a way that delivers the greatest risk reduction relative to our investment and strategic goals?
Modern cyber risk management frameworks are designed to:
- Quantify and prioritize risk scenarios based on likelihood and impact
- Align cybersecurity activities with business priorities
- Enable defensible, ROI-based decisions about controls and investments
By applying risk management principles to the digital domain, organizations can reduce uncertainty, increase resilience, and ensure security programs actively support business growth.
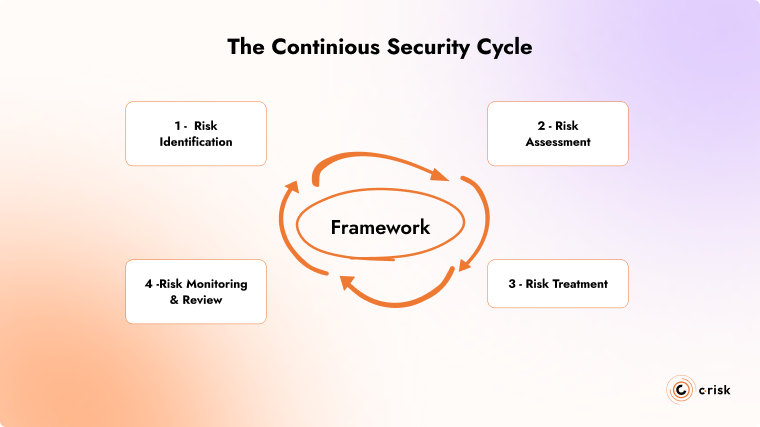
Cyber Risk Management process: the continuous security cycle
The most common risk management standards and frameworks used by large enterprises share a fundamental characteristic: they are cyclical.
The cyber risk management cycle consists of four key phases that repeat continuously:
- Risk Identification: Discovering and documenting potential threats and vulnerabilities
- Risk Assessment: Evaluating and prioritizing identified risks based on likelihood and impact
- Risk Treatment: Implementing controls to address prioritized risks
- Risk Monitoring & Review: Evaluating control effectiveness and identifying new risks
The effectiveness of this approach depends on the frameworks and methods used to identify, collect, and leverage data throughout the cyber risk management cycle.
The high stakes of cyber risk management for large enterprises
Managing Risk in a Complex Digital Ecosystem
In February 2024, a ransomware attack on Change Healthcare, a subsidiary of UnitedHealth Group, America's largest healthcare company, demonstrated how cyber incidents now reach far beyond IT systems. The Change Healthcare ransomware attack paralyzed critical healthcare services nationwide for weeks:
- Pharmacies couldn't process prescriptions
- Hospitals couldn't verify insurance coverage
- Healthcare providers couldn't submit claims
- Patients experienced delays in critical care
For weeks, this single attack on one company disrupted healthcare delivery across the entire United States, affecting millions of patients and thousands of healthcare providers.
This highlights the new reality for large enterprises. Their technology environments have grown exponentially complex, creating unprecedented risk exposure that extends far beyond their own operations. Consider these trends:
- The percentage of breaches involving third parties doubled in 2024, jumping from 15% to 30%
- Cyber insurance data confirms this shift, with 40% of breach claims now involving a third-party connection
- Each new digital initiative, technology integration, and new third-party relationship expands your attack surface
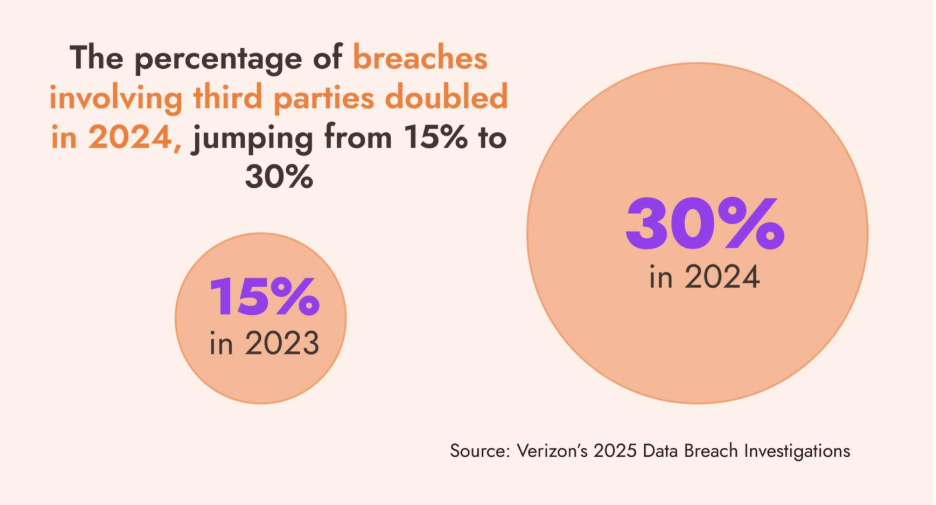
Large organizations operate in interconnected digital ecosystems. Their networks span multiple geographies, cloud environments, partner systems, and remote work locations. Third parties also access your data and networks to increase your productivity. A vulnerability anywhere within the digital ecosystem can compromise an entire organization.
The changing threat landscape requires organizations to prioritize security investments and activities that align with their business objectives, and to use evidence-based methods to mitigate risk.
Evolving compliance requirements
The threat landscapes isn’t the only complexity facing organizations. Regulatory bodies in the US and Europe are writing new regulations to protect consumers and investors. Some of the important regulations to keep an eye on are:
- SEC Cybersecurity Disclosure Rules (US) – requires public companies to disclose material cybersecurity incidents within four business days via Form 8-K and detail their risk management processes with an annual Form 10-K filing.
- DORA (Digital Operational Resilience Act - EU) –mandates that financial entities (incl. banks, insurers, and fintech firms) establish robust ICT risk management frameworks, including third-party risk oversight, and mandatory incident reporting.
- NIS2 Directive (EU) – expands the scope of EU cybersecurity regulations. It applies to a broader set of sectors, including energy, transport, health, and digital infrastructure.
The evolution of cyber risk management methods
In the early days of cybersecurity, infosec leaders employed the same methods used by other business functions to assess and communicate cyber and technology risk: they relied on experience, simplified categorizations, and expert judgment. Security teams built risk registers with color-coded assessments that CISOs presented to the board as heat maps or risk matrices, with clusters of red, amber, and green indicating high, medium, or low risk. This approach was intended to communicate complex cybersecurity risks to non-technical stakeholders, so decision-makers could understand the importance of a risk or a required action.
Subjective analysis reports
This widely adopted approach has some critical limitations. The subjective nature of qualitative assessments makes it difficult for CISOs to effectively communicate security risks and needs in financial and business terms. What constituted "high," "medium," or "low" risk varied dramatically between individuals and departments, which highlights a calibration problem. Two equally knowledgeable professionals could examine the same scenario and reach entirely different conclusions about its severity.
In recognition of these limitations, organizations are now moving beyond these subjective practices toward a data-driven, defensible approach using quantitative methods.
Let’s look at the some of the limitations first.
The limitations of qualitative risk management approaches
Traditional qualitative approaches provide comprehensive frameworks but often lack the financial context needed for prioritization and executive decision-making. While widely practiced by organizations of all sizes, qualitative risk management suffers from several critical weaknesses that undermine its effectiveness in today's complex business environment:
Human bias:
Traditional approaches rely heavily on expert judgment, which inevitably incorporates biases and knowledge gaps. For example, a security expert with recent ransomware recovery experience might rate related threats higher than equally dangerous risks outside their direct experience—creating blind spots and imbalanced security postures.
Inconsistent risk classification:
Ask ten security professionals to rate the same risk, and you'll likely get ten different answers. What one department considers "high risk" might be merely "medium" to another. This inconsistency makes meaningful comparison across business units virtually impossible. Without standardized definitions that everyone understands and applies consistently, risk ratings remain subjective impressions rather than reliable measurements.
Unclear prioritization:
When faced with dozens of "high" risks and red flags, security teams lack a defendable methodology for prioritizing which actions deserve immediate attention or which security investments would deliver the greatest return on investment.
Missing financial context:
"How much will this cost us?" This is the first question most executives ask, yet traditional risk models rarely provide a clear answer. Business leaders allocate resources based on financial impact and return on investment. When CISOs propose risk reduction strategies without addressing the financial impact, they inevitably struggle to justify investment as opposed to competing business projects that come with ROI calculations and revenue projections.
Without the financial and business context that data-driven risk management provides, security programs will continue to struggle to communicate with business leaders and executives. Clear communication using objective data will help strengthen the organization's risk posture by allowing for defensible prioritization and investments.
Evidence-based approaches address these risk management challenges head-on.
The shift to evidence-based, data-driven cyber risk management
Forward-thinking organizations that implement data-driven approaches are able to address the limitations discussed above. This shift to data-driven risk management is a culture shift.
Improved risk analysis and treatment
- Financial Expression of Risk: By quantifying potential loss exposure in monetary terms (dollars, euros, etc.), security teams can speak the language of business executives and board members. This translation establishes cybersecurity as a business issue rather than merely a technical problem.
- Evidence-Based Decision Making: When both risks and controls have associated dollar values, organizations can calculate expected loss reduction per dollar invested, enabling true ROI calculations for security initiatives. These calculations support more informed resource allocation decisions.
- Scenario Comparison: Data-driven methods allow security teams to use objective datapoints to compare different risk scenarios and determine which mitigation strategies deliver the greatest risk reduction relative to cost, which is impossible using traditional high/medium/low ratings.
- Defensible, Transparent Metrics: Data-driven approaches create defensible, repeatable results that stand up to scrutiny in budget discussions and board presentations. This transparency builds trust and credibility for security programs.
- Scalability Through Automation: As organizations face hundreds or thousands of risk scenarios, quantitative frameworks leverage automation to assess risk at scale while maintaining consistency. This is critical for large enterprises with complex digital ecosystems.
FAIR™ Framework: structured risk analysis
The FAIR™ (Factor Analysis of Information Risk) framework is a major part of this culture shift. The FAIR risk analysis method provides a structured approach. The FAIR taxonomy breaks down complex risk scenarios into component parts and applies probabilities and financial impacts. The output of a FAIR analysis generates actionable insights that make it possible to align cyber initiatives with business objectives.
Building a data-driven risk management strategy
Transforming risk conversations
Instead of asking "Is the risk high, medium, or low?", teams employing data-driven methods ask more nuanced questions:
- "What's the financial impact if this asset is compromised?"
- "Is this control investment worth it compared to alternatives?"
- "How much risk reduction do we gain per euro invested?"
Understand Your Business Context
Effective data-driven risk management begins with a deep understanding of your organization's unique business environment. The mapping of critical digital assets, business processes, and value chains builds a comprehensive view of your risk landscape. This contextual awareness ensures that security decisions reflect business priorities rather than abstract technical concerns.
Prioritize Activities and Resources
DDRM employs data-driven analysis to identify which security initiatives will deliver the greatest risk reduction relative to investment and risk appetite. This approach ensures that budget and personnel are directed toward activities that meaningfully reduce business risk rather than simply focusing on the latest threats or compliance requirements.
Strengthen Digital Resilience
Digital resilience extends beyond reducing the likelihood of an incident to ensuring business continuity regardless of disruptions. DDRM builds this resilience by implementing adaptive security frameworks and continuous monitoring that respond to your changing attack surface while maintaining operational efficiency. By quantifying both the impact of potential disruptions and the value of resilience measures using FAIR, organizations can make informed decisions about acceptable risk levels.
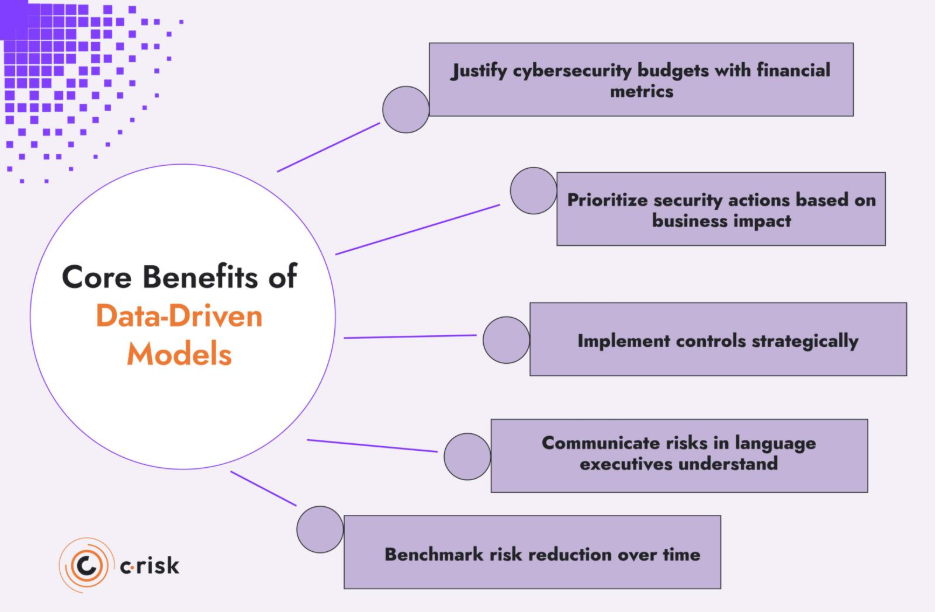
Core benefits of data-driven models
- Justify cybersecurity budgets with financial metrics: Quantitative approaches convert technical risk scenarios into financial terms. This means that security leaders communicate the ROI of security actions and compete effectively for resources during budget cycles.
- Prioritize security actions based on business impact: DDRM identifies which vulnerabilities and threats pose the greatest financial risk to the organization, allowing teams to focus on what matters most.
- Implement controls strategically: Security investments are evaluated based on their cost-effectiveness in reducing specific risk scenarios, optimizing resource allocation.
- Communicate risks in language executives understand: Financial quantification translates complex technical concepts into metrics that resonate with boards and C-suite executives.
- Benchmark risk reduction over time: Consistent measurement methodologies allow organizations to track improvements in their security posture and demonstrate progress to stakeholders.
Elevate the conversation around cyber risk management
Organizations face a critical dilemma: they must take risks to grow, yet most lack the evidence-based insights to do so. While boards push for increased risk appetite to drive growth, executives struggle with risk management frameworks that are designed for compliance, not strategic growth.
Traditional risk management approaches have become a bottleneck through:
- Siloed functions that slow decision-making and create confusion
- Subjective assessments that can't be effectively communicated to leadership
- Focus on operational compliance rather than strategic enablement
- Inability to demonstrate ROI on security and risk investments
- Static frameworks that fail to adapt to changing business conditions
How C-Risk transforms cyber risk management
At C-Risk, we help large organizations use data to tell the story of risk. We can help you address how to:
- Define your DDRM strategy
- Operationalize your cyber risk management
- Accelerate your compliance process
- Manage third-party risk
- Implement a cyber risk management platform
Our data-driven cyber risk management methodology delivers proven results across industries, enabling organizations to move faster, drive strategic growth, and strengthen resilience.
Ready to strengthen your risk posture? Connect with our team to explore how targeted improvements to your cyber risk management process can deliver measurable results.
