Cybersecurity Regulations and Standards: A Practical Mapping of GDPR, ISO 27001, PCI-DSS, SEC, and Emerging Security Frameworks
Most organizations are subject to a mix combination regulations, standards, and market-driven frameworks that differ in enforceability but often require similar controls and reports. What these cybersecurity regulations and standards mean for your existing security program depends on your many factors.
Without a clear view of applicability, overlap, and priorities, compliance efforts can drift toward a checkbox activity rather than strengthening resilience or risk management. This article addresses some of the major standards and regulations and how you can go from self-assessment to operationalizing the compliance process to strengthen resilience and add value.
- Understanding which regulations apply to your organization is the starting point for any compliance effort
- Many regulatory requirements overlap, and mapping them to your current controls helps identify gaps and avoid unnecessary duplication
- Security and compliance programs are most effective when they are adapted to the specific regulatory obligations an organization actually faces
- A risk-based, data-driven approach supports proportionality and helps demonstrate resilience and sound risk management
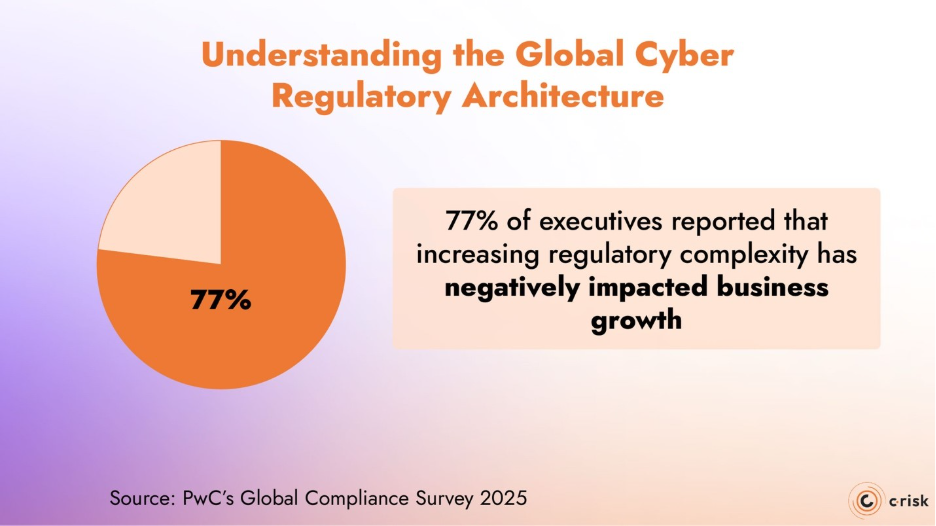
Understanding the Global Cyber Regulatory Architecture
Most organizations operate within a multi-layered architecture of binding regulations, supervisory expectations, and widely adopted security standards. Cyber and business leaders need to understand how frameworks interact, where obligations overlap, and what non-compliance means. In a recent global compliance survey from PwC, 77% of executives reported that increasing regulatory complexity has negatively impacted business growth, with cybersecurity and privacy among the most burdensome areas.
Treating all regulatory frameworks and standards with the same checkbox mentality leads to missed opportunities and unjustified resource allocation.
Mandatory Regulations vs. Standards
Not all cybersecurity frameworks carry the same legal and regulatory weight, but they could all materially affect your organization’s risk profile.
Mandatory regulations are legally binding and enforced by supervisory authorities. Non-compliance can result in:
- Financial penalties
- Regulatory remediation orders
- Executive accountability
- Reputational damage
Examples include:
- GDPR (EU and UK)
- DORA (EU financial sector)
- NIS2 (EU critical and important entities)
- SEC cybersecurity disclosure rules (US-listed companies)
Cybersecurity standards, such as ISO 27001 and PCI-DSS, are not legal obligations. However, they are often:
- Required by customers or partners
- Embedded in contractual obligations
- Used by regulators as evidence of “appropriate security measures”
- Critical for accessing certain markets or services
In practice, failing to meet these standards can lead to:
- Loss of business
- Termination of payment processing rights
- Increased scrutiny during regulatory investigations
While enforceability differs, risk exposure does not. Organizations that strategically combine regulatory compliance with recognized standards are better positioned to demonstrate control maturity, resilience, and governance.
Integrating Regulations and Standards as Part of a Holistic Risk Management Approach
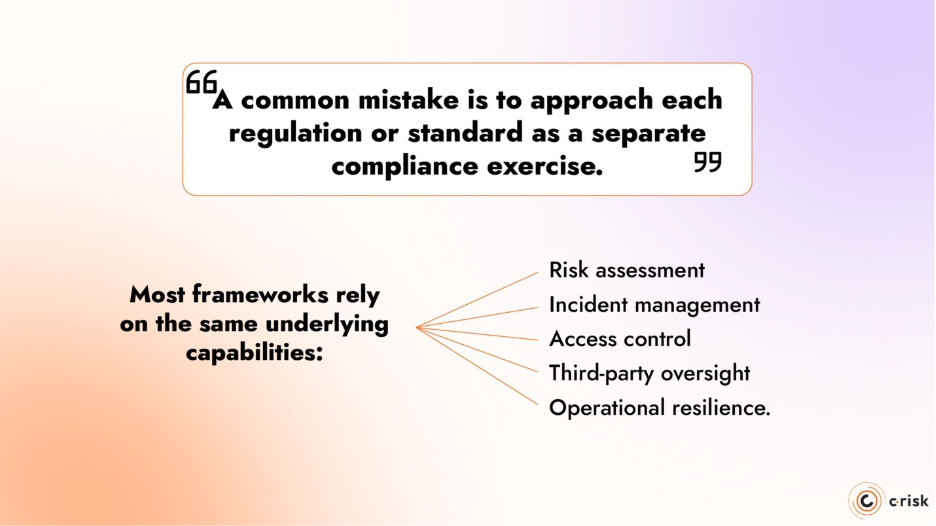
A common mistake is to approach each regulation or standard as a separate compliance exercise. In reality, most frameworks rely on the same underlying capabilities:
- risk assessment
- incident management
- access control
- third-party oversight
- operational resilience.
ISO 27001, for example, provides a structured governance and control framework that supports GDPR security obligations and incident response expectations. PCI-DSS enforces technical safeguards that reduce the likelihood and impact of data breaches, which in turn lowers regulatory and litigation risk. DORA and NIS2 build on these foundations by raising expectations around resilience, testing, and executive accountability rather than introducing entirely new control families.
When these compliance frameworks and standards are managed in silos, organizations duplicate effort and increase cost without meaningfully reducing risk. When they are treated as a single, interconnected system, compliance work becomes easier to justify, easier to explain, and easier to defend internally and to regulators.
Panorama of Major Cybersecurity Regulations and Standards
The regulations and standards outlined below reflect common obligations and control expectations that recur across the global cyber regulatory landscape. While their legal status, scope, and enforcement mechanisms differ, they consistently address the same core areas
What are the Major Cybersecurity Regulations?
GDPR – Data privacy in the EU and UK
The General Data Protection Regulation (GDPR) establishes a comprehensive legal framework for the protection of personal data across the European Union and the United Kingdom. It imposes explicit security and governance obligations that make cybersecurity a core compliance requirement.
Key cybersecurity-related obligations include:
- Implementing appropriate technical and organizational security measures
- Ensuring the confidentiality, integrity, and availability of personal data
- Detecting and reporting qualifying personal data breaches within strict timeframes
- Demonstrating accountability through documentation, governance, and controls
Non-compliance with GDPR can result in a heavy financial penalty. For the most serious violations, fines can reach up to 4% of the company’s global annual turnover, in addition to remediation costs, litigation exposure, and reputational damage.
SEC Cybersecurity Disclosure Rules
In the United States, the Securities and Exchange Commission (SEC) has introduced cybersecurity disclosure requirements for publicly listed companies. These rules focus less on prescriptive security controls and more on governance, transparency, and accountability.
Key elements include:
- Timely disclosure of material cybersecurity incidents
- Clear articulation of cyber risk management and governance practices
- Board-level oversight of cybersecurity risk
- Consistency between internal risk assessments and external disclosures
The SEC framework reinforces the idea that cybersecurity is a board concern and should be treated as an enterprise risk. It focuses on governance and disclosures, with direct implications for executive responsibility and investor confidence.
DORA and Digital Operational Resilience in the Financial Sector
The Digital Operational Resilience Act (DORA) is a binding EU regulation that applies to financial entities and certain third-party service providers supporting the financial sector. Its objective is to ensure that organizations can withstand, respond to, and recover from ICT-related incidents.
DORA establishes harmonized requirements across five core areas:
- ICT risk management and governance
- Incident classification and regulatory reporting
- Digital operational resilience testing, including advanced threat-led testing
- ICT third-party and supply-chain risk management
- Information-sharing arrangements on cyber threats and vulnerabilities
Unlike earlier sector-specific guidance, DORA creates direct and enforceable obligations at the EU level. For regulated financial institutions, DORA elevates cybersecurity and ICT resilience from an operational concern to a supervisory and board-level responsibility, with clear expectations around accountability, documentation, and testing.
NIS2 and the Security of Networks and Information Systems
The NIS2 Directive strengthens and expands the EU’s framework for cybersecurity across critical and important sectors. It significantly broadens the scope of the original NIS Directive and introduces more stringent security, reporting, and governance requirements.
NIS2 applies to organizations operating in sectors such as:
- Energy, transport, healthcare, and digital infrastructure
- Financial market infrastructure
- Manufacturing, logistics, and certain digital service providers
Core obligations under NIS2 include:
- Risk-based technical and organizational security measures
- Incident notification within defined timeframes
- Business continuity and crisis management planning
- Supply-chain and third-party risk controls
- Management accountability for cybersecurity governance
NIS2 introduces stronger enforcement mechanisms, including administrative fines and the possibility of direct sanctions against senior management. While implementation is handled at the national level, the directive aims to create a more consistent baseline of cybersecurity maturity across the EU.
For organizations newly brought into scope, NIS2 represents a material shift: cybersecurity moves from an IT responsibility to an enterprise risk and governance issue with legal and personal accountability implications. DORA and NIS2 are proportional frameworks, meaning that the regulatory authorities do not expect identical controls from all organizations; expectations scale with organizational size, systemic importance, risk exposure, and criticality of services.
HIPAA and Healthcare Data Security
The Health Insurance Portability and Accountability Act (HIPAA) is a US federal regulation governing the protection of health information. Its cybersecurity requirements are defined primarily by the HIPAA Security Rule, which applies to covered entities and their business associates handling protected health information (PHI).
HIPAA requires the implementation of reasonable and appropriate safeguards to protect the confidentiality, integrity, and availability of PHI, including:
- Administrative safeguards (risk analysis, policies, workforce training)
- Physical safeguards (facility, device, and media controls)
- Technical safeguards (access controls, audit logging, integrity and transmission controls)
The regulation is intentionally risk-based and non-prescriptive, placing emphasis on documented risk assessments and governance rather than specific technologies. If the regulatory body finds a violation, there organizations can face civil and criminal penalties.
What are Some Major Cybersecurity Standards?
ISO 27001
ISO/IEC 27001 is an international standard for establishing, operating, and continually improving an Information Security Management System (ISMS). It is not a regulation and carries no direct legal penalties, but it plays a central role in how organizations structure and govern cybersecurity.
ISO 27001 focuses on:
- Risk-based identification and treatment of information security risks
- Governance, policies, and accountability
- Continuous improvement and auditability
- Alignment between security controls and business objectives
Certification is often used to:
- Demonstrate security maturity to customers and partners
- Support regulatory compliance efforts (including GDPR, DORA, and NIS2)
- Standardize security practices across complex or multinational organizations
Rather than adding new obligations, ISO 27001 provides a coherent structure that helps organizations meet multiple regulatory expectations consistently and defensibly.
PCI-DSS and Ensuring Card Payment Security
The Payment Card Industry Data Security Standard (PCI-DSS) applies to any organization that processes, stores, or transmits payment card data. It is a contractual standard enforced by payment card networks, not a government regulation.
PCI-DSS requirements cover:
- Network security and segmentation
- Protection of cardholder data
- Access control and monitoring
- Vulnerability management and testing
- Incident response readiness
Compliance obligations vary based on transaction volume and processing model, but non-compliance can result in financial penalties imposed by acquiring banks, increased transaction fees, investigations as well as the suspension or termination of your payment processing capabilities.
For many organizations, PCI-DSS compliance is a prerequisite for operating, making it operationally as critical as formal regulation.
Building a Strategy to Navigate the Regulatory Landscape and Prioritize Action
Without a structured approach, compliance efforts risk becoming fragmented, reactive, and inefficient. An effective strategy focuses on prioritization, traceability, and integration, which allows you to meet regulatory obligations while maximizing operational value.
Two complementary mechanisms support this approach: a self-assessment to determine applicability and a regulatory and controls mapping across frameworks to assess the current state and what controls to prioritize.
Applicability Self-Assessment Guide
Structuring Regulatory Complexity
Not every regulation applies to every organization in the same way. A structured self-assessment enables organizations to determine which frameworks apply, to what extent, and with what priority, transforming regulatory complexity into a manageable and defensible action plan.
Core Components of the Self-Assessment
An effective assessment typically includes:
- Qualification questionnaire
Identification of sector, geography, organizational size, services provided, data types processed, and overall regulatory exposure. - Applicability criteria
Determination of in-scope status under each relevant framework (for example, NIS2 essential versus important entity classification, or DORA financial entity categorization). - Impact-based prioritization
Assessment of regulatory, operational, financial, and reputational impact to rank obligations and focus efforts where non-compliance would be most material. - Implementation planning
Sequencing of remediation and compliance actions based on urgency, dependencies, available resources, and business constraints.
Example: International Technology SME
For an international technology SME, this process may involve:
- Identifying GDPR applicability based on personal data processing activities and geographic reach
- Assessing potential NIS2 exposure based on sector classification and EU presence
- Evaluating contractual or market-driven obligations linked to ISO 27001 or PCI-DSS
- Mapping overlapping controls across frameworks and identifying gaps
- Developing a compliance roadmap aligned with growth objectives and risk tolerance across functions
Approached this way, compliance efforts remain proportionate, transparent, and aligned with business priorities, rather than simply implementing controls for the sake of compliance.
Regulatory and Controls Mapping Across Frameworks
Identifying Overlaps Between Regulatory Requirements
Despite differences in legal status, scope, and enforcement mechanisms, most cybersecurity regulations and standards rely on a shared set of underlying control domains. These typically include governance, risk assessment, access management, incident response, third-party oversight, and operational resilience.
Rather than managing GDPR, ISO 27001, DORA, PCI-DSS, or sector-specific rules as isolated initiatives, a unified regulatory and control mapping approach enables organizations to identify where requirements overlap and where a single control can satisfy multiple regulatory obligations.
Practical Benefits of Regulatory and Controls Mapping
A unified mapping exercise allows organizations to:
- Identify common control requirements across multiple frameworks
- Reuse controls, documentation, and evidence across regulatory obligations
- Avoid redundant implementation efforts and parallel processes
- Prioritize controls with the highest regulatory and risk impact with FAIR-based assessments
- Demonstrate consistency and transparency to regulators, customers, and auditors
Concrete Example: Mapping ISO 27001, GDPR, and DORA
ISO 27001 provides a governance-driven control framework that aligns closely with multiple regulatory requirements. Controls related to access management, incident handling, supplier security, and business continuity directly support:
- GDPR obligations regarding appropriate technical and organizational measures and personal data breach management
- DORA requirements for ICT risk management, incident reporting, resilience testing, and third-party risk oversight
By mapping ISO 27001 controls to GDPR and DORA requirements, organizations can use a single, coherent control framework to support multiple regulatory obligations, reducing duplication while strengthening governance and resilience.
C-Risk Helps Organizations Build Resilience Through Data-Drive Risk Management
C-Risk supports organizations navigating GDPR, DORA, NIS2, ISO 27001, PCI-DSS, and disclosure-driven regimes by shifting the conversation from “framework-by-framework compliance” to a defensible, risk-based model using the FAIR™ standard.
We help you:
- anchor regulatory requirements to defined risk appetite and tolerance, enabling proportionate and defensible decision-making
- translate cyber risk and compliance requirements into a common language across security, legal, compliance, finance, and the business
- assess the effectiveness of existing controls and identify gaps based on financial impact rather than checklist completeness
- operationalize risk and control assessments so that they inform prioritization, remediation planning, and ongoing governance
If you would like to learn more how we can help you operationalize your compliance program or build a data-driven risk management program, schedule a call with a C-Risk expert today.
