The Cost of Shadow AI: How to Manage AI Risk in a Changing Landscape
Employees are using AI tools your security team doesn't know about. Without clear policies, shadow AI spreads unchecked across your organization. This article breaks down what it costs, why it spreads, and how to manage your exposure using the FAIR framework.
.png)
What Is Shadow AI?
Shadow AI is the use of artificial intelligence tools, including generative AI, by employees without the knowledge, approval, or oversight of IT or security teams.
How is shadow AI different than shadow IT?
Shadow AI is a more specific evolution of shadow IT, the longstanding practice of using unapproved technology at work. The key difference is the nature of the risk. Shadow IT can lead to employees leaking sensitive data or intellectual property (IP) via a public chatbot, or relying on an AI-powered tool for a mission-critical task with no oversight, no audit trail, and no way to reconstruct what happened.
The business cost of unmanaged AI
When an employee pastes a confidential client contract into a public ChatGPT session, your client's data and your reputation are immediately at risk.
IBM’s Cost of a Data Breach Report 2025 reports that shadow AI was a factor in one in five breaches studied, adding an average of $670,000 in additional breach costs compared to organizations with little or no shadow AI. That makes ungoverned AI one of the top three costliest breach factors of the year. Meanwhile, 97% of organizations that experienced an AI-related security incident lacked proper AI access controls, and 63% had no AI governance policy at all.
Why Shadow AI Is Spreading Across Your Organization
Shadow AI is not, for the most part, the result of malicious intent. Employees are using these tools because they want to improve the quality of their work or increase productivity.
GenAI is embedded in tools your employees already use
Many generative AI tools are freely available, browser-based, or added to SaaS products your employees use every day. Microsoft 365, Google Workspace, Notion, Slack, and hundreds of other platforms have embedded AI features into existing subscriptions. Because these capabilities arrive inside already-sanctioned applications, they rarely trigger the scrutiny of a new tool adoption. IT and security teams need policies that govern not just new software, but new AI capabilities embedded within existing tools.
Most organizations still have no AI governance policy
63% of organizations either lack AI governance policies entirely or are still developing them. When no policy around AI use exists, employees make their own decisions.
The result is predictable. By the time a security team implements an AI usage policy, dozens of GenAI tools are already being used in live workflows.
The Cybersecurity Risks of Shadow AI
Shadow AI doesn’t introduce entirely new categories of risk. It accelerates familiar cybersecurity failures, just through a new interface. At its core, AI risk is still about protecting data, systems, and decision integrity.
Data exposure and compliance failures
- Unauthorized data processing: Employees paste sensitive data into public AI tools, where it may be retained, logged, or used for training.
- Regulatory non-compliance: GDPR, the EU AI Act, DORA, and NIS2 impose strict requirements on how data is processed. Unsanctioned AI use creates gaps that are difficult to audit or defend.
- No audit trail: AI-assisted decisions often leave no record of inputs, outputs, or user actions, making incident investigation and accountability difficult.
Attack vectors and model integrity risks
Shadow AI expands the attack surface in ways security teams don’t monitor:
- Expanded attack surface: Unapproved tools, APIs, and plug-ins create unmanaged entry points into corporate data
- Prompt injection: Malicious inputs manipulate models to leak data or perform unintended actions
- Data leakage via outputs: Sensitive information can be exposed through generated responses
- Unvetted models: Unknown training data and behavior introduce risks of bias, hallucination, or hidden data exposure
- AI supply chain risk: Compromised third-party tools or integrations can become a pathway into internal systems

How Shadow AI Leads to Organizational Drift
Organizational drift is what turns approved AI into shadow AI over time. This is what makes organizational drift a distinct challenge in AI governance. The risk profile of a tool at the point of implementation is not the same as its risk profile six or twelve months later.
SaaS-based AI tools ship new features continuously. A tool assessed and approved for one use case may quietly gain the ability to process additional data types, connect to third-party services, or operate more autonomously. If those changes aren't reassessed, the organization is effectively running an unreviewed tool inside an approved wrapper.
At the same time, new employees are joining your team. And without ongoing cyber awareness training that specifically covers AI tools and acceptable use, staff may not know what falls within policy and what doesn't. A developer who joined after the AI policy was last updated has no reliable way of knowing what is and isn't sanctioned unless that information is actively communicated.
This is where governance leaders and risk leaders need to work in step. Governance teams need to communicate policy changes clearly and regularly, not just publish them. Risk teams need to stay current with the generative AI landscape, tracking how tools are evolving and what new capabilities or integrations might change the exposure of tools already in use. An AI risk assessment is not a one-time exercise. The landscape it was designed to reflect keeps changing.
How to Assess and Manage Shadow AI Risk: A 5-Step Framework
Assessing AI risk follows the same structure as any technology or cyber risk assessment: identify the assets, define the threat scenarios, evaluate the controls in place, and quantify the exposure. The first challenge is that "AI" is not a single technology. LLMs, multimodal generative AI, embedded AI features in SaaS products, and custom API-based deployments each have different capabilities, data flows, and threat surfaces, so the scope of the AI risk assessment needs to reflect the specific technology in use.
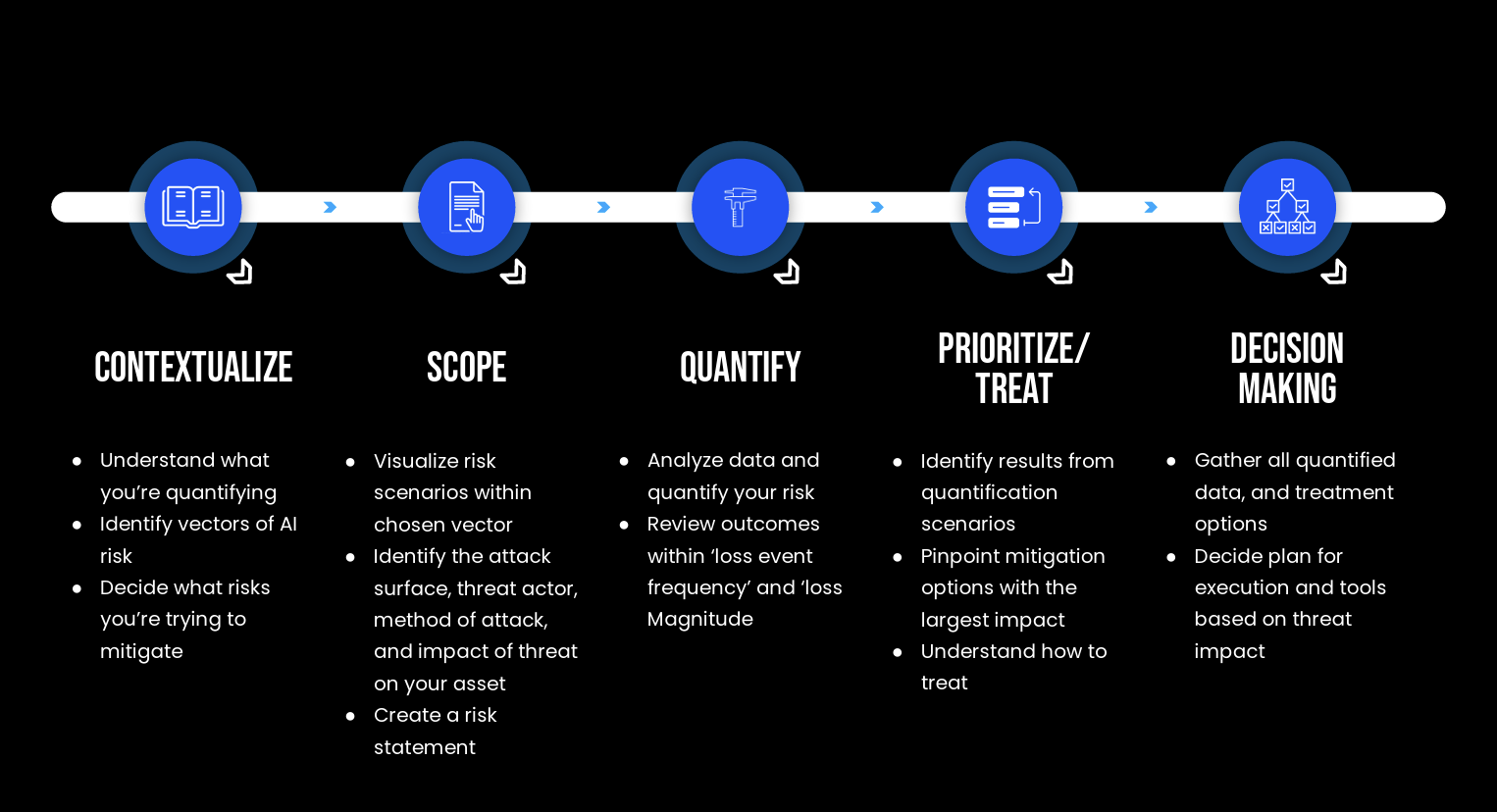
The FAIR Institute has developed a method based on the FAIR standard for AI called FAIR-AIR. FAIR-AIR uses a five-step framework:
1. Contextualize
Establish why you are conducting this assessment and what is driving it. Regulatory pressure, a recent incident, a new AI deployment, or an upcoming audit all produce different scoping priorities and different definitions of what a material loss event looks like.
2. Scope your risk scenarios
For each AI deployment, identify the attack surface, the plausible threat actors, the method of attack, and the asset at risk. Shadow AI scenarios typically cluster around three areas of the CIA triad: confidentiality (data leakage via public LLM, prompt injection), integrity (model poisoning, biased or manipulated outputs), and availability (dependence on a third-party AI service with no fallback).
3. Identify critical assets at risk
For each scenario, determine what data the tool can access or receive as input: personal data, client records, source code, financial information, internal strategy. Asset sensitivity drives exposure severity and shapes which scenarios to prioritize.
4. Quantify with FAIR
Using the FAIR™ framework, each threat scenario produces a range of probable financial outcomes, including frequency of occurrence, expected loss per event, and maximum plausible loss. This gives leadership a basis for decision-making that high/medium/low ratings cannot provide.
5. Prioritize and decide
Based on quantified exposure, identify which controls deliver the best risk reduction per dollar spent, whether that's deploying a private LLM, enforcing data classification before AI tool use, implementing AI-specific DLP policies, or tightening access controls. The output isn't just a ranked list: it's a defensible recommendation for how to act and what to spend.
C-Risk helps security and risk leaders assess and quantify their GenAI and shadow AI risk using the FAIR™ framework, translating exposure into financial terms that drive decisions and satisfy boards.
If you are deploying a new AI initiative or digital tool and need to understand how it reshapes your risk landscape before it goes live, C-Risk delivers quantified risk assessments for new digital initiatives that give project and security stakeholders a shared, financially grounded view of the risks involved.
What is shadow AI?
Shadow AI is the use of AI tools by employees without the knowledge or approval of IT or security teams.
How widespread is shadow AI?
According to the IBM Cost of a Data Breach Report 2025, shadow AI was involved in 20% of breaches studied, and 63% of breached organizations lacked AI governance policies, meaning the majority have no structured oversight of how AI tools are being used internally.
What data is most at risk from shadow AI?
Any data employees can easily copy and paste into AI tools - especially customer data, source code, internal strategy documents, financial information, and HR records, as well as data protected under regulations like GDPR, DORA, and NIS2.
Related articles
Read more on cyber risk, ransomware attacks, regulatory compliance and cybersecurity.

.svg)

.png)