HIPAA: Definition, Rules and Obligations for Cybersecurity Experts
The healthcare sector has become the prime target of cybercriminals. According to the annual IBM and Ponemon Institute report, the average cost of a healthcare data breach in the United States reached $9.77 million in 2024, a record the industry has held since 2011. In this context, HIPAA (Health Insurance Portability and Accountability Act) stands as the essential regulatory framework for any cybersecurity professional working with actors in the American healthcare system. For European organizations, the closest equivalent is the GDPR (General Data Protection Regulation): just as HIPAA does in the United States, the GDPR governs the collection, processing, and protection of personal data, including health data, and provides for significant financial penalties in the event of non-compliance.
Mastering HIPAA its foundations, rules, sanctions, and operational implications is now a core competency for any cybersecurity expert working in an international context. This article offers a comprehensive overview:
- The foundations of HIPAA: origins, scope of application, and protected data (PHI, ePHI)
- The three fundamental rules: the Privacy Rule, Security Rule, and Breach Notification Rule, and their concrete technical requirements
- The implications for cybersecurity experts: financial penalties, the Anthem case study, and key responsibilities
- Compliance best practices: an operational guide for supporting a HIPAA-regulated organization
- HIPAA and artificial intelligence: new risks, specific challenges, and the future of the regulatory framework
.png)
HIPAA: Understanding the Foundations of a Landmark Federal Law
Origins and Objectives
Enacted on August 21, 1996, HIPAA (Health Insurance Portability and Accountability Act) is one of the most important federal laws in the American healthcare system. Originally, it pursued two objectives: ensuring health insurance portability when changing or losing a job, and modernizing the administrative management of the healthcare system.
It is its "Administrative Simplification" provision that has most profoundly transformed cybersecurity practices in healthcare. By establishing national data protection standards, HIPAA forced the entire sector to develop a genuine culture of information confidentiality and security.
In 2009, the HITECH Act (Health Information Technology for Economic and Clinical Health Act) strengthened and extended the law, notably by broadening compliance obligations to subcontractors and tightening financial penalties for HIPAA violations. From that point on, HIPAA compliance became a full-fledged cybersecurity challenge in its own right.
Who Does HIPAA Apply To?
HIPAA applies to two broad categories of actors, overseen by the U.S. Department of Health and Human Services (HHS) and its enforcement arm, the HHS Office for Civil Rights (OCR):
Covered Entities: any actor in the American healthcare system that creates, receives, transmits, or stores health information. This includes healthcare providers (physicians, hospitals, clinics, pharmacies), health plans (health insurance companies, mutual funds, retirement plans with health benefits), and healthcare data processing organizations (clearinghouses).
Business Associates: any external company that handles health data on behalf of a covered entity falls into this category. This includes cloud hosting providers, medical software publishers, cybersecurity service providers, audit firms, and IT subcontractors. These partners must sign a Business Associate Agreement (BAA), a contract formalizing their obligations under the Health Insurance Portability and Accountability Act.
This broad definition has direct implications for cybersecurity experts: as soon as they work on systems handling American health data, they themselves become subject to HIPAA obligations.

Protected Data: PHI and ePHI
At the heart of HIPAA lies the concept of protected health information (PHI), also referred to as individually identifiable health information — meaning any information that can identify an individual and is related to their health status, the provision of healthcare, or payment for healthcare. This covers a very wide scope: names, addresses, Social Security numbers, dates of birth, lab results, medical histories, patient record numbers, billing data, and more.
The digital version of this data is referred to as electronic protected health information (ePHI), and it is precisely the protection of ePHI that sits at the core of HIPAA-related cybersecurity challenges. Any compromise of this data, whether through unauthorized access, exfiltration, or destruction, potentially constitutes a HIPAA violation with serious consequences.
The Three Fundamental HIPAA Rules and Their Technical Requirements
The HIPAA Privacy Rule: Governing the Use of Health Data
The HIPAA Privacy Rule establishes the conditions under which PHI may be used, disclosed, or shared. It came into effect in 2003 and establishes a foundational principle: without explicit patient authorization, the disclosure of health data is prohibited, except in specific cases provided for by law (medical emergencies, public health, judicial investigations, etc.).
In practice, the Privacy Rule requires organizations to:
- Define and document PHI management policies accessible to all staff members.
- Appoint a Privacy Officer responsible for implementing and overseeing compliance.
- Train all employees on confidentiality rules, with documented records of training completion.
- Provide patients with a Notice of Privacy Practices (NPP) explaining how their data is used.
- Guarantee patients the right to access their own health data within 30 days.
For cybersecurity experts, the Privacy Rule demands particular vigilance over data access logs: any consultation or extraction of PHI not justified by a legitimate medical purpose may constitute a violation, even in the absence of malicious intent.
The HIPAA Security Rule: The Core of Cybersecurity Requirements
The HIPAA Security Rule is the most directly relevant text for information security professionals. It applies exclusively to ePHI and mandates three categories of safeguards that form the foundation of any HIPAA privacy and security strategy.
Administrative safeguards form the backbone of compliance. They include conducting a documented risk analysis across the organization (enterprise-wide risk analysis), developing a risk management plan, implementing access control policies, establishing incident response procedures, and maintaining an ongoing staff training program.
Physical safeguards are designed to protect the equipment and facilities that house ePHI: physical access controls for server rooms, workstation use policies, and secure disposal procedures for decommissioned IT equipment.
Technical safeguards directly concern security tools and architectures. The HIPAA Security Rule mandates strict access controls (strong authentication, rights management based on the principle of least privilege), audit and logging mechanisms, data integrity controls, and the implementation of encryption procedures for data both in transit and at rest.
A critical point that is often misunderstood: the Security Rule distinguishes between "required" (mandatory) specifications and "addressable" specifications (to be assessed based on context). The latter does not mean "optional," but rather "to be implemented if appropriate, or replaced by an equivalent documented alternative." In practice, the encryption of ePHI is treated as a de facto requirement by the OCR.
The major update proposed by HHS in January 2025, the most significant since 2013, goes even further: making encryption mandatory (no longer merely "addressable"), requiring multi-factor authentication (MFA) for all access to ePHI, mandating regular penetration testing, and requiring comprehensive inventories of all systems that store health data.
The Breach Notification Rule: Managing and Reporting Incidents
The Breach Notification Rule imposes specific obligations in the event of a data breach involving unsecured PHI. Notification deadlines are strict and non-negotiable:
- Within 60 days of discovering a breach: mandatory notification of affected individuals and the HHS Office for Civil Rights (OCR).
- Without unreasonable delay for breaches affecting more than 500 individuals in a single state: notification of local media outlets.
- Annually for breaches affecting fewer than 500 individuals: an aggregated report submitted to HHS.
There is an important advantage for well-secured organizations: if compromised ePHI is encrypted and therefore unusable by attackers, the incident is not considered a "breach" under HIPAA, and notification obligations do not apply. This is one of the strongest arguments in favor of a systematic encryption strategy, and a concrete reason for cybersecurity experts to build encryption in from the design stage.
The Concrete Implications for Cybersecurity Experts
Severe Financial Penalties That Engage Organizational Liability
Non-compliance with HIPAA exposes organizations to significant civil and criminal sanctions. The penalty structure is organized into four tiers based on the degree of culpability:
Tier 1 - Lack of knowledge, no negligence - $137 – $68,928 penalty per violation
Tier 2 - Reasonable cause, corrected - $1,379 – $68,928 penalty per violation
Tier 3 - Reasonable cause, not corrected - $13,785 – $68,928 penalty per violation
Tier 4 - Willful neglect, not corrected - $68,928 – $2,067,813 penalty per violation
Criminal penalties may also apply in cases of intentional violation, with potential imprisonment of up to 10 years. In 2024, the OCR closed 22 enforcement actions with financial penalties, collecting more than $9.9 million in fines over the year. Beyond regulatory sanctions, organizations must also account for patient class-action lawsuits, technical remediation costs, and reputational damage — costs that often represent the largest share of the total financial impact.

Case Study: The Anthem Breach, the Largest HIPAA Penalty in History
The Anthem Inc. case remains the definitive reference point for the consequences of a violation of the HIPAA Privacy and Security Rules. In 2015, this health insurance company, the second largest in the United States and a licensee of the Blue Cross Blue Shield Association, suffered a series of sophisticated cyberattacks attributed to state-sponsored actors. The attackers exfiltrated the ePHI of nearly 79 million individuals: names, dates of birth, Social Security numbers, postal addresses, employment data, and income information.
The investigation conducted by the HHS Office for Civil Rights (OCR) uncovered several critical failures to meet the requirements of the HIPAA Security Rule:
- No enterprise-wide risk analysis had been documented.
- Insufficient access controls allowed unauthorized connections to go undetected.
- Lack of system activity monitoring (audit controls).
- Absence of adequate incident response procedures.
In October 2018, Anthem agreed to settle for $16 million with the OCR — the largest HIPAA penalty ever imposed, according to HHS. A further $115 million settlement was reached in a class-action lawsuit brought by affected individuals. In total, Anthem paid over $179 million to resolve all legal and regulatory consequences of the breach.
This case illustrates a fundamental point for any cybersecurity expert: the technical failures identified (no MFA, uncontrolled access, no logging) directly constitute HIPAA violations. Preventing them is at the very heart of the work of security professionals operating in healthcare environments.
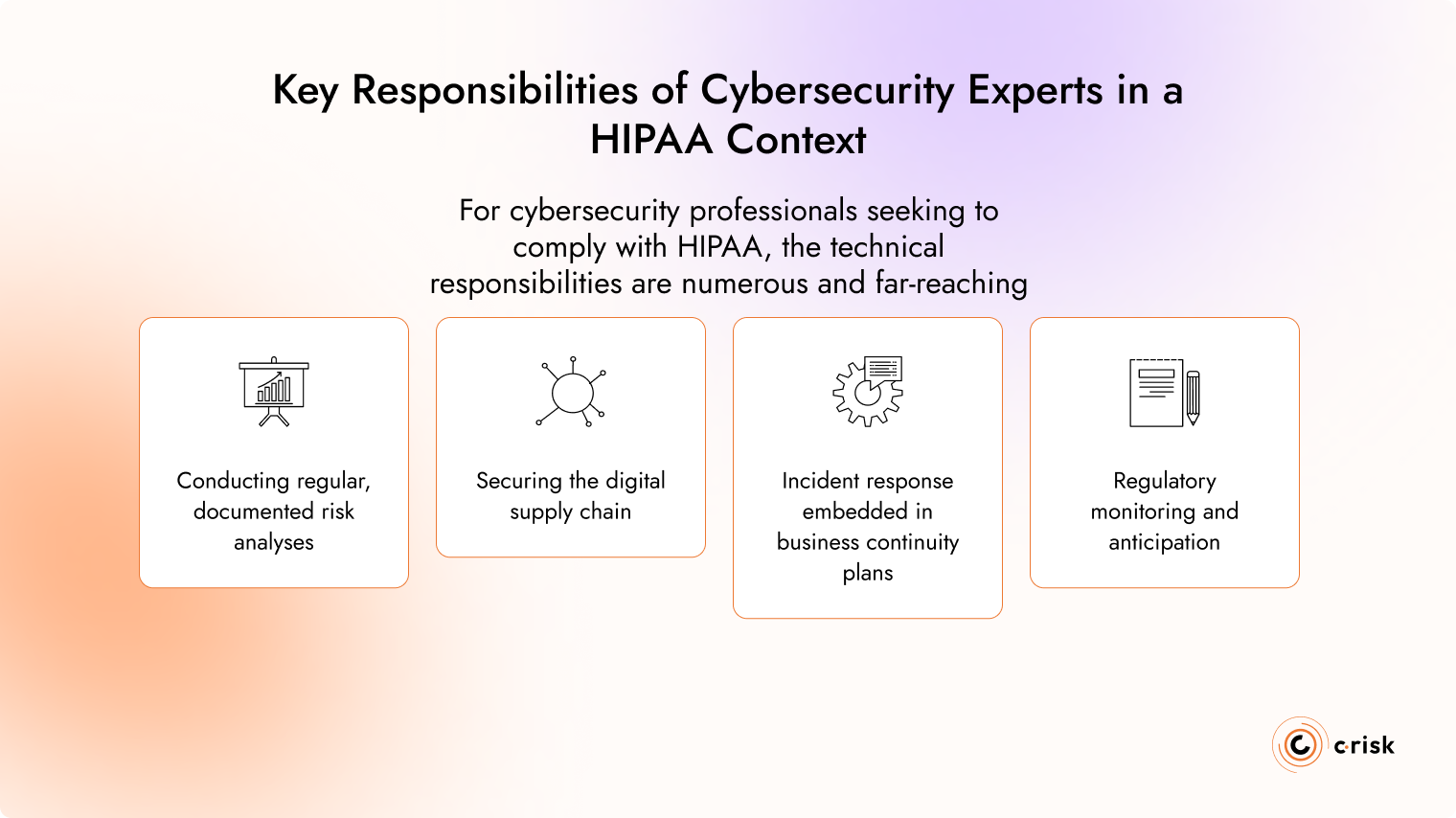
Key Responsibilities of Cybersecurity Experts in a HIPAA Context
For cybersecurity professionals seeking to comply with HIPAA, the technical responsibilities are numerous and far-reaching.
Conducting regular, documented risk analyses is the first pillar. The OCR identifies the absence of a risk assessment as one of the most frequently cited violations during its audits. The analysis must identify all sources of ePHI within the organization, map threats and vulnerabilities, assess the likelihood and impact of each scenario, and document the remediation measures implemented. It must be repeated with every significant change to the information system.
Identity and Access Management (IAM) is a major undertaking. The access controls required by HIPAA demand granular rights management: least privilege principle, unique identifiers for each user, immediate revocation of access upon an employee's departure, and MFA deployment. According to the IBM/Ponemon 2024 report, breaches involving compromised credentials take an average of 292 days to detect and contain — a window of exposure with dramatic consequences for health data.
Securing the digital supply chain is a growing challenge. Every external vendor accessing ePHI must be governed by a Business Associate Agreement (BAA) and subject to regular security assessments (vendor risk assessments). The supply chain now represents a major attack vector: the ransomware attack against Change Healthcare in February 2024, a subsidiary of UnitedHealth Group, exposed the systemic vulnerability of third-party providers. The total cost to UnitedHealth Group is estimated at between $2.3 and $2.45 billion, and the incident compromised the data of nearly 30% of the American population.
Incident response must be embedded in business continuity plans. Cybersecurity teams must be able to quickly qualify an incident (does it constitute a breach under HIPAA?), document the actions taken, preserve evidence, and meet the notification deadlines imposed by the Breach Notification Rule. The proposed update to the Security Rule would require Business Associates to report security incidents within 24 hours of discovery.
Regulatory monitoring and anticipation are, finally, key differentiating competencies. HIPAA is evolving: the new requirements proposed for 2025 (mandatory MFA, systematic encryption, formalized penetration testing, complete asset inventory) will significantly reinforce technical obligations. Cybersecurity experts who anticipate these changes enable their organizations to adapt proactively and turn regulatory pressure into a competitive advantage.
HIPAA Compliance Best Practices: The Operational Guide for Cybersecurity Experts
Achieving HIPAA compliance is not a matter of checking boxes on a checklist. It is a continuous, iterative process that draws on technical, organizational, and legal expertise. Here are the fundamental practices that every cybersecurity expert must master in order to effectively support an organization subject to HIPAA.
Conducting and Maintaining a Comprehensive Risk Analysis
The risk analysis is the cornerstone of any effort to comply with HIPAA. The OCR considers it the most frequently neglected requirement during its audits. Contrary to what one might assume, HIPAA does not prescribe a single methodology: what matters is that the analysis is documented, reproducible, and regularly updated.
A HIPAA-compliant risk analysis must cover the organization's entire ePHI footprint: identifying all data sources (systems, applications, data flows), mapping threats and vulnerabilities, assessing the likelihood and impact of each scenario, and defining a prioritized treatment plan. It must be renewed with every significant change to the information system (cloud migration, new tool deployment, merger or acquisition) — not only during regulatory audits.
Implementing Strict Access Controls and Rigorous Identity Management
Identity and Access Management (IAM) is one of the disciplines most directly impacted by the HIPAA Security Rule. The access controls required by HIPAA rest on several non-negotiable pillars: unique identifiers for every user (generic or shared credentials are explicitly prohibited), the least privilege principle applied to all roles, multi-factor authentication for all access to ePHI (mandatory under the proposed 2025 update), and immediate revocation of rights upon an employee's departure or role change.
Systematic logging of all ePHI access is also mandatory: audit logs must be retained, protected against tampering, and regularly reviewed to detect anomalous behavior.
Protecting Data Through Encryption and Network Segmentation
Encryption of electronic protected health information (ePHI) is today treated as a de facto requirement by the OCR, even though the current HIPAA Security Rule still classifies it as "addressable." The update proposed for January 2025 is expected to make it fully mandatory. Cybersecurity experts must anticipate this change and implement end-to-end encryption for data both in transit (TLS 1.2 minimum) and at rest (AES-256 recommended).
Network segmentation is another key measure: systems hosting ePHI must be isolated from the rest of the network and from uncontrolled internet access. This approach significantly reduces the attack surface and limits the blast radius of a potential compromise.
Rigorously Managing Third Parties and Business Associates
Every external vendor accessing ePHI must be governed by a properly executed Business Associate Agreement (BAA). But compliance does not end with signing the contract: cybersecurity experts must ensure that BAAs are up to date, that vendors are subject to regular security assessments (vendor risk assessments), and that the access granted is documented and limited to what is strictly necessary.
The proposed 2025 HIPAA update would require Business Associates to report security incidents within 24 hours, a development that compels organizations to establish clear, operational incident communication channels with all of their vendors.
Training Teams and Testing Incident Response Procedures
The human dimension is often the weakest link in HIPAA compliance. The HIPAA Privacy Rule mandates documented training for all employees with access to PHI. For cybersecurity experts, this means designing awareness programs tailored to different staff profiles (clinical, administrative, and IT personnel), with specific modules covering phishing detection, workstation management, and the procedures to follow when a suspected incident occurs.
Incident response plans must be regularly tested through simulation exercises (tabletop exercises). These tests verify that the organization is able to quickly qualify an incident (does it constitute a HIPAA breach?), activate the appropriate escalation paths, and meet the notification deadlines imposed by the Breach Notification Rule.

HIPAA and Artificial Intelligence: Compliance Challenges in the Age of AI
Artificial intelligence is rapidly transforming the healthcare sector: medical imaging diagnostic tools, clinical documentation assistants, patient chatbots, predictive algorithms, triage models... These promising technologies raise unprecedented questions about the protection of protected health information (PHI), and the HIPAA framework, designed in a pre-AI era, must evolve to address them.
AI in Healthcare: A New Risk Perimeter for ePHI
As soon as an artificial intelligence system creates, receives, maintains, or transmits ePHI — whether it is a diagnostic model trained on patient records, a clinical transcription tool, or a generative medical assistant — it falls within the scope of the HIPAA Security Rule. In practice, this means the same requirements apply: data encryption, access controls, logging, and risk analysis.
The update proposed by HHS in January 2025 goes further by introducing, for the first time, provisions explicitly addressing AI. Regulated entities will be required to include in their technology asset inventory all AI software that creates, receives, maintains, or transmits ePHI, including when ePHI is used to train the model.
Specific Challenges Posed by AI to HIPAA Compliance
Training models on health data is a first area of significant complexity. If an AI model is trained on identifiable PHI, that data must be de-identified in accordance with HHS-approved methods (Safe Harbor or Expert Determination) before use. If de-identification is not feasible, the entire training infrastructure must satisfy the HIPAA Security Rule. Violations in this phase, which is often poorly monitored, can go undetected for extended periods.
The minimum necessary standard also poses a major challenge for AI systems. AI systems are technically designed to perform best with comprehensive datasets, which creates direct tension with the HIPAA requirement that limits access to only the PHI strictly necessary for the intended purpose. Organizations must implement technical controls to limit data exposure to models based on their actual use case.
Third-party AI vendors represent another critical area of vigilance. Using non-compliant AI APIs or cloud services, even unintentionally, can constitute a serious HIPAA violation. Any external vendor offering AI services that process PHI must be HIPAA-compliant and sign a Business Associate Agreement (BAA). Cybersecurity experts must therefore integrate HIPAA compliance evaluation into their vendor selection and qualification processes.
AI-powered cyberattacks represent an emerging threat directly linked to the expansion of AI. So-called "offensive AI" attacks use code capable of mutating as it learns about its environment, making it harder to detect and neutralize. Faced with these new threats, traditional defenses are showing their limits, and healthcare organizations must invest in behavioral detection solutions and Zero Trust architectures.
The Future of HIPAA: Toward a Regulatory Framework Fit for the Digital Age
The proposed update to the HIPAA Security Rule in January 2025, the first major revision since 2013, is the clearest signal to date that U.S. lawmakers are taking stock of the challenges posed by the digital transformation of the healthcare sector. For organizations deploying AI in healthcare, these changes are particularly significant: they eliminate the distinction between required and addressable safeguards and introduce stricter expectations around risk management, encryption, and resilience.
Beyond this update, several regulatory trends are shaping the future of HIPAA: the possible emergence of a unified U.S. federal data privacy law (which could complement or modify the HIPAA framework), strengthened obligations around algorithmic transparency (informing patients when AI systems are involved in decisions affecting them), and growing international regulatory collaboration, notably between HHS and European data protection authorities under the GDPR.
For cybersecurity experts, this regulatory evolution represents both a challenge (staying current with a rapidly shifting framework) and an opportunity: positioning themselves as strategic partners capable of guiding healthcare organizations through a secure digital transformation.
HIPAA: A Demanding Standard That Calls for Equal Expertise
HIPAA is more than a regulatory compliance framework: it is a high security standard that reflects the exceptional value of health data and the gravity of the consequences when a violation occurs. For cybersecurity professionals, mastering the HIPAA Privacy Rule, the HIPAA Security Rule, the Breach Notification Rule, and the developments brought by the HITECH Act has become a fundamental competency for any engagement involving the American healthcare system.
The complexity of this framework — bridging technical, legal, and organizational obligations, third-party management, incident response, and risk quantification — calls for a structured, tool-supported approach.
This is the mission C-Risk has set for itself: helping organizations understand, quantify, and reduce their cyber risk exposure, including in the most heavily regulated environments such as those subject to HIPAA. Through an approach grounded in Cyber Risk Quantification (CRQ), C-Risk guides its clients toward informed decision-making, optimal allocation of security resources, and concrete demonstration of the value of their cybersecurity investments — all key levers for meeting the requirements of HHS and OCR with rigor and efficiency.
What is HIPAA?
HIPAA (Health Insurance Portability and Accountability Act) is a U.S. federal law enacted in 1996. It establishes national standards to protect the privacy and security of patients' health data. It applies to all actors in the American healthcare system that create, receive, transmit, or store protected health information (PHI), as well as to their external service providers. Non-compliance exposes organizations to financial penalties that can exceed $2 million per violation.
Who does HIPAA apply to?
HIPAA applies to two categories of actors. First, covered entities: healthcare providers (physicians, hospitals, pharmacies), health plans, and healthcare clearinghouses. Second, business associates: any external vendor handling health data on behalf of a covered entity, whether a cloud hosting provider, a medical software publisher, or a cybersecurity firm. Business associates are required to sign a Business Associate Agreement (BAA).
What is the difference between GDPR and HIPAA?
The GDPR and HIPAA share similar objectives — protecting personal and health data — but their scope differs. The GDPR is a European regulation that applies to all personal data, across all sectors, whenever it concerns EU residents. HIPAA is a U.S. law that applies exclusively to health data within the American healthcare system. HIPAA imposes highly specific sectoral requirements (encryption, audit logging, BAA), while the GDPR takes a broader, principle-based approach centered on data minimization and consent.
Related articles
Read more on cyber risk, ransomware attacks, regulatory compliance and cybersecurity.

.svg)
