How to Create a Defensible Third-Party Risk Management Decision Framework
As organizations grow more dependent on their extended enterprise, the financial impact of third-party cyber incidents rises sharply. Regulators, boards, and insurers now expect decisions that are consistent, traceable, and fully defensible. This article covers how to build a third-party risk management decision framework that meets that standard, from establishing objective vendor criteria to integrating FAIR-based quantification and scaling the process operationally.
- Replacing qualitative judgements with objective, financially grounded criteria enables consistent vendor decisions that hold up under regulatory and audit scrutiny
- FAIR-based cyber risk quantification allows organizations to evaluate treatment options on a cost-benefit basis and align decisions with risk appetite using financial thresholds
- Documented decision rationale is a regulatory expectation under DORA, NIST, and ISO 27000, and a practical requirement for governance bodies and executive leadership
- A scalable decision framework depends on a TPRM platform that unifies vendor data, control evidence, and risk signals to make the framework operational rather than theoretical
Building a Defensible Third-Party Risk Decision Framework
A defensible third-party risk management decision framework depends on decisions that are consistent, defensible, and evidence-based. To achieve this, organizations must transition from ad-hoc vendor evaluations to a structured framework that clarifies how decisions are made and why specific risk treatments are chosen.
Establishing Clear, Objective Criteria for Vendor Decisions
A defensible framework begins with replacing broad qualitative judgements with objective data that can put third-party vendors in context. Core elements typically include:
- Risk exposure: inherent risk level, control effectiveness, and residual risk
- Business criticality: vendor access to data, systems or revenue-generating activities
- Data sensitivity: classification, regulatory status, volume, and retention
- Regulatory requirements: sector-specific constraints that may elevate obligations
- Financial loss: measured using FAIR-based quantitative methods
Rather than using only qualitative analysis, the integration of objective data ensures that decisions consider the financial impact and other evidence-based KPIs and KRIs of risk management actions. Objective data allow cross-functional stakeholders to compare risk across the enterprise to build consensus, reducing bias and disagreement.
Risk Quantification and Decision Support
Cyber Risk Quantification (CRQ) and the FAIR™ model strengthen the decision-making process. FAIR provides a structured method for decomposing third-party risk into measurable factors, such as event frequency, control strength, and loss magnitude. Instead of relying on subjective “high/medium/low” labels, FAIR quantifies risk in financial terms, enabling apples-to-apples comparisons across vendors, service types, and treatment options.
CRQ reduces uncertainty by replacing intuition with calibrated estimates based on evidence, available data, and documented assumptions. This level of analytical rigor supports decisions that can withstand regulatory, audit, or executive scrutiny. It also empowers organizations to:
- Evaluate treatment options on a cost-benefit basis, comparing expected loss reduction to the cost of controls, monitoring, insurance, or vendor substitution
- Align decisions with risk appetite, using financial thresholds instead of ambiguous qualitative scores
- Prioritize third-party risks consistently, focusing resources where they create the greatest reduction in expected loss
By integrating FAIR into third-party decision frameworks, organizations gain a defensible, financially grounded foundation for third-party risk acceptance, mitigation or transfer, and when required risk avoidance.
Compliance and Governance Support Decision Rationale
Strong governance in third-party risk management depends on clear, documented decision rationale. Governance bodies, auditors, and regulators expect organizations to show how vendor-related decisions were made.
- DORA (EU’s Digital Operational Resilience Act) requires financial entities to document their decision-making processes and rationale for ICT third-party arrangements, including evidence of due diligence, risk assessment, and treatment choices.
- NIST SP 800-53, NIST CSF expects organizations to maintain documented justification for risk acceptance, including the criteria used, alternative treatments considered, and the basis for approving vendors with residual risk.
- ISO 27000 family emphasizes documented decision criteria and justification, ensuring that supplier selection, onboarding, and risk treatments follow defined, repeatable processes.
Documented decision rationale strengthens the third-party decision framework:
- transparency into why a vendor was approved or escalated
- auditability of risk acceptance and treatment decisions
- consistent application of decision criteria across teams
- clear alignment between business needs, risk posture, and regulatory obligations
Applying Decision Principles to a Third-Party Risk Decision Framework
Decision-Making Principles That Support Defensible Third-Party Risk Decisions
You can design a defensible third-party decision framework based on your organization’s needs. Before looking at TPRM-specific models, it is useful to consider how other organizations think about decision quality in general.
Coinbase’s “Good vs. Bad Decision Making” model is one such example. Although it is not a third-party risk framework, it does illustrate behaviors that lead to better decisions in any domain:
- Truth-seeking
- Defining who the decision-maker is
- Inclusive information sharing rather than siloed input
- Minimizing unconscious bias
- Documenting stakeholders’ roles and input
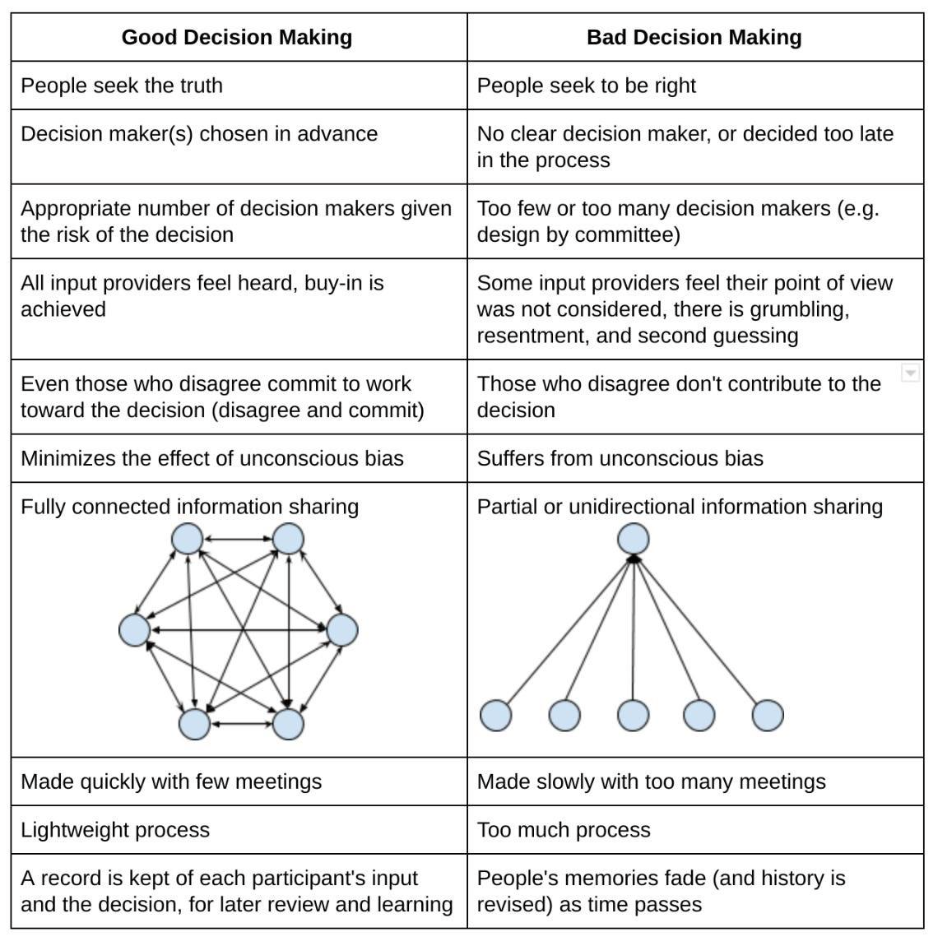
These principles are valuable because TPRM decisions frequently involve multiple stakeholders, competing priorities, and trade-offs between security, cost, and operational continuity. A strong TPRM framework should reflect the same discipline and objectivity.
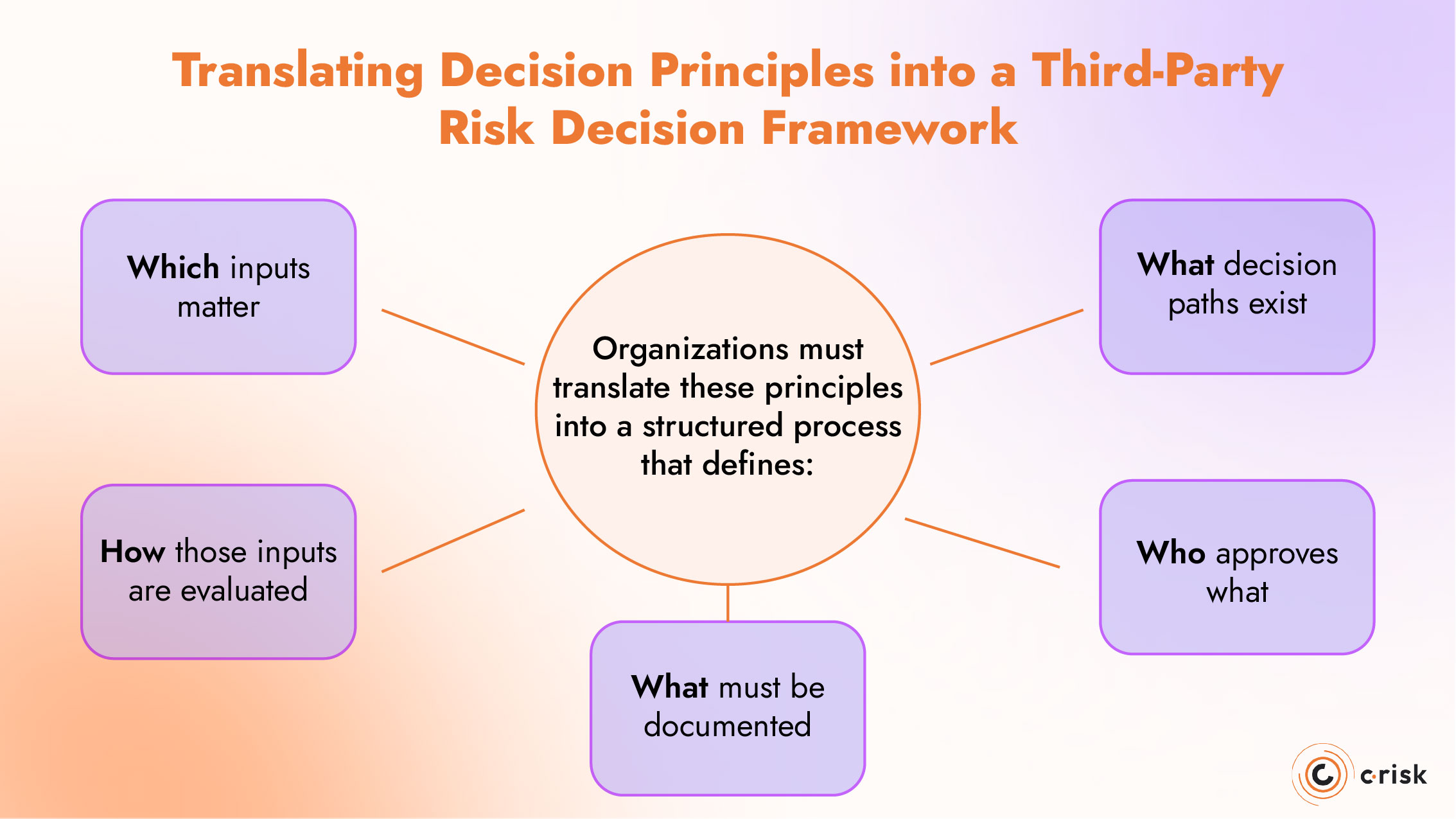
Translating Decision Principles into a Third-Party Risk Decision Framework
To make decisions defensible in a third-party context, organizations must translate these principles into a structured process that defines:
- Which inputs matter: data sensitivity, system access, business criticality
- How those inputs are evaluated: evidence, quantification, control reviews
- What decision paths exist: accept, mitigate, transfer, avoid
- Who approves what: risk owners, business leaders, governance committees
- What must be documented: rationale, evidence, quantification assumptions
This begins with building and maintaining a prioritized vendor inventory, developed during onboarding:
- Could this vendor materially impact the business in a data breach, outage, or operational incident?
- Does this vendor directly support revenue-generating or critical processes?
Next, organizations develop a risk universe and scenario library for the third parties that matter most:
- What are the most plausible and impactful scenarios, given the vendor’s role and access?
Once risk scenarios are defined and quantified, decisions become clearer:
- Given the residual risk and financial impact, should we accept, mitigate, avoid, or transfer the risk?
When presenting recommendations to leadership, risk teams should speak in financial and probabilistic terms, not ambiguous categories like “high/medium/low.”
This shifts discussions from subjective assessments to comparative business logic, making decisions easier to explain and defend.
Strengthening Your Third-Party Risk Decision Framework with FAIR™ Quantification
Using FAIR to Quantify Your Return on Security Investment
Quantification sharpens the decision process by expressing exposure and treatment benefits in financial terms, allowing security and business leaders to compare options on equal footing. The example below illustrates how FAIR brings data-driven evidence to third-party risk decisions.
FAIR scenario:
A marketing automation vendor handles your customer data and integrates with core engagement systems. An external threat actor compromises a vendor’s valid account credentials to gain unauthorized access to your customer records, exploiting your weak monitoring controls; this results in a breach of sensitive data.
Key inputs:
- Data sensitivity: PII and payment information
- Business criticality: Direct link to revenue-generating operations
- Control assessment: SSO enforced; monitoring is weak
- Quantified residual risk:
- Loss Magnitude (LM): €600k–€1.4M
- Expected Annual Loss (EAL): ~€300k
Treatment options:
- Acceptance:
- No cost
- EAL remains €300k
- ROSI: €0
- Mitigation:
- Strengthen logging & monitoring controls
- Cost: ~€60k/year
- Estimated EAL reduction: €220k
- ROSI: €160k
- Transfer (insurance):
- Cyber rider extending to vendor incidents: €90k/year
- EAL reduction: €0–€100k
- ROSI: marginal
- Avoidance (off-boarding):
- Finding new vendor
- Cost: €600k
- Risk reduction: 100%
- Net cost far exceeds benefit
Based on the numbers, one decision stands out as defensible: mitigation. The cost of strengthening monitoring delivers a clear return on security investment. If your risk appetite is €300k, reducing exposure by €220k creates capacity to take on new initiatives that may introduce additional risk. The goal of risk management is not to drive exposure to zero, but to bring it within appetite so the business can grow confidently.
Scaling Your Decision Framework for Third-Party Risk Management
Operationalize the Framework with a Data-Driven Third-Party Platform
A scalable decision framework depends on a TPRM platform capable of unifying vendor information and continuously monitoring the suppliers that matter most. When vendor data, control evidence, and risk signals from across the enterprise are brought together in one place, leadership gains a clear, current view of the organization’s third-party threat landscape and the attack surface they are accountable for managing. This integration transforms the decision framework into an operational capability.
How C-Risk Helps You Implement Quantitative, Scalable Third-Party Risk Management
C-Risk helps organizations operationalize their third-party cyber risk programs. We combine quantitative risk methods, platform expertise, and deep governance experience to ensure your TPRM strategy is aligned with your business objectives.
We support you by:
- Implementing quantitative risk methods using FAIR to model cyber risk in financial terms and compare treatment options
- Deploying and integrating a TPRM platform, including SAFE TPRM, to unify vendor data and risk signals for data-driven risk management
- Training teams to communicate risk in financial and probabilistic terms, improving leadership engagement and decision quality
- Providing ongoing advisory support for CRQ risk assessments, risk and security teams, and operationalizing your program as your vendor ecosystem grows
