Quantification of Third-Party Risks: Using Objective Data for Defendable Risk Management
Traditional third-party risk management still leans heavily on self-reported questionnaires and scoring templates designed for compliance. Without a clear understanding of which digital assets, processes, or revenue-critical systems each supplier touches, risk teams are blind to which partners could disrupt operations. And in an interconnected supply chain, the riskiest vendor could be easily overlooked. This isn’t theoretical: KPMG reports that 73% of organizations experienced at least one third-party incident in the past three years.
In this article, we show how a quantitative approach using objective data helps better map dependencies, quantify financial exposure, and build a more resilient third-party risk program.
- Qualitative ratings often group unlike suppliers together, making it difficult to distinguish critical vendors from those with limited impact
- Mapping suppliers to the systems, data, and business processes they support reveals where a disruption could affect revenue, customers, or regulated functions
- Financial quantification measures third-party risk through two variables: the likelihood of a loss event and the scale of potential financial impact
- CTI and telemetry provide objective indicators of supplier risk
- Continuous monitoring reduces reliance on point-in-time questionnaires and highlights material changes in vendor posture as they occur
Understanding the Stakes of Third-Party Risk Quantification
Where Qualitative Approaches Excel and Where Quantification Adds Value
Third-party risk management has long relied on qualitative tools—scoring models, expert judgment, and color-coded matrices often tied to contract size or perceived criticality. These methods remain essential: they provide rapid triage, enable collaboration, and offer the contextual nuance that no model can fully replicate. They help risk teams identify areas of concern efficiently.
But qualitative methods alone have limits. They support compliance, yet they rarely give decision-makers a defensible, comparable view of exposure. Two vendors may both be labeled “high risk,” but the reality behind those labels can be dramatically different: one might cause a brief service disruption, while the other could halt operations and trigger millions in losses.
It’s no surprise that only 19% of ERM teams believe they effectively prioritize risk (Gartner), because qualitative ratings rarely differentiate between material risk and administrative noise. Most organizations still evaluate suppliers in isolation, detached from their internal business processes, data, and revenue streams those suppliers actually support. This creates a false sense of precision: many scores, but little insight into the impact of an incident.
Without linking each vendor to the “thing of value” they enable (i.e., systems, data, or operational capabilities) risk teams cannot clearly explain why one supplier requires new controls or oversight over another.
This lack of comparability has consequences:
- everything feels “high risk,” so nothing gets prioritized
- budgets are allocated based on fear or compliance pressure, not exposure
- risk communication with leadership is storytelling rather than business-aligned reporting
Quantification fills this gap. By translating qualitative assessments into financially grounded insights, it provides the rigor necessary for defensible prioritization. It transforms supplier risk conversations from “red, amber, green” to investment-ready guidance aligned with business impact.
The Business Imperative for Financial Measurement in TPRM
Organizations increasingly depend on complex digital ecosystems and outsourced services. A single supplier failure can cascade across operations, customers, and revenue. Recent incidents have made these interdependencies highly visible. In this environment, decision-makers require more than color-coded assessments. They need a measurement framework that clearly links vendor failures to business impact.
Quantification provides this bridge. By expressing risk in financial terms, it enables leadership to:
- compare exposures across suppliers, business units, or geographies
- measure the ROSI of mitigation investments
- justify budget allocations with objective data
- comply with evolving regulatory expectations around operational resilience
This shift elevates third-party risk from a compliance obligation to a strategic enabler. By combining qualitative insights with quantitative analysis, risk teams can move beyond nominal risk ratings and present defensible, business-aligned recommendations.
DDRM Methodology and Vendor Risk
The DDRM Approach Applied to Third-Party Risk Management
DDRM is a decision-making discipline to minimize future losses within the organization’s risk tolerance and capacity levels as cost-effectively as possible, utilizing cyber risk quantification principles and objective data. It helps organizations build a structured, evidence-based approach that breaks down silos and drives cross-functional alignment.
According to Gartner, enterprises use 400+ SaaS apps, but have visibility into only about 30% of them. Who is responsible for the management of them?
In practice, DDRM brings together leaders from across the enterprise:
- Procurement and legal teams
- Cybersecurity and IT operations
- Risk and compliance functions
- Business owners and executives
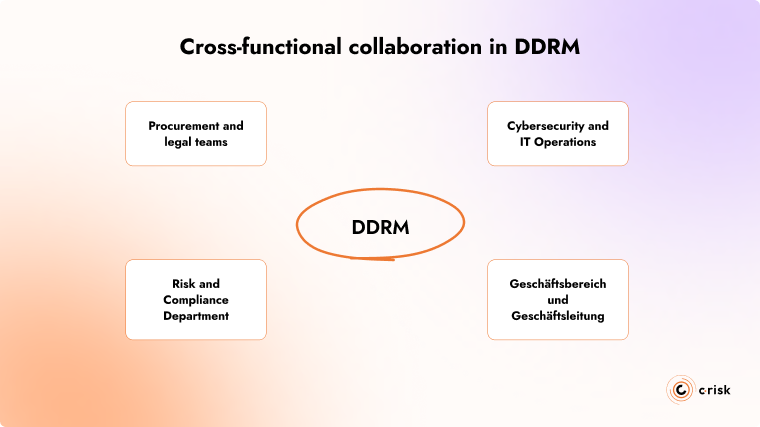
This collaboration ensures that third-party risk decisions are not made in isolation but reflect the broader ecosystem of processes, assets, and dependencies the supplier supports.
Data-Informed Methodology for Quantifying Third-Party Risks
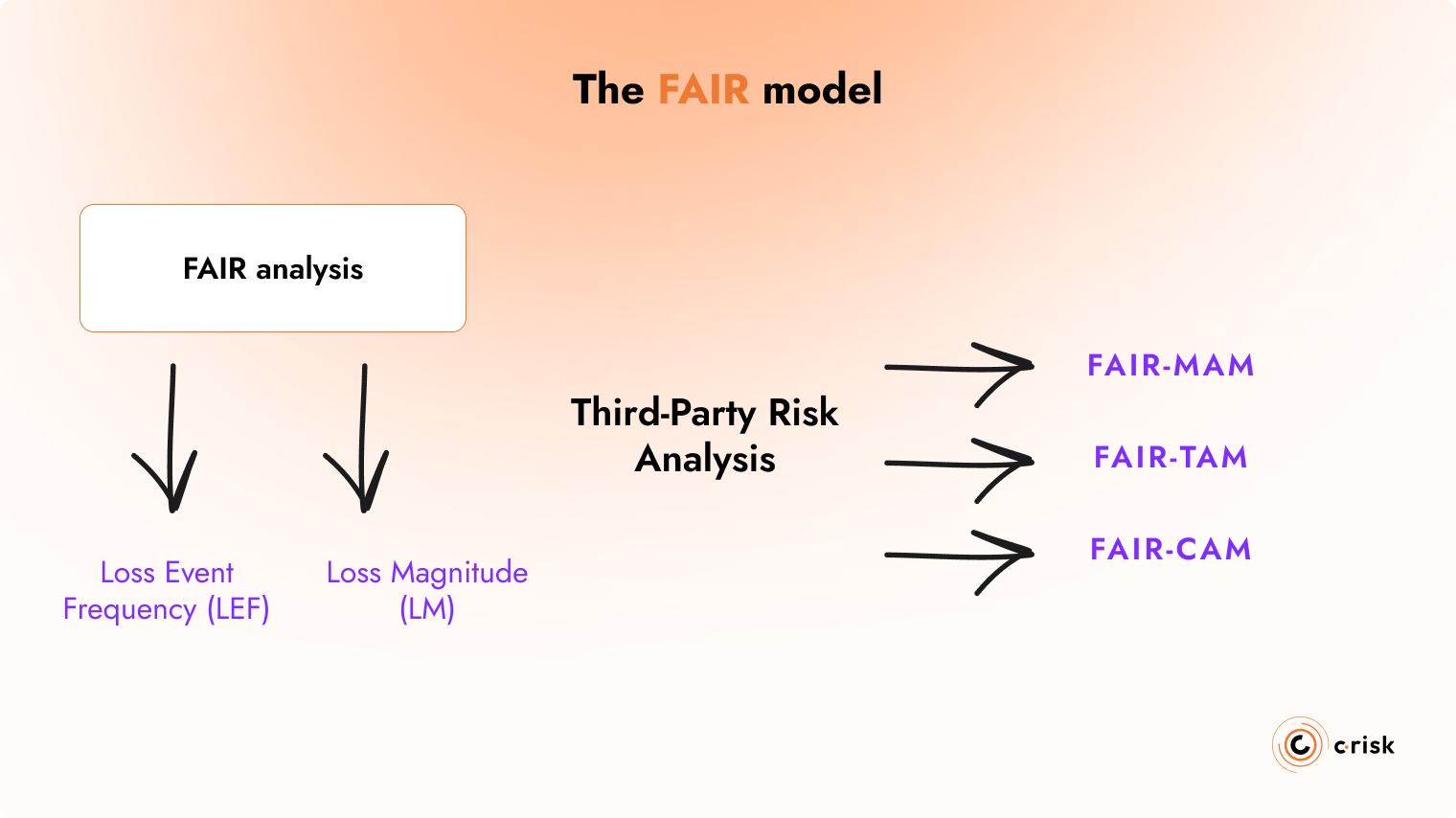
The DDRM approach uses the FAIR (Factor Analysis of Information Risk) model, which provides a structured, industry-standard method for translating third-party risk into financial terms. Its strength lies in breaking risk into measurable components.
According to the FAIR taxonomy, risk is measured by how often a loss event is likely to occur and how costly it would be.
FAIR analysis will tell you two factors for your risk scenarios:
- Loss Event Frequency (LEF):
How often a supplier-related loss event could plausibly occur, based on incident history, outside-in telemetry, threat activity, and control strength.
- Loss Magnitude (LM):
The financial impact of an event, covering operational downtime, revenue disruption, regulatory penalties, replacement service costs, customer impact, etc.
For third-party analysis, FAIR has also developed an extensions to help better measure materiality, third-party risk and controls. These are FAIR-MAM, FAIR-TAM and FAIR-CAM.
Operationalizing Third-Party Risk Through Automation and Continuous Monitoring
As organizations grow more dependent on large ecosystems of service providers, manual third-party risk processes simply cannot keep pace. Point-in-time assessments, spreadsheets, and questionnaire-based reviews offer useful context, but they fail to reflect how quickly a supplier’s risk posture can change. To manage hundreds or thousands of critical vendors effectively, automation becomes essential.
A FAIR-based third-party risk management platform enables organizations to operationalize their third-party risk workflows. Instead of relying on self-reported questionnaires, automated systems continuously collect signals from internal and external sources: cybersecurity telemetry, threat intelligence, leaked-credential monitoring, configuration exposures, financial health indicators, service availability metrics, and changes in business criticality. This creates a dynamic, real-time picture of supplier risk.
Automation also eliminates the manual effort involved in consolidating and interpreting third-party data. Quantitative models can be updated instantly as new evidence emerges to adjust likelihood, recalculate financial exposure, and trigger alerts when a supplier’s risk profile shifts.
What this looks like in practice:
- A central dashboard showing updated risk metrics across a portfolio suppliers
- Automatic recalculation of exposure when controls weaken or incidents occur
- Integrated Cyber Threat Intelligence (CTI) that highlights relevant campaigns targeting specific vendors or services
- Prioritized work queues for remediation efforts, based on financial impact rather than generic severity labels
- Notifications when a critical vendor’s posture changes or new vulnerabilities change control efficacy
With this risk teams are able to focus on analysis and decision-making. Business leaders gain visibility into which suppliers truly matter and why. Most importantly, you can respond to emerging risks before they turn into costly incidents.
Practical Implementation of DDRM Methods Within a TPRM Program
What does this mean for your organization?
Every organization will manage their third-party risk within their business context. Implementing a quantitative approach needs to match your maturity, resources, and risk appetite. A small team supporting a handful of critical vendors needs a lighter approach than a global enterprise with thousands.
The key is focus on what’s important. Start by identifying the suppliers tied to revenue, regulated processes, or customer-facing operations that where quantitative analysis can move the needle. As the program matures, this scope can expand.
Over time, inputs can be refined, with better estimates, more accurate results, and operational metrics that can enable decisions at every level and across business functions.
The result is a right-sized, defensible quantification approach that fits your organization’s context and produces insights you can act on.
Investment Prioritization Based on Quantitative Analysis
Once risk is expressed in financial terms, it becomes much easier to decide where to focus effort. Quantification gives teams a clear way to compare options and understand which actions reduce the most exposure for the least cost. Instead of debating qualitative ratings, decisions can be guided by simple, defensible cost–benefit analysis.
This could takes the form of a basic risk-reduction matrix:
- how much annualized financial risk a supplier carries
- how much each mitigation option would cost
- how much of that risk it would reduce (likelihood and impact)
Even small insights can change how controls are implemented.
Example:
A vendor shows €1M in annualized risk. Three potential actions are evaluated:
- Improve authentication controls — €40k cost → €100k reduction
- Add service redundancy — €150k cost → €800k reduction
- Renegotiate SLA — €20k cost → €150k reduction
Quantification naturally underscores the cost-benefit for each scenario: redundancy delivers the biggest reduction, while the SLA change is a quick win. Authentication is still useful but no longer competes for top priority. Based on your business context, your decision may differ.
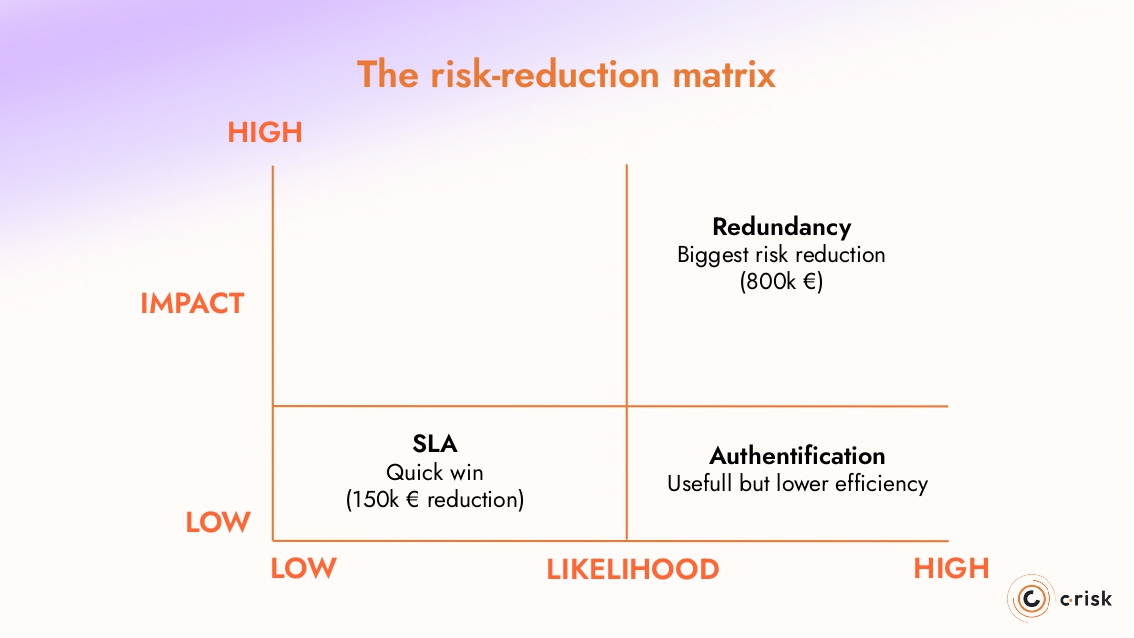
This type of analysis also helps teams sequence work when time and resources are limited. It creates a logical order: what to address now, what can wait, and what no longer justifies investment.
ROI and Executive Value of Quantifying Third-Party Risks
Measuring Effectiveness and Demonstrating Financial Value
Once a third-party risk program is quantified, it becomes much easier to prove whether it is working. Instead of counting questionnaires completed or vendors “assessed,” you can track how much risk has actually been reduced and at what cost.
Over the long term, key performance and risk indicators provide a clear picture of security performance: a steady decline in projected annualized loss, fewer material incidents, and lower average incident cost. more risk managed, per euro invested.
Organizations that adopt quantitative methods consistently report lower breach costs, faster containment, and more efficient use of their security budget. When third-party exposure is expressed in financial terms, the impact of each control, remediation plan, or renegotiated SLA can be measured against the risk it removes.
Executive Communication and Board Reporting
Quantification makes third-party risk far easier to communicate at the executive level. Boards need a clear understanding of how third-party risk management is performing and the actions required to improve resilience.
By expressing exposure in financial terms, reporting can focus on what matters:
- where the largest concentrations of vendor-related risk sit
- how that exposure is changing over time
- which mitigations have delivered measurable reduction
- what controls will bring the greatest risk reduction
This gives leadership a straightforward way to compare risk reduction strategies, understand trade-offs, and decide where investment is most effective. It also strengthens scenario discussions by showing the estimated financial impact of realistic disruptions rather than abstract “high-risk” labels.
Financial metrics give everyone the same frame of reference. When third-party risk is translated into business terms, conversations become more focused, decisions become easier, and oversight becomes more effective.
How C-Risk Supports You in Quantifying Third-Party Risks
C-Risk can help your organization bring structure, clarity, and defensibility to your third-party risk program. Our approach is grounded in DDRM principles and industry-standard quantification using the FAIR methodology, enabling teams to understand supplier dependencies, measure financial exposure, and make informed decisions.
We support you in:
- Building a tailored DDRM roadmap for your third-party ecosystem
- Quantifying vendor risks using FAIR-based methods that reflect your business context
- Operationalizing assessments through automated data ingestion and continuous monitoring using the SAFE TPRM platform
- Turning results into executive-ready reporting, aligned with board expectations
- Developing your internal capability, from training teams to establishing a sustainable operating model
Whether you’re starting with a handful of critical suppliers or scaling quantification across thousands, C-Risk provides the structure, expertise, and tools to transform how you manage third-party risk.
