Third-Party Vendor Management: How to Gain a Unified View of Your Extended Enterprise Ecosystem
In today’s hyper-connected organizations, third-party vendor management has become both indispensable and increasingly difficult to control. Every department collaborates with external providers, from SaaS platforms to operational support. Despite this growing dependency, organizations still operate with a fragmented, siloed understanding of their extended enterprise.
A unified view is no longer a “nice to have.” Security and risk teams cannot prioritize or protect what they cannot see. In this article, we show how you can gain that unified view and support a more strategic vendor management program.
- Most organizations lack a complete view of their third-party ecosystem, and the gaps usually sit where no single function has ownership
- Shadow IT and decentralized implementation introduce risk without third-party oversight
- A complete vendor inventory is achievable under a shared third-party governance model
- Prioritization begins with understanding vendor criticality: who has access to your data, your systems, and the parts of the value chains that generate revenue
- Automation can help operationalize manual processes and track results
Understanding What's Missing in You Third-Party Vendor Management
The Rising Complexity of Vendor Relationships and the Risks They Create
Today’s businesses operate through networks of third-party providers because it lets them scale quickly, access specialized expertise, and focus their internal resources where they create the most value. However, as the numbers grow, deep-dive assessments often reveal a far more complex ecosystem beneath the surface.
The most striking evidence comes from the 2023 Cyentia Institute RiskRecon Nth-Party report, which shows that the third-party relationships also exist at the 4th- and 5th-party level. While an organization may work directly with a few dozen third parties, indirectly, you could be exposed to x14 more vendors through subcontractors and service dependencies. This amplification effect dramatically expands your attack surface beyond what most vendor management programs account for.
When this combines with the siloed way many organizations manage their vendors, the result is an ecosystem where a significant portion of third-party cyber risk remains out of sight. You can’t evaluate or prioritize risks you don’t know exist. And yet these indirect relationships can have an impact on your operations in the event of a cyberattack.
Shadow IT as a Blind Spot in Vendor Management
Shadow IT is another challenge when it comes to managing third-party risk. Shadow IT is any tool, application, or service used by employees without going through the organization’s formal approval process. Employees adopt web tools outside of normal chain of procurement because it helps them work faster or collaborate more easily. While employees integrate these tools in good faith, they introduce new vendors into their environment without oversight that a mature vendor management program relies on.
Kaspersky’s 2023 Human Factor 360 report highlights this reality. The study found that 11% of cyber incidents involved unapproved applications or services introduced by employees. Most of these were unintended consequences of remote work and personal device usage. The pattern is consistent across industries. This reinforces the idea that the core challenge is building a clear, shared process for evaluating and authorizing new tools.
Shadow IT is not just a technology problem. Strong cyber governance helps align teams around shared processes and ensures that new tools and vendors are inventoried and assessed before being brought online.
Laying the Foundations of Effective Third-Party Vendor Management
Designing a Unified Vendor Inventory
Building an accurate view of your third-party ecosystem begins with a unified vendor repository. No single function has the full picture: Procurement knows the contracts, IT manages access and integrations, Security handles assessments, Finance sees payments, and Legal understands the obligations. A cross-functional approach is the only way to assemble a reliable foundation for vendor management.
A 2023 Cyentia Institute analysis found that organizations using four or more data sources to build their vendor inventories identified up to twice as many materially relevant vendors compared with those relying on a single source. As cooperation improves, you will be better equipped to manage your attack surface.
Overcoming Cross-Functional Complexity
Third-party vendor management concerns Procurement, Legal, Business, IT, InfoSec, and every business unit. And when these functions operate in silos, they unintentionally make it harder to maintain an accurate view of the vendor ecosystem and even harder to manage cyber risk effectively.
Cross-functional collaboration is best addressed with a strong third-party governance model that defines:
· Who owns each part of the third-party/vendor lifecycle — onboarding, evidence collection, access, assessments, monitoring, renewal, and offboarding
· How decisions are validated — what triggers a security review, what requires legal approval, workflow
· Which shared tools and workflows support collaboration — third-party risk management tool, unified risk scoring, accessible across functions
· What constitutes “criticality” — a shared definition that aligns business impact, communication of risk appetite, and regulatory obligations
With a complete view of your third parties, another layer of insight becomes possible—one that is often overlooked and allows risk-based prioritization. Third parties process sensitive data, integrate with internal systems, deliver components of core business processes, or support essential parts of the value chain. To manage risk effectively, it becomes necessary to understand exactly where each vendor fits: what data they handle, which systems they access, what operational functions depend on them, and how their failure would affect the business.
Turning Visibility Into Actionable Vendor Intelligence
Enriching Vendor Data with Risk-Based Prioritization
Without a single risk assessment, it is possible to establish vendors in a way that allows initial risk-based prioritization. There are three key questions that you can answer even without third-party input.
· Does the vendor access or process critical or sensitive data, such as personally identifiable information (PII), protected health information (PHI) or intellectual property (IP)?
· Does the vendor access your networks or IT architecture?
· Does the vendor access or manage your revenue-generating activities?
These questions allow you to establish the criticality of vendors within your third-party ecosystem.
Why is a risk-based inventory of vendor access so important to your third-party strategy?
The access a vendor has to your critical assets and where it operates along your value chains allows for a high-level risk-based triage of vendors. Knowing who has access to what data allows you to manage your attack surface more effectively.
How is the traditional approach to third-party risk management different to a data-driven approach?
While traditional third-party vendor management approach does inventory third parties and perform due diligence, the risk assessments are focused on vendors depending on business and contract questionnaires. They will triage based on the size of the contract or the revenue. Contract size doesn’t correlate to risk.
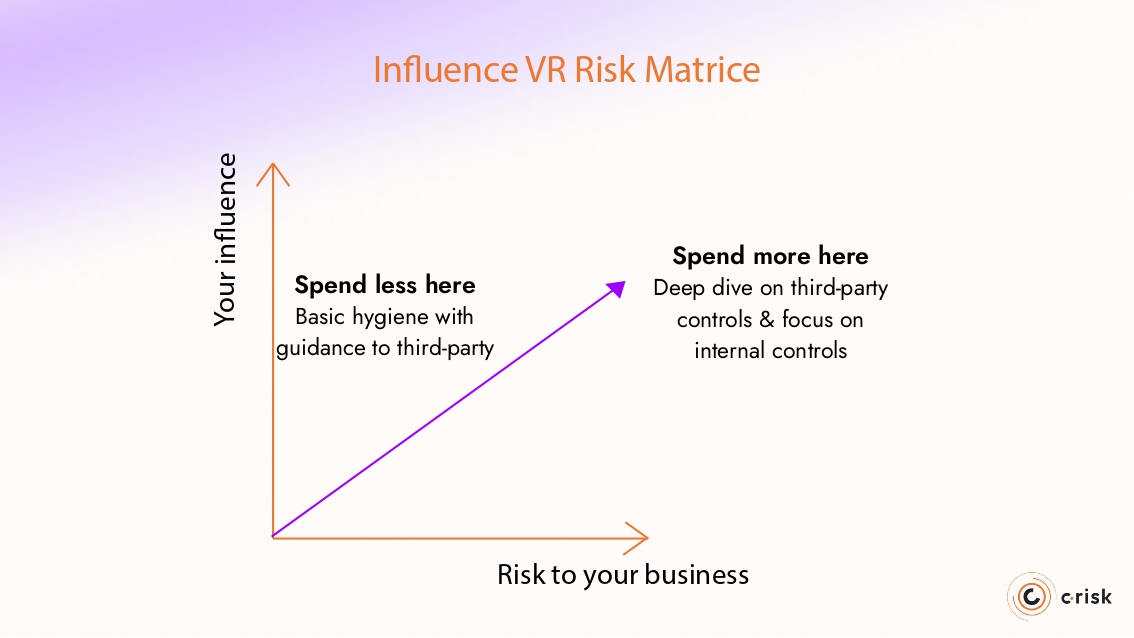
Guiding Collaboration Through an Influence-vs-Risk Model
Prioritization is most effective when it also guides how teams work together. Vendor risk cannot be assessed or managed by one function alone. A practical way to coordinate effort is to map each vendor against two dimensions: the level of risk they introduce and the degree of influence you have over their controls and behavior.
High-risk vendors with access to critical data, networks, or core operations merit a deeper, coordinated approach between Security, IT, Procurement, and the business. These are the relationships where shared assessments, clear expectations, and ongoing monitoring make a measurable difference. Low-risk vendors with limited influence require a different strategy: internal compensating controls, well-defined hygiene expectations, and streamlined review cycles. The matrix helps teams avoid spending time where it has little impact and focus their effort where collaboration reduces the most risk.
Automating Third-Party Vendor Management with Modern Tools
Once you have a unified inventory and a clear prioritization model, automation can scale and help keep your third-party vendor management program current as conditions change. Most teams begin with manual reviews, but data-driven third-party tools can streamline the work and provide early warning signals when vendor exposure shifts.
A few examples include:
· Outside-in visibility to flag exposed assets or configuration drift
· Continuous monitoring for changes in a vendor’s attack surface or access paths
· Basic threat intelligence (CTI) to highlight active campaigns or leaked credentials
· Control and evidence tracking so documentation stays fresh across all functions
· Quantitative methods, such as FAIR-based models, for defensible prioritization
· Workflow automation to route reviews to the right teams based on risk
These capabilities help teams stay aligned and ensure third-party oversight evolves with the vendor ecosystem.
Building a Unified, Data-Driven Vendor Management Capability with C-Risk
Most organizations struggle with the same problems in third-party vendor management: fragmented visibility, inconsistent ownership, and a process that drifts as the business grows. The approach outlined in this article — building a unified inventory, enriching it with exposure-based questions, prioritizing vendors by influence and risk, and putting light automation around the essentials — helps create a program that stays aligned with how the business actually works.
C-Risk helps teams build this capability in a structured, data-driven way. We focus on the fundamentals: defining a unified inventory, clarifying governance, mapping vendor access to your value chain, and establishing a repeatable prioritization model. When clients are ready, we help integrate automation, outside-in visibility, and quantitative methods such as FAIR to support defensible decisions.
If you want to strengthen your third-party vendor management program or move toward a data-driven approach, schedule a meeting with a C-Risk expert today.
Building a Unified, Data-Driven Vendor Management Capability with C-Risk
Most organizations struggle with the same problems in third-party vendor management: fragmented visibility, inconsistent ownership, and a process that drifts as the business grows. The approach outlined in this article — building a unified inventory, enriching it with exposure-based questions, prioritizing vendors by influence and risk, and putting light automation around the essentials — helps create a program that stays aligned with how the business actually works.
C-Risk helps teams build this capability in a structured, data-driven way. We focus on the fundamentals: defining a unified inventory, clarifying governance, mapping vendor access to your value chain, and establishing a repeatable prioritization model. When clients are ready, we help integrate automation, outside-in visibility, and quantitative methods such as FAIR to support defensible decisions.
If you want to strengthen your third-party vendor management program or move toward a data-driven approach, schedule a meeting with a C-Risk expert today.
