Vendor Security Assessments: Integrating Outside-In Scoring into Your TPRM Program
Organizations now depend on third parties for critical systems, customer operations, and key business processes. That reliance has widened the attack surface far beyond the traditional perimeter. Attackers understand this. IBM reports that supply chain compromise accounts for 15% of breaches at an average cost of $4.91 million. They target suppliers because a weak link upstream can provide access to data or systems that would be harder to reach directly. Yet many TPRM programs still rely on point-in-time questionnaires and annual audits.
In this article, we look at a data-driven approach to third-party risk: how outside-in assessments, threat intelligence, incident history, and quantitative analysis can provide a risk-based understanding of your extended enterprise.
- Outside-in techniques reveal what a vendor actually exposes online
- Cyber threat intelligence and incident history show which suppliers align with active threats or repeated weaknesses
- FAIR brings defensible, risk-based analysis to third-party decisions
- Automation keeps TPRM responsive as vendor ecosystems grow
- Modern TPRM prioritizes suppliers by business criticality and real exposure
The Limits of Traditional Third-Party Procurement and Assessment
According to the 2025 Global Third-Party Breach Report from SecurityScorecard, more than a third of all breaches in 2024 originated from vendors, suppliers, or service providers. Procurement still evaluates most new suppliers through point-in-time questionnaires and self-reported assessments. While these checks meet a compliance requirement, they offer little visibility into a vendor’s attack surface or the business impact of a third-party breach. And by the time a questionnaire is returned, it is already out of date.
Why Self-Assessments and Questionnaires Don’t Reflect Reality
Self-assessments describe a vendor’s governance posture, not the conditions that determine whether they can be used as a pathway to your organization critical digital assets. Questionnaires capture information about certificates, controls, etc. They are a snapshot of a vendor at the precise moment the questionnaire was completed. However, vendor infrastructures aren’t static. Shadow IT, credentials leak, integrations expand, controls drift and new products are launched. None of this shows up in a third-party questionnaire.
In addition, most assessments ignore the most critical aspect: how the vendor connects to your data and systems. Even compliant or certified suppliers can become entry points if their external footprint is weak or their access into your environment is not accounted for or poorly controlled.
The Need for Fact-Based Approaches in a Rapidly Evolving Threat Landscape
Risk management is ultimately a decision-making discipline, and defensible decisions require evidence. Third-party risk is no different. If you want to evaluate vendors with the same rigor you apply to financial or operational risks, you need objective data. This is especially true because third parties sit directly in your value chain. They handle your data, support core processes, and interact with internal systems. Attackers know this. They routinely target suppliers because it gives them a faster, quieter path into an organization’s crown jewels than attacking the primary network.
A data-driven approach closes the gap that questionnaires and certifications cannot. It gives you visibility into how a vendor actually operates: their exposed infrastructure, their historical involvement in breaches, the changes in their external footprint, and the potential pathways an attacker could exploit to reach your environment. And because resources are finite, evidence-based insight is essential for deciding where to place controls and attention across an expanding supplier ecosystem.
In practice, data-driven third-party assessments enables you to:
- Prioritize vendors based their access to critical assets
- Understand where third parties intersect with your value chain
- Allocate budget and resources where they reduce risk
- Make decisions you can defend to auditors, leadership, and regulators
- Maintain continuous awareness as vendor conditions change
The way to access this information is by assessing vendors’ using tools that rely on open sources of cyber intelligence to scan for necessary certificates and configurations.
Outside-In TPRM External Assessment Methodologies
Outside-in assessments rely on publicly observable signals to understand how a vendor actually operates on the internet. This is one of the ways to take a data-driven approach to TPRM: inventorying the assets a supplier exposes, monitoring how those assets change, and identifying weaknesses that could be used as entry points. The value is practical. It gives you evidence to support decisions on vendor selection, oversight, and risk treatment.
Techniques for External Vulnerability Assessment of Third Parties
The starting point for any outside-in assessment of your critical third parties is establishing what is public facing. You’re going to see what signals they broadcast. This kind of assessment relies on the same open-source intelligence (OSINT) techniques attackers use to uncover the digital footprint of an organization. That includes DNS enumeration, certificate transparency analysis, cloud metadata inspection, infrastructure correlations, and internet-wide scan data.
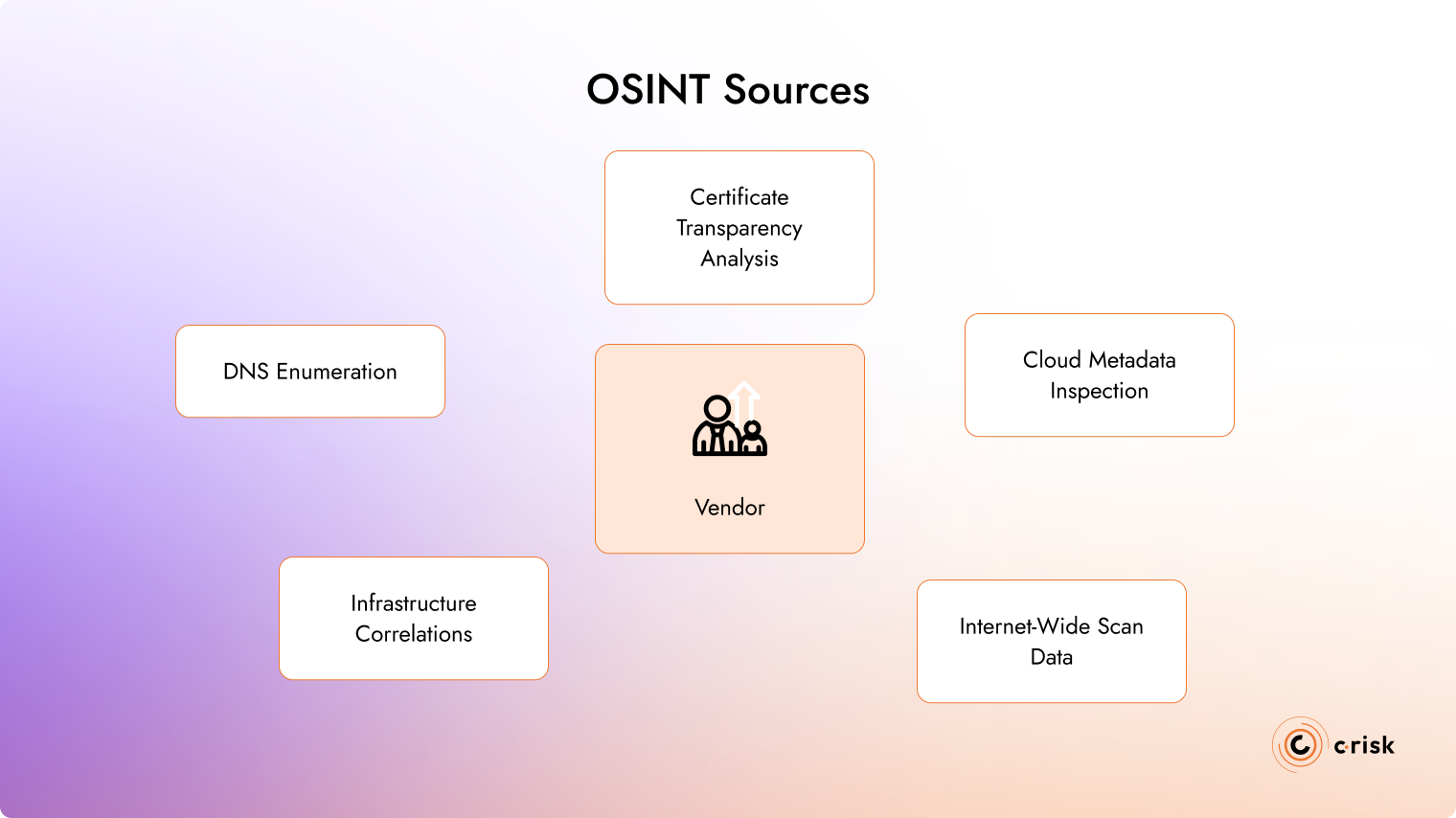
What this reveals:
- Internet-facing assets linked to the vendor
- Shadow IT, forgotten systems, and unmonitored development systems
- How those assets relate to each other and to the vendor’s core services
- Where their external footprint intersects with systems handling your critical assets
OSINT-based discovery provides a basic insight into how a partner operates, including in ways they may not even know about. If a vendor can’t see it, they can’t secure it. And if you can’t see it, you aren’t able to evaluate the risk they introduce to your environment.
Security Ratings and Risk Scoring in TPRM
Security rating tools apply outside-in techniques — OSINT, external scanning, and attack-surface mapping — to generate a score of the vendor’s external exposure. The score could be a letter or number score. The score itself does not provide any insight into the financial or operational impact of a third party. However, these ratings can be helpful for routing work: identifying which suppliers may warrant additional questionnaires, documentation, or review based on their exposure profile.
Examples of security ratings providers are:
- Bitsight
- SecurityScorecard
- UpGuard
- Panorays
Integrating Cyber Threat Intelligence into Third-Party Analysis
For your most critical third parties, Cyber Threat Intelligence (CTI) refines the outside-in picture by adding signals that scanning alone doesn’t capture. CTI surfaces whether a supplier’s technology stack is at risk because of tactics and techniques attackers are actively using. These are mapped through frameworks like MITRE ATT&CK.
Threat intelligence also captures information that doesn’t show up in self-assessments like leaked credentials. It can bring to light exploited activity against their dependencies and shifts in threat campaigns. It’s context that helps determine where additional controls are necessary to protect your value chain.
Using Incident History to Evaluate Vendor Cyber Resilience
A third-party’s incident history can provide you with insight into how their resilience controls perform when deterrent controls fail. Public breach reports, regulatory filings, and forensic summaries provide evidence of how your third party responds, like time to detection, how quickly an intruded was contained. Repeated issues can trace back to control gaps that you may need to address directly with a partner. Because your attack surface is a safe as your weakest third party.
Risk Quantification and Prioritization
An outside-in security score is only one input in a larger evaluation. Once you know what a vendor exposes to the internet, the next step is understanding what that exposure could mean for your business. To assess the potential financial impact and prioritize actions, you can apply a quantitative approach such as the FAIR methodology, which helps translate technical conditions into business-level risk.
Using FAIR to Understand Business Impact of Third Parties
Cyber risk quantification using the FAIR method as part of third-party risk management program provides the defensible data for making recommendations on security activities and how to treat vendors that are critical to the business.
For third-party relationships, FAIR allows you to communicate the financial impact or the likelihood of loss. The FAIR extensions – FAIR-MAM, FAIR-CAM and FAIR-TAM – also allow you to fine-tune your analysis and recommendations on controls and risk treatment.
The result of a FAIR analysis provides a risk picture you can defend to leadership. This moves third-party cyber risk out of the realm of “red, amber, green” charts and into the same decision-making framework used across the rest of the enterprise.
Operationalizing TPRM With Automation and Scalable Workflows
As your third-party portfolio grows, the problem shifts from collecting risk data to keeping pace with it. Automation helps turn outside-in signals, CTI, and quantitative analysis into something you can manage at scale. A cyber risk quantification tool can automate data ingestion and processing so changes in a vendor’s posture trigger the right follow-up without constant manual effort.
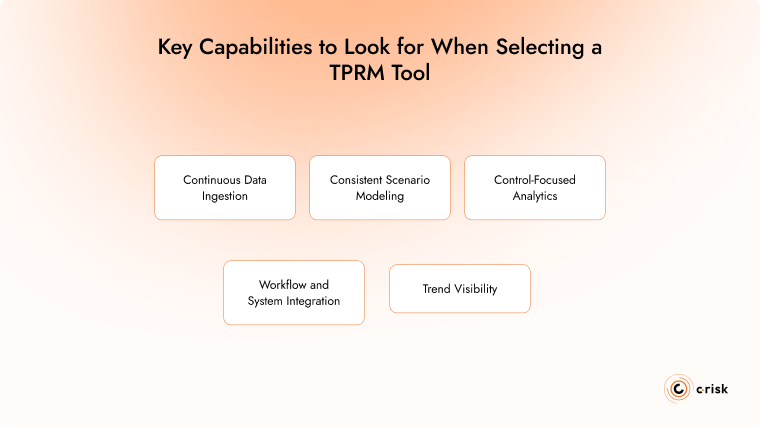
Key capabilities to look for when selecting a TPRM tool:
- Continuous data ingestion to collect and process telemetry, evidence, CTI, vulnerability data, and control assessments
- Consistent scenario modeling based on the FAIR taxonomy
- Control-focused analytics that supports control-effectiveness analysis (e.g., FAIR-CAM) to identify control gaps
- Workflow and system integration to reduce siloed risk management
- Trend visibility with continuous monitoring and alerts
Key Capabilities to look for When Selecting a TPRM Tool
Elevating TPRM With a Data-Driven, Quantitative Approach
Most third-party risk programs still rely on manual questionnaires and annual reviews. These processes weren’t designed for the speed or complexity of today’s vendor ecosystems. A data-driven model changes that.
C-Risk brings deep expertise in building defensible, quantitative cyber risk programs and applying those methods to third-party risk. Our approach helps organizations prioritize suppliers based on criticality — how a third party interacts with your data, the systems they access, and the revenue-generating activities they support. This provides a clearer view of which vendors matter most and where to focus oversight, controls, and investment.
C-Risk supports TPRM teams in:
- Scoping and quantifying third-party risk scenarios using FAIR
- Assessing control effectiveness along your value chains
- Implementing and operationalizing cyber risk quantification tools
- Integrating outside-in, CTI, and incident data into TPRM workflows
- Training teams to apply DDRM using FAIR in risk analysis and decision-making
A modern TPRM program needs to scale with the organization. Quantification, automation, and continuous external visibility provide that foundation. If you’re building or refining a data-driven third-party risk program, C-Risk can help.
