How Collaborative Vendor Relationships Strengthen Cyber Resilience
Traditional vendor management approaches are no longer enough to navigate the interconnected digital ecosystems of large enterprises. This article explores how collaborative, data-driven relationships with third parties can transform vendor oversight into a strategic advantage. And how measurable, financially grounded decisions strengthen your cyber resilience and create shared value across the supply chain.
- Traditional, compliance-driven vendor management no longer keeps pace with today’s interconnected ecosystems
- Data-driven, risk-based methods, including FAIR, enable measurable, financially grounded decisions on third-party controls and relationships
- Collaborative third-party relationships are mutually beneficial for internal controls and externally facing services
- Quantifying third-party relationships allows for data-informed decisions and demonstrating your return on security investments
Rethinking Third-Party Relationships: From Transaction to Collaboration
When a third party fails, you can fail with them. The organizations leading in cyber resilience have recognized a shift in how to manage third-party relationships. Success depends on collaboration. Building trusted, transparent, and measurable partnerships turns third-party risk management into a shared defense and a source of competitive advantage.
The limits of the traditional client–vendor model
Traditional vendor management was designed for procurement efficiency, not resilience. Contracts, audits, and questionnaires define minimum acceptable standards, but they rarely build the mutual visibility or responsiveness needed in today’s dynamic threat environment.
This transactional model creates a compliance mindset: suppliers respond to questionnaires, and clients treat the answers as a compliance exercise. The result is limited transparency into shared risks or how to improve when depending on a point-in-time questionnaire.
When a cyber incident occurs, that distance becomes costly.
- A cloud provider like Microsoft or AWS operates at global scale with millions of customers; the possibility for a close collaboration is unlikely and means understanding the limits of their security and improving internal controls.
- A mid-sized SaaS provider handling customer data, on the other hand, may depend on your guidance and feedback to mature its security posture thereby improving your security as well.
You won’t have the same level of influence for all relationships. Again, prioritization is key. Mature programs calibrate expectations and collaboration models based on each supplier’s criticality and capacity to improve their security posture and maturity.
The goal is to engage smarter with your partners.
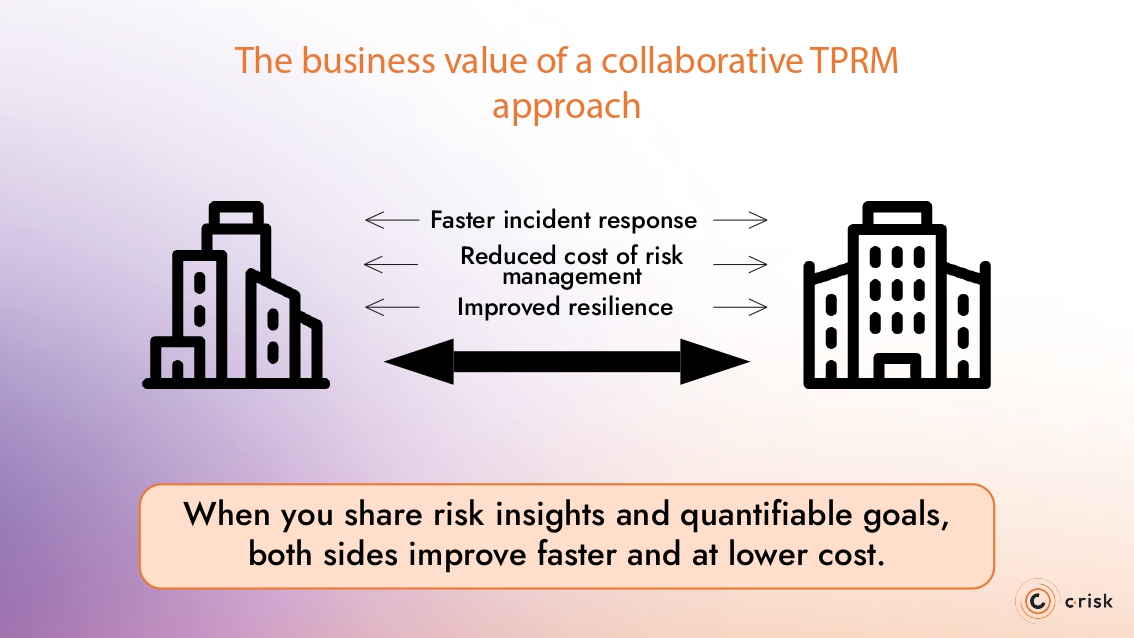
The business value of a collaborative approach
A collaborative approach enhances your governance with data-driven partnerships. When you share risk insights and quantifiable goals, both sides improve faster and at lower cost.
- Reduced cost of risk management: fewer redundant assessments when assessments are triaged based on criticality
- Faster incident response: established communication with third parties ensures remediation efforts can be ramped up quicker
- Improved resilience: suppliers that understand the impact of their control gaps can increase internal performance and security for customers
Methodologies for Building Sustainable Collaborative Relationships
A turning point in third-party risk management is that collaboration is not just a soft skill or a “nice to have,” but a structured capability embedded all aspects of cybersecurity and risk management. As McKinsey notes in a recent report, leading organizations are building executive-level partnerships with critical suppliers, with CISOs working together to improve resilience at ecosystem scale.
To build sustainable third-party collaboration, organizations need to move beyond questionnaires and compliance-driven oversight to create mechanisms that foster open communication between security teams with their critical partners.
Core Attributes for Effective TPRM
Effective third-party risk management depends on three core attributes: it must be risk-based, data-driven, and continuous. These principles, grounded in industry standards, including the FAIR model, enable organizations to prioritize the critical vendors, measure exposure using objective methods, and maintain a continuous inventory as the third-party ecosystem evolves.
- Risk-based means engaging third parties at the right level. High-impact vendors could require deeper dialogue and more frequent coordination
- Data-driven means decisions are informed by measurable indicators rather than only point-in-time scoring
- Continuous means relationships evolve over time. As the threat environment changes, collaboration keeps both sides informed and adaptive.
The addition of a fourth attribute, collaboration, considers that the cybersecurity isn’t mono-directional in a third-party relationship. When clients and vendors open communication channels aligned to risk criticality and data sensitivity, they can adapt faster to change and share accountability for reducing risk.
Embedding Collaboration into Everyday Risk Processes
Collaboration becomes meaningful when it’s built into daily operations. Rather than treating cooperation as an ad-hoc exercise, especially in the event of an incident, more mature programs weave it through each stage of third-party management.
- Onboarding: Engage critical suppliers early to clarify expectations and align on risk priorities in the event of a control gap discovery.
- Joint response plans: Establish predefined communication channels and playbooks so incidents can be contained and resolved faster.
- Shared metrics: Use common dashboards and FAIR-based indicators to track control maturity and exposure trends, turning oversight into performance management.
- Automation: Leverage platforms that enable continuous monitoring and data sharing without increasing administrative effort.
As KPMG notes, collaboration also extends across business functions. IT and procurement are not the only functions involved with third-party risk management.
Embedding collaboration this way makes it routine, measurable, and sustainable — transforming third-party risk management from compliance oversight into operational resilience.
Making Third-Party Collaboration Cross-Functional
Effective collaboration with third parties starts inside the organization. When risk, security, procurement, and business teams operate in silos, suppliers receive mixed signals, such as redundant questionnaires, inconsistent requirements, and conflicting priorities. The result is third-party compliance fatigue rather than improvement.
Cross-functional collaboration aligns internal stakeholders around a shared view of third-party risk. Shared dashboards and unified taxonomies based on FAIR allow teams to evaluate suppliers using the same metrics and language.
Building Skills for Data-Driven, Collaborative Third-Party Risk Management
Collaboration succeeds when all parties involved share a common understanding of risk. Training and awareness programs help translate a data-driven strategy into daily risk management workflows and processes across internal teams and with critical suppliers.
Practical ways to strengthen collective capability:
- Educate internal teams on data-driven risk concepts, such as FAIR, so procurement, security, and business leaders interpret exposure the same way
- Run cross-functional workshops where IT, risk, and procurement teams co-review real supplier scenarios to align language and expectations
- Offer vendor-focused training that explains how your organization measures and reports risk, helping partners respond more effectively
- Simulate joint incidents to test decision-making and communication under pressure
- Share insights post-incident so lessons benefit the wider ecosystem, not just one team
Organizations that invest in these shared learning programs see faster alignment and more consistent decision-making. And when communication is clear, decisions can be data-driven and defendable, improving resilience across the enterprise and its extended enterprise.
Quantifying the Benefits of Strategic Collaboration
In order to prove the benefit of collaboration, you need to measure it. The FAIR model can be used to measure the value or your third-party relationships, investment and return. Because FAIR helps quantify risks in financial terms, it enables data-driven decision-making at all levels.
Tracking measurable outcomes allows you to communicate the ROI of your security investments, such as:
- Reduced risk exposure: using FAIR-derived metrics, you can estimate the reduction in expected loss through improved controls and collaboration
- Lower management & assessment costs: fewer duplicate assessments across functions, streamlined oversight, fewer remediation cycles
- Faster incident response & lower impact: improved communication and trust shorten recovery time and reduce business disruption
- Increased innovation/time-to-market: when partners are aligned and transparent, you enable faster joint development and go-to-market cycles
Measuring Maturity and Return on Collaborative Risk Management
The evolution of collaborative third-party risk management can reflect the broader cybersecurity maturity models such as the NIST Cybersecurity Framework (CSF).
There are four levels to this model that broadly outlines how to define a program:
- Partial: Cyber practices are ad hoc, with limited governance
- Risk-Informed: Policies exist but remain inconsistent across functions
- Repeatable: Processes are formalized and integrated into governance
- Adaptive: Practices are proactive, continuously improved, and aligned with enterprise risk management
Third-party cyber risk management programs can be assessed using a similar analogy.
Each evolution of the TPRM approach yields measurable ROI:
- Reduced third-party management costs, including redundancy in actions
- Lower expected loss resulting from continuous control assessments
- Faster time-to-response with improved communication
- Innovation gains that lead to enterprise growth
As the FAIR Institute emphasizes, quantification enables data-driven decisions and defensible investment cases for resilience. By viewing collaborative third-party risk management maturity and ROI together, organizations can demonstrate that each progression in capability not only reduces risk but creates business value.
Turn Collaboration into Quantified Resilience with C-Risk
C-Risk helps organizations operationalize collaborative third-party risk management through data-driven, financially quantified third-party risk management.
Our FAIR-certified experts apply the FAIR™ model and automation using a unified third-party risk management platform to transform your compliance-based approach into a continuous, value-focused process. This enables CISOs, procurement and risk teams to make aligned, defensible decisions.
C-risk with SAFE TPRM brings your collaborative ecosystem to the next maturity tier by helping you:
- Quantify third-party exposure in financial terms to prioritize where collaboration creates the most value
- Automate assessments and monitoring for ongoing visibility without increasing administrative effort
- Enable shared dashboards and metrics that align internal teams and critical suppliers around the same data
- Demonstrate measurable ROI
Learn how C-Risk and SAFE TPRM can help you operationalize collaborative third-party risk management.
