From subjectivity to objectivity: Why quantifying cyber risks is essential
Organizations have traditionally relied on qualitative risk assessments—think red, yellow, green heat maps—to manage cyber risk. But as businesses evolve, becoming dependent on digital processes, threats become more complex, and regulations require risk-based approaches, traditional methods fall short.
With the global average cost of a data breach at $4.9 million, according to IBM's 2024 Cost of a Data Breach Report, security leaders now face a turning point: the need to transition to data-driven methods that hold up under the microscope.
- Beyond heat maps: Traditional red-yellow-green risk assessments create cognitive bias, inconsistent team interpretations, and prevent organizations from demonstrating measurable security progress to stakeholders.
- Financial impact clarity: Quantitative approaches enable security leaders to express cyber risk in dollar terms, showing executives exactly how much risk reduction their investments deliver—moving from "high risk" to "$500K annual loss exposure."
- Industry-specific precision: Different sectors face unique cyber risk profiles—from healthcare's patient safety concerns to financial services' regulatory capital requirements—that require tailored quantification approaches for accurate business impact modeling.
- FAIR™ framework advantage: The Factor Analysis of Information Risk methodology provides a proven, internationally recognized standard for translating complex cyber scenarios into defensible financial projections that support strategic decision-making.
What are the limitations of qualitative risk management methods?
Both qualitative and quantitative risk management practices do support decision-making. But reducing subjectivity is essential for making defensible, repeatable, and strategically aligned security decisions.
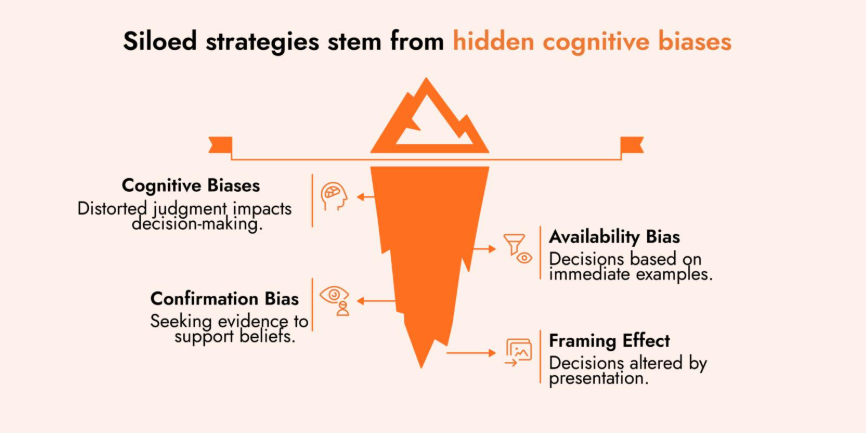
Cognitive bias and noise
In organizations that rely on qualitative assessments, stakeholders will often advocate for investments that help their team advance without considering the broader business impact. This leads to siloed strategies, where different teams compete for resources without a shared framework for comparison.
Cognitive biases distort judgment in subtle but impactful ways. Common examples include:
- Availability bias – making a judgment based on immediate examples at hand (e.g., high profile ransomware attack in the news)
- Confirmation bias – seeking out or interpreting evidence in such a way that supports your own strongly-held beliefs or expectations (e.g., compliance teams focusing on control gaps, while overlooking business objectives)
- Framing effect – altering decisions based on how choices are presented (e.g., framing a security initiative as a cost vs. a savings opportunity, even if both options are financially equivalent)
These biases and the noise they create can lead to inefficient risk prioritization and erode confidence in cybersecurity programs. A quantitative, data-driven approach minimizes these distortions by grounding risk decisions in measurable, repeatable analysis.
Inconsistency across teams
Without a standard language for risk or a data-supported quantified measurement of risk, two teams assessing the same risk scenario will likely come to completely different conclusions. This inconsistency becomes visible during audits and board reviews. And it can undermine trust in the security function.
Inconsistent perception of risk across functions:
- IT security rates unpatched systems as "high" based on technical vulnerability
- Business continuity rates same systems as "medium" based on workaround procedures
- Finance rates the risk as "low" based on revenue impact
- Operations rates as "high" based on productivity concerns
Missed opportunities
Qualitative assessments prevent organizations from demonstrating the evolution of their security posture. When risks remain categorized as "medium" or "high" quarter after quarter, meaningful progress gets lost in semantic meaning. This inconsistency manifests in several ways:
- Inability to demonstrate ROI – Cannot show how much risk was eliminated by security investments in financial terms
- Poor trend analysis – No numerical baselines to measure changes risk posture
- Ineffective prioritization – Decisions are based on rules of thumb or compliance requirements
- Static risk registers – Same risk distribution despite significant security investments
- Stakeholder confusion – Board members see consistent risk levels despite budget approvals

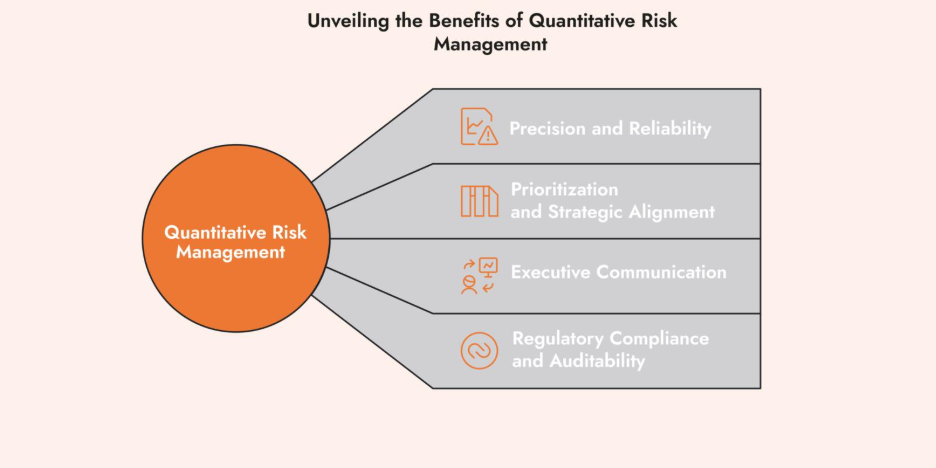
The advantages of an objective, quantitative approach
Moving from subjective assessments to quantitative methods fundamentally transforms how organizations understand and manage cyber risk. While traditional approaches leave security leaders struggling to justify investments or demonstrate progress, data-driven methodologies provide the precision and credibility that modern businesses demand.
The transformation delivers measurable benefits across four critical areas:
- Greater Precision and Reliability – a quantitative approach identifies measurable factors that enable organizations to track risk reduction over time, expressing risk in financial terms rather than perpetually using descriptive terms for risk.
The CISO of a Fortune 500 financial services company could confidently report to the board that security activities "reduced annual loss exposure from $2.3M to $1.8M through targeted security controls."
- Clear Prioritization and Strategic Alignment – Numbers enable direct comparison between different risk types, supporting defendable resource allocation decisions.
- Executive Communication – Security leaders can communicate with executives in ROI terms they understand, providing specific investment justifications with measurable returns that support comprehensive cost-benefit analysis.
- Regulatory Compliance and Auditability – Evolving cybersecurity regulations (DORA, NIS2, SEC) increasingly demand risk-based approaches with documented risk-based methodologies.
Common misconceptions about cyber risk quantification
"Quantitative approaches are too complex."
Many security leaders assume that quantitative risk analysis requires advanced mathematics or dedicated data scientists. In reality, frameworks like FAIR are designed for practical business application. The complexity lies not in the calculations, but in the strategic thinking about risk scenarios.
"We don't have enough data."
Your organization already has vast amounts of data. It’s a matter of contextualizing any amount of data for the problem you’re trying to solve. Douglas Hubbard, author of How to Measure Anything, wrote, “If you know almost nothing, almost anything will tell you something.”
"What we are doing is faster."
While initial qualitative assessments may seem quicker, this speed advantage disappears over time. Quantitative frameworks help you build reusable models that accelerate future assessments.
“While the benefits of cyber risk quantification are compelling, the challenge lies in implementation.”
This is where the international standard quantitative model Factor Analysis of Information Risk (FAIR) shines. It is a model that describes what risk and how to quantify it. The standard establishes a taxonomy and methodology that can be adapted by risk and security teams measure and manage cyber risk in parallel with their current risk management program.
Adapting cyber risk quantification to your industry
While the principles of quantitative risk assessment remain consistent, different industries can benefit from tailored approaches. Understanding these sector-specific considerations helps organizations implement frameworks that address their most critical business risks.
Financial Services
Hacktivists claimed responsibility for over 15,000 DDoS attacks on financial institutions in 2024, marking a 20% increase from the previous year. Banks and financial services have to keep their payment services running. Key quantification focuses include:
- Regulatory requirements and stress testing scenarios
- Control gaps for transaction processing disruption
- Regulatory penalties like DORA or GDPR fines
- Third-party vendor risk in payment processing chains
Healthcare
The healthcare sector continues to face increasing risks from cyber threats, particularly in the form of ransomware and hacking incidents reports the HIPPA Journal’s 2024 Healthcare Data Breach Report. In 2024 alone, over 275 million healthcare records in the US were exposed, stolen, or improperly disclosed.
Healthcare companies can benefit from risk quantification when assessing:
- Patient care disruption costs and potential safety incidents
- HIPAA violation penalties and legal exposure
- Medical device security and FDA compliance requirements
- Third-party and supplier risk
Retail and e-commerce
Retailers and e‑commerce platforms face mounting cyber risks that directly threaten revenue, customer trust, and operational continuity. In April 2025, Marks & Spencer lost nearly six weeks of online sales due to a ransomware attack, with a resulting profit hit of £300 million.
Retail businesses can benefit from risk quantification when assessing:
- Cost of e-commerce platform downtime during peak shopping periods
- Payment card industry (PCI) compliance violations
- Customer data breaches and brand reputation damage
- Third-party and inventory management system disruptions
These industry-specific approaches ensure that quantitative models reflect the actual business consequences that matter, making risk communication more relevant and actionable for decision-makers.
Building a holistic approach with cyber risk quantification
Methods like FAIR augment the work security teams are already doing. Quantification’s purpose is to help decision making by reducing uncertainty about risk.
For example, when a security architect understands that a particular vulnerability could lead to a data breach, quantitative analysis helps translate that technical knowledge into specific financial projections that business leaders can evaluate alongside other investment opportunities. The expertise remains central, while being supported by measurable data and a structured methodology.
What is FAIR?
The Factor Analysis of Information Risk (FAIR) framework was developed in the early 2000s by Jack Jones, who was the CISO for an Nationwide Insurance at the time. FAIR was created to address the limitations that security professionals faced when trying to communicate effectively with decision-makers.
Today, FAIR is globally implemented by companies of all sizes and across all industries. It complements the major cybersecurity and compliance frameworks, such as ISO 27005, NIST CSF, EBIOS RM, SOC 2 and NIS2. And helps organizations avoid duplicating compliance efforts.
Support decisions with data-informed risk management
Quantitative methods don't ignore the expertise that drives qualitative cyber risk assessments. Rather, methods like cyber risk quantification using FAIR provide a standard language to maximize the benefits of a subject matter expert’s knowledge within a structured methodology that reduces bias and increase confidence in cybersecurity decision
How C-Risk transforms cyber risk management
At C-Risk, we help organizations transition from subjective risk assessments to data-driven cyber risk quantification that delivers measurable business value. Our expertise in implementing quantitative risk frameworks enables security leaders to make defensible decisions, communicate effectively with executives, and demonstrate ROI on security investments. We help you:
- Transform risk communication
- Adapt frameworks to your business context
- Accelerate strategic decision-making
- Strengthen regulatory compliance
Our proven approach has helped Fortune 500 companies transform their cyber risk management capabilities. We deliver practical implementation guidance that fits your existing processes and organizational culture.
Connect with our team to explore how cyber risk quantification can transform your risk communication and support enterprise-wide decision-making.
