Risk Management Plan: Building a Data-Driven Cyber Risk Program
Organizations today need a cyber risk management plan that does more than check compliance boxes. As digital ecosystems grow increasingly complex and cyber threats directly impact business continuity, executives face mounting pressure to adopt modern approaches that align cybersecurity with enterprise objectives. Traditional assessments and fragmented tools struggle to keep pace with rapid change.
This guide provides Chief Information Security Officers (CISOs), business leaders, and executives with a practical roadmap to implement a transformative cyber risk management plan. By following this phased methodology—from current-state assessment through continuous improvement—you'll build a security program that is sustainable, strategically aligned, and adaptable to emerging threats.
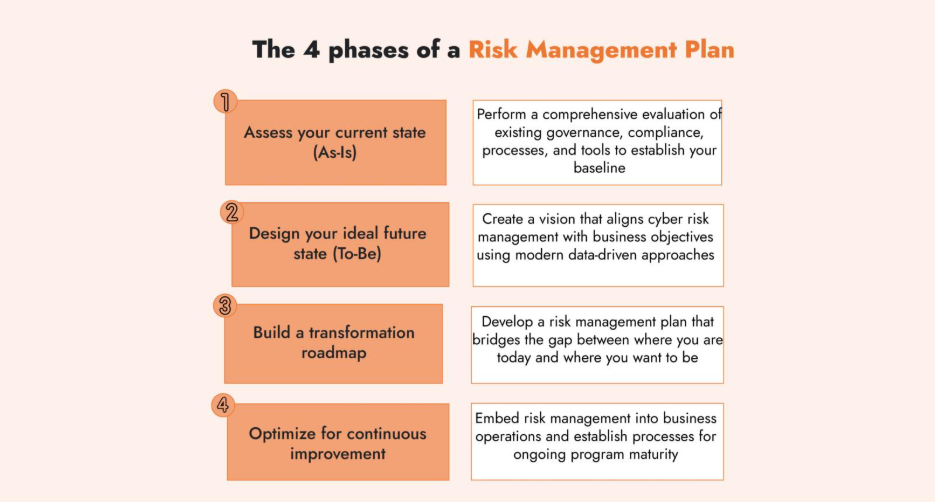
- Assess your current state (As-Is): Perform a comprehensive evaluation of existing governance, compliance, processes, and tools to establish your baseline
- Design your ideal future state (To-Be): Create a vision that aligns cyber risk management with business objectives using modern data-driven approaches
- Build a transformation roadmap: Develop a risk management plan that bridges the gap between where you are today and where you want to be
- Optimize for continuous improvement: Embed risk management into business operations and establish processes for ongoing program maturity
Phase 1: Understand Your Current State of Risk Management
The first phase lays the foundation by establishing where you are and where you need to be. Before any changes are made, it’s crucial to understand the organization’s unique business context, current risk management practices, and overall risk tolerance. It is also an opportunity to gain consensus as stakeholder alignment early on is crucial for setting realistic transformation goals later.
Rather than starting from scratch, the current state assessment phase helps determine which aspects of your risk management program can be strengthened and which areas require attention.
Launch a Comprehensive Current-State Assessment
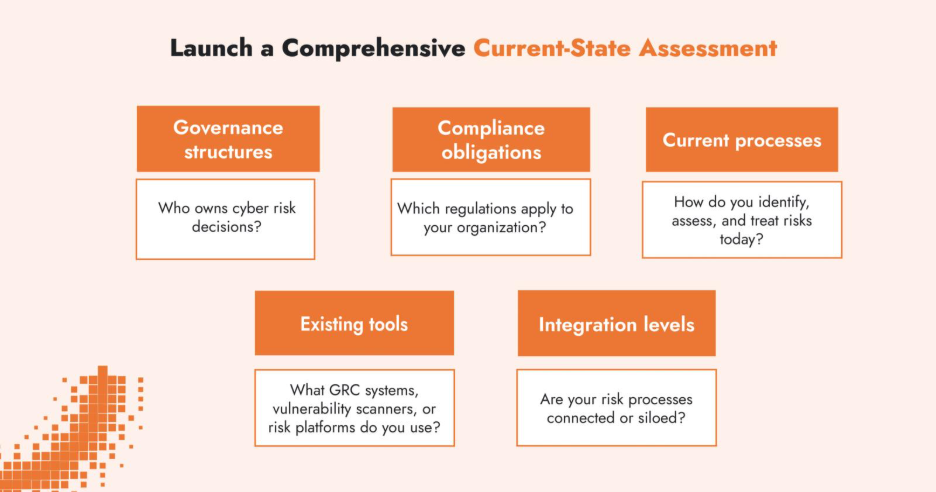
Begin by reviewing your existing cyber risk management components:
- Governance structures: Who owns cyber risk decisions?
- Compliance obligations: Which regulations apply to your organization?
- Current processes: How do you identify, assess, and treat risks today?
- Existing tools: What GRC systems, vulnerability scanners, or risk platforms do you use?
- Integration levels: Are your risk processes connected or siloed?
Document both strengths to leverage and weaknesses to address. Gather input from IT, security, compliance, business units, and executive leadership to ensure a complete picture.
Map Business Objectives to Critical Assets
Your cyber risk management plan must protect what matters most to your business. Identify and prioritize:
- Critical business processes that drive revenue
- Systems and data essential for operations
- Assets whose compromise would damage reputation
- Intellectual property and competitive advantages
For example, an e-commerce company might prioritize customer payment systems and platform uptime, while a pharmaceutical firm focuses on research data and intellectual property protection. This business-aligned approach ensures security investments deliver real value.
Identify the Organizational Risk Appetite and Maturity Level
What is your business’s risk appetite – the level of risk the board and executives are willing to accept in pursuit of business objectives?
Throughout the current state assessment, it is important to collaborate with executive leadership to articulate the cyber risk appetite in clear financial terms. Understanding risk appetite provides a compass for your program: it defines what level of residual risk is tolerable and where management expects risk to be reduced.
Alongside risk appetite, assess your current risk management maturity. Are your risk processes ad-hoc and reactive, or do you have some structured practices in place? Using a maturity model can be helpful to gauge the starting point.
According to the 2025 State of Cyber Risk Management survey, organizations with higher cyber risk maturity are significantly more likely to withstand and recover from incidents.
Many organizations discover that their risk management maturity is characterized by siloed functions, subjective assessments, and a focus on checkbox compliance. High-maturity organizations, by contrast, proactively identify and quantify risks, and integrate risk considerations into decision-making, leading to greater resilience and performance.
Evaluate Your Governance Framework
Strong governance forms the backbone of any effective cyber risk management plan. Assess whether you have:
- Clear roles and responsibilities across business, IT, and security functions
- Documented policies aligned with frameworks (NIST CSF, ISO 27001)
- Defined risk assessment and remediation processes
- Escalation pathways from operational to board level
- Regular risk reporting cadences
Understand Your Compliance Landscape
Cybersecurity today operates within an increasingly complex and high-stakes regulatory environment. Global regulators are holding executive leadership accountable for cyber risk management, with requirements that extend far beyond traditional IT controls. A data-driven security program aims higher than compliance checklists.
As part of the current state assessment, organizations should:
- Identify all applicable laws, regulations, and standards based on geography, industry, and business operations
- Evaluate current compliance posture, including formal gaps, audit results, or control deficiencies
- Document areas of non-compliance, and determine the associated operational or legal risk
Key regulatory and standards bodies are driving change at a rapid pace:
- EU NIS2 Directive: Requires executive oversight and board-level approval of cybersecurity risk management measures
- US SEC Cyber Rules: Mandate disclosure of material cybersecurity risks and incidents in financial filings
- Sector-specific mandates: HIPAA, PCI DSS, DORA, SOX, GLBA, and others
- Industry frameworks: ISO/IEC 27001, NIST CSF, UK Cyber Essentials, SOC 2
Document current compliance gaps and their associated risks to prioritize remediation efforts.
Inventory Your Risk Management Technology Stack
Another aspect of the current-state assessment is an inventory of the technology stack that supports your business and risk management activities.
Existing tools might include:
- Governance, Risk, and Compliance (GRC) platforms
Tools that house risk registers, automate workflows, manage assessments, and track remediation.
- Vulnerability and threat management tools
Platforms that identify technical exposures and ingest threat intelligence.
- Third-party risk management tools
For assessing vendors, partners, and external dependencies.
- Risk quantification platforms
Emerging platforms, particularly those using the FAIR model for cyber risk quantification help organizations translate technical metrics into financial terms.
Are your systems integrated? Do they provide actionable insights or just more data silos?
Conduct Gap Analysis
Phase 1 concludes with a comprehensive gap analysis that reveals:
- Unclear roles and unassigned risk ownership
- Outdated policies and procedures
- Inefficient resource allocation
- Missing integrations between tools
- Disconnects between security metrics and business objectives
This baseline assessment provides the foundation for building your transformation roadmap.
Phase 2: Designing an Ideal Future State–the Roadmap
With a solid understanding of the state of your current risk management program and existing gaps and workstreams within the business context, Phase 2 focuses on building a strategic vision for the organization. This includes defining the guiding principles, identifying use cases and looking at how to improve current workstreams and create new ones that don’t yet exist.
Define Your Transformation Goals
Establish concrete objectives for enhancing your risk management lifecycle:
Risk Identification:
- Implement continuous asset discovery
- Automate threat intelligence integration
- Establish cross-functional risk identification processes
Risk Assessment:
- Improve qualitative methods with data-driven approach
- Adopt quantitative framework (like FAIR) to understand risk in business terms
- Clearly articulate ROSI (return on security investments)
Risk Treatment:
- Create risk acceptance criteria tied to business impact
- Identify cyber insurance policies that adequately cover unavoidable risk
Risk Reporting:
- Develop executive dashboards with business-relevant metrics
- Identify KRIs and KPIs that support decisions
- Establish board-level reporting cadences
For example, a target state objective might be implementing a quantitative risk analysis framework (such as FAIR) for key risk scenarios that were identified in the as-is assessment, instead of relying solely on qualitative risk assessments. Another goal could be establishing a robust risk treatment process where mitigation efforts are prioritized based on risk-reduction impact and cost-benefit analysis, rather than treating all “high” risks equally.
Improvements to risk reporting might include developing data-informed and risk-based dashboards. By setting clear goals like “quantify top 10 risks per business unit” or “integrate key cyber risk indicators into enterprise risk reports for each quarter”, you create concrete targets to improve capabilities, resource allocation, and resilience.
Incorporate Data-Driven Methods
Modern risk management increasingly means data-driven risk management (DDRM) – leveraging both qualitative and quantitative methods to support cybersecurity decisions. When drawing up the to-be state, include initiatives and tools that implement data-driven risk assessment techniques.
The FAIR model (Factor Analysis of Information Risk) provides a structured methodology to analyze cyber risk in financial terms. Integrating a quantitative approach like FAIR can be a game-changer for any security program. It provides risk analysts with a framework to estimate probable loss frequencies and impacts in dollars or euros, translating cyber risk into the language of the business. This way of communicating risk enables comparisons of risk mitigation options by expected ROI.
The improvement of your risk management tooling stack (such as risk quantification software or enhanced GRC platforms) should also be on the roadmap. The end goal is to move towards evidence-based risk management where decisions are supported by metrics and models rather than gut feeling.
Phase 3: Initial Implementation
The initial implementation phase focuses on prioritizing workstreams, defining milestones, and educating employees at every level within the enterprise to become more risk-aware.
Create Workstreams and Define Milestones
The roadmap should be divided into manageable workstreams. Each stream addressing a core pillar of risk transformation and tied to measurable, short-term milestones that demonstrate value.
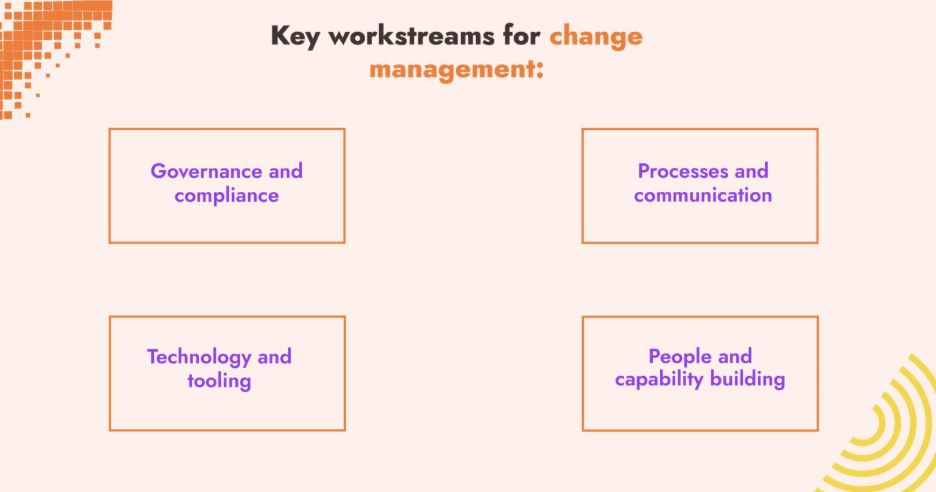
Key workstreams for change management:
- Governance and compliance
- Processes and communication
- Technology and tooling
- People and capability building
Launch Pilot Initiatives or Targeted Improvements
Rather than attempting the rollout of an entirely new program, start with incremental wins. These could be specific business units, particular risk domains, or select processes that are ripe for improvement.
Build Cross-Functional Risk Management Teams
Cyber risk management cannot succeed as a siloed function; it requires cross-functional collaboration. Use the initial implementation phase to formalize a cross-functional team or working group that will drive the risk program. This includes input from from IT security, IT operations, compliance/legal, enterprise risk management, procurement, finance and key business units.
Phase 4: Optimization of the Risk Management Plan
After initial rollout, the goal is to embed cyber risk management into everyday business activities and keep improving over time. This phase turns risk management from a project into a permanent capability.
Embed Risk Management into Governance and Business Processes
- Include risk updates in quarterly business reviews and risk committee meetings
- Require risk assessments for major IT projects and vendor changes
- Align with enterprise governance cycles like strategic planning or procurement
Track cyber security risk management progress using KPIs such as:
- Mean time to detect (MTTD)
- Mean time to remediate/respond (MTTR)
- Policy compliance rate
- Cost per incident
Executive and board-level oversight of performance metrics plays a critical role in maintaining accountability.
Critical Success Factors and Change Management
There are several critical success factors can determine the success of a change management initiative:
- Executive support
- Cross-functional collaboration
- Realistic scope with clear milestones
- Training and skills development
- Demonstrate value

Technology and frameworks alone aren’t enough. Success centers around strong leadership, clear data-driven objectives and a workforce that continually develops their communication and risk management skills.
Ready to Put Your Cyber Risk Management Plan into Action?
Building a data-driven cyber risk management program is a complex journey. C-Risk supports organizations move from ad-hoc cyber risk management to a data-driven approach with our expertise, methods, and tools to accelerate your transformation.
Here’s how we help:
- Assess and benchmark: We work with risk and security teams to assess current capabilities, identify gaps, and map your maturity against industry standards
- Design a data-driven risk management program: Develop a phased transformation plan aligned with your business and risk appetite
- Implement a quantitative risk management platform: The SafeOne platform supports risk quantification, third-party risk management, and executive reporting
If your organization is serious about connecting cybersecurity with business outcomes, we’re here to help you move faster and make better decisions.
