Data-Driven Prioritization: Allocating Cybersecurity Resources Effectively
Cybersecurity risk management is no longer a back-office function. It now sits under board oversight, alongside financial and operational risk. With this strategic elevation comes a new imperative: organizations must allocate security resources based on risk. Yet many still operate reactively. This disconnect weakens resilience and obscures the business value of cybersecurity investments.
Data-driven prioritization changes that. It helps CISOs and risk leaders align limited resources with the threats that matter most to the business. Using risk-based insights to direct effort where it reduces risk or drives growth, organizations can shift from tactical firefighting to strategic enablement. When cybersecurity decisions reflect business priorities and financial impact, security becomes a lever for resilience.
- Understand Criticality and Business Impact Mapping your digital assets to business processes provide insights to begin prioritizing investments
- Quantitative Risk Modeling Leads to Better Allocation FAIR is a quantitative method that complements all cybersecurity risk management frameworks
- Make Effective Comparisons Data-driven risk analysis enables cybersecurity initiatives to be compared with business initiatives and to weigh the cost-benefit
- Dashboards Enable Better Executive Engagement Quantified KPIs and KRIs enable senior leadership to understand risk in business terms
Why Resource Allocation Fails Without Prioritization
Security and risk teams often operate in fragmented risk management environments. Siloed cybersecurity approaches are not focused on risk reduction rather than organizational resilience. This can lead to:
- Over-investment in controls that don’t materially reduce risk
- Resources spread evenly rather than focusing on financial or operational impact
- Allocation of resources based on headlines or audit findings instead of business context
As a result, there are operational inefficiencies and a persistent gap between cybersecurity activities and organizational resilience. With the introduction of data-driven methods, cybersecurity is no longer a liability but a driver of growth.
From Cybersecurity Frameworks to Data-Driven Prioritization
Traditional cybersecurity frameworks like NIST CSF, ISO/IEC 27001, or EBIOS RM provide valuable structure for identifying and managing cyber risk. But these frameworks often emphasize control maturity, compliance readiness, or qualitative risk scenarios. For example, NIST CSF encourages assessment of control implementation levels, and EBIOS RM supports scenario-based qualitative analysis.
While these approaches offer clarity and structure, they often stop short of answering a key question: how much risk are we actually reducing? That’s where a quantitative model like FAIR (Factor Analysis of Information Risk) adds critical value.
FAIR complements these frameworks by quantifying risk in financial terms. It helps shift the perception of cybersecurity from a compliance checklist to a strategic business issue.
By combining frameworks that map processes and controls with FAIR-based quantification, organizations gain both the structure and the financial insight needed to prioritize effectively.
Aligning Resources with Business-Critical Risks
Organizations face an ever-expanding attack surface while operating with finite security resources. The key to effective cyber risk management lies not in protecting everything equally, but in strategically allocating resources based on business impact and criticality. By adopting a data-driven approach that maps cyber risks to core business functions, organizations can maximize their security ROI while building sustainable resilience.

Map Digital Assets to Business Processes
Prioritize risks that could disrupt customer service, operational continuity, or regulatory compliance. Understand the value chain and identify where disruptions would cost the most.
Inventory Third-Party Relationships
The extended enterprise model also extends your attack surface. Maintain an inventory of third parties with access to sensitive data, networks and revenue generating activities.
Incorporate Risk Appetite
This shared understanding helps dissolve functional silos and encourages a holistic view of cyber risk, aligning operational decisions with enterprise-wide strategic priorities.
Account for Operational Constraints
Prioritization must reflect operational realities, including available staff capacity, technology compatibility, and the organization's readiness for change.
Tools and Techniques for Optimal Allocation
As part of a data-driven cyber risk management approach, quantitative tools and methods are essential for translating prioritization into meaningful outcomes. These mechanisms help risk and security teams deploy effort where it drives the most value, while also equipping executive leadership with the visibility needed to understand trade-offs, evaluate investment decisions, and monitor performance over time. Done well, they turn prioritization from an abstract planning activity into a concrete set of actions aligned with measurable risk reduction.
Financial Risk Modeling using FAIR
The FAIR method is a quantitative model that calculates risk scenarios by analyzing how often a risk event might happen, or the likelihood of an event, and the potential financial impact of a risk event occurring, expressed in financial terms. The FAIR taxonomy defines these as the Loss Event Frequency and Loss Magnitude, respectively.
Risk = Likelihood (%) x Impact ($) of Loss Event Scenarios
Understanding the overall risk exposure in financial terms supports informed and risk-based decisions.
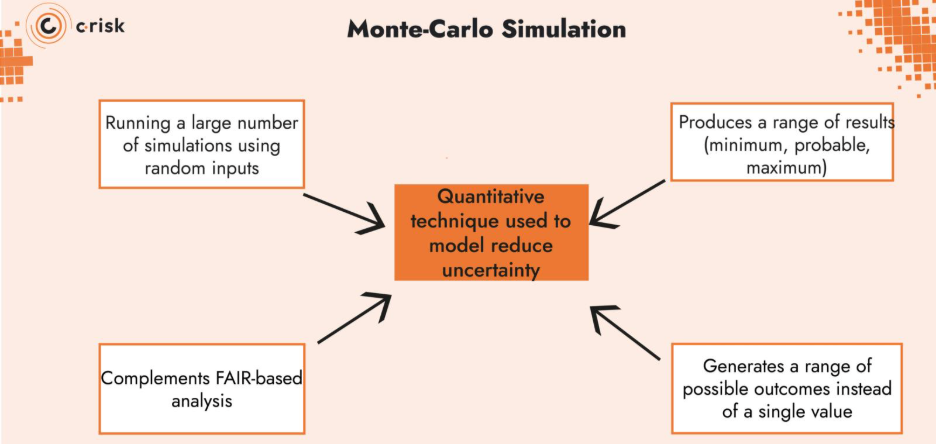
Monte Carlo Simulation
Monte Carlo simulation is a quantitative technique used to model reduce uncertainty by running a large number of simulations using random inputs that outputs a range with a minimum, most likely and maximum). It’s particularly useful when you’re dealing with variables that don’t have a single known value, but rather a range of possible outcomes, like how often a loss event might occur or how much it could cost.
This technique complements FAIR-based analysis, particularly when estimating Loss Event Frequency or Loss Magnitude.
Cost-Benefit Analysis
Not all security investments yield the same value. A cost-benefit analysis helps identify which initiatives deliver the most risk reduction per euro invested. This is particularly important in resource-constrained environments where CISOs need to justify cybersecurity spend against competing priorities.
A quantitative approach like FAIR makes this analysis possible by modeling both the expected loss from a risk scenario (Annualized Loss Exposure) and the potential reduction achieved by a proposed control. And a Monte Carlo simulation can further reduce uncertainty by providing a more accurate range.
Security teams can use this approach to:
- Compare competing mitigation strategies
- Rationalize legacy controls with minimal ROI
- Prioritize future investments based on impact per euro spent
CBA enables defensible decisions. Rather than asking for budget based on audit findings or peer comparisons, security leaders present clear, financial arguments rooted in business outcomes.
Scaling with a Platform
Point-in-time risk assessments provide only a temporary view of cyber risk. As threat landscapes evolve and business processes shift, these static assessments become outdated and lose their value for informing decisions.
A data-driven cyber risk management platform helps address this challenge by supporting continuous, data-driven prioritization. By combining quantitative analysis, threat intelligence, and third-party risk data, such platforms enable security and business leaders to align decisions around shared, measurable risk insights.
Key capabilities include:
- Dynamic data integration: Consolidates inputs from across security, IT, and business systems, including updated threat indicators, asset inventories, and control performance.
- Ongoing scenario evaluation: Updates key risk scenarios as new data becomes available, reducing reliance on periodic assessments.
- Support for resource prioritization: Helps teams allocate resources based on current risk exposure and potential business impact.
Using a platform shifts risk analysis from a periodic activity to a continuous process, helping organizations make better decisions about where to focus security efforts.
Measuring the Effectiveness of Resource Allocation
Once a data-driven prioritization model is operationalized, tracking progress is important for securing ongoing support at the executive level. The right metrics tie actions to outcomes and support decisions.
KPIs and KRIs
To evaluate whether resources are reducing risk effectively, organizations should track a focused set of key performance indicators (KPIs) and key risk indicators (KRIs). KPIs measure outcomes like risk reduction over time or cost per unit of risk reduced, while KRIs act as early warnings—highlighting changes in threat exposure or control performance. These metrics help ensure cybersecurity remains aligned with business objectives and risk appetite.
Benchmarking for Better Comparisons
Benchmarking helps organizations understand how their cybersecurity posture compares to industry peers or industry standards. This includes collecting data on the incident response times, security spend as a percentage of IT budget, or the cost of a cybersecurity incident for other businesses operating in your industry. Benchmarking provides valuable context for performance and investment decisions. It also helps identify over- or under-investment areas and supports continuous improvement.
Data-Driven Dashboards
Effective dashboards are decision-support tools. By communicating risk scenarios, control performance, and investment impact in financial terms, data-driven dashboards give stakeholders a shared frame of reference. They also help answer critical questions: Where are we spending resources? Are we addressing our highest-risk scenarios? What’s the ROI on those investments? When linked to business processes and risk appetite, dashboards highlight misalignments, track the effectiveness of mitigation efforts, and guide reallocation when needed. They also foster accountability.
Prioritization Powers Performance
Effective cybersecurity isn’t about defending everything—it’s about defending what matters most. In an environment of rising threats and limited resources, data-driven prioritization provides the clarity and structure organizations need to align cybersecurity investments with business-critical risks. By quantifying risk, incorporating business context, and continuously updating priorities, organizations can move beyond reactive firefighting and into strategic enablement.
When resource allocation is tied to measurable outcomes and financial impact, cybersecurity evolves from a technical burden to a strategic asset. CISOs gain a credible voice at the leadership table, boards gain visibility into risk trade-offs, and the entire organization benefits from a more resilient and cost-effective security posture.
Bring Focus to Your Cybersecurity Strategy with C-Risk
At C-Risk, we help security and risk leaders cut through the noise. We turn risk registers into action plans, investment proposals into business cases, and dashboards into decision tools. Our data-driven approach combines deep technical understanding with FAIR-based financial quantification, so you can focus on business growth
We help you:
- Map your digital assets to business processes
- Quantify cyber risk scenarios with FAIR
- Perform control efficiency assessments
- Build data-driven dashboards for decision support
- Scale risk management capabilities with automation and AI
