Cybersecurity Investment Strategy: From Cost Center to Business Driver
Cybersecurity investment is a critical pillar of enterprise risk management. Yet, many organizations still struggle to translate security spending into business-aligned outcomes. Traditional justifications such as improving security posture or meeting regulatory requirements often fail to satisfy executive stakeholders seeking clear return on investment.
According to ENISA’s 2024 report, EU organizations now allocate an average of 9% of their IT budgets to cybersecurity, while 90% anticipate an increase in cyberattacks in the coming year. With stakes this high, cybersecurity leaders must adopt a defensible, risk-based strategy, one that frames security in terms of financial risk reduction and operational resilience.
- Define ROI for cybersecurity: using financial and risk-based logic rather than abstract maturity models
- Quantify impact of security investments: with FAIR™ and other models to express impact in economic terms
- Evaluate investment performance: by comparing expected loss reduction to the cost of control
- Prioritize spend: focusing on high-leverage controls aligned with business-critical risks
- Report outcomes strategically: with metrics that resonate with CFOs, boards, and investment committees
The Problem with Traditional Security Metrics
Cybersecurity reporting often fails to resonate with executive decision-makers because it emphasizes operational activity over business impact. Commonly reported indicators include:
- Volume of threats blocked
- Compliance audit scores
- Number of vulnerabilities patched
- Completion rates for training programs
These metrics are useful for tracking internal performance, but they rarely quantify how security investments influence organizational risk. As a result, security teams can find themselves at a disadvantage when competing for budget alongside departments that present investments in terms of financial return, efficiency, or growth.
The challenge becomes more acute when regulatory obligations increase spending pressure. Without a framework to express risk reduction in economic terms, it’s difficult to demonstrate how security funding contributes to the organization’s broader objectives — or to justify incremental investment in a constrained environment.
A Financial Framework for Security ROI
Quantifying Cyber Investments using FAIR
While regulatory compliance sets a minimum threshold for cybersecurity investment, this doesn’t translate to effective cyber risk management. To demonstrate strategic value, organizations need a structured approach to quantifying the financial impact of cybersecurity decisions.
The Factor Analysis of Information Risk (FAIR) methodology provides the missing link between cybersecurity activities and financial outcomes, enabling organizations to optimize both compliance and business risk reduction. Unlike maturity models that measure activity, FAIR quantifies risk in economic terms by decomposing risk it into two measurable components:
- Loss Event Frequency (LEF): How often will this type of incident occur?
- Loss Magnitude (LM): What will it cost when it happens?
By modeling risk in this way, FAIR enables direct comparison between cybersecurity initiatives and other business investments using the same financial language.
Calculating Annualized Loss Exposure (ALE)
At the outcome of a FAIR analysis to measure an organization’s Annualized Loss Exposure (ALE) — the estimated financial loss an organization faces from a specific risk over a 12-month period.
Basic ALE Calculation: Frequency (over one year) × Impact = Annual Expected Loss
Example 1 - High Frequency, Low Impact:
- Data breach incidents: 10 per year
- Average cost per incident: $50,000
- ALE: 10 × $50,000 = $500,000
Example 2 - Low Frequency, High Impact:
- Ransomware attack: Once every 3 years
- Average cost per incident: $2,000,000
- ALE: (1/3) × $2,000,000 = $667,000
Total Risk Exposure: $1,167,000 annually
This quantification allows for financially defensible decisions. For instance, if a security control costs $500,000 and is expected to reduce total exposure by 40%, it effectively reduces annual risk by $466,800 — offering a clear view of return on security investment.
Unlike compliance-driven models or maturity scorecards, FAIR supports evidence-based prioritization. It reframes cybersecurity as a risk management function with measurable economic outcomes, not just an operational concern.
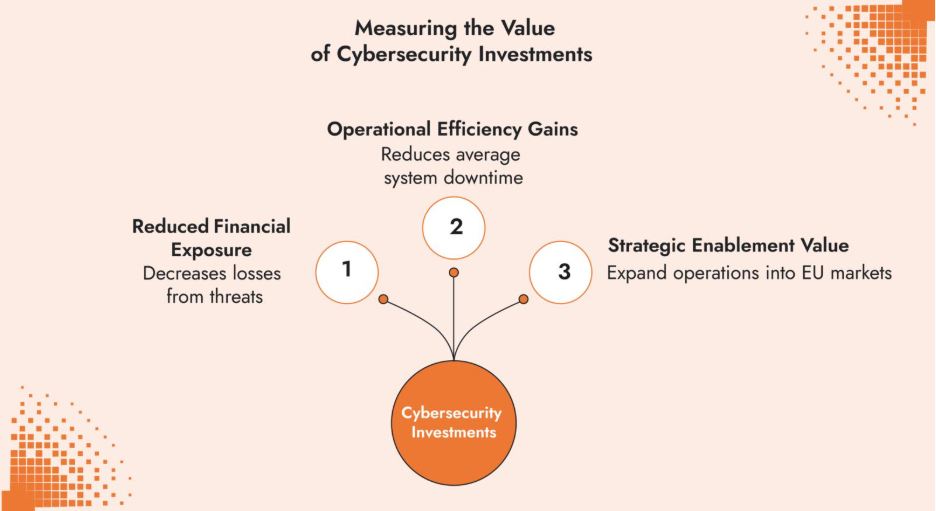
Measuring the Value of Cybersecurity Investments
A meaningful return on security investment can be measured in more than just threat mitigation. A financial perspective reveals three key value areas:
- Reduced Financial Exposure
Security controls can reduce the probability of a threat event or reduce the financial loss resulting in a loss event. For example, if implementing multi-factor authentication reduces account compromise incidents from 12 to 3 annually, and each incident costs $25,000, the annual loss reduction from implementing MFA is $225,000 annually.
- Operational Efficiency Gains
Automated incident response might reduce average system downtime from 8 hours to 2 hours, saving $350 per employee in staff costs. With 250 employees, that's $87,500 in operational savings.
If robust data protection controls allow an organization to expand operations into EU markets worth $5M annually, those controls enable new sources of revenue.
Optimizing Investments Through Risk-Based Prioritization
Security budgets need to be rationalized for decision-makers. With regulatory frameworks laying the foundation for cybersecurity, organizations can layer strategic risk reduction on top of mandatory investments. This ensures you meet any regulatory minimums while optimizing additional spending for maximum business impact.
Are you investing in controls that address your highest-probability, highest-impact risks rather than defending everything equally?
4-step prioritization model:
- Identify high-value assets and critical processes
- Map relevant threat scenarios and associated financial losses
- Evaluate control performance against those risks
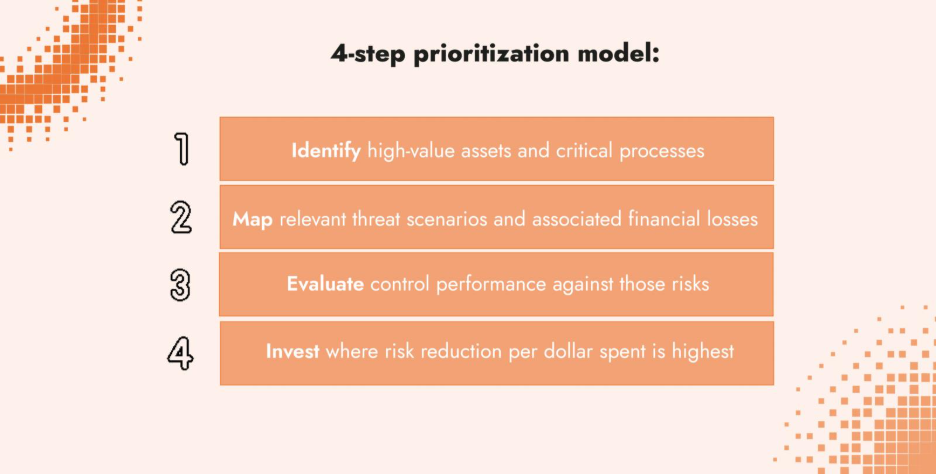
Control Optimization
Organizations with siloed cybersecurity programs often experience tool sprawl — overlapping technologies and controls that consume budget without materially reducing risk. These redundancies may not inform decision-making or improve outcomes, yet they still draw resources away from higher-value initiatives.
Regular control assessments can reveal:
- Redundancies across security tools with similar functionality
- Underutilized capabilities that offer little return
- Coverage gaps where small investments could significantly reduce risk
- Misaligned controls that no longer support current threat scenarios or business operations
- Opportunities for consolidation to reduce cost and complexity
Enterprise-Scale Efficiency
Breaking down silos across teams or business units can also uncover savings. Shared SOCs, integrated threat intel, and consolidated tooling often lead to lower cost per incident.
Communicating ROI to Decision-Makers
Framing Risk for Business Stakeholders
When presenting a cybersecurity budget to the board or executive committees, a CISO should be able to demonstrate how security initiatives and controls reduce financial risk and strengthen operational resilience.
Use framing that resonates:
- Financial Risk Mitigation: "This investment reduces our annual cyber risk exposure from $2.1M to $800K." Business Continuity
- Business Continuity: "Enhanced incident response capabilities reduce average downtime from 12 hours to 3 hours, preventing $400K in lost revenue per incident." Strategic Enablement
- Strategic Enablement: "Compliance with SOC 2 requirements enables us to pursue enterprise clients worth $15M in annual contract value." Regulatory Protection
- Regulatory Protection: " Improved data governance reduces GDPR exposure from €20M to €2M."
The Power of Narrative
Data alone rarely convinces anyone. It's the story behind the data that helps drives decisions, especially in the boardroom. Security leaders will gain the most buy-in when they are able to craft a narrative that ties cyber risk to business outcomes.
One of the most effective storytelling tools in cybersecurity is the use of visual models, such as heat maps and 5x5 risk matrices. When designed thoughtfully, these visuals can contextualize risk in a way executives can immediately grasp.
But these tools must be supported by real data. A well-built heat map should visually reflect quantifiable risk exposure, such as Annualized Loss Exposure, not just qualitative severity ranking.
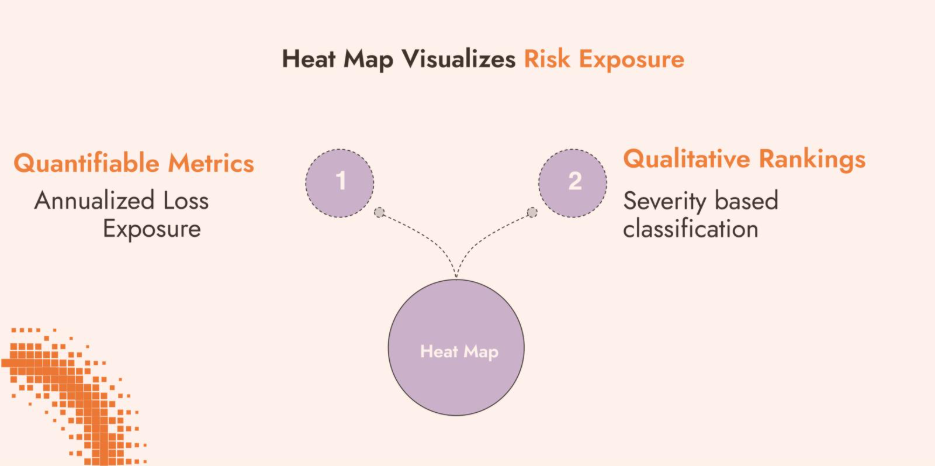
- Red = > €1M annualized loss
- Tell a cohesive story:
- Yellow = €250K–€1M
- Green = < €250K
- Show strategic alignment:
This bridges the gap between technical complexity and business clarity, allowing CISOs and security leaders to:
- Make ROI tangible:
“Here’s what we’re defending, why it matters financially, and where our investments make a difference.”
“These high-risk items directly impact revenue, operations, or compliance.”
“This control moves a red zone to yellow, reducing €700K in expected loss.”
Narratives rooted in economic risk and business relevance resonate far more with business leaders.
From A Cost Center to Strategic Asset
Cybersecurity ROI transforms security from cost center to strategic business driver. Organizations that implement financial risk quantification using a framework like FAIR benefit from:
- Risk-based investment recommendations that optimize spending across the highest-impact threats
- Executive buy-in by speaking the language of financial risk reduction rather than using an oversimplified or overcomplicated relative scale
- Data-driven prioritization that targets resources where they deliver maximum business value
- Security controls that enable growth opening up new markets or building strategic partnerships
FAIR methodology reduces uncertainty in security investment decisions, providing the data-driven foundation needed to support strategic decision-making.
Optimize Your Cybersecurity Investments with C-Risk
At C-Risk, we help large organizations quantify cyber risk and demonstrate financial value. We can help you address how to:
- Define your cyber risk management strategy
- Quantify and communicate your cybersecurity investments
- Optimize your security tool portfolio
- Build executive-ready data-driven risk dashboards
Our data-driven cyber risk management methodology delivers proven results across industries, enabling organizations to move from compliance-driven spending to strategic risk-based investment.
Ready to transform your cybersecurity investment approach? Connect with our team to explore how financial risk quantification can strengthen your security program's strategic value.
