DDRM (Data-Driven Risk Management): Revolutionizing your cyber risk approach with data
In the face of increasingly complex cyber threats, traditional risk management approaches—often subjective—are no longer enough. Data-Driven Risk Management (DDRM) offers a new direction: a more factual, continuous, and proactive strategy.
By leveraging the full potential of available data, DDRM enables a deeper understanding of risks, smarter security prioritization, and stronger organizational resilience. A clearer, fairer, and more effective approach.
- Fact-based decisions: DDRM (Data-Driven Risk Management) replaces subjective assessments with objective data analysis to identify, evaluate, and treat cyber risks.
- Key strategic advantages: It offers improved objectivity, process automation, continuous adaptation to threats, and predictive capabilities to anticipate incidents.
- Comprehensive data leverage: This approach relies on collecting and analyzing diverse data (technical, threat, business) for a 360-degree view of risks.
- Informed security steering: DDRM transforms risk management into a strategic lever, enabling prioritized actions and optimized cybersecurity investments.
- Shift to proactivity: Adopting DDRM means moving from reactive risk management to a proactive and continuous posture, crucial in the face of constantly evolving cyber threats.
Principles and methodology of DDRM
Data-Driven Risk Management is a strategic approach that places data at the heart of the cyber risk management process.
Comprehensive definition of DDRM and its components
DDRM (Data-Driven Risk Management) is a risk management methodology that uses quantitative and qualitative data analysis to identify, assess, treat, and monitor cyber risks continuously and informedly. Unlike traditional approaches that may rely on subjective assessments or static compliance checklists, DDRM is based on tangible facts and evidence derived from data.
The key components of DDRM include:
- Data Collection: Sourced from multiple origins (event logs, vulnerability analyses, threat intelligence, financial data, business processes, etc.).
- Data Analysis: Using statistical techniques, artificial intelligence (AI), and machine learning (ML) to identify trends, anomalies, and correlations.
- Risk Modeling: Creating quantitative models to assess the probability and financial impact of risk scenarios.
- Data Visualization: Presenting information clearly and actionably through dashboards and reports.
- Automation: Automating data collection, analysis, and reporting processes for increased efficiency.
- Informed Decision-Making: Using data-driven insights to prioritize security investments, adapt controls, and respond to incidents.

Fundamental principles of the data-driven approach
The data-driven approach to risk management is based on several fundamental principles:
- Objectivity: Decisions are based on measurable data rather than intuitions or opinions.
- Continuity: Risk management is an iterative and continuous process, fueled by a constant flow of data.
- Contextualization: Risks are assessed within the specific context of the organization, its industry, and its strategic objectives.
- Prediction and Anticipation: Analyzing past and current trends allows for the anticipation of future threats and proactive preparation.
- Measurability: The effectiveness of security measures and the return on investment (ROI) of cybersecurity initiatives can be measured. Necessary data and its collection

To implement an effective DDRM strategy, a wide variety of data must be collected and centralized:
- Technical Data: System and application logs, alerts from security tools (SIEM, EDR, IDS/IPS), vulnerability scan results, asset configurations.
- Threat Data: External and internal threat intelligence, indicators of compromise (IoCs).
- Business Data: Information on critical processes, the value of informational assets, potential financial impacts of service interruptions.
- Past Incident Data: Analysis of previous incidents to understand attack patterns and weaknesses.
- Compliance Data: Information related to regulatory requirements and audits.
Collection should be automated as much as possible, using connectors and APIs to aggregate data into a data lake or a security-dedicated data warehouse.
Required technical and organizational architecture
Implementing DDRM requires a suitable architecture:
- Technical: Big Data analytics platforms, visualization tools, SIEM/SOAR solutions, and potentially Cyber Risk Quantification (CRQ) platforms. The infrastructure must ensure the quality, integrity, and security of the collected data.
- Organizational: Close collaboration between IT, security, data science, and business departments is essential. Clear roles must be defined (e.g., Security Data Analyst, Quantitative Risk Manager). A data-driven culture must be promoted within the company.
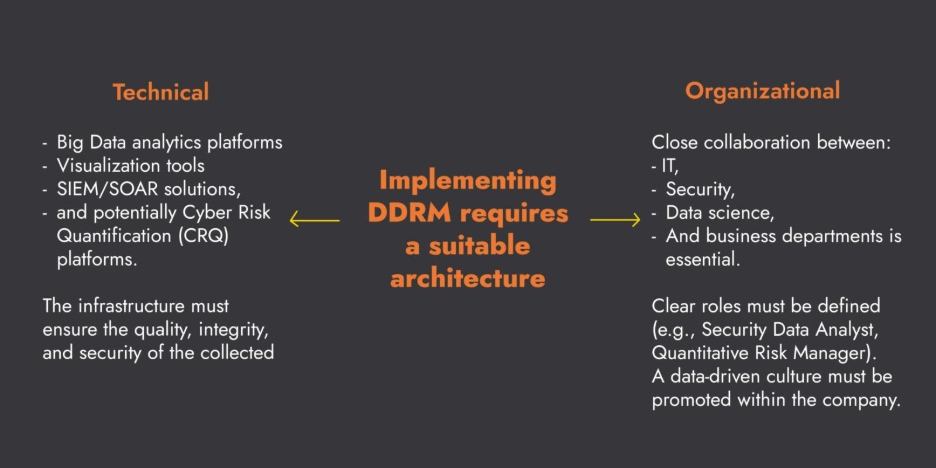
Implementing DDRM requires technical and organizational architecture
Advantages over traditional approaches
DDRM offers significant advantages over traditional risk management methods.
Objectivity vs. subjectivity
Traditional approaches often rely on qualitative assessments (low, medium, high risk) which can be subjective and vary from one assessor to another. DDRM, by basing itself on concrete data and quantitative models, introduces a level of objectivity allowing for more reliable comparisons and more rational decisions. (This topic will be explored further in our next article: Risk Quantification vs. Qualitative Approaches).
Automation and reproducibility
DDRM promotes the automation of risk data collection, analysis, and reporting. This not only saves time and reduces human error but also ensures the reproducibility of assessments. Reports can be generated regularly with consistent Key Risk Indicators (KRIs).
Continuous adaptation to the evolving threat landscape
The cyber threat landscape evolves at a breathtaking pace. Traditional approaches, with their periodic assessment cycles, struggle to keep up. DDRM, through continuous data analysis and threat intelligence feeds, allows for near real-time adaptation of defense strategies and dynamic updating of risk profiles.
Predictive and anticipatory capabilities
By analyzing historical trends, weak signals, and abnormal behaviors, DDRM, often coupled with AI and Machine Learning techniques, offers predictive capabilities. It becomes possible to anticipate the most likely types of attacks, identify the assets most likely to be targeted, and implement preventive measures before an incident occurs.
Use cases and implementation in large organizations
DDRM finds concrete applications in many aspects of cyber risk management within large structures.
Risk scenario analysis with concrete examples
DDRM allows for more precise modeling and analysis of risk scenarios.
- Example in Finance: A bank can use DDRM to simulate the financial impact of a ransomware attack on its critical payment systems, based on transaction data, estimated remediation costs, and potential revenue losses.
- Example in Energy: An energy provider can assess the risk of an attack on its industrial control systems (SCADA) by analyzing equipment vulnerabilities, past intrusion attempts, and the potential impact on distribution.
- Example in Healthcare: A hospital can use DDRM to quantify the risk associated with a patient data breach, considering regulatory fines (e.g., HIPAA), notification costs, and reputational damage.
These analyses provide a better understanding of exposures and justify targeted security investments.
Integration with detection and monitoring systems
DDRM naturally integrates with detection (SIEM, EDR, NDR) and continuous monitoring systems. Alerts and events from these systems feed into DDRM models, thus refining risk assessment in real time. Conversely, priorities identified by DDRM can help fine-tune detection rules and alert thresholds.
Application in different sectors (Finance, Energy, Healthcare)
Although the principles of DDRM are universal, its application can be tailored to the specifics of each sector:
- Finance: Strong emphasis on regulatory compliance (e.g., DORA, Basel III), fraud protection, and business continuity. DDRM helps quantify exposure to systemic and operational risks.
- Energy: Securing critical infrastructure, protecting SCADA/ICS systems, managing supply chain risks. DDRM enables modeling of cascading impacts.
- Healthcare: Protecting sensitive patient data (e.g., HIPAA), security of connected medical devices, managing risks related to the availability of hospital information systems.
Implementation challenges and success factors
Transitioning to DDRM is a major project with its own set of challenges.
Managing cultural change
Shifting from a qualitative approach to a quantitative, data-driven one requires a change in mindset at all levels of the organization. It is necessary to overcome resistance to change, train teams, and promote a culture of data-based decision-making.
Data quality and availability
The success of DDRM intrinsically depends on the quality, completeness, and availability of data. Incomplete, incorrect, or siloed data can distort analyses and lead to poor decisions. Implementing data governance processes is crucial.
Necessary skills
Implementing and operationalizing DDRM require advanced skills in data analysis, statistical modeling, cybersecurity, and risk management. Companies must invest in training their existing teams or recruit new talent (data scientists, quantitative risk analysts).
Alignment with overall strategy
The DDRM strategy must be closely aligned with the company's overall strategy and business objectives. Risk indicators and security priorities must reflect what matters most to the organization.
How C-Risk can support you
At C-Risk, we help large organizations better understand, quantify, and manage their cyber risks using data. Our specialty: turning the complexity of cyber risk into clear, evidence-based decisions.As experts in frameworks like FAIR (Factor Analysis of Information Risk), we support you in:
- Define your DDRM strategy:
A customized roadmap, aligned with your objectives and context. - Identify and collect relevant data:
Select the right sources and set up collection mechanisms. - Model and quantify your cyber risks:
Transform your data into actionable financial insights. - Implement dashboards and reporting:
Communicate effectively about your risks to all stakeholders, including executive management and the board of directors. - Train your teams:
Build the skills necessary for data-driven risk management. - Support cultural change:
Embed a data-driven culture for cybersecurity.
DDRM is not just a new methodology; it is a fundamental transformation in how cyber risks are perceived, managed, and communicated. By adopting DDRM, you turn risk management into a true lever for performance and resilience.
