Defining and communicating cyber risk appetite
Cybersecurity has become a central pillar of corporate governance. As organizations pursue digital transformation, expand into new markets, and increase third-party collaboration, they encounter not only opportunity but also new forms of cyber risk. The challenge is not whether to accept risk, but how much to accept, under what conditions, and in pursuit of what reward.
This is where the concept of cyber risk appetite plays a critical role. However, the UK’s National Cyber Security Centre (NCSC) observed in one study that, while many organizations reference appetite in policies, they fail to use it as a practical tool for supporting decisions. When defined, measured in financial terms, and actionable, risk appetite provides clarity to boards and executives on acceptable exposure and the trade-offs between resilience, compliance, and innovation.
- Cyber risk appetite is a board-level decision
It defines how much potential loss an organization is willing to accept in pursuit of growth, innovation or operational continuity.
- Financial framing makes risk appetite actionable
Qualitative “low/medium/high” language is subjective and without clear objectives.
- Scenario-based risk appetite statements clarify risk vs reward
Boards can decide what is acceptable risk versus unacceptable risk with data-driven metrics.
- Operational drivers connect strategy to execution
KRIs such as data exposure, privileged access, and resilience measures ensure appetite is monitored in practice.
- FAIR methodology sharpens cyber risk appetite statements
This shared financial language helps align boards, executives, and security teams, and demonstrates resilience to regulators, investors and customers.
Defining cyber risk appetite
Risk appetite represents the amount and type of cyber risk an organization is willing to pursue or retain in order to achieve its objectives. It is not set by the CISO or security function alone, but by leadership as a business decision.
At its core, appetite answers a simple governance question:
“How much loss are we willing to tolerate in exchange for growth, innovation, or operational continuity?”
Importantly, appetite is not static. It may differ across risk categories:
- An organization may be averse to regulatory breaches.
- Cautious about reputational risk.
- Open to certain financial exposures where upside potential outweighs downside risk.
- Hungry for innovation risk when experimentation drives competitive advantage.
These distinctions should be explicit so that boards know where the business is willing to push boundaries and where it must remain conservative.
Framing appetite in financial terms
The most effective way to define risk appetite is in financial terms. Rather than relying on qualitative ratings like high, medium, or low, organizations should translate cyber incidents into potential monetary impact. This enables direct comparison with other business initiatives.
Example: A retailer launching a new e-commerce channel anticipates $10 million in new revenue over three years. Alongside that upside sits a credible downside: a customer data breach could cost $1 million in fines, remediation, and reputational damage. Accepting risk exposure is not reckless; it is a deliberate business decision to balance risk and reward.
Practical steps include:
- Quantifying plausible cyber risk scenarios such as ransomware, data breaches, or outages
- Expressing potential losses relative to revenue or income, ensuring comparability with materiality thresholds
- Setting appetite at levels that support strategy while avoiding exposures that threaten financial stability
Linking appetite to operational drivers
Financial framing should be grounded in operational drivers that make risk appetite measurable and actionable. Boards and audit committees need to understand which factors increase or decrease exposure, and how security teams are managing them.
Examples of operational drivers include:
- Data exposure: volume of customer records held and whether they are encrypted
- Access management: number of administrators or third parties with privileged access
- Resilience measures: system redundancy, recovery readiness, and incident response capacity
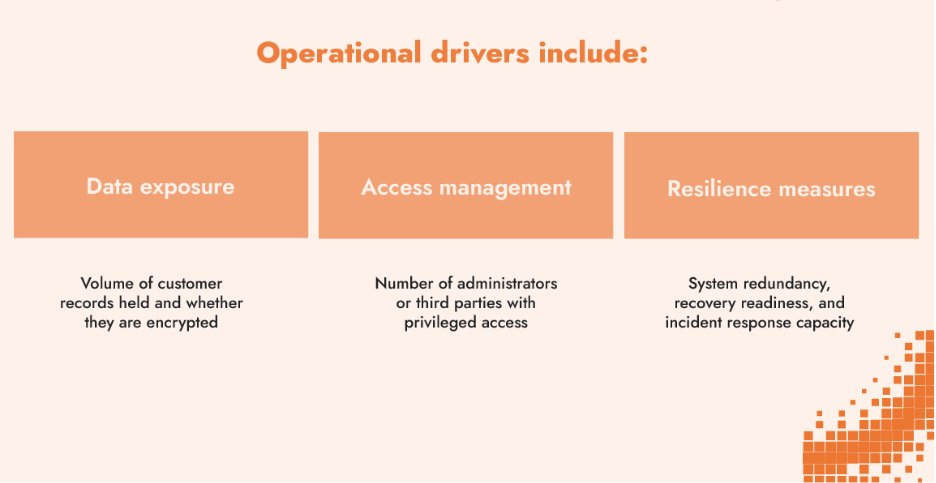
By monitoring these levers, organizations can demonstrate how appetite is being respected in practice. Key risk indicators (KRIs) become the bridge between strategy at the top and operations on the ground.
Measuring appetite through scenarios
The most practical way to embed cyber risk appetite into governance is through scenarios. A scenario takes a real initiative and frames both its potential upside and downside, asking: “Is this level of loss acceptable given the benefits we expect?”
- An e-commerce business accepts risk for up to 1 million PII records lost in return for the launch of a new site with $10 million in projected revenue over the course of a holiday weekend.
- A national emergency hotline, by contrast, may have zero appetite for downtime. Outages of even a few seconds are unacceptable. Here, staffing levels, technical redundancy, and call-center resilience are critical KRIs.
Scenarios ensure appetite is not a vague statement but a decision-making tool. They also allow appetite to vary across business units, initiatives, or categories of risk. This is exactly the challenge the NCSC highlights: risk appetite needs to guide informed business decisions.
Making risk appetite actionable: The FAIR perspective
Jack Jones, Chairman Emeritus of The FAIR Institute and creator of the FAIR (Factor Analysis of Information Risk) model, offers a clear way to sharpen risk appetite statements to make them more useful. In his RSA Conference talk on risk appetite, he emphasized the need for a creating a “working” risk appetite, one that translates directly into loss event scenarios, thresholds, and governance decisions.
He gives five characteristics for useful risk appetite statements, so that they can support decisions:
- Be realistic and actionable
- Provide clarity in expectations
- Improve focus in risk management efforts
- Improve communication with stakeholders
- Reduce the potential unacceptable loss
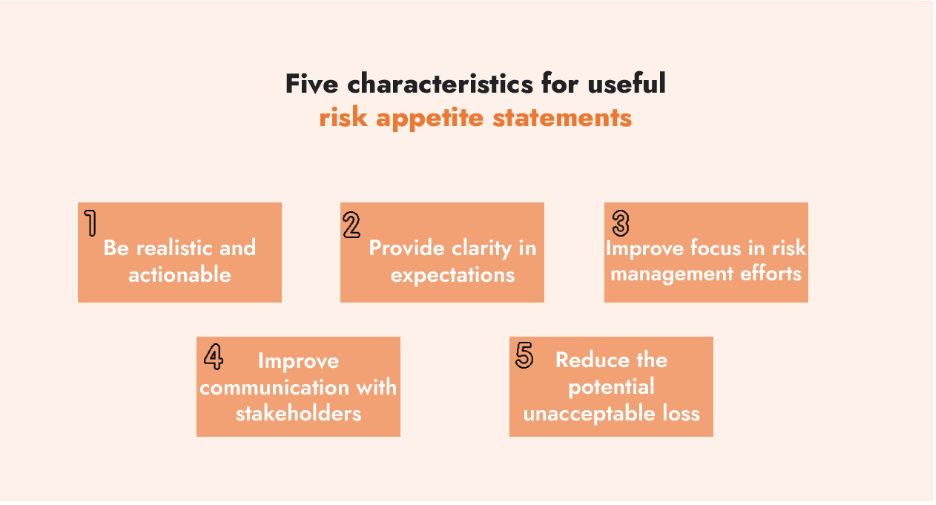
According to FAIR, risk is defined as the probable frequency and probable magnitude of future loss. Building on that, a useful appetite framework needs to be specific, measurable, and tied to the organization’s most critical assets.
From vague statements to actionable boundaries
According to Jones, many risk appetite statements fail because they are not actionable or clear on thresholds. Below are some examples of risk appetite statements that, while they are better than nothing, don’t support any decisions or set clear boundaries. For example:
- “We have a low appetite for customer data loss.” — signals intent but is ambiguous
- “We don’t want to exceed $10 million in losses.” — clearer, but still incomplete without knowing the type of loss, the assets at stake, or the timeframe
What’s needed is an appetite statement that provides decision boundaries. For example:
“We will not accept more than a 5% probability of losses exceeding $5 million from customer PII disclosure in any 12-month period.”
This establishes a measurable threshold that executives and security leaders can use to guide resource allocation and risk treatment.
Scenario-based appetite
In FAIR terms, appetite should always be linked to specific loss event scenarios. This ensures clarity and alignment between appetite and the real risks the organization faces.
Scenarios could include:
- Disclosure of customer PII
- Outage of a critical business process
- Failure to meet regulatory obligations
By anchoring appetite to scenarios, organizations can express different appetites for different contexts. For example, an enterprise may accept higher appetite for innovation risk but zero appetite for extended downtime of a payment processing system.
Focusing on the crown jewels
Not all risks are equal. Appetite should be defined most rigorously for your “crown jewels.” These are the assets and processes most critical to your organization’s mission, operations, or financial stability.
Anything that threatens the crown jewels beyond the defined threshold must be treated as a priority for remediation. How an organization defines and protects its crown jewels is both a reflection of its risk appetite and a signal of its risk maturity.
Reinforcing appetite through governance
Finally, appetite must be sustained through governance processes that ensure alignment over time. This includes:
- Policies and standards — e.g., maintaining asset inventories, requiring awareness training for privileged users
- Processes and controls — assess control performance and manage scenarios within the risk threshold
- KRIs and KPIs — measurable indicators to detect when conditions drift outside appetite and to trigger corrective action and show improvements
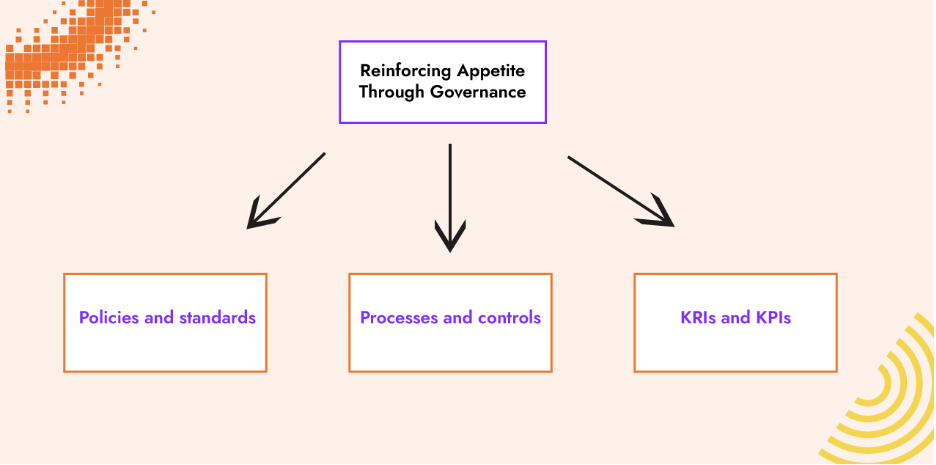
Through these mechanisms, cyber risk appetite becomes more than a written statement. It evolves into an operational framework that defines decision-making boundaries, guides investment, and reduces the probability of unacceptable loss.
Appetite, tolerance, and capacity
It is important to distinguish between appetite, tolerance, and capacity. Risk appetite reflects the level of loss the business chooses to accept. A risk appetite is also referred to as risk tolerance. This is the line drawn in the sand where an organization is willing to accept risk. The risk capacity is the absolute maximum a business could sustain without jeopardizing its viability.
A helpful way to visualize the difference between risk appetite and capacity is to imagine standing on a cliff’s edge. The very edge of the cliff represents your maximum tolerance, the absolute limit before you fall.
Risk appetite, however, is not about living at the edge. It is the deliberate distance you choose to keep from the edge. A prudent person may stay several steps back to ensure safety, while someone with an anchored rope and harness may feel comfortable moving a little closer. The rope in this analogy represents the controls, redundancies, and safeguards that give confidence to operate nearer to the edge without falling.
Tolerance defines the outer boundary of survival, but appetite reflects a conscious choice of how much distance a business wants to maintain and what additional protections, or controls, are needed to move closer to opportunity without courting catastrophe.
Reviewing and communicating risk appetite
Risk appetite should be reviewed regularly. An annual reassessment is the minimum cadence. The risk appetite should also be reviewed whenever:
- Strategic objectives change (e.g., expansion into new markets)
- Major initiatives are launched (e.g., mergers, acquisitions, digital transformation)
- Financial conditions shift (e.g., cash reserves fall or surge)
- Threat landscape changes significantly
Clear communication is critical. Risk appetite statements should be defined by leadership and clearly communicated to business owners and security and risk teams. They can then build scenarios and monitor KRIs to build actionable reports.
When done well, risk appetite ceases to be a paper exercise. It becomes a living governance mechanism that enables boards to balance growth with resilience, and security leaders to align their actions with business strategy.
Operationalizing risk appetite for business resilience
The NCSC's observation that most organizations fail to operationalize their risk appetite statements points to a fundamental challenge: bridging the gap between boardroom intentions and operational reality. This gap closes when financial quantification meets scenario-based risk appetites.
The real test comes when the next major initiative lands on the board's agenda. Will the risk appetite framework inform their decision, or will it be forgotten in the enthusiasm for growth? The answer often depends on whether the organization has built the muscle memory of asking: What's the potential loss? Is it within our stated risk appetite? Do we have the controls to operate at this level of exposure?
When these questions become routine, cyber risk appetite becomes the mechanism through which boards balance innovation with resilience. Security teams can align their efforts with business strategy. What remains is implementation, turning risk appetite from a governance process into a competitive advantage.
How C-Risk helps you define and operationalize cyber risk appetite
C-Risk enables organizations to transform risk appetite statements into actionable decision frameworks by combining expert advisory, quantitative methods and purpose-built technology.
We help you:
- Develop clear, financially quantified risk appetite statements that boards and security leaders can use to guide initiatives
- Apply FAIR™ methodology to set measurable thresholds for different loss scenarios
- Identify and protect your crown jewels with appetite-aligned controls
- Build KRIs that bridge the gap between strategic appetite and operational reality
- Embed risk appetite into governance processes that guide real business decisions
C-Risk expertise together with SAFE’s cyber risk management platform operationalizes these frameworks, ensuring your security strategy can balance growth and resilience using a data-driven approach.
