Cultural transformation: From compliance to active risk management
For decades, cybersecurity has been framed as a compliance challenge. Organizations raced to meet regulatory requirements, pass audits, and obtain certifications. While these efforts created a baseline of security, they also fostered a checklist mentality: once the box was ticked, the job was done. This mindset is no longer sustainable.
Gartner predicts that by 2030, widely adopted cybersecurity frameworks will measure success by behavioral change and cultural maturity, not by compliance metrics. Cyber incidents now have systemic consequences that can disrupt global supply chains, erode customer trust, and trigger massive financial losses. In this environment, organizations need is cultural transformation when it comes to addressing cybersecurity. A central challenge for cyber-aware executives and CISOs is how to lead the transition from a compliance approach to an active cyber risk management culture across the enterprise.
- Compliance frameworks establish a baseline — moving beyond checklist logic is critical for developing a risk-based approach and building resilience.
- Awareness depends on governance — cross-functional processes and clear communication embed cyber risk into company culture.
- Active risk management is proactive, informed, and continuous — risk must be quantified, prioritized, and integrated into decision-making.
- Cyber risk awareness is a long-term process — cultural change takes time, but structured methods and data-driven assessments deliver quick wins that reduce uncertainty and build momentum.
Diagnosing the compliance mindset
To strengthen governance, leaders need to recognize the weaknesses of a compliance-only mindset. Passing audits and achieving certifications can create a false sense of security. While external validation proves that minimum requirements are met, it does little to prepare an organization for fast-moving threats, systemic incidents, or reputational damage.
A compliance-driven posture narrows cybersecurity to a bureaucratic exercise. It satisfies auditors but fails to build resilience across the enterprise.
Compliance-driven approaches to security are characterized by:
- Checklist logic – security tasks aligned to audit requirements
- Reactivity – action taken after incidents, rather than in anticipation of them
- Minimal accountability – responsibility delegated to IT, not shared across the business
According to the SANS Security Awareness & Culture Maturity Model this is called the “Compliance-Focused” stage, where training is limited to an annual or ad hoc basis and employees remain unclear about policies and their personal role in protecting assets.
The losses resulting from a compliance-focused maturity model are not theoretical. Major breaches disrupt daily life, businesses and governments. Across all industries, airlines, hospitals, and banks have all been impacted. It’s clear that while most large organizations have a cyber-compliant program, they can reduce the impact of a breach and strengthen resilience with a data-driven and risk-based strategy.
ENISA highlights that 80% of SMEs believe a serious cyber incident would have a severe impact on their business, and 57% fear it could put them out of business. Compliance isn’t going to keep an SME from closing up shop when they are attacked.
This cultural shift cannot be delegated to IT or compliance functions. It must be championed by executives, boards, and managers who set expectations, model behaviors, and integrate cyber risk into strategic decision-making. Only then can organizations evolve from compliance to resilience.
What does a cultural shift look like?
In contrast, active risk management reframes cybersecurity as:
- Proactive – anticipating and mitigating risks before they materialize
- Informed – using data to quantify exposure and prioritize resources
- Continuous – embedding resilience into day-to-day decisions and governance
Designing multi-level awareness programs
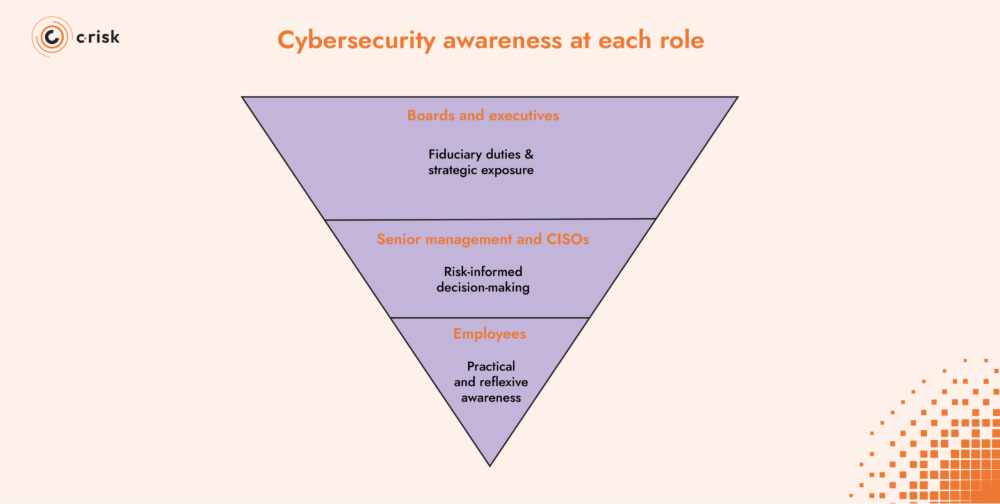
Cybersecurity awareness at each role
Building cybersecurity awareness can be approached differently by different roles across the enterprise with content that is relevant, measurable, and tied to business outcomes.
- Boards and executives: Awareness at this level must focus on fiduciary duties and strategic exposure. Directors need clarity on how cyber incidents translate into financial loss, regulatory scrutiny, and resilience gaps. Frameworks such as the NACD Cyber-Risk Oversight Handbook reinforce that cyber risk is a board responsibility.
- Senior management and CISOs: For those leading business units and security teams, awareness must center on risk-informed decision-making. This is where the FAIR model (Factor Analysis of Information Risk) becomes indispensable. By quantifying cyber exposure in financial terms, CISOs and senior managers can prioritize initiatives, allocate budgets effectively, and demonstrate resilience in language aligned with enterprise risk management.
- Employees: For the broader workforce, cybersecurity awareness needs to be practical and reflexive. People are the first line of defense. The ability to recognize a phishing email or knowing how to report an incident quickly can build resilience. ENISA’s AR-in-a-Box provides concrete resources for SMEs, including KPIs and gamified exercises to make awareness both engaging and measurable.
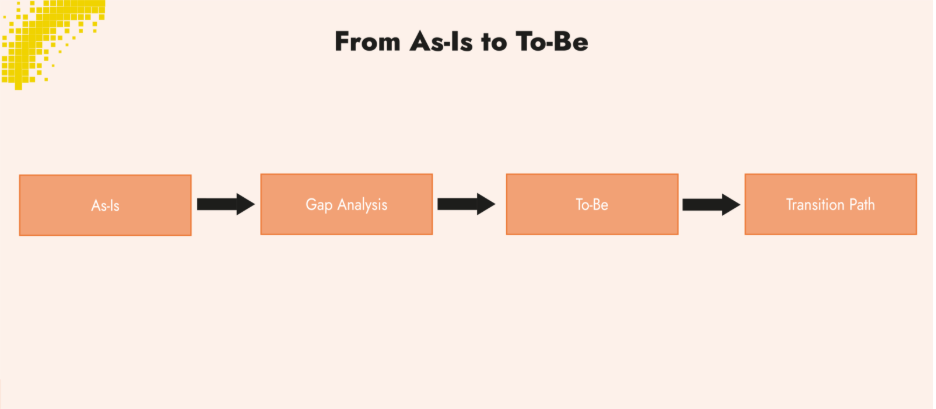
Defining awareness by role is important, but it is only a snapshot of the present. To embed risk management into culture, organizations need a structured way to evolve awareness programs over time. This is where the change management lens — from as-is to to-be — becomes useful.
From as-is to to-be
Like other organizational change initiatives, cybersecurity awareness requires a structured journey. It is effective to take an as-is / to-be approach: first diagnosing the current state, then defining the desired target, and finally managing the transition. This acknowledges that cultural change does not happen overnight; it takes time, leadership commitment, and sustained reinforcement.
- As-Is: The baseline state of the organization’s cybersecurity practices, awareness and culture. Assessing this current level provides clarity on strengths, weaknesses, and the distance to the desired target.
- Gap Analysis: The process of identifying the differences between the current state and the desired target. This includes reviewing whether the right controls, practices, and governance processes are in place to support cultural maturity.
- To-Be: The defined target state, where the cybersecurity program is risk-driven and treated as a strategic enabler. Data-driven risk management is embedded into governance and daily operations, and maturity is tracked with clear performance indicators.
- Transition Path: Pilot new approaches, measure engagement using ENISA’s KPIs, and reinforce progress over time. Leadership sponsorship and cross-functional collaboration are critical to sustaining change.
Awareness, framed in this way, becomes a driver of cultural transformation. It equips decision-makers at every level to understand, own, and act on cyber risk in a manner consistent with the organization’s broader governance and resilience objectives.
Transformation takes time
Cultural change does not happen overnight. The SANS 2025 Security Awareness Report shows that building a mature program requires sustained investment:
- 3–5 years to change behavior across the workforce.
- 5–10 years to embed culture organization-wide.
- 10+ years to reach optimization, where culture actively reduces risk.
This is why awareness cannot be treated as a campaign. It is a continuous program that evolves with new threats, regulatory expectations, and business priorities.
At the same time, adopting Data-Driven Risk Management (DDRM) methods can accelerate progress. A structured as-is assessment can highlight quick wins and low-hanging fruit.
For example, identifying gaps in reporting channels or misaligned controls that can be addressed immediately. By quantifying cyber risk with approaches such as FAIR, organizations also reduce uncertainty in decision-making. This gives executives greater confidence in allocating resources and demonstrates early value, even as longer-term cultural maturity develops.
In other words, transformation does not mean waiting years to see impact. Early wins, backed by data, build the momentum and leadership support needed for cultural change to take root.
Building a shared and sustainable risk culture
Cybersecurity culture emerges when a risk-based and data-driven approach becomes the default way of working across the enterprise. The NACD and ISA Cyber-Risk Oversight Handbook underlines that boards have a fiduciary duty to oversee cyber risk, not as a technical detail but as a core element of governance. That expectation extends throughout the organization: culture is shaped by leadership, reinforced by processes, and sustained through accountability.
Key enablers include:
- Values and principles: Establish clear expectations — transparency, accountability, and shared responsibility for cyber risk.
- Integration into processes: Embed risk-based assessments into procurement, development, HR, and vendor management. Accepting risk can drive value creation.
- Storytelling and communication: Share real incidents and lessons learned, celebrate quick reporting of threats, and normalize speaking up. ENISA stresses the importance of post-incident reviews as opportunities to refine procedures and strengthen resilience.
- Leadership by example: Culture comes from the top. When leaders visibly prioritize cyber risk, it signals its strategic importance to the entire workforce.
Research consistently shows that the most effective programs focus on simplifying policies, strengthening cross-department partnerships, and aligning cybersecurity with business goals. In governance terms, that means treating cyber not as an operational burden but as an essential condition for resilience and trust.
Human capabilities drive cybersecurity
Cybersecurity is the “practice of deploying people, processes, policies and technologies to protect organizations, their critical systems and sensitive information from digital attacks.” In this definition from Gartner, people are the first line of defense. Any employee, with the effective awareness training has the ability to stop an attack. When we talk about control performance, the workforce is an agile and responsive control to invest in.
Gartner highlights this shift with its focus on Security Behavior and Culture Programs (SBCPs), noting that the effectiveness of security functions will increasingly be measured by behavioral change and cultural maturity rather than compliance activity alone. In other words, resilience depends on how well people understand, own, and act on risk.
Building these capabilities requires continuous investment in:
- Awareness programs for the workforce: Practical, engaging, and role-specific training that normalizes secure behaviors and gives employees the confidence to act.
- Professional training for security teams: Skills in Data-Driven Risk Management (DDRM), risk quantification (FAIR), and risk communication ensure CISOs and their teams can provide leadership with actionable, financial insight.
- Cross-functional preparedness: Embedding cyber considerations into procurement, vendor management, HR, and development ensures risk awareness is distributed across the enterprise, not confined to IT.
- Agility and responsiveness: Programs must evolve with threats. Phishing simulations, crisis exercises, and iterative learning loops help organizations adapt quickly rather than relying on annual training cycles.
Resilience is a human capability. Technology can mitigate risk, but people equipped with the right knowledge, training, and judgment can create the cultural foundation that transforms cybersecurity into a strategic asset.
From compliance to resilience
Cyber resilience is enterprise-wide and governance-driven. It depends on every level of the organization acting as a line of defense: boards and executives setting expectations, managers embedding risk into processes, and employees applying awareness in daily work. Certification and audits are a solid baseline, but resilience requires treating cyber risk as a business capability that is governed, measured, and continuously improved.
As Gartner notes, the effectiveness of security functions will increasingly be viewed through the lens of maturity and behavior change, not compliance activity. FAIR and Data-Driven Risk Management provide the methods to quantify risk in financial terms and align it with enterprise risk management, while tailored awareness and training programs develop the human capabilities that make resilience possible.
Organizations that succeed are those that integrate cyber into governance, strategy, and culture, managing it with the same discipline as finance or operations.
C-Risk perspective
At C-Risk, we help organizations move beyond compliance and embed cyber risk into governance and culture. Our as-is / to-be assessments give risk and security leaders a clear picture of current maturity and identify the practical steps needed to reach their target state. Through Data-Driven Risk Management (DDRM) as a Service, we provide continuous visibility into loss exposure and the performance of controls, enabling better decisions and faster response to change. And with C-Risk Education and training programs, we build capabilities in FAIR, DDRM, and risk communication so that executives, CISOs, and managers can quantify cyber risk and integrate it into enterprise strategy.
Cultural transformation is a long-term journey, but with the right methods and training, organizations can realize quick wins, reduce uncertainty, and build the enterprise-wide resilience that regulators, customers, and boards now expect.
