Cyber governance maturity model
An organization’s ability to manage cyber risk depends not only on the controls it implements but on how effectively and consistently those controls are governed.
A cyber governance maturity model helps leaders assess where their organization stands today, define where it needs to be, and chart a roadmap for improvement. In this article, we explore what cybersecurity maturity means, how frameworks like NIST and COBIT define it, and how a data-driven, risk-informed approach can help organizations move from reactive compliance to proactive governance.
- Maturity models help organizations answer three key questions: Where are we now? Where do we want to be? How do we get there?
- ISO 37004, NIST CSF 2.0, and COBIT 2019 define cyber maturity through their process, effectiveness, and continuous improvement.
- The As-Is / To-Be approach creates a data-driven roadmap for improving governance, oversight, and resilience.
- FAIR methodology helps communicate the strengths and weaknesses of your program in business terms
- Moving from compliance to proactive governance enables boards and executives to demonstrate accountability and strengthen enterprise resilience.
What is a maturity model in cybersecurity?
In cybersecurity governance, maturity describes the degree to which an organization’s cyber risk oversight is structured, effective, and continuously improved. It assumes certain controls are in place because they are generally effective. In addition to controls, your maturity can also be measured by how you address cyber risk. Frameworks describe what controls should exist; maturity models help answer how well it is being done, and how far it still needs to go.
ISO’s recent guidance on governance maturity, ISO 37004:2023, defines maturity as the extent to which governance principles are consistently applied, effective in achieving outcomes, and efficient in execution. While not cybersecurity-specific, these principles are directly applicable: in cyber risk, maturity is about whether boards and executives demonstrate clear accountability, effective oversight, and adaptive improvement.
From a cybersecurity perspective, a maturity model will answer three questions:
- Where are we today?
- Where do we want to be?
- How do we get there?
Why maturity models matter
There is no shortage of guidance on cybersecurity. Regulators, governments, and standards bodies publish countless regulations and frameworks, from CIS Controls to NIST CSF. They all tell us what needs to be done: access management, data protection, incident response, governance, monitoring, training.
What they don’t tell us is how much is enough. Organizations know they need physical security, policies and monitoring, but how much investment, effort, and oversight is appropriate for their context?
This is where maturity models add value. They help identify how well cybersecurity is being managed, how consistently it is applied, and how effectively it supports the organization’s objectives. In other words, cybersecurity maturity is less about the existence of controls and more about an organization’s capability and processes:
- Are governance processes ad hoc, or repeatable and standardized?
- Are they measured and continuously improved?
- Do they align with the organization’s risk thresholds, business objectives, and regulatory requirements?
By answering these questions, maturity models help to identify the gaps to improve capabilities and processes that are organization specific.
Frameworks that define maturity
There are some established cybersecurity frameworks that define maturity along a spectrum and can be applied directly to cybersecurity governance. Each of them provides a structured way to evaluate how well processes are embedded, repeatable, and continuously improved. While their origins differ, they share a common logic: moving from ad hoc practices to optimized governance.
NIST cybersecurity framework (CSF)
The NIST Cybersecurity Framework 2.0 is widely used as a reference for cyber risk management. It has defined Implementation Tiers to provide a way to measure maturity in both cybersecurity risk governance and risk management outcomes. According to NIST, the tiers “capture an organization’s outcomes over a range: Partial (Tier 1), Risk-Informed (Tier 2), Repeatable (Tier 3), and Adaptive (Tier 4).”
- Tier 1 – Partial: Cybersecurity practices are ad hoc or reactive, with limited governance structures.
- Tier 2 – Risk-Informed: Risks are recognized, and some policies and assessments are in place, but they are inconsistent across the organization.
- Tier 3 – Repeatable: Processes are formalized, documented, and consistently implemented across functions. Cyber risk is considered systematically in governance and decision-making.
- Tier 4 – Adaptive: Practices are proactive, continuously improved, and informed by lessons learned and threat intelligence. Cyber risk governance is dynamic and fully integrated into enterprise risk management.
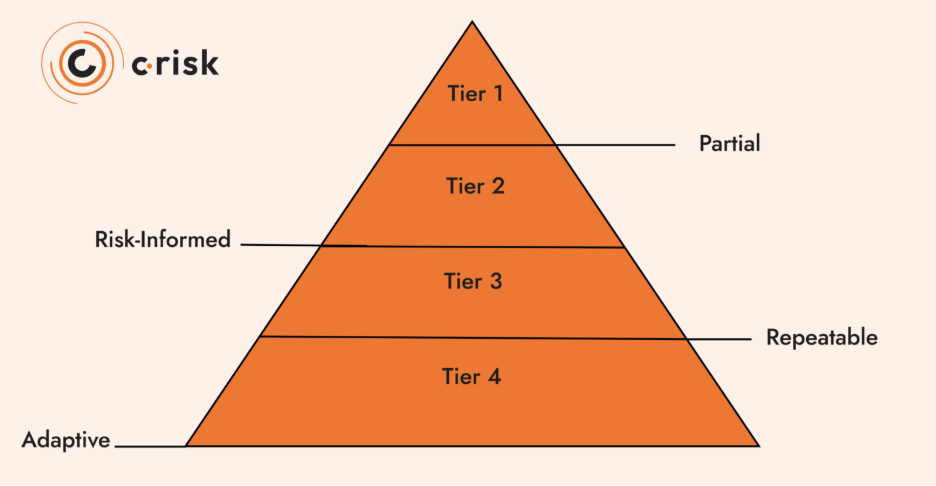
NIST emphasizes that the implementation tiers should guide and inform governance and management methodologies. This tiered approach makes the CSF a useful framework for having board-level discussions.
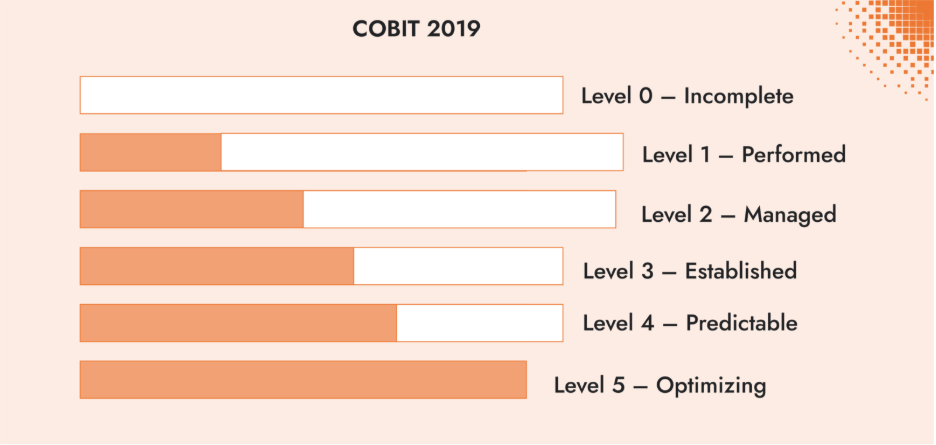
COBIT 2019
COBIT 2019, developed by ISACA, is a framework for designing an IT governance system. It includes a capability model based on CMMI that helps organizations assess how consistently and effectively governance processes are carried out. The model uses six levels, from 0 to 5:
- Level 0 – Incomplete: The process is missing or fails to reliably achieve its purpose.
- Level 1 – Performed: There is a process, but it’s informal and inconsistent.
- Level 2 – Managed: A basic, complete set of activities is in place, and the process usually achieves its purpose.
- Level 3 – Established: The process is well-structured, uses organizational standards and assets, and is consistently applied.
- Level 4 – Predictable: The process is well-defined, tracked and measured for performance.
- Level 5 – Optimizing: The process is measured, continuously improved, and refined based on feedback and performance data.
The COBIT capability levels are often used for assessments and audits, giving organizations a way to describe their governance maturity in structured terms, similar to the NIST CSF implementation tiers.
Assessing cybersecurity maturity
Maturity models are valuable because they outline what different levels of cybersecurity governance look like. They describe the hallmarks of an ad hoc process versus an optimized one. However, they don’t tell you how to advance from one level of maturity to the next. Just as control frameworks list the security functions every organization should have, (e.g., access management, data protection, incident response), without prescribing their exact implementation, maturity models set the broad markers of progress while leaving it to organizations to determine their own roadmap.
That flexibility is both a strength and a challenge. It allows organizations to adapt maturity expectations to their own context, but it can also create some confusion.
What does it mean for our organization to progress from Risk-Informed to Adaptive maturity level, or from Established to Optimizing? How do these maturity shifts translate into new ways of working, decision-making, and delivering value?
Forward-looking approach to cyber maturity
Improving cyber maturity within an organization is not simply about adopting more controls or adding new tools. It is about systematically moving from today’s business reality (the As-Is state) toward a desired future (the To-Be state). This process allows leadership to take an objective look using data-driven risk management methods at what is working, but also what is missing, misaligned, or underdeveloped.
The As-Is/To-Be process:
- As-Is: A clear, evidence-based picture of current practices, governance processes, and cultural attitudes toward cyber risk. This means identifying strengths, weaknesses, and gaps in how cyber risk is embedded into decision-making.
Cyber risk quantification using FAIR is a risk-based methodology to help communicate the strengths and weaknesses in business terms to help drive data-driven decisions.
- To-Be: A defined target state, aligned with the organization’s strategic objectives and risk appetite. This future state describes what effective governance should look like—repeatable processes, consistent oversight, and risk-informed decision-making at all levels.
- Bridging the Gap: The most valuable part of the exercise mapping the path between the two states. This includes prioritizing investments, sequencing changes, and establishing milestones that can be tracked and communicated to stakeholders. And as GRC and risk managers perform ongoing assessments, new gaps could be identified.
As part of a data-driven risk management approach, the as-is / to-be process creates a roadmap for more resilience, better governance and more informed decision-making across an organization. Boards and executives can engage in concrete discussions: not whether controls exist, but whether the organization has the capability to govern cyber risk at the level required by its business strategy and regulatory requirements.
Building a roadmap with the To-Be approach
The To-Be approach allows organizations to build a roadmap that moves from a lower tier to a higher tier of maturity through intentional improvement:
- Strategic planning – aligning a multi-year roadmap with the overall business strategy that considers value chains and risk scenarios.
- Prioritization – focusing on the most critical gaps first, balancing cost, benefit, and resource constraints.
- Change management – engaging stakeholders, communicating progress, and raising awareness of cyber as a business imperative.
- Continuous monitoring – tracking indicators, measuring effectiveness, and adapting the roadmap as the business model, threat landscape and regulatory context evolve.
Maturity as a governance imperative
A data-driven cybersecurity program creates a shared language that allows the board and senior executives to manage in a risk-informed way and address cyber risk with the same rigor as financial or operational risks.
By comparing your organization’s approach to cyber governance and the maturity models, like NIST’s implementation tiers or COBIT’s capability levels, organizations can demonstrate accountability, benchmark against peers, and build a roadmap for resilience. At the core, maturity means moving from reactive compliance to proactive, risk-informed governance.
From cyber risk assessments to a continuous cyber governance practice
Insights from a cyber governance maturity assessment can help improve governance in a quantifiable way. That requires implementing risk-based and data-driven methods for evaluating the efficiency of controls, quantifying risk in financial terms, and ensuring oversight extends across third parties and supply chains. It also requires people — executives, risk managers, and security leaders — to share a common language when discussing cyber risk.
This is the work we do at C-Risk. We apply data-driven risk management methods and the FAIR standard to cyber risk quantification (CRQ) to help organizations assess their current state and build a roadmap for improvement. Our work ranges from control efficiency assessments to ongoing risk management as a service, the implementation of unified quantitative risk tools, and training programs for boards and risk leaders.
By bringing structure and evidence to the process, we help organizations move from maturity assessment to practice, building the governance capabilities regulators expect and the resilience businesses need.
