Integrating cyber risk management into Enterprise Risk Management (ERM)
Enterprise Risk Management (ERM) is designed to break down information silos and give organizations a coherent view of risk across all functions. ERM aims to minimize unexpected performance shocks and ensure consistent risk management at every level of the business. Yet the current state of cybersecurity presents a paradox that challenges this vision. Despite significant investment in time and money, over 70% of large UK businesses experienced some form of cyberattack last year, making it clear that cyber risk cannot be managed in isolation.
The good news is that organizations are beginning to close this gap. The average cost of a cyber incident has fallen 9% to $4.4 million, driven by better cyber governance. This shift reflects a broader transformation: cyber risk management is evolving from a technical silo into a core component of ERM.
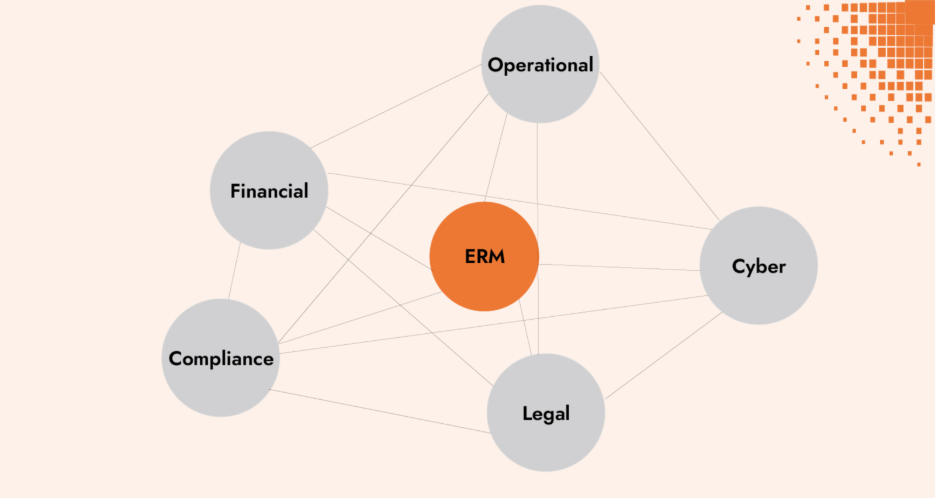
- Cyber as a core component of ERM Cyber threats are too complex and interconnected to be managed in isolation. Embedding them into enterprise risk management gives leaders a complete view of exposures across the business.
- Interdependencies need to be managed holistically A cyber incident can cascade into operational disruption, financial losses, reputational harm, and compliance failures.
- Aligning frameworks for a common view NIST CSF, FAIR, ISO 27005 ensure that cyber risk management fits into the same governance cycles, reporting, and language as other risk domains.
- Quantification supports cyber integration in ERM Using methods like FAIR brings cyber into financial terms, making it directly comparable with other enterprise risks.
Evolution of ERM and its intersection with cyber risk management
Early origins and the "firmwide" concept
The concept of integrated risk management began taking shape in the early 1990s. James Lam, widely recognized as the first-ever Chief Risk Officer (CRO) and a pioneer of ERM, introduced the idea of “firmwide risk management.” His perspective emerged from recognizing that managing risks in isolated silos, such as credit, market, and operational risks, was inefficient and often misleading. Instead, he advocated for a holistic approach where risks were managed on an integrated basis, using tools such as economic capital to address interdependencies consistently across the enterprise. This was the foundation of what we now call Enterprise Risk Management.
Formalization and industry standardization of risk management
Lam’s 2003 book Enterprise Risk Management: From Incentives to Controls became a cornerstone in formalizing enterprise risk management and driving corporate adoption. In the book, Lam predicted several key trends that have since materialized:
- ERM as the Industry Standard: Today, the majority of large public companies with revenues exceeding $1 billion have ERM programs in place.
- Rise of the CRO Role: All industries have adopted the Chief Risk Officer role alongside financial institutions.
- Institutionalization of Risk Education: Risk management has become part of corporate training programs, expanding awareness and expertise across organizations.
Board-Level attention and expanding scope
Over the past two decades, corporate boards have undergone a dramatic shift in their approach to risk oversight. Once relegated to the bottom of the agenda, risk discussions now occupy center stage. Directors increasingly view ERM as a critical mechanism for influencing strategic decision-making and safeguarding long-term value.
ERM’s scope has also broadened significantly, now addressing:
- Governance and board-level oversight
- Strategic risk
- Cybersecurity
- Disruptive and existential risks
Understanding risk as a range of possibilities
Risk is best understood not as a single outcome but as a range of potential outcomes, each with its own probability and impact.
This perspective mirrors the FAIR methodology, where risk is defined as the probable frequency and magnitude of future loss. In this view, the goal of risk management is not to eliminate risk, but to reduce uncertainty and enable better decision-making.
Key principles :
- Risk-taking is essential: Every business must take risk to survive and grow. The question is not whether to take risk but which risks to take, and how much.
- Balanced view of upside and downside: While risk can lead to losses, it is also the source of innovation, growth, and competitive advantage.
- Focus on variability, not absolutes: Measuring and managing the distribution of outcomes, particularly the unexpected tail risks, creates stability and supports long-term value creation.
The interconnected nature of risk
Cyber, operational, financial, compliance and legal risks are deeply interconnected and treating them in silos leaves organizations exposed. A modern ERM lens highlights how these risk categories converge and why boards must address them together.
Why interdependencies matter
It no longer makes sense to manage cybersecurity separate from other enterprise risks. Interdependencies are everywhere:
- Operational disruption: A cyber incident can impact critical systems, supply chains and damage customer trust.
- Financial impact: Breaches or compliance failures translate directly into financial costs, i.e., regulatory fines, litigation, share price volatility or lost revenue.
- Reputational fallout: Customers, partners, and regulators view failures holistically. Even if the “root cause” is technical, the perception is a failure of governance and culture.
- Compliance and legal exposure: A cyber incident can quickly escalate requiring regulatory reporting.
- Strategic trade-offs: Decisions in one area may reduce some operational costs while introducing new cyber dependencies and third-party risks.
Inefficiencies and blind spots
When cyber risk is managed as a silo without consideration of the other enterprise risks, inefficiencies and blind spots inevitably emerge. For example, duplicative controls may waste resources, while gaps between cyber and operational planning leave organizations unprepared.
ERM and cyber: The case for quantification
Enterprise Risk Management has always relied on quantification to make risk decisions consistent across the enterprise. Models such as economic capital were created to allocate resources across different risks on a comparable basis, enabling leaders to judge where to deploy capital and how much risk to accept.
In many large organizations, cyber is still managed with heat maps or control checklists that are really just about ticking compliance boxes. They look tidy in a report, but they don’t inform defendable decisions. You can’t compare the results across the business or use them to decide what to fix first.
Cyber risk quantification
Cyber Risk Quantification (CRQ) and the Open FAIR standard model and measure cyber and technology risk in financial terms, using the same type of probability distributions applied to market, credit, and operational risk. CRQ translates uncertainty into a language executives already understand. This makes cyber risk directly comparable within ERM, enabling more coherent decisions about investment, prioritization and risk appetite.
Why quantification matters
- Integration: Cyber can be assessed alongside financial, operational, and strategic risks in the same terms
- Decision-making: KRIs and KPIs guide investment, insurance and risk appetite decisions
- Value creation: Data-driven and risk-based analysis allows organizations to embrace digital opportunities, provided the expected return outweighs the risk
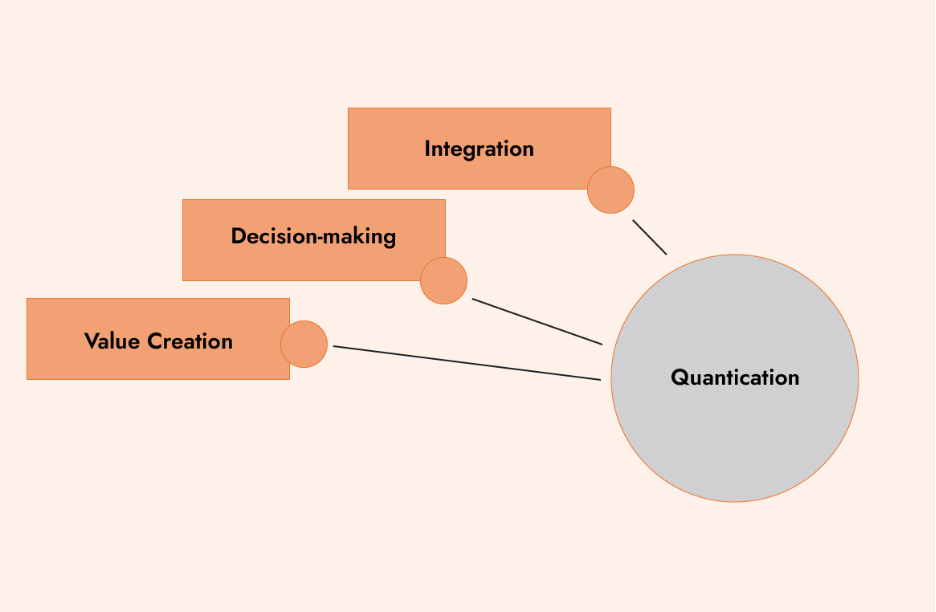
By including cyber risk as part of ERM, organizations move from subjective judgments to data-driven strategy. This integration allows leaders to make trade-offs with confidence, ensuring cyber risk is not just managed, but leveraged to create value.
Methodological alignment and common frames of reference
One of the biggest barriers to integrating cyber into Enterprise Risk Management is the fragmentation of methodologies. Different teams often use different frameworks, vocabularies, and reporting styles. The result of this can be the duplication of efforts, misinterpretation of reports or blind spots. To overcome this, organizations need to measure and manage cyber risk using the same language, metrics and governance cycle as other enterprise risks.
Cybersecurity frameworks
Cybersecurity has a rich ecosystem of frameworks, each serving a different purpose. The NIST Cybersecurity Framework (CSF) and ISO/IEC 27005 are widely used by CIOs and CISOs as operational guides. They provide structured approaches to controls, processes, and day-to-day information security risk management. These frameworks are invaluable for practitioners, but they stop short of answering the question boards and executives care most about: how much risk do we have, and what does it mean in business terms?
This is where FAIR provides critical value. FAIR complements operational frameworks by translating cyber exposure into financial terms. It aligns with standards such as NIST CSF and ISO 27005, creating a common analytical lens that allows cyber risk to be measured, compared, and communicated alongside other enterprise risks. With FAIR, security leaders can present decision-ready, financially grounded recommendations to executives and boards.
At the enterprise level, ISO 31000 and COSO ERM frameworks define the governance structures within which all categories of risk — financial, operational, strategic, and cyber — should fit. They set principles for risk appetite, reporting, and alignment with strategy.
When harmonized, these frameworks work together:
- NIST CSF / ISO 27005 for operational cybersecurity risk management
- FAIR for analytical quantification in financial terms
- ISO 31000 / COSO ERM for enterprise-wide governance and strategic integration
Shared tools for cyber risk management
Equally important is a common tool for managing digital risk. A unified cyber risk management platform to support third-party risk management, compliance risk, new initiatives, mergers and acquisitions, etc.
- Shared metrics and repositories that eliminate duplication and ensure a consistent record of exposures and incidents
- Consolidated dashboards that integrate cyber risks into the broader ERM view, giving directors a clear picture of vulnerabilities, controls and trends.
Using shared metrics allow cyber risks remain to be part of the enterprise risk management conversation, enabling leaders to weigh trade-offs.
Thinking in terms of cyber value will lead to business-justified decisions, such as increasing cyber risk exposure for an innovative new product or service, when the reward clearly outweighs the risk and it is within risk appetite.
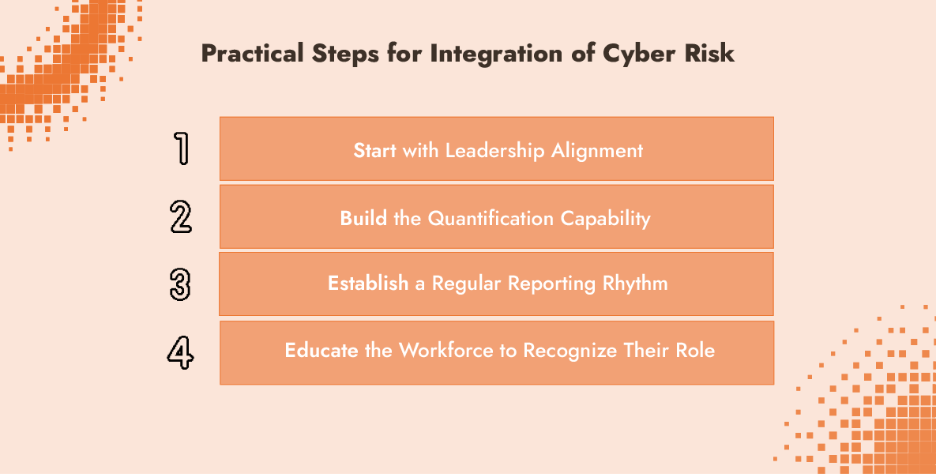
Practical steps for integration of cyber risk
The journey from siloed cybersecurity to integrated cyber value does not happen overnight. Organizations that successfully embed cyber risk into their ERM programs tend to follow a deliberate path:
- Start with Leadership Alignment
Integration begins at the top. Executives and directors need a shared understanding of cyber risk as part of enterprise strategy. This means moving past fear-based narratives of hackers and breaches toward discussions framed in terms of risk tolerance, investment trade-offs, and value creation. When the C-suite and the board speak about cyber risk in the same language as market, credit, or operational risk, convergence with ERM becomes natural rather than forced. - Build the Quantification Capability
What cannot be measured in business terms cannot be managed effectively. Building cyber risk quantification capabilities requires investment in tools, but also in people. Risk professionals should learn to apply quantitative methods to cyber scenarios, while cybersecurity teams strengthen their expertise in risk modeling. The goal is a shared analytical foundation that bridges technical detail with financial and strategic impact. - Establish a Regular Reporting Rhythm
Cyber risk should follow the same cadence and structure as other enterprise risks. This includes periodic reporting to the board using consistent metrics, integration into strategic planning cycles, and explicit alignment with the organization’s risk appetite statements. Regular, comparable reporting ensures cyber risk is evaluated on equal footing with other risks. - Educate the Workforce to Recognize Their Role
Finally, integration depends on people across the enterprise. Employees at all levels influence the organization’s cyber posture, whether through daily decisions, process design, or strategic initiatives. Training should help the workforce understand how their actions affect both risk and value creation. Embedding this awareness into culture ensures that cyber risk management is a shared responsibility aligned with enterprise objectives.
From cybersecurity to cyber Value: A measured progression
The shift from cybersecurity to cyber risk, and ultimately to cyber value, reflects the natural maturation of how organizations understand cyber risk. Instead of treating cyber exposure as something to avoid at all costs, leaders are beginning to view it as a strategic factor that can be measured, managed, and balanced against opportunity. By applying data-driven methods to reduce uncertainty, organizations gain clearer insight into trade-offs, strengthen resilience, and make better-informed decisions that support both protection and growth.
Practical benefits of ERM integration
When cyber risk becomes part of the ERM framework, concrete benefits emerge:
- Resource Optimization: Organizations can allocate security investments based on actual risk reduction.
- Improved Decision-Making: Board and executive discussions shift from technical vulnerabilities to business impacts.
- Operational Efficiency: Common frameworks and shared metrics eliminate duplicate assessments and conflicting risk ratings.
Toward a unified view of risk
There is no single maturity threshold required to begin integrating cyber risk into Enterprise Risk Management. Organizations with established ERM programs can extend existing governance structures and risk appetite frameworks to include cyber as another risk category. Those at an earlier stage may use cyber risk as a starting point to formalize broader risk processes, given its clear business impact and attention at the board level. Likewise, companies with mature cybersecurity functions but limited ERM integration can begin by translating technical measures into business-relevant terms, such as expressing patching performance in terms of financial exposure.
Integration is effective when adopted incrementally. A pilot project focused on quantifying a single cyber scenario, a proof-of-concept for a single business unit, or alignment of third-party risk across cyber and operational functions can demonstrate the value of including cyber within the ERM ecosystem.
Widely adopted frameworks support this process: FAIR for quantification, NIST for operational management, and ISO 31000 or COSO for enterprise governance. These tools are designed to be layered rather than implemented simultaneously, allowing organizations to build progressively. The outcome is a more consistent and comparable view of risk across categories, supporting clearer reporting and better-informed decisions.
Turning insight into action with C-Risk
C-Risk helps organizations put these principles into practice by making cyber risk measurable, comparable, and actionable within Enterprise Risk Management. Our services combine expertise, training, and practical implementation to align cyber with strategy and governance.
How C-Risk supports your journey:
- Cyber Risk Quantification (CRQ): Translate cyber risk into financial terms to inform board decisions, justify budgets, and clarify exposure using FAIR-based analysis.
- Training & Education: Equip executives, CISOs, and risk professionals with the skills to apply data-driven risk management through instructor-led and e-learning programs.
- Consulting & Advisory: From tailored CRQ projects to regulatory planning, we provide expert guidance backed by measurable data.
- Platform Support & Integration: Accelerate ERM integration with a unified CRQ platform that deliver real-time, financial-impact dashboards into your governance and reporting processes.
