Roles and responsibilities in cybersecurity governance
In today’s interconnected business environment, cybersecurity governance has evolved into a core pillar of enterprise resilience and long-term value preservation. It is no longer a technical concern confined to the IT department. Instead, it is a multi-disciplinary approach, requiring engagement from boards of directors, executive leadership, operational managers, and external stakeholders.
The digital transformation of global business has led regulators to increase scrutiny of how companies manage risk. Recently, the EU NIS2 Directive and the US SEC Cybersecurity Disclosure Rules have raised expectations for corporate accountability for cybersecurity. As expectations evolve, governance models must adapt. Clearly defined roles and responsibilities allow organizations to respond quickly when incidents do happen, allocate resources effectively, and build a risk-aware culture.
- Cybersecurity is a Core Governance Priority
Boards cyber risk alongside enterprise risk management.
- Clear Roles Drive Faster Response
Distinguishing accountability from responsibility strengthens resilience.
- Proven Principles Guide Board Oversight
Six WEF-endorsed practices shape effective governance.
- Committees Connect Strategy to Execution
Structured reviews keep cyber risk aligned with business goals.
- External Stakeholders Shape Governance
Regulators, partners, and investors influence risk priorities.
The evolving cyber risk governance landscape
As threat environments grow more complex, governance models must adapt. Only a few years ago, many organizations treated cyber risk management as a siloed IT function. Today, successful business leaders treat cybersecurity as a board-level governance issue alongside enterprise risk management.
Clarity over who owns the risk (accountability) and who manages the risk (responsibility) is central to building cyber resilience. This distinction enables organizations to respond decisively during incidents, allocate resources effectively, and maintain a culture where accountability extends from strategic oversight to operational execution.
Cybersecurity governance at the board level
Boards of directors with a strong focus on cybersecurity governance take responsibility for ensuring that cyber risk is managed within the organization’s risk appetite. This requires ongoing engagement with cross-functional teams and committees to understand what resources are needed and the support they need.
From a compliance perspective, boards also have increasing pressure to manage cybersecurity from the top.
For example, the introduction of NIS2 in the EU imposes direct obligations on senior management to oversee cybersecurity risk management measures. Similarly, the SEC’s 2023 rules in the US require publicly listed companies to disclose material cyber incidents and detail governance practices in their annual reports. These developments are shaping how boards approach oversight, moving from passive review to informed governance participation.
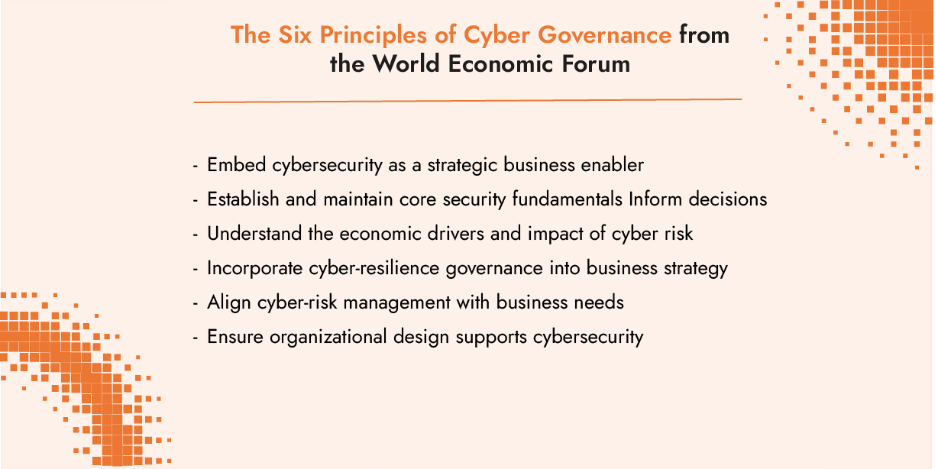
The World Economic Forum has defined six consensus-based principles for board governance of cyber risk:
- Embed cybersecurity as a strategic business enabler
- Establish and maintain core security fundamentals
- Understand the economic drivers and impact of cyber risk
- Incorporate cyber-resilience governance into business strategy
- Align cyber-risk management with business needs
- Ensure organizational design supports cybersecurity
Linking cyber strategy and operations: The role of committees
In many organizations, cybersecurity oversight is delegated to a board subcommittee, often the Audit Committee or Risk Committee. These committees act as the bridge between strategic oversight and operational implementation.
- Audit Committees focus on the reliability of internal controls, reviewing findings from cybersecurity audits, and ensuring that remediation steps are tracked and completed.
- Risk Committees evaluate whether cyber risk levels remain within the defined appetite and whether mitigation measures are effective and aligned with broader enterprise risk management (ERM) strategies.
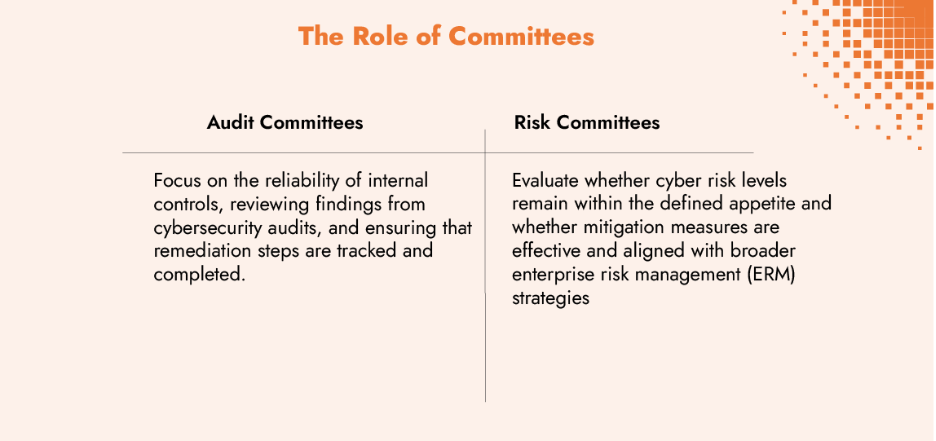
The cadence of meetings and reporting to the board is key. Leading organizations use structured quarterly committee reviews, supplemented by ad-hoc meetings when emerging threats or incidents require board attention. Committees often receive input from the Chief Information Security Officer (CISO), Chief Risk Officer (CRO), Chief Financial Officer (CFO), and Legal Counsel, ensuring that reporting is both technically accurate and strategically relevant.
What is the Role of Executive Leadership in Cyber Governance?
While boards set the tone, executive leaders operationalize cyber risk governance. Their coordinated actions determine whether cyber strategy is effectively embedded into business operations:
- Chief Executive Officer (CEO): Ensures that cyber risk management is integrated into corporate strategy and culture
- Chief Financial Officer (CFO): Aligns cybersecurity investments with fiscal strategy, evaluating potential return on security investment (ROSI)
- Chief Risk Officer (CRO): Merges cyber risk into the broader ERM framework, ensuring consistent treatment alongside financial, operational, and regulatory risks
- Legal Counsel: Provides interpretation of legal and contractual obligations, particularly during incident response scenarios
- Chief Information Security Officer (CISO): Holds operational responsibility for assessing and managing cyber risk, producing reports that cover:
- Cyber risk posture
- Threat landscape updates
- Control maturity
- Operational and business impact
- Planned and ongoing investments in cyber resilience
The integration of the CISO role into senior leadership varies. In some organizations, the CISO reports directly to the board; in others, they report through the CIO, COO, or CEO. Research by ISACA shows that direct board access often correlates with greater investment in cyber resilience and faster escalation of critical threats.
How do external stakeholders influence governance decisions?
Cybersecurity governance extends beyond the organization’s walls. External parties often play a critical role in shaping cybersecurity governance:
- External auditors and consultants provide independent assessments of your risk posture and give feedback about how to improve prioritization, controls or reporting.
- Regulators require documented evidence of governance activities.
- Shareholders want to understand how you are protecting their interests.
- Customers and partners request evidence of cybersecurity governance and controls before entering into contracts.
- Investors, particularly in mergers and acquisitions, evaluate cyber resilience as part of due diligence.
A study in Verizon’s 2025 Data Breach Investigations Report found that 30% of data breaches involved a third-party, underscoring the importance of extending cybersecurity governance to the extended enterprise.
How to structure responsibilities for effective governance
Effective governance depends on a structured approach to defining and coordinating responsibilities:
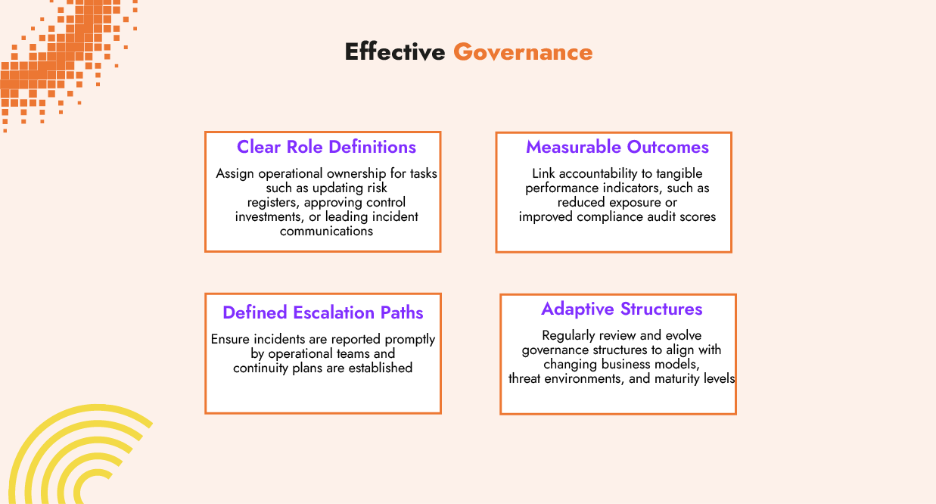
- Clear Role Definitions: Assign operational ownership for tasks such as updating risk registers, approving control investments, or leading incident communications
- Measurable Outcomes: Link accountability to tangible performance indicators, such as reduced exposure or improved compliance audit scores
- Defined Escalation Paths: Ensure incidents are reported promptly by operational teams and continuity plans are established
- Adaptive Structures: Regularly review and evolve governance structures to align with changing business models, threat environments, and maturity levels
Breaking down silos: A shared language for risk
One of the most persistent challenges in cyber governance is the silo effect, the isolation of information within specific departments. Siloed management slow down decision-making and can lead to duplicated efforts by teams across functions.
A shared language for risk is a key to unlocking better communication. By using quantification frameworks like FAIR, CISOs can translate technical threats into financial risk terms that resonate across the organization. This enables teams to weigh cyber investments alongside other activities, and to contextualize the tangible, real-world impact of an incident.
Regular joint risk reviews, integrated dashboards, and aligned reporting formats ensure that decision-makers across functions work from a common set of data and assumptions.
Cyber Resilience as a Function of Collaboration
Effective cybersecurity governance is dynamic. The cyber threat landscape is constantly in flux and the regulatory landscape is trying to protect the interests of businesses, consumers and shareholders. The success of a governance program can be measured how well information flows, decisions are coordinated, and a company can recover in the event of a cyberattack.
In high-performing organizations, the board defines the level of cyber risk the business is willing to accept, senior executives translate that into a growth strategy, and operational teams execute within an adapted framework that supports the decisions at the top. This chain of accountability is especially important when regulators, investors, or customers demand evidence. Under frameworks such as the EU’s NIS2 Directive, for example, a regulator may ask a board to produce the minutes from the last meeting where cyber posture was reviewed, controls assessed, and actions agreed. The ability to respond quickly and comprehensively is both a compliance requirement and a sign of governance maturity.
Cyber resilience depends on the cooperation across functions. When risk, legal, cyber, and operational leaders work from different assumptions, misalignment is inevitable. But when risk is expressed in consistent, measurable terms, security and risk leaders can shift from abstract qualitative, biased opinions to concrete decisions about prioritization and action.
Partner with C-Risk to Build Measurable, Board-Ready Cyber Resilience
At C-Risk, our team of cybersecurity and risk management experts help organizations turn complex cyber risk governance challenges into actionable solutions. We focus on reducing bias and supporting decisions with our data-driven approach. We complement traditional risk management methods with a quantitative methodology to assess cyber risk in financial terms, enabling clear communication across teams and with the board.
Our data-driven As-Is / To-Be approach identifies gaps, prioritizes investments and helps align cybersecurity initiatives with your business strategy. We help streamline cyber risk management and third-party risk management with the SafeOne unified cyber risk management platform from Safe Security.
