Cyber risk communication: a practical guide for CISOs and executives
Nearly one in two executives say their CISOs need urgent improvement in how they communicate about risk. In fact, an FTI Consulting survey published by the Wall Street Journal found that 98% of executives support more funding for training CISOs in communication, with 45% calling it an immediate need. The message is clear: misaligned communication between security leaders and senior decision-makers is a major barrier to effective cyber risk management. When boards can’t connect cyber metrics to business outcomes, critical investments get delayed, underfunded, or misunderstood.
Fixing this problem starts with shifting the role of cyber communication. It is not about flooding directors with technical details or employees with compliance checklists. It is about telling a clear, credible story of risk, grounded in data, framed in business terms, and tailored to the audience. Whether it’s the board deciding on risk appetite, an audit committee reviewing controls, or a non-technical employee recognizing and reporting suspicious activity, the CISO’s role is to make the complex understandable and the invisible tangible. This article offers a practical guide for executives and CISOs to bridge those communication gaps and build cyber resilience through contextualized, outcome-oriented dialogue.
- Information silos are outdated Clear, cross-functional communication is now essential for effective cyber risk governance
- Data-driven methods reduce bias and fear Objective quantification helps prioritize initiatives that create measurable business value
- CRQ reframes cyber risk in financial terms Cyber threats can be weighed alongside supply chain disruption, compliance penalties, or market volatility
- Transparent communication builds trust CISOs earn credibility when risk is presented with evidence, consistency, and financial context
- Effective dialogue drives resilience Communication strategic capability for business continuity and growth
Communication challenges in across business functions
Effective communication is at the heart of good governance and decision-making. Yet even in organizations with solid governance structures, communication within a single department or across functions can break down. Some common business communication challenges include:
- Unclear communication channels
- Information overload
- Different communication styles
- Cultural differences
- Poor documentation
- Lack of feedback
These are familiar challenges in any corporate setting. But when it comes to cyber risk communication, the challenges are magnified.
Cyber risk communication challenges for CISOs and executives
In cyber risk communication, it is critical to ensure that you adapt your communication to your audience. For one, cyber risks can be interpreted by non-technical executives and management as too technical. It is the job of the communicator to adapt their language so that the audience is comfortable with the subject and familiar with the concepts presented.
If a CISO presents to the audit committee using primarily infosec telemetry and neglecting the business context, committee members could misinterpret information, leading to less effective decisions. A CISO who can speak in business terms, i.e., in terms of risk appetite, financial loss, return on investment will greatly improve the quality of cross-functional interaction. The FTI survey highlights the tension: 31% of C-suite executives say they struggle to understand the ROI of cyber investments.
There is a proven way to explain the ROI of cyber investments and the financial impact of cyber incidents. By translating technical metrics into business outcomes, measuring how security initiatives reduce financial exposure, protect revenue streams, and enable business growth, CISOs can bridge this communication gap. The key lies in quantifying risk reduction in monetary terms and connecting security investments directly to business objectives.
Transitioning from technical metrics to business language
Good communication assumes that all parties are operating at a common level of understanding. In cyber risk discussions, this fundamental assumption can break down. CISOs measure success in patch compliance and maturity scores. Executives measure success in ROI and capital efficiency. Without a shared framework for understanding, even the most critical security conversations might fail to drive effective action.
CISOs traditionally organize their work around technical domains:
- Cyber Risk Management - Security posture, threat landscape, control effectiveness
- Vulnerabilities & Threats - CVEs, threat intelligence, attack surface
- Compliance & Governance - Regulatory requirements, audit findings, policy adherence
- Incident Response - Detection rates, response times, recovery capabilities
- Security Operations - Monitoring coverage, alert volumes, investigation metrics

While these domains are essential for information security risk management, they present a challenge: How do you translate "1,200 unpatched vulnerabilities" or "Tier 3 NIST maturity" into business impact? How do you compare cyber risk against supply chain disruption or market volatility when making investment decisions?
Leading CISOs are adopting quantitative risk methodologies that transform these technical metrics into financial language. By expressing cyber risk in terms of probable loss scenarios, expected annual losses, and risk reduction ROI, they enable true apples-to-apples comparison with other business risks.
This shift toward data-driven, financially grounded cyber risk quantification is reshaping how security leaders communicate across functions and with executives. Methods like Data-Driven Risk Management provide the framework for more objective security metrics that drive defendable decision-making.
Bridging the gap: How data-driven risk methods transform communication
Cyber Risk Quantification and Data-Driven Risk Management fundamentally change how security and risk teams communicate risk across the enterprise
Understanding CRQ and DDRM
Cyber Risk Quantification (CRQ) applies rigorous statistical and financial modeling to express cyber risks in monetary terms. Using frameworks like FAIR (Factor Analysis of Information Risk), CRQ moves beyond subjective risk ratings to provide:
- Probabilistic loss scenarios - Not "high/medium/low" but "15% chance of €2-5M loss"
- Expected annual losses - Aggregated financial exposure across all cyber scenarios
- Risk reduction ROI - Clear financial returns on security investments
Data-Driven Risk Management (DDRM) extends this approach by embedding quantification into ongoing risk management processes, creating feedback loops between risk assessment, control implementation, and business outcomes.
How CRQ and DDRM elevate communication
1. Creating a shared financial language
Quantification translates abstract cyber threats into the financial language executives use daily. When a CISO can demonstrate that a specific vulnerability creates an €8M expected loss with a 12% annual probability, it becomes comparable to other enterprise risks like supply chain disruption or market downturns.
Example: Instead of reporting "critical vulnerabilities in customer-facing systems," the CISO presents: "Our e-commerce platform vulnerabilities translate to a 15% probability of breach this year, with expected losses ranging from €5M to €12M, including incident response, regulatory fines, and customer churn."
2. Enabling objective prioritization
DDRM replaces subjective debates with data-driven prioritization. By calculating the risk reduction per euro (dollar, pounds, etc.) invested, security teams can rank initiatives by their actual business impact.
*Example: Three competing initiatives—
- Cloud security improvements: €2M investment reduces expected losses by €8M
- Multi-factor authentication upgrade: €1M investment reduces expected losses by €3M
- Security awareness training: €500K investment reduces expected losses by €4M
The return on security risk investments becomes clear: prioritize training (8:1 return), then cloud security (4:1), then MFA (3:1).*
3. Reducing subjectivity and bias
DDRM grounds discussions in objective data alongside subject matter experts. When risk assessments include statistical modeling based on internal and industry data, it becomes harder to dismiss cyber risks as "IT problems" or inflate them through fearmongering.
When cyber risk discussions shift from technical jargon to financial impact, from subjective ratings to data-driven analysis, and from isolated metrics to business outcomes, the way risk is understood and managed changes. CISOs become strategic partners, and cyber risks can be assessed alongside other enterprise risks in boardroom decisions.
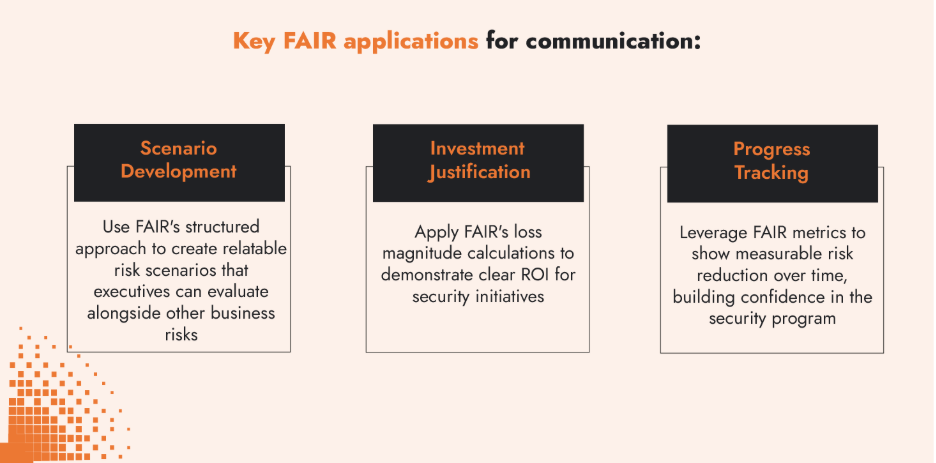
Leveraging FAIR for consistent communication
The Factor Analysis of Information Risk (FAIR) framework provides CISOs with a standard taxonomy for risk communication. By breaking down risk into measurable factors like threat frequency, vulnerability, and impact, FAIR enables consistent, comparable risk discussions across the enterprise.
Key FAIR applications for communication:
- Scenario Development: Use FAIR's structured approach to create relatable risk scenarios that executives can evaluate alongside other business risks
- Investment Justification: Apply FAIR's loss magnitude calculations to demonstrate clear ROI for security initiatives
- Progress Tracking: Leverage FAIR metrics to show measurable risk reduction over time, building confidence in the security program
Adapting communication for different audiences
Board communication: governance and strategic oversight
Board-level communication must address fundamental questions of risk tolerance, competitive positioning, and resource allocation. Effective presentations provide directors with the context and metrics to make informed decisions about cyber risk acceptance, mitigation initiatives, and oversight priorities, while maintaining alignment with broader enterprise risk management frameworks.
Key elements for board presentations:
- Link cyber risk to enterprise risk and risk appetite statements
- Present risk scenarios in terms of potential impact on revenue
- Frame security investments as enablers of digital transformation initiatives
- Use peer benchmarking data to provide context for cyber maturity levels
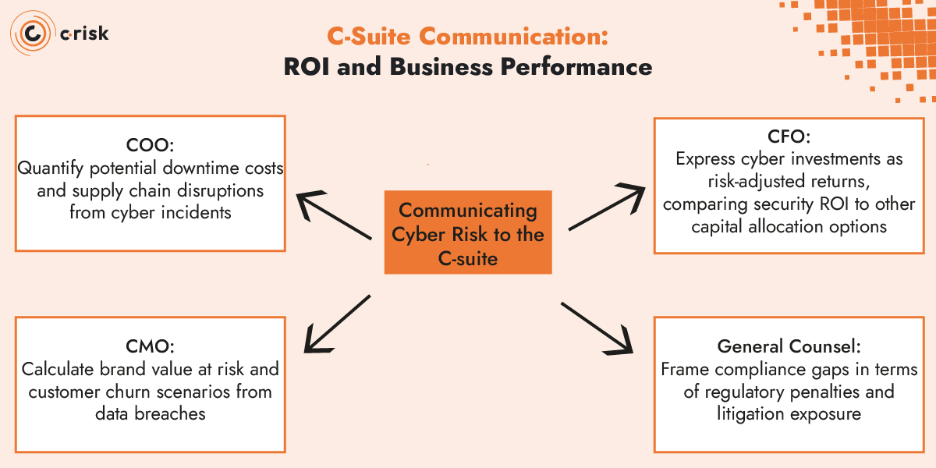
C-Suite communication: ROI and business performance
C-suite executives require cyber risk information that directly connects to their operational metrics and business performance indicators. Unlike board-level governance discussions, executive conversations focus on immediate business impact, resource allocation decisions, and competitive positioning. Effective communication at this level demands precision in linking security initiatives to measurable business outcomes, whether that's protecting revenue streams, ensuring operational resilience, or safeguarding market position.
Communicating Cyber Risk to the C-suite:
- CFO: Express cyber investments as risk-adjusted returns, comparing security ROI to other capital allocation options
- COO: Quantify potential downtime costs and supply chain disruptions from cyber incidents
- CMO: Calculate brand value at risk and customer churn scenarios from data breaches
- General Counsel: Frame compliance gaps in terms of regulatory penalties and litigation exposure
Communicating with operational security teams
Security teams require clear guidance on risk reduction priorities backed by measurable outcomes. Data-Driven Risk Management transforms traditional security operations by creating direct connections between technical actions and business risk reduction. The result is more engaged teams who understand their direct contribution to cyber and business resilience, more efficient resource allocation based on risk-adjusted returns, and clearer communication up the chain about what's working and what needs adjustment.
Embedding Data-Driven risk management in communication practices
Data-Driven Risk Management fundamentally transforms how CISOs communicate cyber risk by replacing subjective assessments with quantifiable business impact. This shift from opinion-based to evidence-based communication creates a foundation of credibility.
Building Trust Through Data Transparency
Executive confidence grows when cyber risk assessments demonstrate the same analytical rigor as other business functions. Transparent communication about data sources, calculation methods, and confidence levels transforms security from a black box into a comprehensible business discipline:
- Explain the data: "This €8M loss estimate comes from: 2 hours downtime × €2M/hour revenue + €3M incident response + €1M regulatory fines"
- Acknowledge uncertainty: "We have high confidence (90%) in the €5-10M range, moderate confidence (70%) in the €10-15M range"
- Reference benchmarks: "This aligns with industry reports showing median breach costs of €4.5M for our sector"
Making decisions defendable
Quantification relies on many different data sources to support security decisions. When challenged on investments or priorities, CISOs can point to objective analysis. This approach acknowledges bias and uncertainty and focuses on internal and industry, making it easier to defend decisions to auditors, regulators, or shareholders.
Optimizing presentation formats
Different communication contexts require different formats. The key is matching format to audience needs and time constraints.
Executive dashboards: The power of routine visibility
Regular dashboard reviews with adapted metrics like basic key performance indicators (KPIs) and risk indicators (KRIs) with trends will build familiarity with the threat landscape and how it impacts the business. Effective dashboards use visuals and data to paint a clear picture of the information security program.
Essential dashboard elements:
- Cyber risk exposure trends (in financial terms)
- Control effectiveness mapped to risk reduction
- Investment ROI tracking against projections
- Peer benchmarking on key risk indicators
Data-Driven presentations: Telling the story of risk
Annual reports sometimes require a telling a more complete story backed by data:
Proven presentation structure:
- Current state (As-Is): Quantified risk exposure and control gaps
- Desired state (To-Be): Target risk levels aligned with business strategy
- Investment roadmap: Prioritized initiatives with ROI calculations
- Expected outcomes: Measurable risk reduction milestones
Always lead with the business impact, then explain the technical approach. If it’s done well, senior executives should understand your key message within the first 60 seconds.
The strategic imperative of cyber risk communication
Cyber risk communication fails when information stays trapped in silos or without defendable metrics to contextualize the risk. This disconnect leads to delayed decisions, misallocated resources, and organizations unprepared for the threats they face.
Data-driven risk management changes this dynamic. By quantifying cyber risk in financial terms, it creates a shared language across the enterprise. This approach reduces the bias and subjectivity that plague traditional cyber risk discussions and allows for:
- Better Decisions: When cyber risks are expressed in financial terms, boards can make informed tradeoffs between cyber investments and other business priorities
- Faster Action: Clear ROI calculations accelerate approval for critical security initiatives
- Stronger Alignment: Shared understanding of cyber risk creates unified response to threats
- Enhanced Resilience: Risk-aware cultures detect and respond to threats more effectively
How C-Risk empowers CISOs & executives with data-driven cyber risk communication
At C-Risk, we support security leaders and executives navigate the challenges of managing information security and technology risk. Using risk quantification and data-driven methods, our services, training, and platform enable you to:
- Quantify cyber risk in clear financial terms that resonate with decision-makers
- Prioritize security investments based on measurable return on risk reduction
- Strengthen compliance and third-party risk management with defensible analysis
- Build lasting confidence with boards, regulators, and shareholders
- Reach out to find out how C-Risk can help you translate cyber risk into strategic advantage.
